The Importance of Monitoring Active Directory
Active Directory (AD) is a critical component of many organisations’ IT infrastructures, serving as the central hub for managing users, computers, and resources. As the backbone of network security and access control, it is essential to monitor AD effectively to ensure the integrity and security of your systems.
Why Monitor Active Directory?
Monitoring AD provides real-time visibility into user activities, changes in configurations, and potential security threats. By monitoring AD, organisations can:
- Detect suspicious activities: Monitoring AD allows you to identify unusual user behaviours or unauthorised access attempts that could indicate a security breach.
- Track changes: Keeping track of changes made to AD objects, group policies, or permissions helps maintain system integrity and compliance with security policies.
- Ensure uptime: Monitoring AD can help detect performance issues or bottlenecks that may impact system availability and user productivity.
- Facilitate compliance: Many regulatory standards require organisations to monitor and audit their AD environment to ensure data protection and privacy compliance.
Best Practices for Monitoring Active Directory
To maximise the effectiveness of AD monitoring, consider implementing the following best practices:
- Implement real-time monitoring tools that provide alerts for suspicious activities or critical events in AD.
- Regularly review audit logs and reports to identify trends, anomalies, or potential security risks.
- Enforce least privilege access controls to limit user permissions and reduce the risk of unauthorised changes.
- Monitor privileged accounts closely as they have elevated access rights that could pose significant security risks if compromised.
- Establish a comprehensive incident response plan to address security incidents detected through AD monitoring promptly.
The Role of Automation in AD Monitoring
Automation plays a crucial role in streamlining AD monitoring processes by enabling proactive threat detection, rapid response to incidents, and efficient compliance management. Automated tools can help reduce manual efforts required for monitoring tasks while improving accuracy and consistency in detecting potential threats.
In Conclusion
Monitoring Active Directory is a fundamental aspect of maintaining a secure and resilient IT environment. By implementing robust monitoring practices and leveraging automated tools, organisations can enhance their ability to detect threats early, respond effectively to security incidents, and ensure compliance with regulatory requirements. Prioritising AD monitoring is key to safeguarding sensitive data, protecting against cyber threats, and maintaining the trust of stakeholders in an increasingly digital world.
Understanding Active Directory: FAQs on Monitoring and Management
- Why monitor Active Directory?
- How do I monitor ad changes?
- What is ad monitor?
- How do I monitor Active Directory services?
- What is Active Directory monitoring?
- How to display Active Directory?
- How to monitor AD health?
Why monitor Active Directory?
Monitoring Active Directory is crucial for maintaining the security and integrity of an organisation’s IT infrastructure. By monitoring Active Directory, businesses can proactively detect and respond to suspicious activities, unauthorised access attempts, and changes in configurations that could pose security risks. Monitoring AD also helps ensure compliance with regulatory standards, track user behaviours, and maintain system uptime by identifying performance issues early on. Overall, monitoring Active Directory is essential for safeguarding sensitive data, protecting against cyber threats, and upholding the overall security posture of an organisation.
How do I monitor ad changes?
Monitoring Active Directory (AD) changes is essential for maintaining the security and integrity of your IT environment. To effectively monitor AD changes, you can utilise specialised audit tools that track modifications to user accounts, group policies, permissions, and other AD objects in real-time. These tools provide detailed logs and reports that help you identify who made the changes, what changes were made, and when they occurred. By implementing robust AD change monitoring processes and leveraging automation where possible, you can proactively detect suspicious activities, ensure compliance with security policies, and respond promptly to any unauthorised alterations that could compromise the confidentiality and availability of your data.
What is ad monitor?
An AD monitor, short for Active Directory monitor, is a crucial tool used to oversee and track activities within an organisation’s Active Directory environment. It provides real-time visibility into user actions, system changes, and potential security threats within the AD infrastructure. By continuously monitoring AD, organisations can proactively detect suspicious behaviours, unauthorised access attempts, and configuration modifications that could compromise the integrity and security of their network. AD monitors play a vital role in ensuring compliance with security policies, identifying vulnerabilities, and maintaining the overall health of the Active Directory system.
How do I monitor Active Directory services?
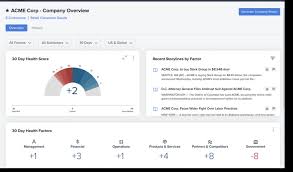
Monitoring Active Directory services is essential for maintaining the security and performance of your IT infrastructure. To effectively monitor Active Directory services, you can utilise specialised monitoring tools that provide real-time insights into the health and activity of your AD environment. These tools can track critical metrics such as domain controller performance, replication status, authentication requests, and changes to AD objects. By setting up alerts for potential issues and regularly reviewing monitoring reports, you can proactively identify and address any anomalies or security threats, ensuring the smooth operation of your Active Directory services.
What is Active Directory monitoring?
Active Directory monitoring involves the continuous surveillance and analysis of activities within an organisation’s Active Directory environment. It encompasses tracking user logins, permissions changes, group policy modifications, and other critical events to ensure the security, integrity, and compliance of the Active Directory infrastructure. By monitoring Active Directory, organisations can proactively identify suspicious behaviours, detect potential security threats, and maintain a robust defence against cyber attacks. Effective Active Directory monitoring is essential for safeguarding sensitive data, mitigating risks, and upholding operational efficiency within an organisation’s IT ecosystem.
How to display Active Directory?
Displaying Active Directory information can be achieved through various tools and methods, depending on the specific information you wish to view. One common way to display Active Directory data is by using Microsoft Management Console (MMC) snap-ins such as Active Directory Users and Computers or Active Directory Sites and Services. These tools provide a graphical interface for managing and viewing AD objects, users, groups, and other directory components. Additionally, PowerShell scripts can be utilised to query and display specific AD information programmatically for more advanced users who prefer command-line interfaces. Overall, displaying Active Directory effectively requires familiarity with the available tools and techniques tailored to your monitoring needs.
How to monitor AD health?
Monitoring the health of Active Directory (AD) is crucial for ensuring the stability and security of your IT environment. To monitor AD health effectively, organisations can implement various strategies, such as regular performance monitoring, event log analysis, and proactive alerting mechanisms. Monitoring tools specifically designed for AD health can provide insights into domain controller performance, replication status, database integrity, and overall system availability. By establishing comprehensive monitoring processes and leveraging appropriate tools, IT teams can detect issues early, address potential problems promptly, and maintain the optimal functioning of their AD infrastructure. Regularly reviewing AD health metrics and implementing proactive maintenance measures are essential steps in safeguarding the integrity and reliability of Active Directory within an organisation.