The Importance of Entitlement Management in Azure Active Directory
Managing user access and permissions within an organisation’s IT infrastructure is crucial for maintaining security and compliance. With the increasing complexity of modern IT environments, having robust entitlement management solutions is essential to prevent unauthorised access and ensure data protection. In this context, Azure Active Directory (Azure AD) offers powerful tools for effective entitlement management.
What is Entitlement Management?
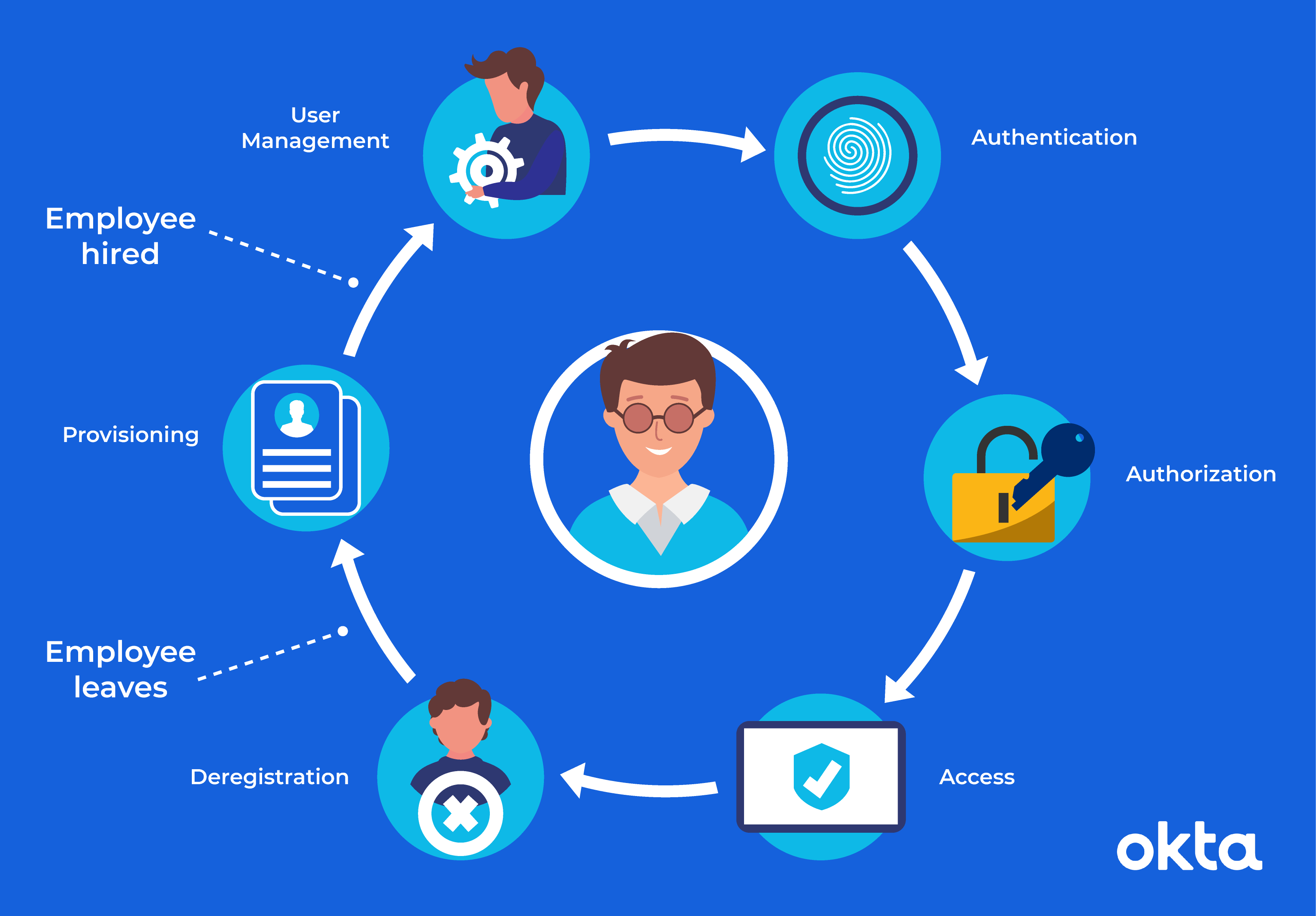
Entitlement management refers to the process of defining and managing user access rights to resources within an organisation. This includes granting appropriate permissions based on roles and responsibilities, as well as revoking access when necessary. By implementing a structured entitlement management system, organisations can reduce the risk of data breaches, insider threats, and compliance violations.
The Role of Azure Active Directory
Azure Active Directory is Microsoft’s cloud-based identity and access management service that provides a comprehensive set of features for managing user identities and access permissions. Within Azure AD, organisations can leverage entitlement management capabilities to streamline access control processes and enhance security.
Key Features of Entitlement Management in Azure AD:
- Role-Based Access Control (RBAC): Azure AD allows administrators to define roles with specific permissions and assign users to these roles. This role-based approach simplifies access management by ensuring that users have only the necessary permissions to perform their tasks.
- Entitlement Catalog: Organisations can create an entitlement catalog that lists resources and associated entitlements. This centralised repository helps in defining fine-grained access policies and tracking user entitlements across applications.
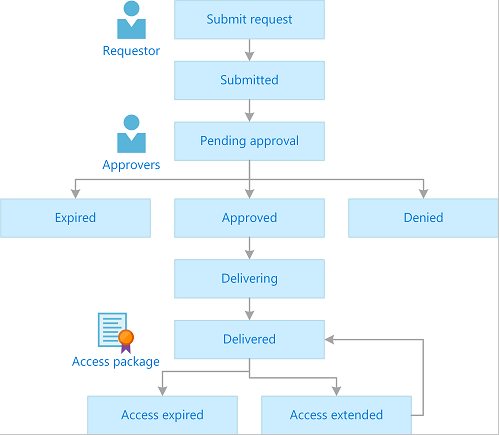
- Lifecycle Management: Azure AD offers automated workflows for provisioning and deprovisioning user access based on predefined policies. This ensures that users receive appropriate access during their tenure with the organisation and that access is revoked promptly upon departure.
- Audit Trails: Detailed audit logs in Azure AD enable administrators to monitor user activities, track changes in permissions, and investigate security incidents. By maintaining audit trails, organisations can demonstrate compliance with regulatory requirements.
The Benefits of Entitlement Management in Azure AD
Implementing effective entitlement management in Azure AD brings several benefits to organisations:
- Enhanced Security: By enforcing least-privileged access principles, organisations can minimise the risk of unauthorised data exposure or malicious activities.
- Improved Compliance: Compliance mandates often require organisations to implement stringent access controls. With Azure AD’s entitlement management features, organisations can easily demonstrate compliance with regulations such as GDPR or HIPAA.
- Efficient Access Control: Automation capabilities in Azure AD streamline the process of granting and revoking access rights, reducing administrative overhead and ensuring timely responses to access requests.
- User Experience: Users benefit from a seamless experience with simplified login processes, self-service options for requesting access, and clear visibility into their assigned entitlements.
In Conclusion
In today’s digital landscape where data security is paramount, effective entitlement management is a critical component of an organisation’s cybersecurity strategy. By leveraging the capabilities of Azure Active Directory for entitlement management, organisations can strengthen their security posture, improve operational efficiency, and ensure regulatory compliance.
If you are looking to enhance your organisation’s access control mechanisms, consider utilising Azure AD’s powerful entitlement management features to safeguard your valuable assets effectively.
7 Essential Tips for Effective Entitlement Management in Azure AD
- Define clear entitlement policies for different roles within your organisation.
- Regularly review and update entitlements to ensure they align with current business needs.
- Implement least privilege access to restrict user permissions to only what is necessary for their role.
- Utilise Azure AD Privileged Identity Management to manage, control, and monitor access within your organisation.
- Enable multi-factor authentication to add an extra layer of security to user logins.
- Monitor and audit entitlement changes to detect any unauthorized access or unusual activities.
- Provide regular training and awareness programs on entitlement management best practices for employees.
Define clear entitlement policies for different roles within your organisation.
To enhance access control and security within your organisation, it is essential to define clear entitlement policies for different roles in Azure Active Directory. By establishing specific permissions and access levels based on job functions and responsibilities, you can ensure that users have the appropriate level of access to resources. This approach not only reduces the risk of unauthorised data exposure but also streamlines the management of user entitlements. Clear entitlement policies help maintain a structured approach to access control, promoting accountability and compliance with regulatory requirements.
Regularly review and update entitlements to ensure they align with current business needs.
It is essential to regularly review and update entitlements in Azure Active Directory to ensure they align with current business needs. By conducting periodic reviews of user access rights and permissions, organisations can proactively identify any discrepancies or unnecessary entitlements that may pose security risks. This practice not only helps maintain a secure IT environment but also ensures that users have the appropriate level of access required to fulfil their roles effectively. Regularly updating entitlements in Azure AD is a proactive measure that enhances security, compliance, and overall operational efficiency within an organisation.
Implement least privilege access to restrict user permissions to only what is necessary for their role.
Implementing least privilege access is a fundamental principle in entitlement management within Azure Active Directory. By restricting user permissions to only what is essential for their specific role, organisations can minimise the risk of unauthorised access and potential security breaches. This approach ensures that users have the necessary permissions to fulfil their responsibilities without granting unnecessary privileges that could compromise data security. By adopting least privilege access in Azure AD, organisations can enhance their overall security posture and mitigate the potential impact of insider threats or malicious activities.
Utilise Azure AD Privileged Identity Management to manage, control, and monitor access within your organisation.
To enhance access control and security within your organisation, it is recommended to leverage Azure AD Privileged Identity Management. This feature enables you to effectively manage, control, and monitor access to privileged roles and resources in Azure Active Directory. By implementing Privileged Identity Management, you can reduce the risk of insider threats, prevent unauthorised access to critical systems, and ensure that only authorised personnel have elevated privileges. This proactive approach strengthens your overall security posture and helps in maintaining compliance with industry regulations.
Enable multi-factor authentication to add an extra layer of security to user logins.
Enabling multi-factor authentication in Azure Active Directory is a highly recommended practice to enhance security for user logins. By requiring users to provide an additional form of verification beyond just a password, such as a code sent to their mobile device or biometric data, organisations can significantly reduce the risk of unauthorised access and potential data breaches. This extra layer of security adds an essential barrier against cyber threats, ensuring that only authorised users can successfully authenticate and access sensitive resources within the Azure AD environment.
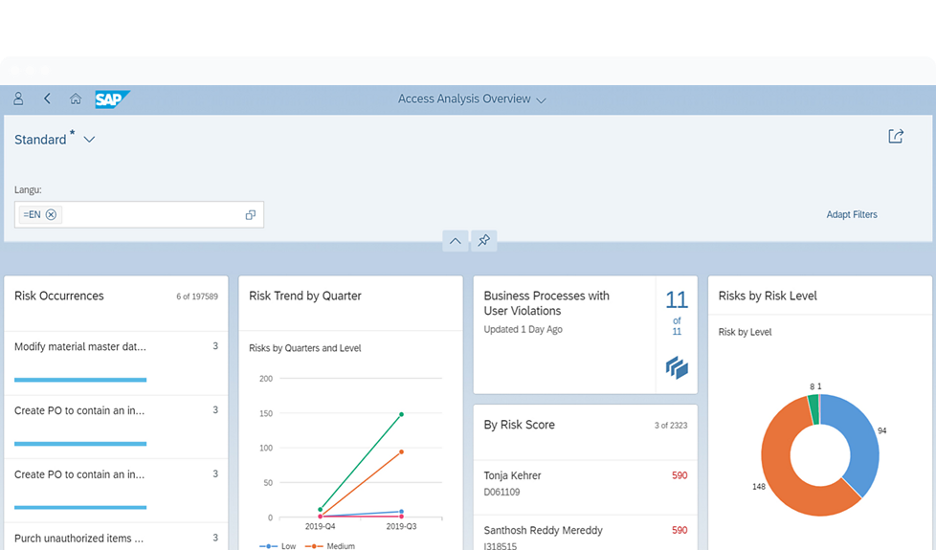
Monitor and audit entitlement changes to detect any unauthorized access or unusual activities.
Monitoring and auditing entitlement changes in Azure Active Directory is a crucial tip to enhance security and detect any unauthorised access or suspicious activities within an organisation’s IT environment. By closely tracking changes in user permissions and entitlements, administrators can quickly identify any deviations from established access policies, potential insider threats, or security breaches. Regular monitoring of entitlement changes enables proactive detection of unusual activities, allowing for prompt investigation and mitigation actions to safeguard sensitive data and maintain the integrity of the IT infrastructure.
Provide regular training and awareness programs on entitlement management best practices for employees.
To enhance the effectiveness of entitlement management in Azure AD, it is essential to provide regular training and awareness programs on best practices for employees. By educating staff members on the importance of access control, role-based permissions, and proper handling of user entitlements, organisations can empower their workforce to contribute to a secure IT environment. Training sessions can help employees understand their roles in maintaining data security, recognise potential risks associated with access privileges, and adhere to established policies and procedures. Through ongoing education and awareness initiatives, organisations can cultivate a culture of responsibility and vigilance towards entitlement management within Azure AD.