The Importance of IAM (Identity Access Management) Products in Today’s Digital Landscape
In the fast-paced world of cybersecurity, organisations are constantly facing threats to their sensitive data and critical systems. One of the key strategies for protecting digital assets is Identity Access Management (IAM). IAM products play a crucial role in ensuring that only authorised individuals have access to specific resources within an organisation’s IT infrastructure.
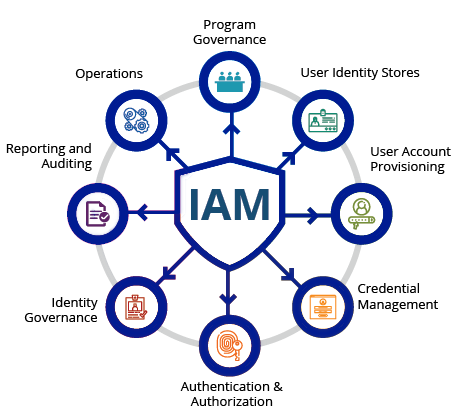
What are IAM Products?
IAM products are tools and solutions designed to manage and control user identities and their access rights within an organisation. These products help streamline the process of granting or revoking access privileges, enforcing security policies, and monitoring user activities across various systems and applications.
The Benefits of IAM Products
Implementing IAM products offers several benefits to organisations, including:
- Enhanced Security: By centralising identity management and access control, IAM products help prevent unauthorised access to sensitive data and resources.
- Improved Compliance: IAM solutions assist organisations in meeting regulatory requirements by enforcing access policies and providing audit trails of user activities.
- Efficiency: Automating user provisioning and deprovisioning processes reduces administrative overhead and ensures timely access management.
- User Experience: IAM products can enhance user experience by providing single sign-on capabilities, simplifying authentication across multiple systems.
Key Features of IAM Products
Modern IAM products offer a range of features to address the evolving needs of organisations in managing identities and access rights. Some key features include:
- Single Sign-On (SSO): Allows users to log in once to access multiple applications without re-entering credentials.
- Multi-Factor Authentication (MFA): Adds an extra layer of security by requiring users to provide multiple forms of verification before accessing resources.
- User Provisioning/Deprovisioning: Streamlines the process of onboarding new users and removing access for departing employees.
- Role-Based Access Control (RBAC): Assigns permissions based on predefined roles, simplifying access management.
The Future of IAM Products
As cyber threats continue to evolve, the role of IAM products will become even more critical in safeguarding organisational assets. Future developments in IAM technology may include enhanced biometric authentication methods, AI-driven analytics for threat detection, and seamless integration with cloud services.
In conclusion, IAM products are indispensable tools for organisations looking to strengthen their security posture, improve operational efficiency, and ensure regulatory compliance. By investing in robust IAM solutions, businesses can effectively manage identities and access rights in today’s digital landscape.
Top 5 Tips for Enhancing Security with IAM Identity Access Management Products
- Implement strong password policies to enhance security.
- Regularly review and update user permissions to ensure least privilege access.
- Enable multi-factor authentication for an extra layer of security.
- Monitor and audit user activities to detect any suspicious behaviour.
- Provide training to users on best practices for using IAM products.
Implement strong password policies to enhance security.
Implementing strong password policies is a fundamental aspect of enhancing security within IAM (Identity Access Management) products. By requiring users to create complex passwords that include a mix of alphanumeric characters and special symbols, organisations can significantly reduce the risk of unauthorised access to sensitive data and systems. Strong passwords act as a crucial line of defence against cyber threats such as brute force attacks and password guessing. Additionally, regular password changes and enforcing minimum length requirements further bolster the overall security posture of an organisation’s IAM infrastructure, ensuring that user identities remain protected from potential security breaches.
Regularly review and update user permissions to ensure least privilege access.
Regularly reviewing and updating user permissions is a crucial tip in Identity Access Management (IAM) products to enforce the principle of least privilege access. By regularly auditing and adjusting user permissions, organisations can ensure that individuals only have access to the resources necessary for their roles, reducing the risk of unauthorised activities or data breaches. This proactive approach not only enhances security but also helps maintain compliance with regulations by aligning access privileges with job responsibilities. Regular reviews of user permissions demonstrate a commitment to maintaining a robust IAM strategy that prioritises security and data protection.
Enable multi-factor authentication for an extra layer of security.
Enabling multi-factor authentication is a highly recommended tip when it comes to IAM (Identity Access Management) products. By implementing this additional security measure, organisations can significantly enhance their defence against unauthorised access. Multi-factor authentication requires users to provide multiple forms of verification before gaining access to sensitive resources, adding an extra layer of protection beyond traditional password-based security. This proactive approach helps mitigate the risk of identity theft, credential compromise, and other cyber threats, making it an essential feature for bolstering overall security posture in today’s digital landscape.
Monitor and audit user activities to detect any suspicious behaviour.
Monitoring and auditing user activities is a crucial tip when it comes to IAM (Identity Access Management) products. By actively tracking and reviewing user actions within an organisation’s IT infrastructure, suspicious behaviour can be quickly identified and addressed. This proactive approach not only enhances security but also helps in maintaining compliance with regulations by providing a detailed trail of user interactions. Regular monitoring and auditing of user activities serve as a powerful deterrent against potential security threats, ensuring the integrity of the system and protecting sensitive data from unauthorised access.
Provide training to users on best practices for using IAM products.
Providing training to users on best practices for using IAM products is essential for maximising the effectiveness of identity access management within an organisation. By educating users on how to securely navigate IAM systems, organisations can mitigate the risk of human error and enhance overall security posture. Training sessions can cover topics such as creating strong passwords, recognising phishing attempts, and understanding access control policies. Empowering users with the knowledge and skills to interact with IAM products responsibly not only protects sensitive data but also fosters a culture of cybersecurity awareness across the workforce.