Article: Access Management Controls
The Importance of Access Management Controls in Cybersecurity
Access management controls play a crucial role in maintaining the security and integrity of digital systems and data within organisations. By implementing robust access management practices, businesses can effectively control who has access to what information, systems, and resources, thereby reducing the risk of unauthorised access and data breaches.
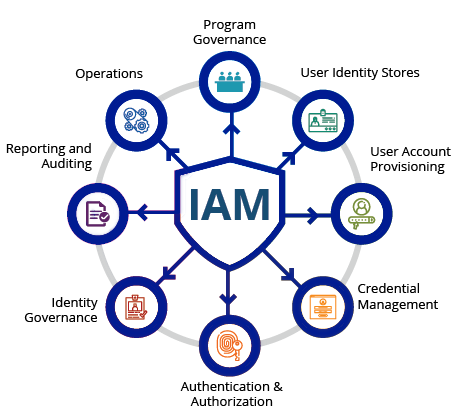
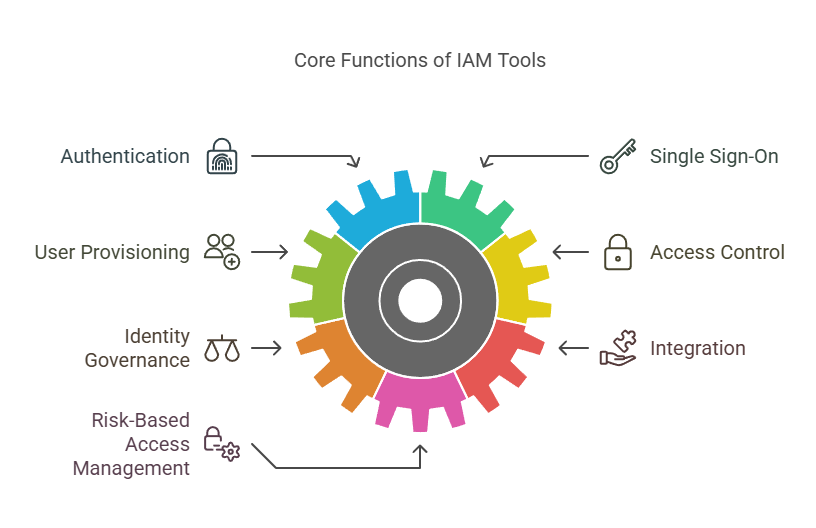
What are Access Management Controls?
Access management controls refer to the processes and technologies used to regulate and manage user access to IT resources. This includes controlling user authentication, authorisation, and permissions throughout the organisation’s network and systems.
The Benefits of Access Management Controls
Implementing strong access management controls offers several key benefits:
- Enhanced Security: By limiting access to sensitive data and systems only to authorised individuals, organisations can significantly reduce the risk of insider threats and external cyber attacks.
- Compliance: Access management controls help organisations meet regulatory requirements by ensuring that only authorised personnel can access certain types of data or systems.
- Improved Productivity: By streamlining access processes and granting appropriate permissions efficiently, employees can focus on their tasks without unnecessary restrictions or delays.
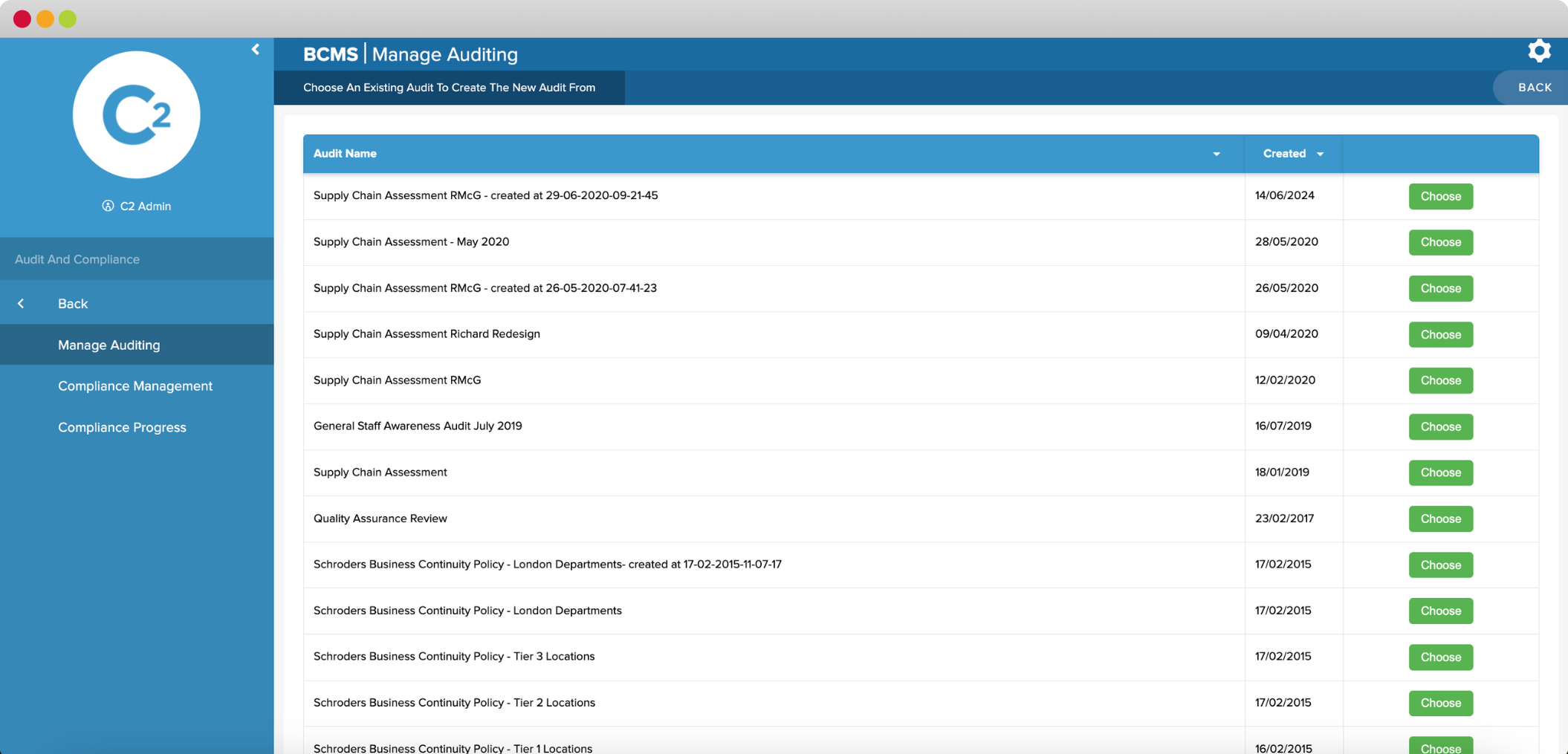
- Auditing Capabilities: Access management controls provide visibility into who accessed what resources at what time, enabling organisations to track user activities for auditing and forensic purposes.
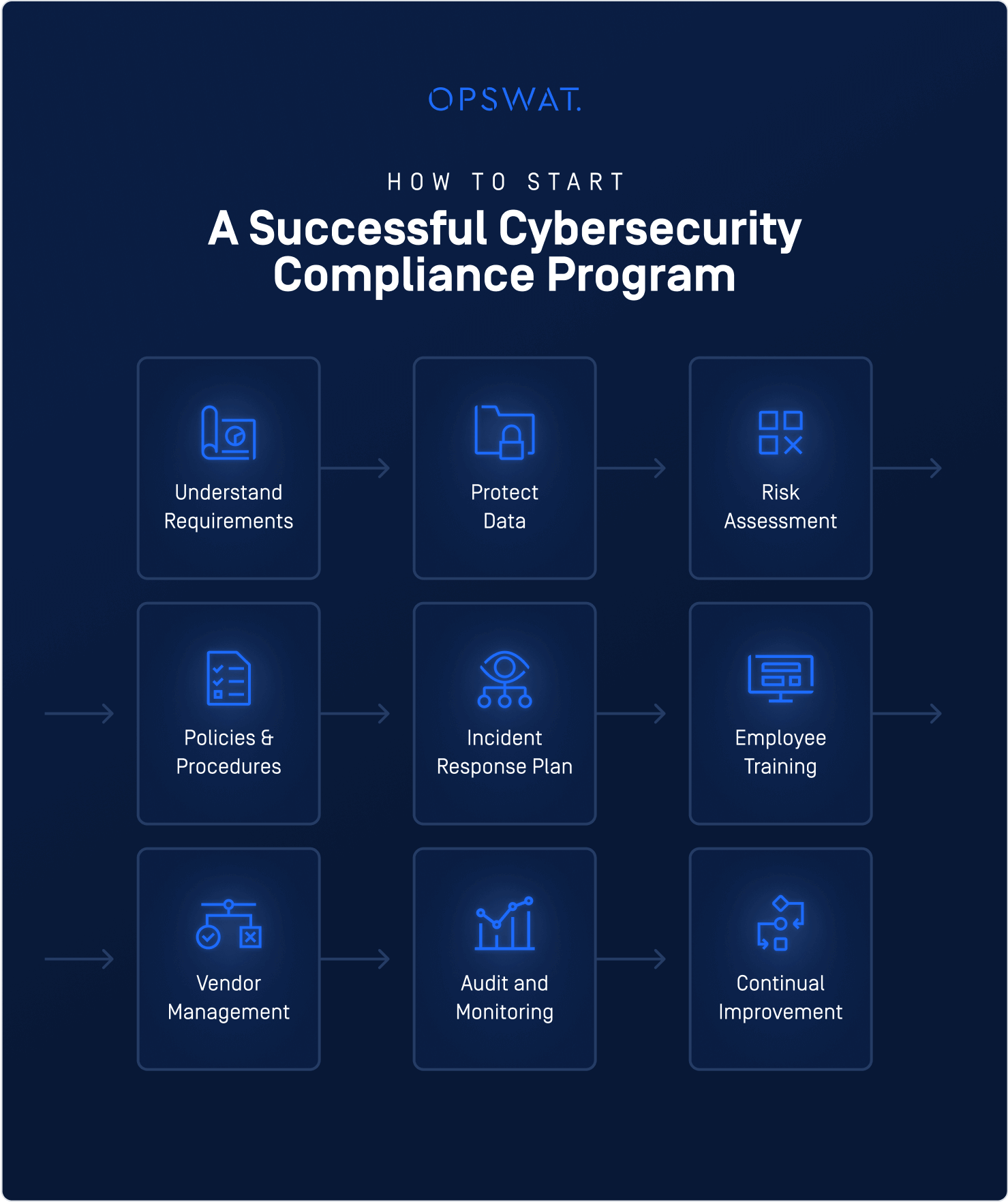
Best Practices for Implementing Access Management Controls
To maximise the effectiveness of access management controls, organisations should consider the following best practices:
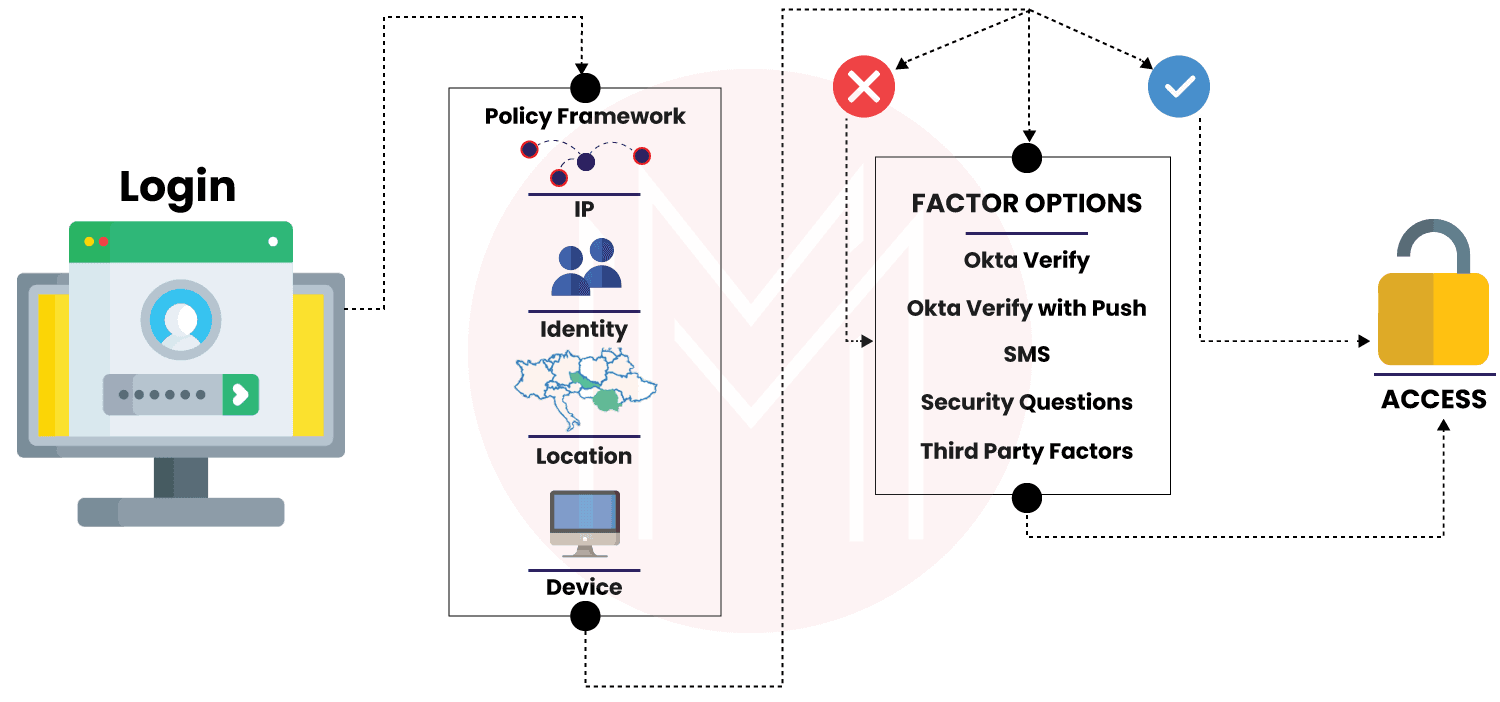
- User Authentication: Implement multi-factor authentication (MFA) to verify user identities securely.
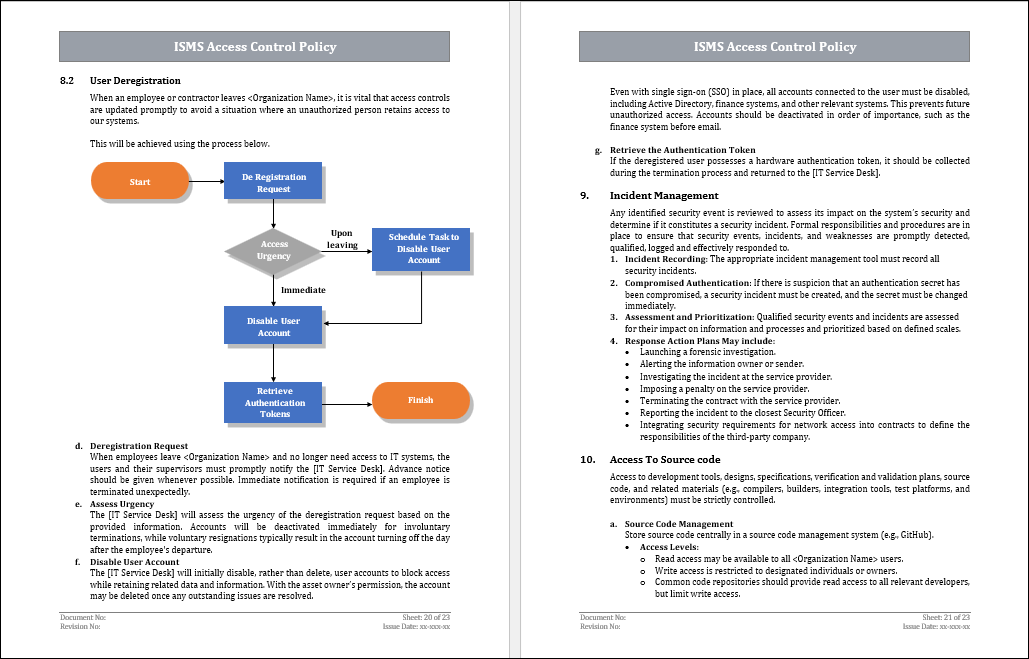
- User Provisioning: Automate user provisioning processes to ensure timely access rights assignment and revocation.
- Role-Based Access Control (RBAC): Assign permissions based on job roles to simplify access management and reduce human errors.
- Ongoing Monitoring: Continuously monitor user activities for suspicious behaviour or policy violations.
- Educate Users: Provide training on security best practices to raise awareness about the importance of access management controls among employees.
In Conclusion
In today’s digital landscape where cyber threats are prevalent, implementing robust access management controls is essential for safeguarding sensitive information and maintaining operational resilience. By adopting best practices in access management, organisations can strengthen their cybersecurity posture and mitigate risks associated with unauthorised access or data breaches.
Nine Advantages of Access Management Controls: Strengthening Security and Compliance
- Enhanced security by restricting access to sensitive data
- Improved compliance with regulatory requirements
- Reduction of insider threats and external cyber attacks
- Efficient user authentication through multi-factor authentication (MFA)
- Streamlined user provisioning for timely access rights assignment
- Simplified access management with Role-Based Access Control (RBAC)
- Enhanced auditing capabilities for tracking user activities
- Increased productivity by granting appropriate permissions efficiently
- Heightened awareness of cybersecurity best practices among employees
Challenges in Access Management Controls: Navigating Complexity, Cost, and Security Gaps
- Complexity
- Cost
- User Resistance
- Single Point of Failure
- False Positives
- Overhead
- Security Gaps
Enhanced security by restricting access to sensitive data
Enhanced security through the restriction of access to sensitive data is a fundamental benefit of implementing robust access management controls within an organisation. By limiting access to confidential information only to authorised personnel, businesses can significantly reduce the risk of data breaches, insider threats, and cyber attacks. This proactive measure ensures that critical data remains protected from unauthorised access, thereby safeguarding the integrity and confidentiality of sensitive information, ultimately bolstering the overall security posture of the organisation.
Improved compliance with regulatory requirements
Improved compliance with regulatory requirements is a significant benefit of implementing access management controls within an organisation. By enforcing strict access policies and permissions, businesses can ensure that only authorised individuals have access to sensitive data and systems, aligning their practices with regulatory standards such as GDPR, HIPAA, or PCI DSS. This proactive approach not only helps in avoiding costly fines and penalties but also enhances trust among customers and stakeholders by demonstrating a commitment to data protection and security compliance.
Reduction of insider threats and external cyber attacks
One significant advantage of implementing access management controls is the reduction of insider threats and external cyber attacks. By restricting access to sensitive data and critical systems to only authorised individuals, organisations can effectively mitigate the risk of malicious activities from within their workforce as well as thwart external attackers attempting to breach their security defences. This proactive approach enhances the overall cybersecurity posture of the organisation, safeguarding valuable assets and confidential information from potential breaches and unauthorised access attempts.
Efficient user authentication through multi-factor authentication (MFA)
Efficient user authentication through multi-factor authentication (MFA) is a key advantage of access management controls. By requiring users to provide multiple forms of verification, such as passwords, biometrics, or security tokens, MFA significantly enhances the security of digital systems. This approach not only strengthens user authentication but also minimises the risk of unauthorised access to sensitive data and resources. Implementing MFA as part of access management controls ensures that only legitimate users with verified identities can access critical information, thereby bolstering overall cybersecurity measures within an organisation.
Streamlined user provisioning for timely access rights assignment
Streamlined user provisioning is a significant advantage of access management controls as it ensures the efficient and timely assignment of access rights to users within an organisation. By automating the user provisioning process, businesses can quickly grant appropriate permissions to employees based on their roles and responsibilities. This not only enhances operational efficiency but also reduces the risk of delays or errors in access assignment, ultimately improving overall productivity and security posture.
Simplified access management with Role-Based Access Control (RBAC)
Simplified access management with Role-Based Access Control (RBAC) is a significant advantage of implementing access management controls in organisations. RBAC allows for the assignment of permissions based on predefined roles, streamlining the process of granting and revoking access rights. By aligning access privileges with job responsibilities, RBAC reduces complexity in managing user permissions, minimises the risk of errors, and enhances overall security posture. This approach not only improves operational efficiency but also ensures that individuals have the appropriate level of access to perform their duties effectively while maintaining data integrity and confidentiality.
Enhanced auditing capabilities for tracking user activities
Enhanced auditing capabilities provided by access management controls empower organisations to meticulously track and monitor user activities within their IT systems. By maintaining detailed logs of who accessed what resources and when, businesses can gain valuable insights into user behaviour, detect anomalies or security breaches promptly, and ensure compliance with regulatory requirements. This level of visibility not only enhances security posture but also facilitates effective incident response and forensic investigations, ultimately bolstering the overall resilience of the organisation’s digital infrastructure.
Increased productivity by granting appropriate permissions efficiently
By granting appropriate permissions efficiently through access management controls, organisations can enhance productivity within their workforce. Employees are able to access the necessary resources and systems without unnecessary delays or obstacles, allowing them to focus on their tasks effectively. This streamlined approach to permission allocation ensures that individuals have the right level of access to carry out their responsibilities, leading to improved efficiency and workflow continuity across the organisation.
Heightened awareness of cybersecurity best practices among employees
One significant advantage of implementing access management controls is the heightened awareness of cybersecurity best practices among employees. By enforcing strict access protocols and providing necessary training on secure data handling, employees become more conscious of the importance of safeguarding sensitive information. This increased awareness not only enhances overall security within the organisation but also empowers employees to play an active role in maintaining a secure digital environment, thereby contributing to a culture of cybersecurity awareness and responsibility.
Complexity
One significant drawback of access management controls is the inherent complexity involved in their implementation. Establishing and maintaining effective access management systems can be a challenging task that demands a high level of expertise and attention to detail. Organisations may face hurdles in configuring intricate authentication mechanisms, defining granular permissions, and managing user access across diverse IT environments. The complexity of access management controls can lead to potential errors, delays in user provisioning, and increased administrative overhead, highlighting the need for dedicated resources and skilled professionals to navigate these challenges effectively.
Cost
One notable drawback of access management controls is the associated costs. Implementing effective access management solutions often requires a substantial financial investment in terms of licensing, implementation, and ongoing maintenance. The expenses involved in acquiring the necessary technology, setting up the infrastructure, and ensuring regular updates and support can pose challenges for organisations with limited budgets. This cost factor may deter some businesses from fully embracing comprehensive access management controls, potentially leaving them vulnerable to security risks and compliance issues. Balancing the benefits of enhanced security with the financial implications of access management control implementation is a crucial consideration for organisations striving to protect their digital assets while managing expenses effectively.
User Resistance
User resistance is a significant con of access management controls within organisations. Employees may push back against strict access restrictions that could potentially impede their workflow or productivity. This resistance can stem from inconvenience, perceived limitations on their job responsibilities, or simply a lack of understanding about the necessity of access controls for security purposes. Balancing the need for robust security measures with employees’ concerns and ensuring effective communication about the reasons behind access restrictions is crucial in overcoming this challenge and fostering a culture of compliance and security awareness among staff.
Single Point of Failure
Over-reliance on a centralised access control system can present a significant drawback in the form of a single point of failure. If the centralised system experiences a failure or is compromised, it can have far-reaching consequences, potentially leading to widespread disruptions in access management and security protocols. This vulnerability underscores the importance of implementing backup measures and redundancies to mitigate the risks associated with relying solely on a single access control system.
False Positives
Strict access controls, while essential for maintaining security, can sometimes lead to the generation of false positives, resulting in the blocking of legitimate user actions. This occurrence can cause frustration among users who are unnecessarily restricted from accessing resources they genuinely require. False positives in access management controls highlight the delicate balance organisations must strike between robust security measures and ensuring smooth operational efficiency. Finding ways to minimise false positives while still maintaining a high level of security is crucial for creating a positive user experience and maximising productivity within the workplace.
Overhead
One significant drawback of access management controls is the potential for increased overhead. When managing access permissions for a vast number of users and resources, organisations may face administrative challenges and complexities. This can lead to time-consuming tasks, such as setting up and maintaining access rights, which may strain IT resources and introduce inefficiencies in the access management process. Additionally, the complexity of managing a large volume of permissions increases the likelihood of errors or oversight, potentially compromising security and hindering overall system performance.
Security Gaps
Security Gaps: One significant con of access management controls is the potential for security vulnerabilities to arise from misconfigurations or weaknesses in access control settings. These gaps in security could be inadvertently created during the implementation or maintenance of access controls, providing opportunities for malicious actors to exploit and gain unauthorised access to sensitive data or systems. It is crucial for organisations to regularly review and update their access management controls to identify and address any security gaps promptly to prevent potential breaches and mitigate risks to their cybersecurity posture.