The Importance of Cloud Security in Network Infrastructure
In today’s digital age, cloud computing has revolutionised the way businesses operate by offering flexibility, scalability and cost-effectiveness. However, with the adoption of cloud services comes the crucial need for robust security measures to protect sensitive data and ensure uninterrupted operations.
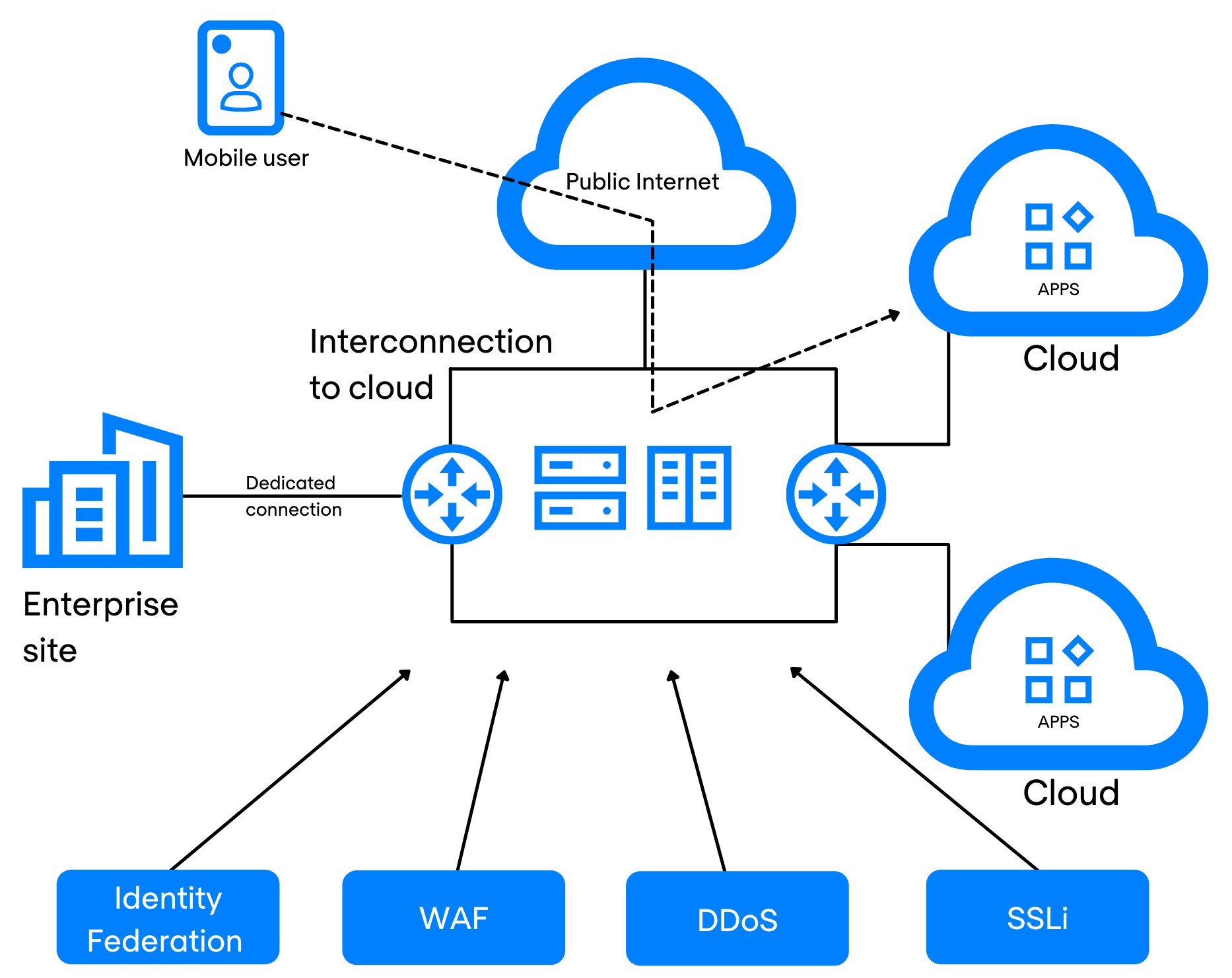
Cloud security in network infrastructure refers to the practices and technologies implemented to safeguard cloud-based resources, applications and data from cyber threats. As organisations increasingly rely on cloud services for storage, communication and collaboration, it is imperative to prioritise security to mitigate risks and maintain trust with customers.
Key Aspects of Cloud Security in Network Infrastructure:
- Data Encryption: Encrypting data both at rest and in transit is essential to prevent unauthorised access or interception.
- Access Control: Implementing strict access controls and authentication mechanisms ensures that only authorised users can access sensitive information.
- Network Monitoring: Continuous monitoring of network traffic helps detect anomalies or suspicious activities that may indicate a security breach.
- Vulnerability Management: Regularly scanning for vulnerabilities and applying patches promptly helps prevent exploitation by cyber attackers.
- Compliance: Adhering to industry regulations and standards ensures that data protection requirements are met, reducing legal risks.
By investing in cloud security solutions and best practices, businesses can enhance their resilience against cyber threats, minimise downtime due to security incidents, and build a reputation for trustworthiness among their clients. Collaboration between IT teams, security experts and cloud service providers is essential to create a comprehensive security strategy that addresses potential risks effectively.
In conclusion, cloud security plays a vital role in safeguarding network infrastructure in the era of digital transformation. Proactive measures such as encryption, access control and monitoring are essential components of a robust defence against evolving cyber threats. By prioritising cloud security, organisations can leverage the benefits of cloud computing while maintaining the integrity and confidentiality of their data.
Essential Cloud Security Network Tips: Protecting Your Data and Resources
- Encrypt data both in transit and at rest to ensure confidentiality.
- Implement strong access controls to restrict who can interact with your cloud resources.
- Regularly update and patch all software and systems to protect against vulnerabilities.
- Enable multi-factor authentication for an added layer of security when accessing cloud services.
- Monitor network traffic and user activity for any signs of suspicious behaviour or potential threats.
- Backup your data regularly to prevent data loss in case of a security breach or outage.
Encrypt data both in transit and at rest to ensure confidentiality.
To ensure the confidentiality of sensitive data in cloud network security, it is crucial to encrypt information both in transit and at rest. Encrypting data during transmission protects it from interception by malicious actors, while encrypting data at rest ensures that even if stored information is compromised, it remains unintelligible without the decryption key. By implementing robust encryption practices, organisations can significantly enhance the security of their cloud infrastructure and safeguard their valuable data from unauthorised access.
Implement strong access controls to restrict who can interact with your cloud resources.
Implementing strong access controls is a fundamental tip in ensuring robust cloud security network. By restricting access to only authorised individuals or entities, organisations can significantly reduce the risk of data breaches and unauthorised activities within their cloud resources. Strong access controls encompass mechanisms such as multi-factor authentication, role-based permissions, and regular access reviews to maintain a secure environment. By enforcing strict access policies, businesses can effectively manage user privileges and protect their valuable data from potential threats.
Regularly update and patch all software and systems to protect against vulnerabilities.
Regularly updating and patching all software and systems is a fundamental tip in cloud security network management. By staying current with software updates, organisations can effectively fortify their defences against potential vulnerabilities that cyber attackers may exploit. These updates often include critical security patches that address known weaknesses, ensuring that the network infrastructure remains resilient and secure. Proactive maintenance through updates is a proactive measure that significantly enhances the overall security posture of cloud-based systems, safeguarding sensitive data and maintaining operational continuity.
Enable multi-factor authentication for an added layer of security when accessing cloud services.
Enabling multi-factor authentication is a highly recommended practice to enhance security when accessing cloud services. By requiring users to provide multiple forms of verification, such as a password and a unique code sent to their mobile device, multi-factor authentication significantly reduces the risk of unauthorised access to sensitive data stored in the cloud. This additional layer of security adds an extra barrier for potential cyber threats, ensuring that only authorised users can authenticate and access cloud resources, thereby bolstering the overall security posture of the network infrastructure.
Monitor network traffic and user activity for any signs of suspicious behaviour or potential threats.
Monitoring network traffic and user activity is a fundamental tip in enhancing cloud security within a network infrastructure. By diligently observing and analysing network traffic patterns and user behaviours, organisations can swiftly detect any anomalies or signs of suspicious activity that may indicate potential threats. Proactive monitoring allows for timely response to security incidents, helping to prevent data breaches, unauthorised access, or other cyber threats. This vigilance is essential in maintaining the integrity and confidentiality of sensitive information stored in the cloud, ensuring a robust defence against evolving cybersecurity risks.
Backup your data regularly to prevent data loss in case of a security breach or outage.
Regularly backing up your data is a fundamental tip in ensuring cloud security network resilience. By maintaining up-to-date backups, businesses can mitigate the impact of potential security breaches or outages on their critical data. In the event of a cyber attack or system failure, having secure and accessible backups enables swift recovery and minimises data loss. Incorporating regular data backups as part of your cloud security strategy is a proactive measure that safeguards against unforeseen incidents, providing peace of mind and continuity for your operations.