The Importance of Cloud Security: Identity and Access Management
Cloud computing has revolutionised the way businesses operate, offering flexibility, scalability, and cost-efficiency. However, with this convenience comes the critical need for robust security measures to protect sensitive data stored in the cloud. One of the key aspects of cloud security is Identity and Access Management (IAM).
What is IAM?
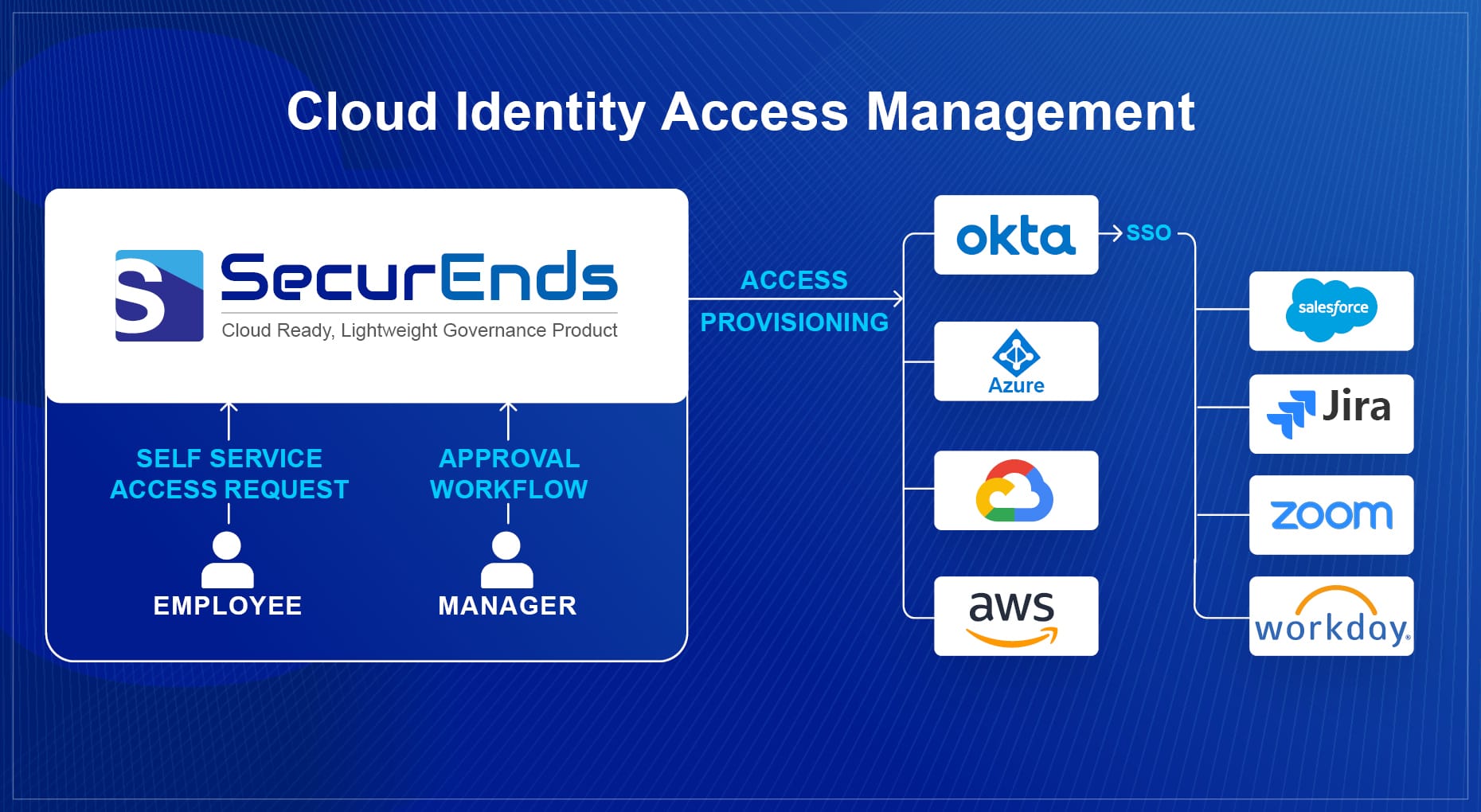
Identity and Access Management is a framework of policies and technologies that ensure the right individuals have access to the right resources at the right time. In a cloud environment, IAM plays a crucial role in controlling who can access data and applications, as well as what actions they can perform.
The Role of IAM in Cloud Security
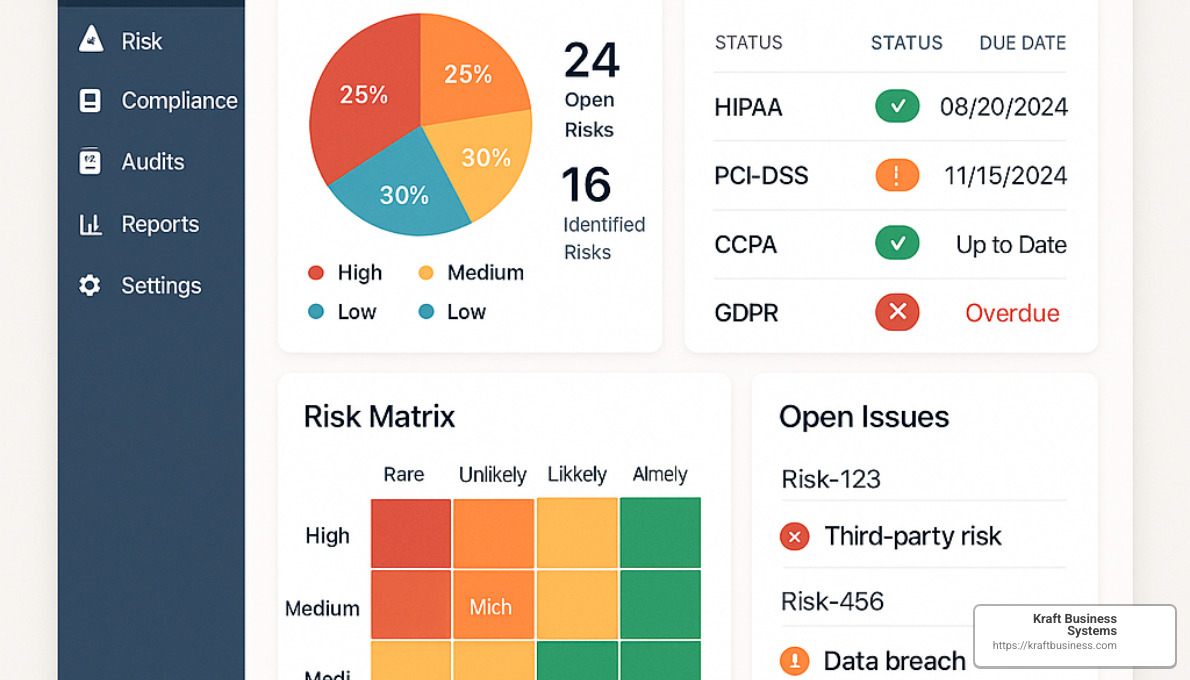
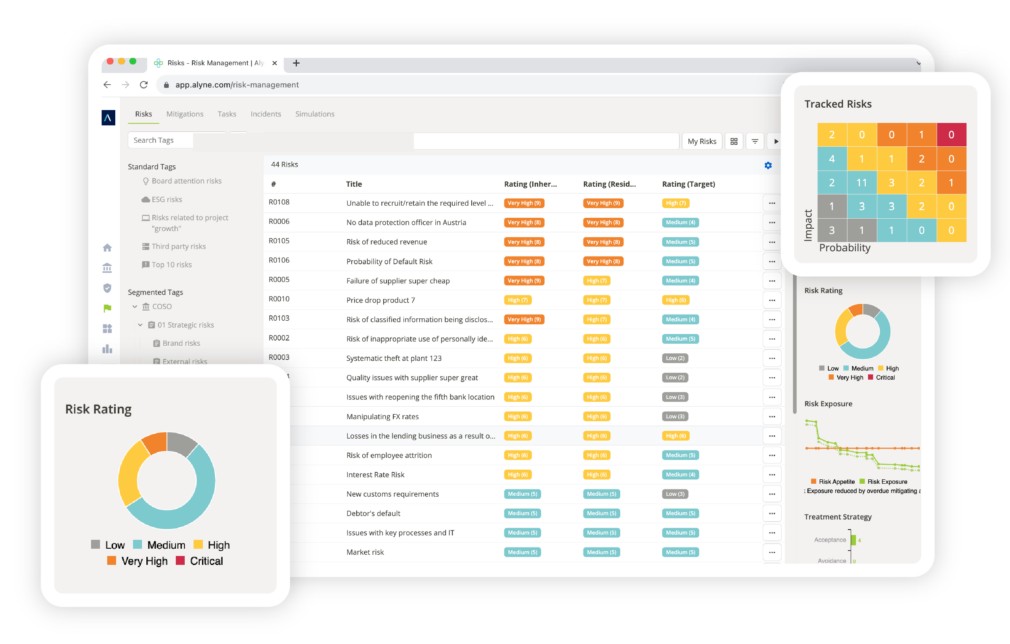
Effective IAM practices help organisations mitigate risks associated with unauthorised access, data breaches, and insider threats. By implementing strong authentication mechanisms, role-based access controls, and continuous monitoring, businesses can maintain a secure cloud environment.
Benefits of IAM in Cloud Security
- Enhanced Data Protection: IAM ensures that only authorised users can access sensitive information stored in the cloud.
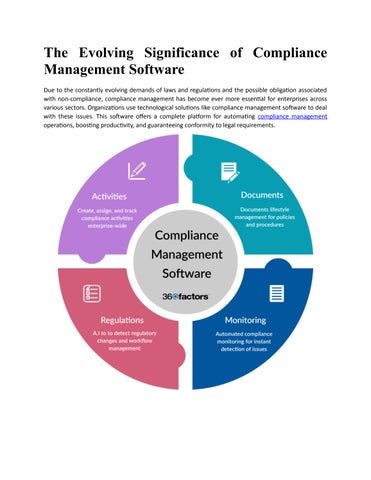
- Compliance Adherence: IAM helps organisations meet regulatory requirements by enforcing strict access controls and audit trails.
- Improved Operational Efficiency: By automating user provisioning and deprovisioning processes, IAM streamlines administrative tasks.
- Risk Mitigation: IAM reduces the likelihood of data breaches and insider threats by enforcing least privilege principles.
Best Practices for Implementing IAM in Cloud Environments
To enhance cloud security through IAM, organisations should consider adopting the following best practices:
- Multifactor Authentication: Require users to authenticate using multiple factors such as passwords, biometrics, or tokens.
- Role-Based Access Controls: Assign permissions based on job roles to limit access to critical resources.
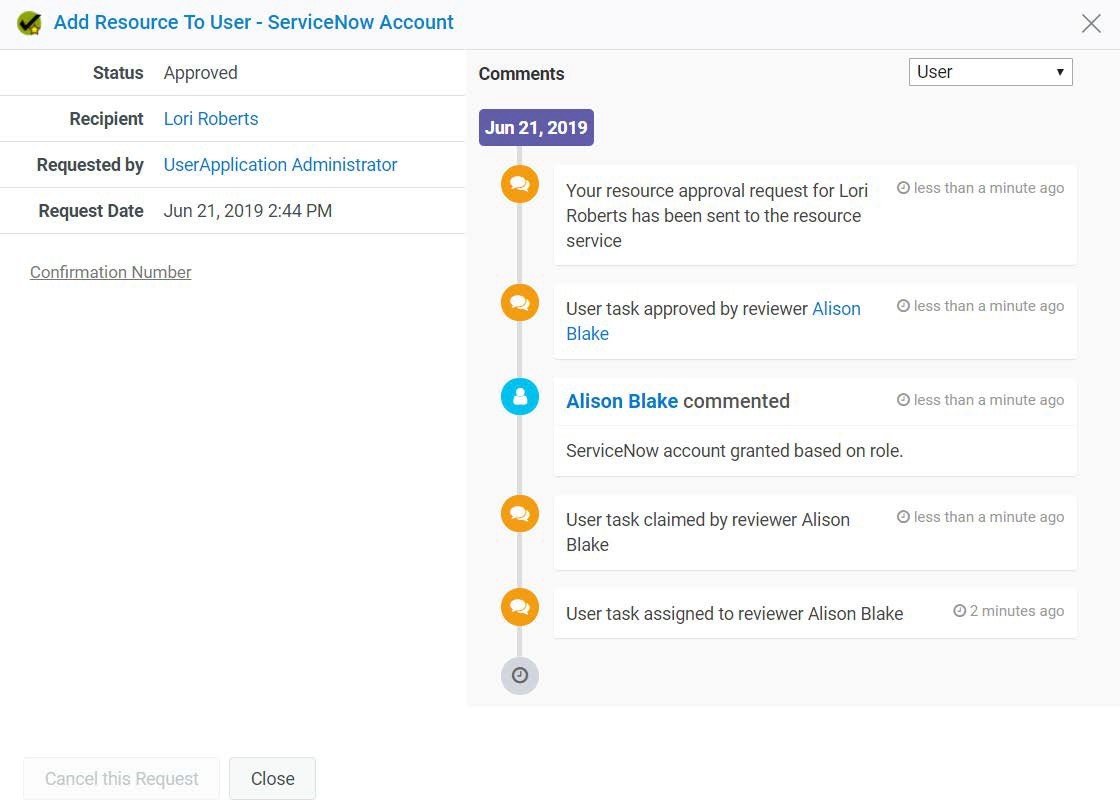
- Audit Logging: Monitor user activities and generate audit logs to track changes and detect suspicious behaviour.
- User Training: Educate employees on security best practices to prevent social engineering attacks and phishing scams.
In conclusion, Identity and Access Management is a fundamental component of cloud security that helps organisations safeguard their data assets from potential threats. By implementing robust IAM practices and staying vigilant against evolving cyber risks, businesses can confidently embrace the benefits of cloud computing while maintaining a secure digital environment.
Understanding Cloud Security: Key Aspects of Identity and Access Management
- What is identity and access management in cloud security?
- What are the 4 components of identity access management?
- What is consumer identity and access management in the cloud?
- What is the difference between IAM and cloud identity?
What is identity and access management in cloud security?
Identity and Access Management (IAM) in cloud security refers to the framework of policies and technologies implemented to control and manage user identities, permissions, and access to resources within a cloud environment. IAM ensures that only authorised individuals have the appropriate level of access to data, applications, and systems, while also enforcing security best practices such as authentication, authorisation, and auditing. By defining roles, setting access controls, and monitoring user activities, IAM plays a crucial role in enhancing data protection, regulatory compliance, and overall security posture in the cloud.
What are the 4 components of identity access management?
In the realm of cloud security identity and access management, understanding the four key components of IAM is essential for maintaining a secure digital environment. These components include: authentication, authorisation, user management, and auditing. Authentication verifies the identity of users accessing resources, while authorisation determines the level of access each user is granted. User management involves creating, updating, and deleting user accounts as well as assigning roles and permissions. Lastly, auditing tracks user activities and changes to ensure compliance and detect any potential security breaches. By comprehensively addressing these four components, organisations can establish a robust IAM framework to protect their sensitive data in the cloud.
What is consumer identity and access management in the cloud?
Consumer Identity and Access Management (CIAM) in the cloud refers to the set of processes and technologies that enable businesses to securely manage and authenticate their customers’ identities across various digital platforms and services. CIAM solutions allow organisations to provide a seamless and secure user experience by implementing features such as single sign-on, social login, self-registration, and consent management. By leveraging CIAM in the cloud, businesses can establish trust with their customers, enhance data privacy compliance, and deliver personalised services while maintaining a high level of security and user control over their identities.
What is the difference between IAM and cloud identity?
When discussing cloud security, a common question that arises is the distinction between IAM (Identity and Access Management) and cloud identity. While IAM focuses on managing user access to resources within an organisation’s IT infrastructure, cloud identity specifically pertains to managing identities in a cloud-based environment. IAM encompasses broader security policies and controls related to user authentication, authorisation, and permissions across various systems and applications, both on-premises and in the cloud. On the other hand, cloud identity is more narrowly focused on managing user identities within a specific cloud platform or service. Understanding this difference is crucial for implementing effective security measures tailored to the unique requirements of both IAM and cloud identity management in today’s digital landscape.