The Importance of Networking Security in the Digital Age
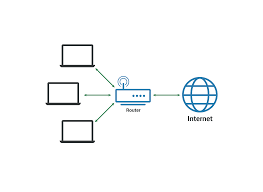
In today’s interconnected world, where businesses rely heavily on digital networks to operate efficiently, the importance of networking security cannot be overstated. With the rise of cyber threats and data breaches, safeguarding your network infrastructure has become a critical priority for organisations of all sizes.
Protecting Sensitive Information
Networking security plays a crucial role in protecting sensitive information from falling into the wrong hands. Whether it’s customer data, intellectual property, or financial records, a secure network ensures that confidential information remains confidential. By implementing robust security measures such as firewalls, encryption protocols, and access controls, businesses can mitigate the risk of data breaches and safeguard their valuable assets.
Preventing Cyber Attacks
Cyber attacks are becoming increasingly sophisticated and prevalent in today’s digital landscape. From ransomware to phishing scams, malicious actors are constantly looking for vulnerabilities to exploit in network systems. Networking security measures such as intrusion detection systems, regular security audits, and employee training can help prevent cyber attacks and minimise their impact on your organisation.
Ensuring Business Continuity
A secure network is essential for ensuring business continuity in the face of unexpected disruptions. Whether it’s a natural disaster, hardware failure, or cyber attack, having robust networking security measures in place can help mitigate downtime and ensure that critical business operations continue uninterrupted. By implementing backup systems, disaster recovery plans, and redundancy protocols, businesses can maintain resilience in the face of unforeseen challenges.
Compliance with Regulations
Many industries are subject to strict regulatory requirements concerning data protection and privacy. Failure to comply with these regulations can result in hefty fines and reputational damage for businesses. Networking security measures such as data encryption, access controls, and audit trails help organisations meet regulatory standards and demonstrate their commitment to safeguarding customer information.
Conclusion
In conclusion, networking security is a fundamental aspect of modern business operations. By investing in robust security measures and staying vigilant against emerging threats, organisations can protect their sensitive information, prevent cyber attacks, ensure business continuity, and comply with regulatory requirements. In an era where digital risks are ever-present, prioritising networking security is essential for maintaining a safe and resilient network infrastructure.
Top 7 Benefits of Networking Security for Organisations
- Enhances data protection and confidentiality
- Mitigates the risk of cyber attacks and data breaches
- Ensures business continuity in case of disruptions
- Helps organisations comply with regulatory requirements
- Improves network performance and reliability
- Enhances trust and credibility with customers and partners
- Provides peace of mind for stakeholders regarding network security
Challenges in Networking Security: Addressing Complexity, Cost, and Other Key Concerns
- Complexity
- Cost
- User Resistance
- False Positives
- Maintenance Overhead
- Compatibility Issues
- Overreliance on Technology
Enhances data protection and confidentiality
Networking security plays a crucial role in enhancing data protection and confidentiality within an organisation. By implementing encryption protocols, access controls, and secure communication channels, businesses can safeguard sensitive information from unauthorised access or interception. This proactively ensures that confidential data remains protected from cyber threats and malicious actors, bolstering the overall security posture of the network infrastructure. Maintaining a focus on networking security not only mitigates the risk of data breaches but also instils trust among stakeholders regarding the organisation’s commitment to upholding data privacy and confidentiality standards.
Mitigates the risk of cyber attacks and data breaches
One of the key benefits of networking security is its ability to mitigate the risk of cyber attacks and data breaches. By implementing robust security measures such as firewalls, intrusion detection systems, and encryption protocols, organisations can significantly reduce the likelihood of malicious actors gaining unauthorized access to sensitive information. This proactive approach not only helps in safeguarding valuable data but also enhances the overall resilience of the network infrastructure against potential threats, ensuring a more secure and trustworthy digital environment for businesses and their stakeholders.
Ensures business continuity in case of disruptions
Networking security plays a crucial role in ensuring business continuity in the event of disruptions. By implementing robust security measures and disaster recovery plans, organisations can minimise downtime and maintain critical operations even during unexpected events such as natural disasters, cyber attacks, or hardware failures. A secure network infrastructure provides the resilience needed to swiftly address disruptions and mitigate their impact on business activities, allowing companies to uphold productivity and service delivery without significant interruptions.
Helps organisations comply with regulatory requirements
Networking security plays a crucial role in helping organisations comply with regulatory requirements. By implementing stringent security measures such as data encryption, access controls, and audit trails, businesses can demonstrate their commitment to safeguarding sensitive information in accordance with industry regulations. Compliance with data protection and privacy laws not only protects the organisation from potential fines and legal consequences but also enhances trust and credibility among customers and stakeholders. Networking security ensures that organisations meet the necessary standards set forth by regulatory bodies, fostering a culture of accountability and responsibility in handling confidential data.
Enhancing network performance and reliability is a significant advantage of implementing networking security measures. By optimising network configurations, monitoring traffic patterns, and identifying potential bottlenecks, organisations can ensure that their networks operate efficiently and smoothly. With improved performance comes increased productivity, as employees can access resources and collaborate seamlessly. Moreover, by enhancing reliability through measures such as redundancy and failover systems, businesses can minimise downtime and maintain continuous operations, ultimately boosting customer satisfaction and trust in their services.
Enhances trust and credibility with customers and partners
Enhancing trust and credibility with customers and partners is a significant benefit of networking security. By demonstrating a commitment to safeguarding sensitive information and maintaining the integrity of data exchanges, businesses can build strong relationships based on reliability and confidence. When customers and partners feel assured that their data is secure within your network, they are more likely to engage with your services or collaborate with your organisation, leading to long-term partnerships and positive brand reputation. Networking security not only protects valuable assets but also fosters trust among stakeholders, ultimately contributing to the growth and success of the business.
Provides peace of mind for stakeholders regarding network security
Networking security provides invaluable peace of mind for stakeholders by assuring them that robust measures are in place to safeguard the integrity and confidentiality of network systems. Knowing that the network is protected against cyber threats and data breaches instils confidence in stakeholders, whether they are employees, customers, or business partners. This assurance not only enhances trust in the organisation’s ability to protect sensitive information but also demonstrates a commitment to prioritising security as a core aspect of operations. Ultimately, networking security offers stakeholders a sense of reassurance and confidence in the reliability and resilience of the network infrastructure.
Complexity
The complexity of implementing and managing networking security measures poses a significant challenge for organisations. It demands specialised knowledge and expertise to navigate the intricacies of security protocols, configurations, and threat detection mechanisms. This complexity can lead to delays in deployment, increased operational costs, and potential gaps in security if not managed effectively. Moreover, the ever-evolving nature of cyber threats means that continuous monitoring and adaptation are essential, adding to the time-consuming nature of maintaining robust networking security. Organizations must carefully balance the need for comprehensive security measures with the resources required to manage the complexities involved in order to effectively safeguard their network infrastructure.
Cost
One significant con of networking security is the cost involved in implementing robust security measures. For small businesses with limited budgets, investing in comprehensive networking security solutions can be a financial challenge. The expenses associated with purchasing and maintaining firewalls, intrusion detection systems, encryption tools, and other security technologies can quickly add up, potentially straining the financial resources of smaller organisations. As a result, some businesses may struggle to afford the level of protection needed to effectively safeguard their network infrastructure against cyber threats and data breaches.
User Resistance
User Resistance can pose a significant challenge in implementing effective networking security measures within an organisation. When employees push back against stringent security protocols that limit their access or introduce additional authentication steps, it can create potential vulnerabilities in the network. User resistance may stem from inconvenience, perceived hindrance to productivity, or lack of understanding about the importance of security measures. Addressing this con requires a delicate balance between ensuring robust security practices and educating employees about the necessity of following protocols to safeguard sensitive data and mitigate cyber risks. Failure to overcome user resistance can leave networks exposed to exploitation and compromise overall cybersecurity efforts.
False Positives
False positives in networking security present a significant challenge for organisations, as security systems may inadvertently flag legitimate activities as threats, resulting in unnecessary disruptions and confusion. When security systems generate false alerts, it can lead to wasted time and resources investigating non-existent issues, diverting attention away from genuine threats. This can create a sense of complacency within the organisation, where real security risks may be overlooked or underestimated due to the noise generated by false positives. Addressing the issue of false positives requires a delicate balance between maintaining a high level of vigilance against potential threats while minimising the impact of inaccurate alerts on daily operations.
Maintenance Overhead
One significant con of networking security is the maintenance overhead it imposes on organisations. Regular maintenance and updates are essential to keep security measures effective and up-to-date, which can significantly increase the workload of IT teams. Constant monitoring, patching vulnerabilities, and ensuring compliance with security protocols demand time and resources, diverting attention from other critical IT tasks. The ongoing need for maintenance can strain IT resources and lead to potential gaps in security if not managed diligently, highlighting the challenge of balancing proactive security measures with day-to-day operational demands.
Compatibility Issues
Compatibility issues are a significant con of networking security that organisations often face. Integrating various security tools and technologies within a network environment can result in compatibility challenges that impede the overall effectiveness of the security measures in place. When different systems do not communicate seamlessly or work together cohesively, gaps in protection may arise, leaving vulnerabilities exposed. These compatibility issues can create complexities for IT teams, leading to increased maintenance efforts and potential gaps in security coverage, ultimately compromising the network’s resilience against cyber threats. Addressing compatibility issues requires careful planning, testing, and coordination to ensure that all security components work harmoniously to provide comprehensive protection for the network infrastructure.
Overreliance on Technology
Overreliance on technology in networking security poses a significant con as it can lead to a false sense of security and neglect crucial vulnerabilities. Depending solely on automated security solutions without human oversight may result in overlooking nuanced threats that require human intuition and analysis. Human involvement is essential for identifying potential weaknesses, adapting to evolving cyber threats, and implementing strategic security measures that go beyond the capabilities of automated systems. Failing to balance technological solutions with human expertise can leave networks exposed to sophisticated attacks that automated tools alone may not detect or effectively mitigate.