The Importance of Identity Management in Salesforce
Identity management plays a crucial role in the efficient and secure operation of any organisation’s IT infrastructure. When it comes to Salesforce, a leading customer relationship management (CRM) platform, effective identity management is essential for ensuring data security, user access control, and regulatory compliance.
Enhanced Security
By implementing robust identity management practices in Salesforce, businesses can significantly enhance their security posture. This includes features such as multi-factor authentication, single sign-on capabilities, and role-based access control. These measures help prevent unauthorised access to sensitive customer data and protect against potential security breaches.
Improved User Experience
Identity management in Salesforce also contributes to an improved user experience. With streamlined authentication processes and single sign-on functionality, users can access the platform seamlessly without the need to remember multiple login credentials. This not only saves time but also enhances productivity across sales teams and other departments using Salesforce.
Regulatory Compliance
In today’s regulatory landscape, compliance with data protection laws such as GDPR and CCPA is non-negotiable. Identity management solutions in Salesforce enable organisations to enforce data privacy regulations by controlling user access permissions, monitoring user activity, and maintaining audit trails. This ensures that sensitive customer information is handled in accordance with legal requirements.
Scalability and Flexibility
As businesses grow and evolve, their identity management needs may change. Salesforce offers scalable solutions that can adapt to the changing requirements of an organisation. Whether it’s integrating with third-party identity providers or customising user access controls based on specific roles, Salesforce provides the flexibility needed to accommodate diverse business environments.
Conclusion
In conclusion, identity management is a critical component of maintaining a secure and efficient Salesforce environment. By prioritising security measures, enhancing user experience, ensuring regulatory compliance, and leveraging scalable solutions, organisations can maximise the benefits of using Salesforce while safeguarding their data assets.
For businesses looking to optimise their Salesforce deployment, investing in robust identity management practices is key to unlocking the platform’s full potential while mitigating risks associated with data breaches and compliance violations.
Understanding Identity Management in Salesforce: Key Concepts and FAQs
- What is a identity user in Salesforce?
- What are the 4 pillars of IAM?
- What is identity management used for?
- What is an example of identity management?
- What is IAM in Salesforce?
- What’s the difference between IdP and IAM?
- What are the identity features of Salesforce?
What is a identity user in Salesforce?
In Salesforce, an identity user refers to a unique individual or entity within the system that has been granted access to the platform. These users are typically associated with a specific identity and are authenticated through login credentials such as usernames and passwords. Identity users play a crucial role in Salesforce as they interact with the CRM system, access data, and perform various actions based on their assigned permissions. By defining and managing identity users effectively, organisations can control access to sensitive information, track user activity, and maintain data security within their Salesforce environment.
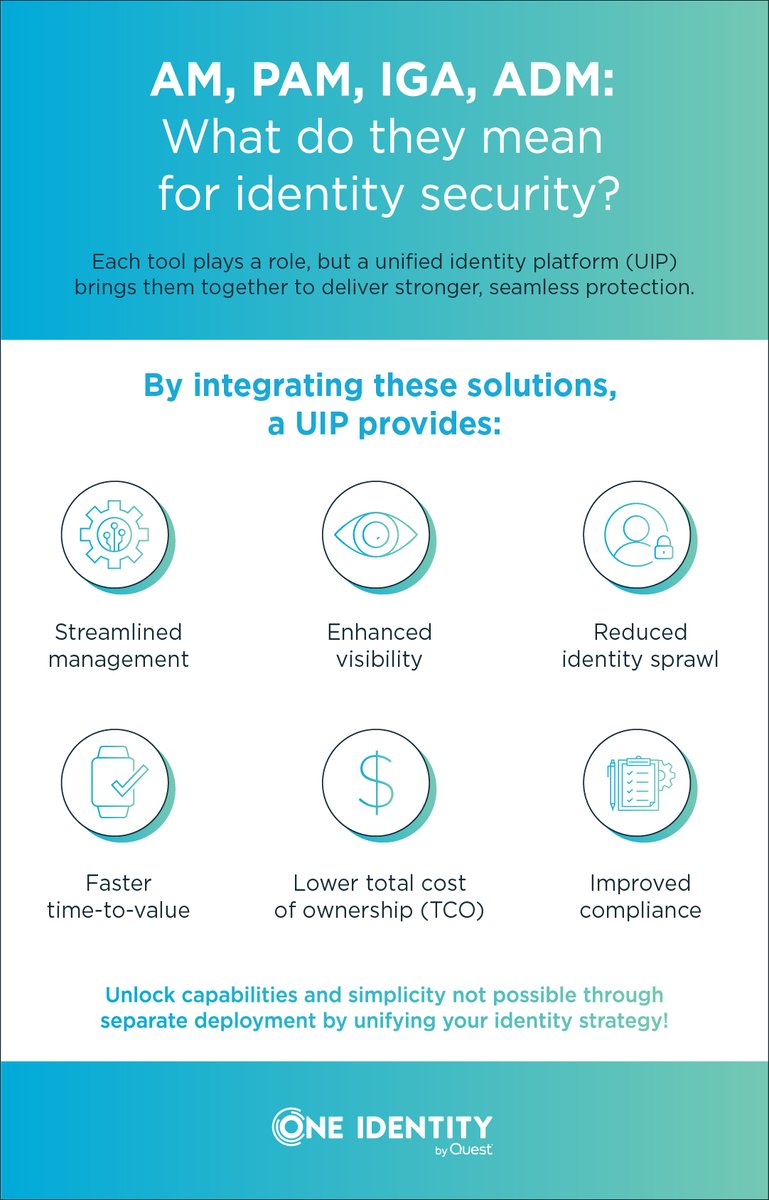
What are the 4 pillars of IAM?
Identity and Access Management (IAM) in Salesforce is built on four fundamental pillars that form the foundation of a secure and efficient identity management strategy. These pillars include authentication, authorisation, accountability, and assurance. Authentication ensures that users are who they claim to be through methods such as passwords, biometrics, or multi-factor authentication. Authorisation controls the access levels and permissions granted to users based on their roles and responsibilities within the organisation. Accountability involves tracking and monitoring user activities to maintain transparency and compliance with security policies. Finally, assurance focuses on verifying the integrity of identity data and ensuring that access controls are consistently enforced to protect sensitive information within Salesforce. These four pillars work together to establish a robust IAM framework that safeguards data integrity and enhances overall security measures in Salesforce environments.
What is identity management used for?
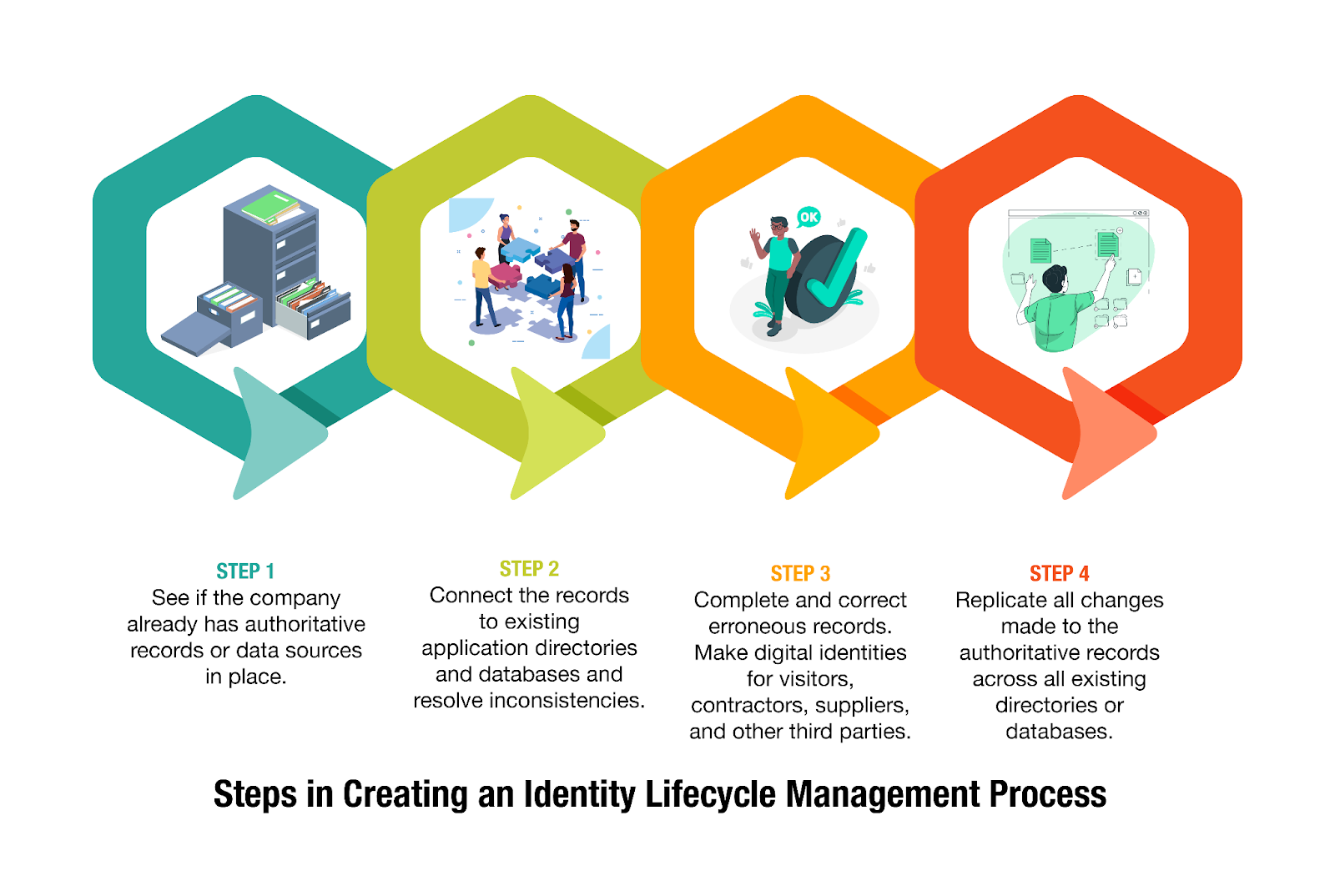
Identity management in Salesforce serves a crucial purpose in ensuring the security, efficiency, and compliance of an organisation’s operations. It is primarily used to control and manage user access to the Salesforce platform, allowing administrators to define and enforce authentication mechanisms, access privileges, and data permissions. By implementing robust identity management practices, businesses can safeguard sensitive information, prevent unauthorised access, streamline user authentication processes, and maintain regulatory compliance. Additionally, identity management in Salesforce enables organisations to enhance user experience by providing seamless access to the platform while maintaining a high level of security across all user interactions.
What is an example of identity management?
An example of identity management in Salesforce is the implementation of single sign-on (SSO) functionality. With SSO, users can access multiple applications, including Salesforce, using a single set of login credentials. This not only simplifies the authentication process for users but also enhances security by reducing the risk of password fatigue and potential vulnerabilities associated with managing multiple passwords. By integrating SSO with Salesforce, organisations can streamline user access control, improve user experience, and strengthen data security across their CRM platform and other integrated systems.
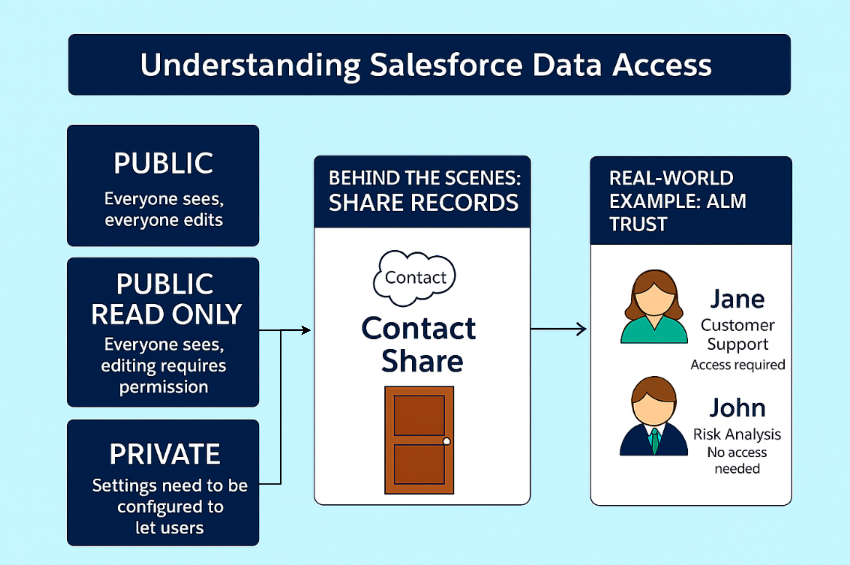
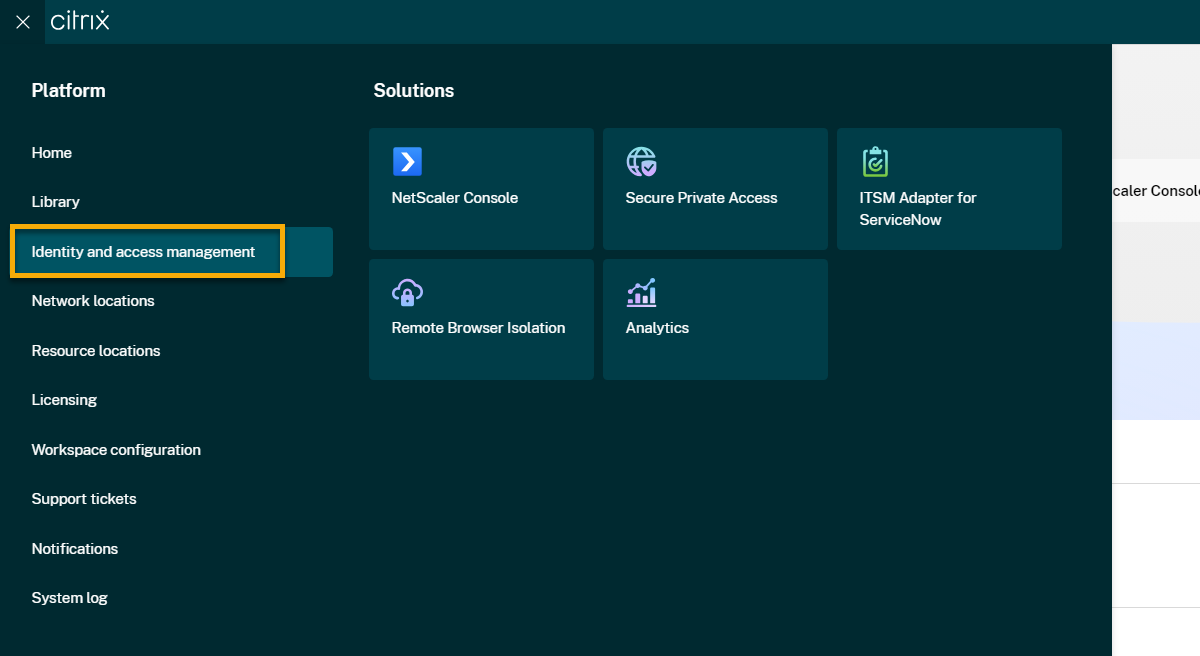
What is IAM in Salesforce?
IAM, or Identity and Access Management, is a fundamental aspect of Salesforce that focuses on controlling and managing user identities and their access to the platform. In Salesforce, IAM encompasses various security measures such as user authentication, authorisation, and user provisioning. By implementing IAM practices in Salesforce, organisations can ensure that only authorised users have access to specific data and functionalities within the CRM system. IAM in Salesforce plays a crucial role in enhancing security, improving user experience, and maintaining regulatory compliance by effectively managing user identities and access privileges.
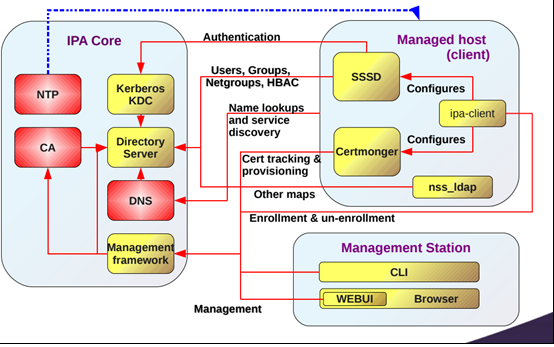
What’s the difference between IdP and IAM?
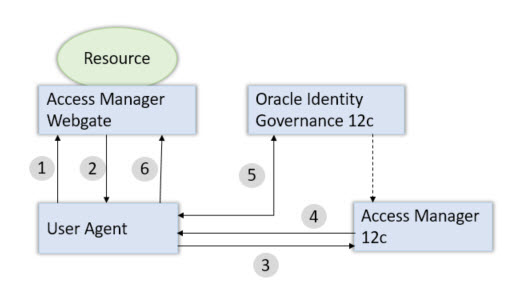
Understanding the distinction between IdP (Identity Provider) and IAM (Identity and Access Management) is essential in the realm of identity management within Salesforce. An Identity Provider, or IdP, is a service that authenticates users and issues security tokens for access to applications and resources. On the other hand, Identity and Access Management (IAM) encompasses a broader set of practices and technologies aimed at managing user identities, access permissions, and authentication processes across an organisation’s IT infrastructure. While an IdP focuses on user authentication specifically, IAM encompasses a more comprehensive approach to ensuring secure access control, compliance adherence, and seamless user experience within Salesforce and other systems. Clarifying the differences between IdP and IAM is crucial for organisations looking to implement effective identity management strategies that align with their security requirements and operational needs.
What are the identity features of Salesforce?
One of the frequently asked questions regarding identity management in Salesforce is about the platform’s identity features. Salesforce offers a range of robust identity management capabilities to enhance security and streamline user access control. These features include multi-factor authentication, single sign-on functionality, role-based access control, and integration with external identity providers. By leveraging these identity features, organisations can strengthen their data security measures, improve user experience, ensure regulatory compliance, and adapt to evolving business needs effectively within the Salesforce environment.