The Importance of Cyber Security Companies in Safeguarding Digital Assets
In today’s digital age, where businesses rely heavily on technology for their operations, the threat of cyber attacks looms large. Cyber criminals are constantly evolving their tactics to exploit vulnerabilities in networks and systems, making it imperative for organisations to invest in robust cyber security measures. This is where cyber security companies play a crucial role in safeguarding digital assets and protecting sensitive information from malicious actors.
Expertise and Specialisation
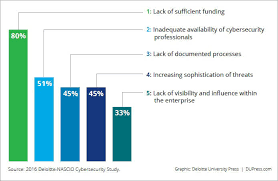
Cyber security companies bring a wealth of expertise and specialisation to the table. They employ skilled professionals who are well-versed in the latest cyber threats and security best practices. These experts conduct thorough assessments of an organisation’s IT infrastructure, identify potential vulnerabilities, and implement effective security measures to mitigate risks.
Advanced Technologies
Many cyber security companies leverage advanced technologies such as artificial intelligence, machine learning, and behavioural analytics to enhance their threat detection capabilities. These technologies enable them to detect anomalies and suspicious activities in real-time, allowing for swift response to potential threats before they escalate into full-blown attacks.
Proactive Monitoring and Incident Response
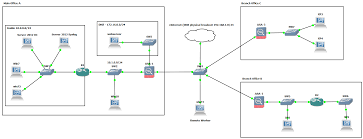
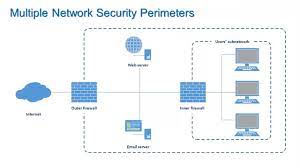
Cyber security companies provide round-the-clock monitoring of networks and systems to detect any unusual activity that may indicate a security breach. In the event of a cyber attack, these companies have dedicated incident response teams that are trained to contain the breach, investigate the root cause, and restore operations swiftly to minimise downtime and data loss.
Compliance and Regulations
With data protection regulations becoming increasingly stringent, cyber security companies help organisations ensure compliance with industry standards such as GDPR, HIPAA, PCI DSS, and others. By implementing robust security measures and conducting regular audits, these companies help businesses avoid costly fines resulting from non-compliance.
Partnership Approach
Cyber security companies often take a partnership approach with their clients, working collaboratively to understand their unique security needs and tailor solutions accordingly. By building strong relationships based on trust and transparency, these companies become trusted advisors that help organisations navigate the complex landscape of cyber threats.
In conclusion, cyber security companies play a vital role in protecting businesses from the ever-evolving landscape of cyber threats. By investing in the services of reputable cyber security firms, organisations can safeguard their digital assets, maintain customer trust, and ensure business continuity in an increasingly interconnected world.
Eight Essential Cyber Security Strategies for Businesses: Safeguarding Data and Managing Risks
- Invest in robust cybersecurity measures to protect sensitive data.
- Regularly update software and systems to prevent vulnerabilities.
- Implement strong password policies and use multi-factor authentication.
- Train employees on cybersecurity best practices and how to identify threats.
- Conduct regular security audits and risk assessments.
- Establish incident response plans to quickly address any security breaches.
- Consider outsourcing certain cybersecurity functions to experts if needed.
- Stay informed about the latest cyber threats and industry trends.
Invest in robust cybersecurity measures to protect sensitive data.
It is crucial for businesses to invest in robust cybersecurity measures to safeguard their sensitive data from cyber threats. Cyber security companies play a vital role in helping organisations identify vulnerabilities, implement strong security protocols, and proactively monitor for any suspicious activities. By prioritising cybersecurity investments, businesses can protect their valuable information assets, maintain customer trust, and mitigate the risks associated with potential data breaches.
Regularly update software and systems to prevent vulnerabilities.
Regularly updating software and systems is a fundamental tip in maintaining strong cyber security practices. By staying current with updates and patches, organisations can effectively address known vulnerabilities and reduce the risk of exploitation by cyber criminals. Outdated software is often targeted by malicious actors seeking to exploit weaknesses for their gain. Therefore, by prioritising regular updates, businesses can enhance their overall security posture and better protect their digital assets from potential threats.
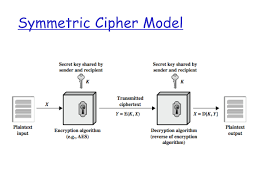
Implement strong password policies and use multi-factor authentication.
To enhance your organisation’s cyber security posture, it is crucial to implement strong password policies and utilise multi-factor authentication. Strong password policies involve creating complex passwords that are difficult for cyber criminals to guess, thus adding an extra layer of protection to your accounts and sensitive data. Additionally, multi-factor authentication adds an extra level of security by requiring users to provide multiple forms of verification before accessing their accounts, significantly reducing the risk of unauthorised access even if passwords are compromised. By incorporating these practices, cyber security companies can significantly bolster their defences against potential threats and safeguard their digital assets effectively.
Train employees on cybersecurity best practices and how to identify threats.
Training employees on cybersecurity best practices and how to identify threats is a fundamental aspect of maintaining a strong security posture within an organisation. By educating staff members on the importance of safe online behaviour, such as using complex passwords, being cautious of phishing emails, and keeping software up to date, companies can empower their workforce to act as the first line of defence against cyber attacks. Recognising potential threats and knowing how to respond appropriately not only helps prevent security breaches but also fosters a culture of vigilance and responsibility towards protecting sensitive information and digital assets.
Conduct regular security audits and risk assessments.
It is essential for businesses to prioritise cyber security by conducting regular security audits and risk assessments. By proactively evaluating the vulnerabilities in their IT infrastructure, organisations can identify potential weak points that could be exploited by cyber attackers. Regular audits help in assessing the effectiveness of existing security measures and implementing necessary improvements to enhance overall resilience. Through thorough risk assessments, businesses can stay ahead of emerging threats and ensure that their data and systems remain protected against evolving cyber risks.
Establish incident response plans to quickly address any security breaches.
Establishing incident response plans is a crucial step in enhancing the cyber security posture of organisations. By having well-defined protocols in place, cyber security companies can swiftly address any security breaches that may occur. These plans outline the actions to be taken in the event of a cyber attack, including containment measures, forensic investigations, and restoration of systems. A proactive approach to incident response not only minimises the impact of security incidents but also demonstrates readiness and resilience in the face of evolving threats.
Consider outsourcing certain cybersecurity functions to experts if needed.
When it comes to enhancing your organisation’s cyber security posture, it is essential to consider outsourcing certain cybersecurity functions to experts when needed. Cyber security companies bring a wealth of expertise, advanced technologies, and specialised skills to the table, allowing them to effectively manage and mitigate cyber risks. By entrusting specific security tasks to professionals in the field, businesses can benefit from proactive monitoring, incident response capabilities, compliance assistance, and a partnership approach that ensures their digital assets are well-protected against evolving threats. Outsourcing cybersecurity functions to experts not only enhances an organisation’s security posture but also allows internal teams to focus on core business activities while leveraging external expertise for comprehensive protection.
Stay informed about the latest cyber threats and industry trends.
It is crucial for individuals and organisations to stay informed about the latest cyber threats and industry trends in order to effectively protect their digital assets. By staying up-to-date with emerging cyber threats, such as ransomware attacks, phishing scams, and data breaches, they can proactively implement security measures to mitigate risks. Additionally, being aware of industry trends allows them to adapt their cyber security strategies accordingly and stay ahead of potential threats. Continuous education and awareness are key components in maintaining a strong defence against cyber attacks in today’s rapidly evolving digital landscape.