The Importance of IAM and SSO in Modern Cybersecurity
In today’s interconnected digital world, Identity and Access Management (IAM) and Single Sign-On (SSO) have become essential components of robust cybersecurity strategies for organisations of all sizes. These technologies play a crucial role in safeguarding sensitive data, protecting against cyber threats, and ensuring seamless user experiences.
Identity and Access Management (IAM)
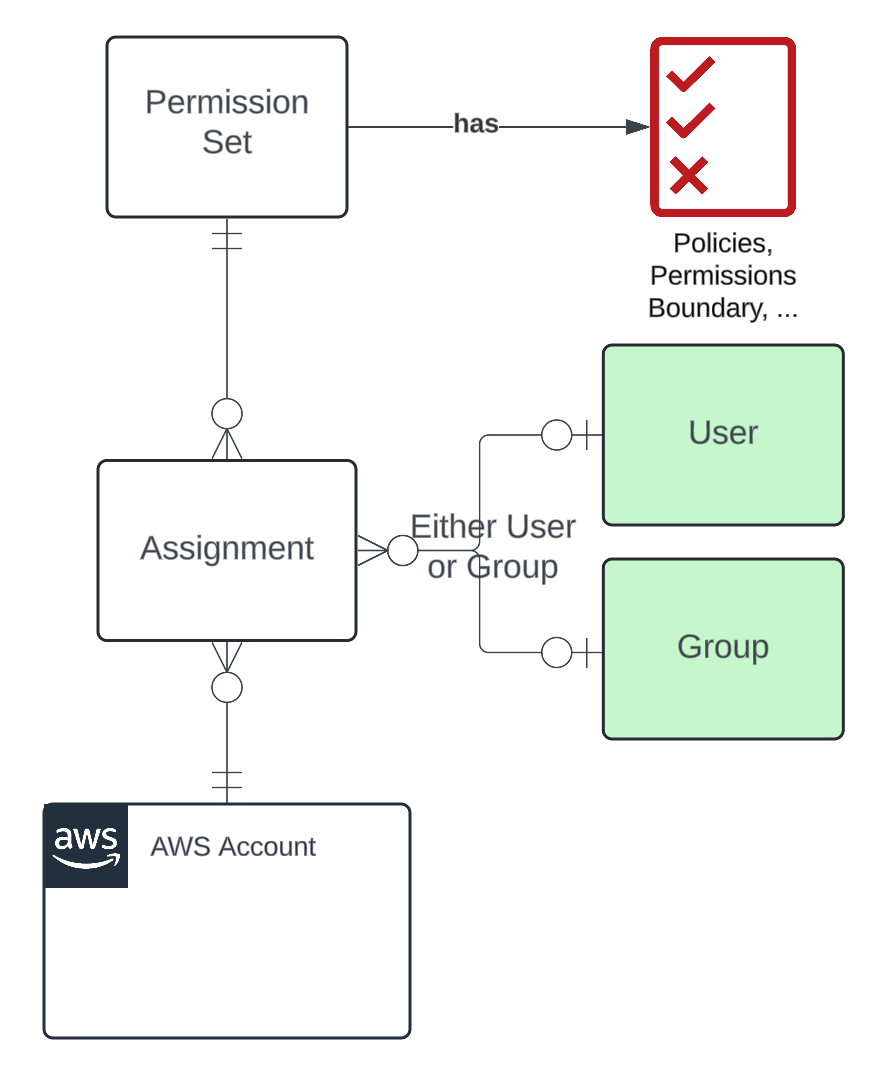
IAM solutions are designed to manage user identities, control access to resources, and enforce security policies within an organisation’s IT ecosystem. By centralising identity management processes, IAM systems help administrators define user roles, assign permissions, and monitor user activities across various applications and systems.
Effective IAM implementation enhances security by reducing the risk of unauthorised access to critical data and applications. It also simplifies compliance with regulatory requirements by providing detailed audit trails and access control mechanisms.
Single Sign-On (SSO)
SSO technology allows users to access multiple applications with a single set of login credentials. Instead of remembering numerous passwords for different systems, users can authenticate once and gain seamless access to authorised resources without the need for repeated logins.
SSO not only improves user convenience but also strengthens security by reducing the likelihood of password-related vulnerabilities such as weak passwords or password reuse. Centralised authentication through SSO simplifies identity management tasks for IT teams while enhancing overall system usability.
The Synergy Between IAM and SSO
Combining IAM with SSO creates a powerful security framework that streamlines access control processes while enhancing user productivity. IAM solutions provide the foundation for defining user identities, roles, and permissions, while SSO technology ensures secure authentication across multiple applications without compromising usability.
Organisations that leverage both IAM and SSO benefit from improved operational efficiency, reduced IT management overheads, enhanced data protection, and better regulatory compliance. By integrating these technologies seamlessly into their cybersecurity posture, businesses can mitigate risks effectively in an increasingly complex threat landscape.
Conclusion
In conclusion, Identity and Access Management (IAM) and Single Sign-On (SSO) are indispensable tools for modern cybersecurity efforts. By implementing robust IAM policies alongside efficient SSO mechanisms, organisations can fortify their defences against cyber threats while empowering users with secure access to essential resources. Embracing these technologies is not just a best practice but a strategic imperative in safeguarding digital assets and maintaining operational resilience in today’s dynamic business environment.
Eight Advantages of IAM and SSO: Boosting Security, Efficiency, and User Experience
- Enhanced security through centralised user identity management
- Streamlined access control for better data protection
- Improved compliance with regulatory requirements
- Reduced risk of unauthorised access to critical resources
- Simplified authentication processes for users
- Increased operational efficiency for IT teams
- Enhanced user experience with seamless access to multiple applications
- Mitigation of password-related vulnerabilities through single sign-on
Challenges of Implementing IAM and SSO: Navigating Complexity, User Resistance, Vulnerabilities, and Security Risks
Enhanced security through centralised user identity management
Enhanced security through centralised user identity management is a key benefit of implementing Identity and Access Management (IAM) and Single Sign-On (SSO) solutions. By consolidating user identities, roles, and permissions into a centralised system, organisations can effectively control access to sensitive data and critical applications. This approach not only reduces the risk of unauthorised access but also simplifies security administration tasks such as user provisioning, deprovisioning, and access control. Centralised user identity management ensures that only authorised individuals have appropriate access privileges, thereby strengthening overall security posture and mitigating potential cybersecurity threats.
Streamlined access control for better data protection
Streamlined access control facilitated by Identity and Access Management (IAM) and Single Sign-On (SSO) technologies is a significant advantage that enhances data protection in modern cybersecurity strategies. By centralising user authentication and authorisation processes, IAM and SSO solutions enable organisations to efficiently manage access to sensitive data and applications. This streamlined approach not only reduces the risk of unauthorised access but also simplifies the enforcement of security policies, leading to improved data protection measures. With IAM and SSO in place, businesses can establish granular control over user permissions, monitor user activities effectively, and strengthen their overall cybersecurity posture to safeguard critical information assets.
Improved compliance with regulatory requirements
One significant advantage of implementing Identity and Access Management (IAM) and Single Sign-On (SSO) solutions is the improvement in compliance with regulatory requirements. By centralising identity management processes, defining user roles, and enforcing access control policies, IAM systems ensure that organisations can easily track and audit user activities to meet regulatory standards. Additionally, SSO technology simplifies authentication processes across multiple applications, enhancing security measures and facilitating compliance with data protection regulations. Overall, the combination of IAM and SSO not only strengthens cybersecurity but also helps organisations adhere to regulatory mandates efficiently.
Reduced risk of unauthorised access to critical resources
One significant advantage of implementing Identity and Access Management (IAM) alongside Single Sign-On (SSO) is the reduced risk of unauthorised access to critical resources. By centralising identity management processes and enforcing strict access control policies, IAM ensures that only authorised users can access sensitive data and applications. SSO further enhances security by simplifying authentication across multiple systems, reducing the likelihood of password-related vulnerabilities. This proactive approach to user identity verification not only strengthens cybersecurity defences but also instils confidence in the protection of valuable organisational assets from potential security breaches.
Simplified authentication processes for users
One significant advantage of implementing Identity and Access Management (IAM) and Single Sign-On (SSO) solutions is the simplified authentication processes they offer to users. With SSO technology, users can access multiple applications and systems using a single set of credentials, eliminating the need to remember and manage multiple passwords. This streamlined authentication experience not only enhances user convenience but also reduces the risk of password-related security vulnerabilities. By centralising identity management and authentication through IAM and SSO, organisations can provide their users with a seamless and secure access experience across various resources, boosting productivity and user satisfaction.
Increased operational efficiency for IT teams
The integration of Identity and Access Management (IAM) and Single Sign-On (SSO) solutions offers a significant benefit of increased operational efficiency for IT teams. By centralising user identity management and authentication processes, IAM and SSO streamline access control tasks, reducing the administrative burden on IT staff. This efficiency enhancement allows IT teams to focus on strategic initiatives rather than routine user account maintenance, leading to improved productivity and resource allocation within the organisation’s IT infrastructure.
Enhanced user experience with seamless access to multiple applications
One significant advantage of implementing Identity and Access Management (IAM) alongside Single Sign-On (SSO) is the enhancement of user experience through seamless access to multiple applications. By utilising SSO technology, users can conveniently log in once with a single set of credentials and navigate across various platforms without the need for repeated authentication. This streamlined process not only improves user productivity but also reduces frustration associated with managing multiple passwords, ultimately fostering a more efficient and user-friendly digital environment.
Mitigation of password-related vulnerabilities through single sign-on
By implementing Single Sign-On (SSO) as part of an Identity and Access Management (IAM) strategy, organisations can effectively mitigate password-related vulnerabilities. SSO allows users to authenticate once and access multiple applications without the need to remember and manage multiple passwords. This not only enhances user convenience but also reduces the risk of password-related security incidents such as weak passwords, password reuse, or password theft. By centralising authentication through SSO, organisations can strengthen their security posture, improve user experience, and streamline access control processes, ultimately enhancing overall cybersecurity resilience.
Complex Implementation
Complex Implementation: One significant drawback of Identity and Access Management (IAM) and Single Sign-On (SSO) solutions is the complexity involved in their implementation. Setting up IAM and SSO systems can be a daunting task, demanding substantial time and resources for configuration and integration. Organisations may face challenges in aligning these technologies with existing IT infrastructure, ensuring compatibility with various applications, and training staff on new authentication processes. The intricate nature of implementation can lead to delays, increased costs, and potential disruptions to daily operations as IT teams navigate the complexities of deploying robust IAM and SSO solutions.
User Resistance
User Resistance: Introducing Identity and Access Management (IAM) and Single Sign-On (SSO) systems can encounter challenges due to user resistance. Some users may perceive the transition as disruptive, resulting in initial reluctance to adapt to new authentication processes. This resistance could potentially lead to productivity issues as employees navigate unfamiliar login procedures and adjust to changes in their daily workflows. Effective communication, training, and user support are essential in addressing these concerns and facilitating a smooth transition to IAM and SSO technologies.
Single Point of Failure
Dependence on a single sign-on mechanism poses a significant con of IAM and SSO due to the potential for a Single Point of Failure. In this scenario, if the SSO solution encounters downtime or falls victim to security breaches, the entire system may face a critical risk of failure. This vulnerability highlights the importance of implementing robust backup measures and contingency plans to mitigate the impact of such incidents and ensure continuous access to essential resources for users. Organizations must carefully weigh the convenience of SSO against the potential risks associated with relying solely on a single authentication mechanism to maintain operational resilience in the face of unforeseen challenges.
Increased Security Risks
Increased Security Risks: While IAM and SSO enhance security in many aspects, they can also introduce new vulnerabilities if not properly configured or monitored. Inadequate implementation of IAM policies or misconfiguration of SSO settings may create loopholes that malicious actors can exploit to gain unauthorised access to sensitive data or systems. Without vigilant oversight and regular security assessments, the benefits of IAM and SSO could be overshadowed by the potential risks posed by these overlooked vulnerabilities. It is crucial for organisations to invest in robust security measures and ongoing monitoring to mitigate these inherent risks associated with IAM and SSO implementations.