The Benefits of Hosted Identity Management as a Service
In today’s digital age, businesses are increasingly relying on cloud-based solutions to streamline their operations and enhance security. One such service that has gained popularity is Hosted Identity Management as a Service (IDaaS). This innovative approach to identity management offers a range of benefits for organisations looking to improve their security posture and user experience.
Enhanced Security
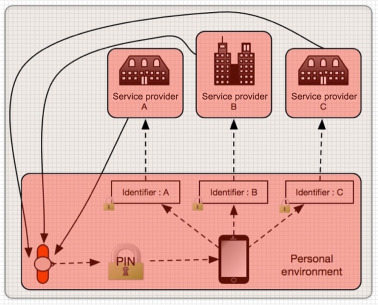
Hosted IDaaS provides robust security features that help protect sensitive data and prevent unauthorised access. By centralising identity management in the cloud, organisations can implement multi-factor authentication, role-based access controls, and automated provisioning/deprovisioning processes. This not only strengthens security but also ensures compliance with industry regulations.
Scalability and Flexibility
With Hosted IDaaS, businesses can easily scale their identity management capabilities based on their needs. Whether expanding operations or adding new users, the service offers flexibility to adapt to changing requirements without the need for significant infrastructure investments. This scalability allows organisations to focus on growth without worrying about resource constraints.
Improved User Experience
Hosted IDaaS simplifies user authentication and access management, leading to a seamless experience for employees and customers. Single sign-on capabilities reduce the need for multiple passwords, while self-service portals empower users to manage their own accounts efficiently. This improved user experience enhances productivity and satisfaction across the organisation.
Cost-Efficiency
By opting for Hosted IDaaS, businesses can benefit from cost savings associated with reduced maintenance and infrastructure expenses. The service eliminates the need for on-premises hardware and software maintenance, allowing organisations to allocate resources more effectively. Additionally, pay-as-you-go pricing models ensure that businesses only pay for the services they use.
Conclusion
Hosted Identity Management as a Service offers a comprehensive solution for organisations seeking enhanced security, scalability, user experience, and cost-efficiency. By leveraging cloud-based identity management services, businesses can stay ahead of evolving cyber threats while optimising their operations for success in the digital era.
Top 6 Tips for Choosing a Hosted Identity Management Service
- Consider the scalability of the hosted identity management service to ensure it can accommodate your growth.
- Evaluate the security measures in place, such as encryption protocols and access controls, to protect sensitive data.
- Look for a service provider that offers seamless integration with your existing systems and applications.
- Regularly review and update user access permissions to prevent unauthorized access to resources.
- Ensure the service provider complies with relevant regulations and standards to maintain data privacy and security.
- Provide adequate training for users on how to use the hosted identity management service effectively.
Consider the scalability of the hosted identity management service to ensure it can accommodate your growth.
When exploring hosted identity management as a service, it is crucial to consider the scalability of the solution to align with your business’s growth trajectory. Ensuring that the hosted identity management service can accommodate your expanding needs and user base is essential for seamless operations and cost-effective scalability. By choosing a service that can easily scale alongside your organisation, you can future-proof your identity management strategy and avoid potential disruptions as your business evolves.
Evaluate the security measures in place, such as encryption protocols and access controls, to protect sensitive data.
When considering Hosted Identity Management as a Service, it is crucial to evaluate the security measures implemented to safeguard sensitive data effectively. This includes assessing the encryption protocols and access controls put in place to prevent unauthorised access and data breaches. By ensuring robust security measures are in place, organisations can trust that their valuable information is protected against potential threats, maintaining confidentiality and integrity within their identity management system.
Look for a service provider that offers seamless integration with your existing systems and applications.
When considering Hosted Identity Management as a Service, it is crucial to seek a service provider that ensures seamless integration with your current systems and applications. By selecting a provider that offers compatibility with your existing infrastructure, you can streamline the implementation process and minimise disruptions to your operations. Seamless integration facilitates a smooth transition to the new identity management solution, enabling efficient collaboration between different platforms and enhancing overall system performance.
Regularly review and update user access permissions to prevent unauthorized access to resources.
Regularly reviewing and updating user access permissions is a crucial aspect of maintaining robust security in hosted identity management as a service. By conducting periodic audits of user access rights, organisations can identify and rectify any discrepancies or outdated permissions that may lead to unauthorised access to resources. This proactive approach not only helps prevent security breaches but also ensures that users have the appropriate level of access needed to perform their tasks efficiently. By staying vigilant and responsive to changes in user roles or responsibilities, businesses can mitigate risks and uphold the integrity of their digital assets effectively.
Ensure the service provider complies with relevant regulations and standards to maintain data privacy and security.
When opting for Hosted Identity Management as a Service, it is crucial to ensure that the chosen service provider adheres to pertinent regulations and standards to uphold data privacy and security. By confirming compliance with industry-specific guidelines and best practices, organisations can trust that their sensitive information is safeguarded against potential threats and breaches. Prioritising data protection measures within the framework of established regulations not only enhances security but also instils confidence in the reliability of the hosted identity management service, ultimately contributing to a robust and compliant operational environment.
Provide adequate training for users on how to use the hosted identity management service effectively.
To maximise the benefits of hosted identity management as a service, it is crucial to provide adequate training for users on how to utilise the platform effectively. By offering comprehensive training sessions, organisations can ensure that employees understand how to navigate the system, set up their accounts securely, and make the most of the available features. Proper training not only enhances user proficiency but also minimises the risk of errors and security breaches, ultimately contributing to a more secure and efficient identity management process.