The Importance of Access Management Lifecycle in IT Security
In today’s digital age, where data breaches and cyber threats are prevalent, implementing a robust access management lifecycle is crucial for maintaining the security of an organisation’s sensitive information. The access management lifecycle encompasses the processes involved in managing user access rights to systems, applications, and data throughout their entire lifecycle within an organisation.
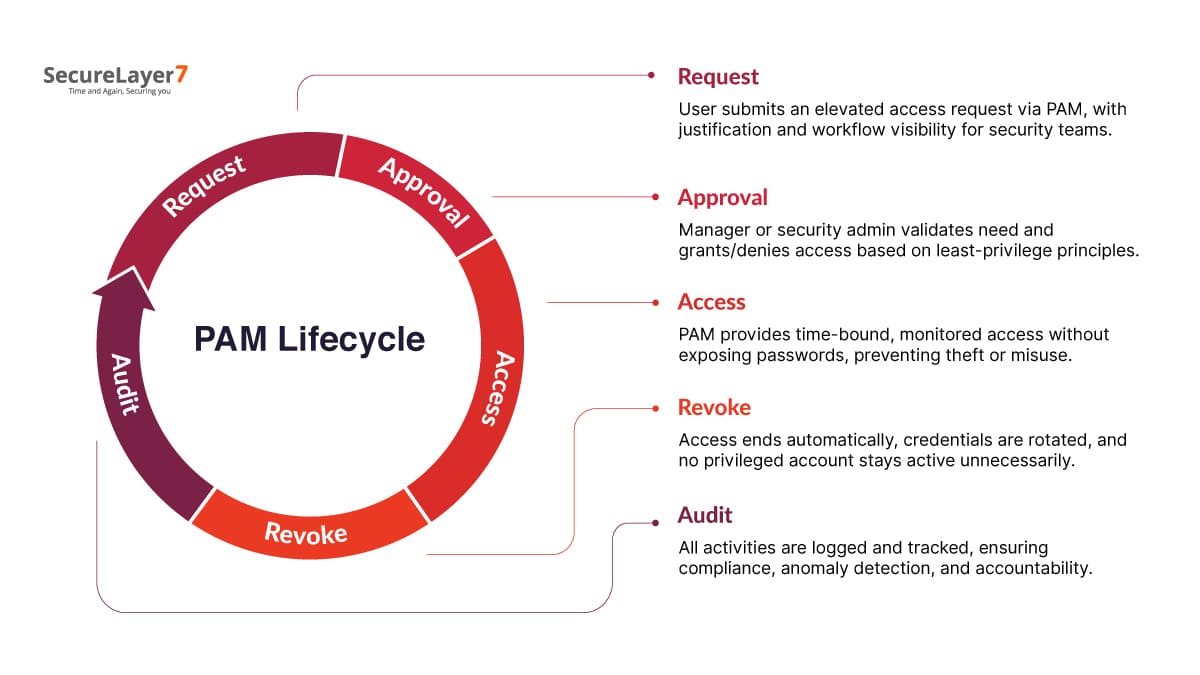
Phases of Access Management Lifecycle:
- Access Request: The lifecycle begins with users requesting access to specific resources based on their roles and responsibilities within the organisation.
- Access Approval: Once a request is made, it goes through an approval process where designated authorities review and approve or deny the access based on security policies and requirements.
- Provisioning: Upon approval, the necessary access rights are provisioned to the user, allowing them to utilise the requested resources effectively.
- Monitoring: Continuous monitoring of user activities and access rights is essential to detect any anomalies or unauthorised actions that may pose a security risk.
- Review and Recertification: Regular reviews and recertifications of user access rights ensure that permissions are up-to-date and aligned with current job roles. This phase helps in mitigating risks associated with dormant or excessive privileges.
- Revocation: When users change roles or leave the organisation, their access rights need to be promptly revoked to prevent unauthorised access to confidential information.
The Benefits of Implementing Access Management Lifecycle:
- Enhanced Security: By following a structured approach to managing user access throughout its lifecycle, organisations can significantly reduce the risk of data breaches and insider threats.
- Regulatory Compliance: Many regulatory frameworks require organisations to implement proper access controls and regularly review user permissions. Adhering to these regulations helps in avoiding penalties and maintaining compliance.
- Operational Efficiency: Automating access management processes streamlines operations, reduces manual errors, and improves overall efficiency within IT departments.
- Audit Trail: Maintaining detailed records of user access requests, approvals, provisioning, reviews, and revocations creates a comprehensive audit trail that can be invaluable during security audits or investigations.
In conclusion, a well-defined access management lifecycle is fundamental for safeguarding sensitive data assets, ensuring regulatory compliance, enhancing operational efficiency, and maintaining a robust security posture in today’s digital landscape. Organisations that prioritise implementing and continuously improving their access management processes are better equipped to mitigate security risks effectively.
Understanding the Access Management Lifecycle: Key Stages and Processes Explained
- What are the 5 stages of the data life cycle?
- What is the user access management lifecycle?
- What is the access lifecycle process?
- What is the user management lifecycle?
- What is access lifecycle management?
- What is access management lifecycle?
What are the 5 stages of the data life cycle?
The five stages of the data lifecycle encompass the processes involved in managing data from its creation to its eventual disposal. The stages typically include data creation, where information is generated or collected; data storage, where it is saved and organised for easy access; data processing, involving analysis and manipulation for various purposes; data sharing, enabling collaboration and dissemination within and outside the organisation; and finally, data archiving or deletion, ensuring compliance with retention policies and regulations. Each stage plays a crucial role in maintaining the integrity, security, and usability of data throughout its lifecycle.
What is the user access management lifecycle?
The user access management lifecycle refers to the systematic process of managing and controlling user access rights to various systems, applications, and data within an organisation throughout their entire lifecycle. It encompasses stages such as access request, approval, provisioning, monitoring, review and recertification, and revocation. By following this structured approach, organisations can ensure that users have the appropriate level of access based on their roles and responsibilities while also proactively addressing security risks associated with unauthorised access or dormant privileges. The user access management lifecycle plays a critical role in enhancing security, maintaining regulatory compliance, improving operational efficiency, and establishing a comprehensive audit trail for accountability and transparency.
What is the access lifecycle process?
The access lifecycle process refers to the series of stages involved in managing user access rights to systems, applications, and data within an organisation. It begins with users requesting access based on their roles and responsibilities, followed by an approval process where designated authorities review and grant access according to security policies. Once approved, access rights are provisioned to users, who are then monitored for any unusual activities. Regular reviews and recertifications ensure that access permissions remain appropriate, while prompt revocation of access is carried out when users change roles or leave the organisation. This structured approach helps organisations maintain security, compliance, and operational efficiency throughout the entire lifecycle of user access.
What is the user management lifecycle?
The user management lifecycle refers to the end-to-end process of managing user accounts and access rights within an organisation. It encompasses various stages, including user onboarding, where new users are granted access to necessary resources; access provisioning, which involves assigning appropriate permissions based on roles and responsibilities; ongoing monitoring to detect any unauthorised activities; periodic reviews and recertifications to ensure access remains appropriate; and offboarding, where access is revoked when users change roles or leave the organisation. By following a structured user management lifecycle, organisations can effectively control access to sensitive information, maintain compliance with regulations, and enhance overall security posture.
What is access lifecycle management?
Access lifecycle management, also known as access management lifecycle, refers to the systematic process of managing user access rights to IT resources throughout their entire lifecycle within an organisation. This comprehensive approach involves stages such as access request, approval, provisioning, monitoring, review and recertification, and revocation. By following this structured methodology, organisations can effectively control user permissions, reduce security risks, ensure compliance with regulations, enhance operational efficiency, and maintain a detailed audit trail of access-related activities. Access lifecycle management plays a vital role in safeguarding sensitive data assets and mitigating potential security threats in today’s digital environment.
What is access management lifecycle?
The access management lifecycle refers to the systematic process of managing user access rights to IT resources throughout their entire lifecycle within an organisation. It encompasses various phases, including access request, approval, provisioning, monitoring, review and recertification, and revocation. By following this structured approach, organisations can effectively control and monitor user access, reduce security risks, ensure regulatory compliance, enhance operational efficiency, and maintain a comprehensive audit trail of access-related activities. The access management lifecycle plays a critical role in safeguarding sensitive information assets and maintaining a robust security posture in today’s digital environment.