The Importance of Access Management: Understanding the Magic Quadrant
Access management is a critical aspect of cybersecurity that involves controlling and monitoring user access to digital resources within an organisation. As technology continues to advance, the need for robust access management solutions becomes increasingly vital in safeguarding sensitive data and maintaining operational efficiency.
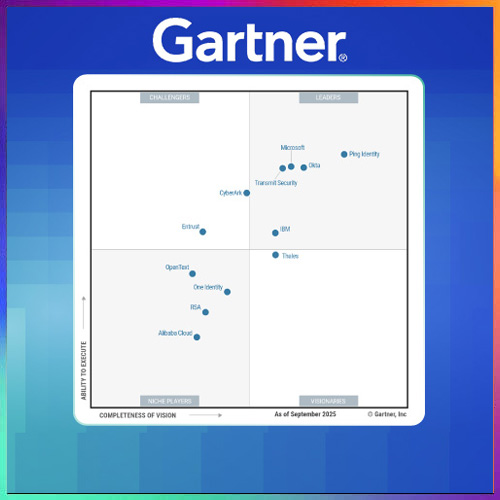
One useful tool for evaluating access management solutions is Gartner’s Magic Quadrant. The Magic Quadrant is a research methodology developed by Gartner, a leading technology research and advisory company, to assess various technology markets and provide insights into the competitive landscape of vendors within those markets.
Understanding the Magic Quadrant
The Magic Quadrant evaluates vendors based on two key criteria: their ability to execute and the completeness of their vision. Vendors are positioned on a quadrant graph with four categories: Leaders, Challengers, Visionaries, and Niche Players. This visual representation helps organisations understand each vendor’s strengths and weaknesses relative to their competitors.
Benefits of Using the Magic Quadrant for Access Management
For organisations seeking access management solutions, the Magic Quadrant offers several benefits:
- Market Insights: The Magic Quadrant provides a comprehensive overview of the access management market, including key trends, challenges, and emerging technologies.
- Vendor Evaluation: By analysing where vendors fall within the quadrants, organisations can assess which vendors align best with their specific requirements and strategic goals.
- Risk Mitigation: Choosing a vendor positioned as a Leader or Visionary in the Magic Quadrant can help mitigate risks associated with implementing subpar access management solutions.
- Evidence-Based Decision Making: The data-driven analysis presented in the Magic Quadrant enables informed decision-making when selecting an access management solution provider.
Looking Ahead
In today’s digital landscape, effective access management is crucial for protecting sensitive data, ensuring regulatory compliance, and enhancing overall security posture. By leveraging tools such as Gartner’s Magic Quadrant to evaluate access management solutions, organisations can make strategic decisions that align with their cybersecurity objectives and drive business success.
As technology continues to evolve rapidly, staying informed about market trends and vendor capabilities will be essential for maintaining a robust access management strategy that meets the dynamic needs of modern enterprises.
Contact us today to learn more about how our cutting-edge access management solutions can help secure your organisation’s digital assets and streamline user access processes.
Key Advantages of the Access Management Magic Quadrant for Strategic Decision-Making
- Provides a comprehensive overview of the access management market.
- Enables organisations to assess vendor strengths and weaknesses effectively.
- Helps in identifying vendors that align with specific requirements and strategic goals.
- Mitigates risks by choosing vendors positioned as Leaders or Visionaries.
- Supports evidence-based decision-making when selecting access management solutions.
- Offers insights into key trends, challenges, and emerging technologies in the market.
- Facilitates informed decision-making for enhancing security posture and compliance measures.
- Assists in staying abreast of market dynamics to maintain a robust access management strategy.
Critical Drawbacks of Access Management Magic Quadrant: A Comprehensive Overview
- Limited Scope
- Subjectivity
- Static Assessment
- Vendor Bias
- Costly Investment
- Complexity
- Dependency on Analysts
Provides a comprehensive overview of the access management market.
One key advantage of the Access Management Magic Quadrant is its ability to provide a comprehensive overview of the access management market. By evaluating and positioning various vendors within the quadrant based on their execution capabilities and vision, organisations gain valuable insights into the competitive landscape of access management solutions. This comprehensive view allows businesses to understand key market trends, emerging technologies, and the strengths of different vendors, empowering them to make informed decisions when selecting an access management solution that best aligns with their specific requirements and strategic objectives.
Enables organisations to assess vendor strengths and weaknesses effectively.
By utilising the Access Management Magic Quadrant, organisations can effectively evaluate vendor strengths and weaknesses in the access management market. This assessment allows businesses to make informed decisions based on a comprehensive understanding of each vendor’s capabilities and strategic direction. By identifying key strengths and potential areas for improvement, organisations can select vendors that best align with their specific requirements, ultimately enhancing their access management strategies and cybersecurity posture.
Helps in identifying vendors that align with specific requirements and strategic goals.
One key advantage of utilising the Access Management Magic Quadrant is its ability to assist organisations in identifying vendors that closely align with their specific requirements and strategic goals. By evaluating vendors based on their vision and execution capabilities, businesses can pinpoint solutions providers whose offerings best match their unique needs. This targeted approach not only streamlines the vendor selection process but also ensures that organisations partner with providers who can support their long-term objectives effectively.
Mitigates risks by choosing vendors positioned as Leaders or Visionaries.
Mitigating risks is a crucial benefit of leveraging the Access Management Magic Quadrant, as it allows organisations to make informed decisions when selecting vendors positioned as Leaders or Visionaries. By choosing vendors in these categories, organisations can significantly reduce the risks associated with implementing subpar access management solutions. Leaders and Visionaries are recognised for their innovation, market presence, and ability to execute their vision effectively. This strategic approach not only enhances security measures but also instils confidence in the reliability and effectiveness of the chosen access management solution, ensuring a robust defence against potential threats and vulnerabilities within the digital ecosystem.
Supports evidence-based decision-making when selecting access management solutions.
The access management Magic Quadrant offers a valuable advantage by supporting evidence-based decision-making when selecting access management solutions. By providing a structured evaluation of vendors based on their ability to execute and the completeness of their vision, organisations can make informed choices backed by data and analysis. This evidence-based approach enables businesses to assess vendors objectively, aligning their specific requirements with the capabilities and strategic direction of potential solution providers. Ultimately, leveraging the insights from the Magic Quadrant empowers organisations to choose access management solutions that best fit their needs and contribute to enhancing overall cybersecurity posture.
Offers insights into key trends, challenges, and emerging technologies in the market.
The Access Management Magic Quadrant offers valuable insights into key trends, challenges, and emerging technologies within the market. By analysing the positioning of vendors on the quadrant graph, organisations can gain a deeper understanding of the current landscape of access management solutions. This information enables businesses to stay informed about industry trends, anticipate potential challenges, and identify innovative technologies that can enhance their security posture. Armed with this knowledge, organisations can make strategic decisions that align with their long-term goals and ensure they are equipped to address evolving cybersecurity threats effectively.
Facilitates informed decision-making for enhancing security posture and compliance measures.
The Access Management Magic Quadrant serves as a valuable tool in facilitating informed decision-making for organisations looking to enhance their security posture and compliance measures. By analysing vendors’ positions within the quadrant based on their ability to execute and the completeness of their vision, businesses can make strategic choices that align with their specific security requirements. This enables organisations to select access management solutions that not only bolster their overall security defences but also ensure adherence to regulatory standards, ultimately strengthening their cybersecurity framework and safeguarding sensitive data effectively.
Assists in staying abreast of market dynamics to maintain a robust access management strategy.
By utilising the Access Management Magic Quadrant, organisations can effectively stay abreast of market dynamics, enabling them to adapt and evolve their access management strategies in response to changing cybersecurity landscapes. This proactive approach ensures that businesses can maintain a robust access management strategy that aligns with current industry trends, emerging technologies, and evolving threats. By leveraging the insights provided by the Magic Quadrant, organisations can make informed decisions that enhance their overall security posture and enable them to effectively mitigate risks associated with unauthorised access and data breaches.
Limited Scope
One notable drawback of relying on the Access Management Magic Quadrant is its limited scope. While the Magic Quadrant provides valuable insights into key vendors in the access management market, it may not encompass all access management solutions available. This limitation could result in overlooking niche or emerging vendors that offer innovative approaches to access management. Organisations seeking specialised or cutting-edge solutions may need to conduct additional research beyond the Magic Quadrant to ensure they consider all relevant options and find the best fit for their unique requirements and objectives.
Subjectivity
Subjectivity is a notable con of relying on the Access Management Magic Quadrant for vendor evaluation. The evaluation criteria employed in the Magic Quadrant are formulated by Gartner’s analysis, which may not always perfectly align with the unique requirements and priorities of every organisation. This subjectivity can lead to discrepancies between what Gartner deems as important factors and what a particular organisation considers crucial in their access management solution selection process. As a result, organisations should exercise caution and supplement their decision-making process with additional research and tailored assessments to ensure that the chosen vendor truly meets their individual needs and objectives.
Static Assessment
One notable downside of relying on the Access Management Magic Quadrant is the static nature of vendor positioning within it. The snapshot provided by the Magic Quadrant represents a specific point in time and may not capture real-time developments or improvements made by vendors. This limitation can potentially lead to discrepancies between a vendor’s position in the quadrant and their current performance or offerings. Organisations should be aware that the Magic Quadrant assessment is not a dynamic, continuously updated evaluation, and they may need to conduct additional research to ensure they have the most up-to-date information when selecting an access management solution provider.
Vendor Bias
One notable drawback of relying solely on the Access Management Magic Quadrant is the presence of vendor bias. Vendors positioned as Leaders or Visionaries often attract more attention, potentially overshadowing innovative solutions offered by Challengers or Niche Players. This bias may lead organisations to overlook emerging technologies and unique approaches to access management that could better suit their specific needs. It is essential for decision-makers to critically evaluate all vendors across the quadrants to ensure they consider a diverse range of solutions and make informed choices based on their individual requirements and objectives.
Costly Investment
One significant drawback of relying solely on the Magic Quadrant for vendor selection in access management is the potential for organisations to overlook cost-effective solutions that align with their specific requirements. While the Magic Quadrant provides valuable insights into vendor capabilities and market positioning, focusing solely on vendors positioned as Leaders or Visionaries may lead to a bias towards higher-priced solutions. Organisations must consider their budget constraints and evaluate a broader range of vendors to ensure they find a solution that not only meets their access management needs but also offers the best value for their investment. By balancing the insights from the Magic Quadrant with a thorough cost-benefit analysis, organisations can make informed decisions that optimise both security effectiveness and financial resources.
Complexity
Navigating the complexity of Gartner’s Magic Quadrant for access management can pose a significant challenge for non-technical stakeholders. Understanding the intricacies of how vendors are assessed and positioned within the quadrant requires a certain level of technical expertise that may not be easily grasped by individuals outside the IT realm. The terminology, criteria, and evaluation process involved in the Magic Quadrant can be daunting, making it difficult for non-technical stakeholders to interpret and utilise the information effectively in decision-making processes. Clear communication and guidance are essential to bridge this gap and ensure that all stakeholders, regardless of their technical background, can make informed choices when evaluating access management solutions based on the Magic Quadrant analysis.
Dependency on Analysts
One significant drawback of relying on Gartner’s Magic Quadrant for access management evaluations is the potential dependency it creates on analysts’ assessments. Organisations may inadvertently limit their exploration of alternative access management options by placing excessive trust in Gartner’s rankings. This over-reliance can result in a narrow focus on vendors positioned favourably in the Magic Quadrant, potentially overlooking innovative solutions or niche players that could better align with specific business requirements. It is essential for organisations to use the Magic Quadrant as a valuable reference point rather than a definitive guide, allowing room for independent research and evaluation to ensure the selection of an access management solution that best suits their unique needs and objectives.