The Importance of Using a Backlink Tool for SEO Success
Backlinks are a crucial factor in determining the authority and credibility of a website in the eyes of search engines. They play a significant role in boosting your website’s search engine rankings and driving organic traffic. However, managing and monitoring backlinks can be a challenging task without the right tools.
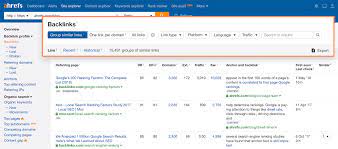
This is where a backlink tool comes into play. A backlink tool is a software or online service that helps website owners track, analyse, and manage their backlinks effectively. These tools provide valuable insights into your backlink profile, allowing you to identify high-quality links, detect toxic links, and monitor your overall link-building strategy.
One of the key benefits of using a backlink tool is the ability to track the performance of your backlinks over time. By monitoring factors such as link authority, anchor text diversity, and referring domains, you can make informed decisions about which links to keep, disavow, or pursue for future link-building efforts.
Furthermore, a backlink tool can help you stay ahead of your competitors by analysing their backlink profiles and identifying potential link-building opportunities. By understanding where your competitors are getting their backlinks from, you can develop strategies to acquire similar or better-quality links for your own website.
In addition to monitoring and analysing backlinks, some advanced backlink tools offer features such as automatic link discovery, broken link detection, and real-time alerts for new backlinks. These features can save you time and effort in managing your link-building efforts efficiently.
Overall, investing in a reliable backlink tool is essential for any website owner looking to improve their SEO performance. By leveraging the insights provided by these tools, you can enhance the quality of your backlink profile, increase your website’s visibility in search engine results pages, and ultimately drive more organic traffic to your site.
Take control of your website’s SEO success today with a powerful backlink tool that empowers you to make data-driven decisions and achieve long-term growth online.
7 Essential Tips for Maximising Your Backlink Strategy with the Right Tool
- Choose a backlink tool that provides accurate and up-to-date data.
- Regularly monitor your backlink profile to identify new links and disavow toxic ones.
- Analyse your competitors’ backlinks to discover potential linking opportunities.
- Focus on quality over quantity when building backlinks to your site.
- Diversify anchor text to avoid being penalised by search engines for over-optimisation.
- Track the impact of your backlink building efforts on search engine rankings and organic traffic.
- Stay updated with the latest SEO trends and algorithm changes to adapt your backlink strategy accordingly.
Choose a backlink tool that provides accurate and up-to-date data.
When selecting a backlink tool for your website, it is crucial to choose one that offers accurate and up-to-date data. Reliable and current information about your backlink profile is essential for making informed decisions regarding your SEO strategy. An accurate backlink tool ensures that you have a clear understanding of the quality and quantity of your backlinks, allowing you to identify opportunities for improvement and track the effectiveness of your link-building efforts. By opting for a tool that provides precise data, you can enhance your website’s search engine rankings and drive organic traffic more effectively.
Regularly monitor your backlink profile to identify new links and disavow toxic ones.
Regularly monitoring your backlink profile is a critical aspect of maintaining a healthy and effective SEO strategy. By keeping a close eye on your backlinks, you can quickly identify any new links that have been acquired and assess their quality and relevance. Equally important is the ability to detect and disavow toxic or spammy links that could harm your website’s credibility and search engine rankings. By proactively managing your backlink profile with the help of a reliable backlink tool, you can ensure that your link-building efforts are contributing positively to your SEO performance and overall online presence.
Analyse your competitors’ backlinks to discover potential linking opportunities.
By analysing your competitors’ backlinks using a backlink tool, you can uncover valuable insights and discover potential linking opportunities to enhance your own website’s SEO performance. Understanding where your competitors are gaining their backlinks from allows you to identify key websites and sources that could benefit your own link-building strategy. By leveraging this information, you can develop targeted approaches to acquire similar high-quality backlinks, improve your website’s authority, and stay competitive in search engine rankings.
Focus on quality over quantity when building backlinks to your site.
When utilising a backlink tool for enhancing your website’s SEO performance, it is crucial to prioritise quality over quantity when acquiring backlinks. While having a large number of backlinks may seem beneficial, the focus should be on obtaining high-quality links from reputable and relevant sources. Quality backlinks from authoritative websites not only improve your site’s credibility in the eyes of search engines but also drive targeted traffic to your site. By emphasising quality over quantity in your link-building strategy, you can ensure long-term success and sustainable growth for your website’s SEO efforts.
Diversify anchor text to avoid being penalised by search engines for over-optimisation.
It is crucial to diversify anchor text when utilising a backlink tool to prevent potential penalties from search engines due to over-optimisation. By varying the anchor text used in your backlinks, you can create a more natural and organic link profile that appears genuine to search engines. Overusing exact match keywords or phrases as anchor text can raise red flags and may lead to penalties for manipulating search rankings. Therefore, by incorporating a mix of relevant and diverse anchor text variations, you can maintain a healthy backlink profile and improve the overall credibility and authority of your website in the eyes of search engines.
Track the impact of your backlink building efforts on search engine rankings and organic traffic.
Tracking the impact of your backlink building efforts on search engine rankings and organic traffic is essential for evaluating the effectiveness of your SEO strategy. By using a backlink tool to monitor changes in your website’s rankings and traffic metrics after acquiring new backlinks, you can gain valuable insights into which links are contributing positively to your online visibility. This data allows you to refine your link-building tactics, focus on acquiring high-quality backlinks from authoritative sources, and ultimately improve your website’s performance in search engine results pages. Regularly analysing the correlation between your backlink profile and key SEO metrics enables you to make informed decisions that drive sustainable growth and success for your online presence.
Stay updated with the latest SEO trends and algorithm changes to adapt your backlink strategy accordingly.
Staying updated with the latest SEO trends and algorithm changes is crucial for adapting your backlink strategy effectively. Search engines continuously evolve their algorithms to provide users with the most relevant and high-quality search results. By keeping abreast of these changes, you can adjust your backlink strategy to align with current best practices and avoid any penalties that may arise from outdated tactics. Being proactive in monitoring SEO trends allows you to stay ahead of the curve, ensuring that your backlink profile remains strong and positively contributes to your website’s search engine rankings.