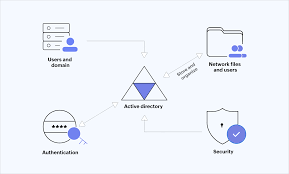
The Importance of Active Directory in Modern IT Environments
In the realm of IT infrastructure, Active Directory stands as a cornerstone for managing users, computers, and resources within a network. Developed by Microsoft, Active Directory serves as a centralised database that stores information about objects such as users, groups, and devices while providing authentication and authorisation services.
One of the key functions of Active Directory is to facilitate single sign-on for users, allowing them to access multiple resources across the network with a single set of credentials. This not only enhances user convenience but also streamlines security by reducing the need for multiple passwords and logins.
Active Directory plays a crucial role in enforcing security policies within an organisation. Administrators can define access controls based on user roles and group memberships, ensuring that sensitive data remains protected from unauthorised access. By implementing granular permissions and auditing capabilities, organisations can track user activities and maintain compliance with industry regulations.
Furthermore, Active Directory simplifies the management of network resources by enabling administrators to deploy software applications, configure devices, and distribute updates efficiently. Group policies allow for centralised control over settings and configurations across multiple machines, reducing manual intervention and ensuring consistency throughout the network.
In modern IT environments characterised by remote workforces and cloud-based services, Active Directory has evolved to support hybrid infrastructures through solutions like Azure Active Directory. This integration enables seamless access to cloud applications while maintaining synchronisation with on-premises directories.
As cyber threats continue to evolve in complexity, the security provided by Active Directory becomes increasingly critical. Implementing best practices such as regular audits, strong password policies, multi-factor authentication, and timely software updates are essential for safeguarding against potential vulnerabilities.
In conclusion, Active Directory remains an indispensable tool for organisations seeking efficient user management, robust security controls, and streamlined IT operations. By leveraging its capabilities effectively and staying abreast of emerging trends in directory services, businesses can ensure a secure and well-managed network environment that supports their growth and success.
9 Key Advantages of Implementing Active Directory: Centralisation, Security, and Compliance
- Centralised user management for easy access control
- Enhanced security through authentication and authorisation services
- Efficient single sign-on capability for users
- Granular permissions to control access to resources
- Streamlined software deployment and updates with group policies
- Support for hybrid cloud environments with Azure Active Directory integration
- Simplified network resource management for administrators
- Comprehensive auditing capabilities for tracking user activities
- Facilitates compliance with industry regulations
Six Drawbacks of Active Directory: Configuration Complexity, Single Point of Failure Risks, Cross-Platform Limitations, Cost Concerns, Security Vulnerabilities, and Cloud Integration Challenges
- Complexity of configuration and management, especially for large-scale deployments.
- Potential single point of failure if not adequately backed up or replicated.
- Limited support for non-Windows operating systems, which can create compatibility issues.
- Cost implications for licensing and maintenance may be prohibitive for smaller organisations.
- Vulnerability to security breaches if proper access controls and monitoring are not in place.
- Challenges in integrating with cloud services and modern IT architectures without additional tools or services.
Centralised user management for easy access control
Centralised user management in Active Directory offers a significant advantage by simplifying access control across an organisation’s network. By consolidating user accounts, permissions, and group memberships in a central database, administrators can efficiently manage and regulate user access to resources. This streamlined approach not only enhances security by enabling consistent enforcement of access policies but also improves operational efficiency by reducing the complexity of user administration tasks. With centralised user management in Active Directory, organisations can effectively control who has access to what within the network, ensuring a secure and well-organised IT environment.
Enhanced security through authentication and authorisation services
Active Directory offers enhanced security through its robust authentication and authorisation services. By centralising user authentication processes and defining access controls based on user roles and group memberships, Active Directory helps organisations enforce strict security policies. This ensures that only authorised users have access to sensitive data and resources, reducing the risk of unauthorised access or data breaches. With features such as multi-factor authentication and granular permissions, Active Directory provides a strong defence against cyber threats, enhancing the overall security posture of an organisation’s IT infrastructure.
Efficient single sign-on capability for users
Active Directory offers a highly efficient single sign-on capability for users, allowing them to access various network resources with a single set of credentials. This feature not only enhances user convenience by eliminating the need to remember multiple passwords but also boosts productivity by streamlining the authentication process. With Active Directory’s single sign-on functionality, users can seamlessly navigate through different applications and services within the network without encountering repetitive login prompts, ultimately improving user experience and operational efficiency across the organisation.
Granular permissions to control access to resources
Active Directory offers a significant advantage through its provision of granular permissions, allowing administrators to finely control access to resources within a network. This feature enables organisations to tailor access rights based on user roles and responsibilities, ensuring that sensitive data remains secure from unauthorised users. By defining specific permissions at a detailed level, Active Directory empowers administrators to restrict or grant access to files, applications, and other resources with precision, thereby enhancing data protection and compliance efforts within the IT environment.
Streamlined software deployment and updates with group policies
Active Directory offers a significant advantage in the streamlined deployment of software and updates through the use of group policies. By utilising group policies, administrators can centrally manage and distribute software applications and updates across multiple machines within the network. This not only reduces the time and effort required for manual installation but also ensures consistency in configurations and settings throughout the organisation. With the ability to define specific policies based on user roles or group memberships, Active Directory empowers administrators to efficiently deploy software resources while maintaining control over version management and compliance requirements.
Support for hybrid cloud environments with Azure Active Directory integration
The seamless integration of Active Directory with Azure Active Directory offers organisations the flexibility to embrace hybrid cloud environments effortlessly. By bridging on-premises infrastructure with cloud services, businesses can extend their directory services to the cloud while maintaining synchronisation and centralised control. This integration enables users to access a wide range of cloud applications securely, streamlining authentication processes and enhancing overall productivity. With Azure Active Directory integration, organisations can leverage the scalability and agility of the cloud without compromising on security or user management, ensuring a cohesive and efficient IT environment that meets the demands of modern digital landscapes.
Simplified network resource management for administrators
Active Directory simplifies network resource management for administrators by providing a centralised platform to efficiently deploy, configure, and monitor resources across the network. Through the use of group policies, administrators can enforce consistent settings and access controls for users and devices, reducing the complexity of managing individual machines. This streamlined approach not only saves time and effort but also ensures uniformity in configurations, enhancing security and operational efficiency within the IT environment.
Comprehensive auditing capabilities for tracking user activities
Active Directory offers comprehensive auditing capabilities that provide organisations with the ability to track and monitor user activities effectively. By logging events such as logins, file access, group membership changes, and administrative actions, administrators can gain valuable insights into user behaviour and system interactions. This feature not only enhances security by detecting suspicious activities and potential threats but also aids in compliance efforts by maintaining detailed records for regulatory purposes. With Active Directory’s robust auditing capabilities, organisations can proactively identify and address security issues while promoting accountability and transparency within their IT environment.
Facilitates compliance with industry regulations
Active Directory plays a crucial role in facilitating compliance with industry regulations by providing robust security controls and auditing capabilities. Organisations can define access permissions, track user activities, and enforce security policies to align with regulatory requirements seamlessly. By implementing granular controls and regular audits, businesses can ensure that data privacy standards are met, reducing the risk of non-compliance penalties. Active Directory’s ability to centralise user management and access controls simplifies the process of demonstrating adherence to industry regulations, ultimately enhancing data security and regulatory compliance within the organisation.
Complexity of configuration and management, especially for large-scale deployments.
The complexity of configuration and management, particularly in large-scale deployments, stands as a significant challenge when utilising Active Directory. As the size of the network grows, so do the intricacies involved in setting up and maintaining an effective directory structure. Managing user permissions, group policies, domain controllers, and replication across numerous locations can become a daunting task for IT administrators. The need for meticulous planning, continuous monitoring, and adherence to best practices is paramount to ensure the smooth operation of Active Directory in expansive environments.
Potential single point of failure if not adequately backed up or replicated.
One significant drawback of Active Directory is its potential to become a single point of failure if proper backup and replication measures are not in place. In the event of a system failure or data loss, organisations reliant on Active Directory may face disruptions in user authentication, access control, and resource management. Without adequate backups or replication strategies, the loss of Active Directory data could result in downtime, security vulnerabilities, and operational inefficiencies. It is crucial for businesses to implement robust backup solutions and replication mechanisms to mitigate the risks associated with this vulnerability and ensure continuity of IT services.
Limited support for non-Windows operating systems, which can create compatibility issues.
One significant drawback of Active Directory is its limited support for non-Windows operating systems, leading to potential compatibility issues within heterogeneous IT environments. While Active Directory excels in managing Windows-based systems seamlessly, the integration of non-Windows platforms such as Linux or macOS may present challenges. This limitation can hinder cross-platform collaboration, user authentication, and resource access, requiring additional configuration and third-party tools to bridge the gap effectively. Organisations operating diverse operating systems must carefully consider this con of Active Directory to ensure smooth interoperability across their entire infrastructure.
Cost implications for licensing and maintenance may be prohibitive for smaller organisations.
For smaller organisations, the cost implications associated with licensing and maintenance of Active Directory can pose a significant challenge. The financial burden of acquiring the necessary licenses and ensuring ongoing maintenance may be prohibitive, limiting the adoption of this robust directory service. Smaller businesses with constrained budgets may find it difficult to justify the expenditure required to implement and sustain an Active Directory infrastructure, potentially hindering their ability to leverage its benefits for streamlined user management and enhanced security controls. As a result, these organisations may need to explore alternative solutions or consider managed service options to address their directory service needs within budget constraints.
Vulnerability to security breaches if proper access controls and monitoring are not in place.
One significant con of Active Directory is its vulnerability to security breaches when proper access controls and monitoring measures are lacking. Without stringent security protocols in place, such as granular permissions, regular audits, and real-time monitoring of user activities, malicious actors may exploit weaknesses in the system to gain unauthorised access to sensitive data or resources. This can lead to potential data breaches, compromised user accounts, and other security incidents that pose a significant risk to the integrity and confidentiality of an organisation’s IT infrastructure. It is imperative for businesses to address these vulnerabilities proactively by implementing robust security practices and staying vigilant against evolving cyber threats.
One significant challenge of Active Directory lies in its integration with cloud services and modern IT architectures without the use of additional tools or services. As organisations increasingly adopt cloud-based solutions and hybrid infrastructures, the limitations of traditional Active Directory implementations become apparent. Issues such as compatibility, scalability, and security arise when attempting to extend Active Directory’s functionality to encompass cloud resources effectively. Without supplementary tools or services tailored for seamless integration, businesses may face complexities in managing user identities, enforcing access controls, and ensuring data protection across diverse IT environments. Addressing these challenges requires a strategic approach that combines innovative solutions with best practices to bridge the gap between on-premises systems and cloud platforms effectively.