The Importance of Nessus Active Directory Audit
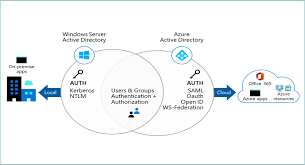
Active Directory is a critical component of many organisations’ IT infrastructure, serving as the central hub for managing user accounts, permissions, and access to resources. With the increasing complexity of cyber threats and the growing emphasis on data security and compliance, it is more important than ever to ensure the integrity and security of your Active Directory environment.
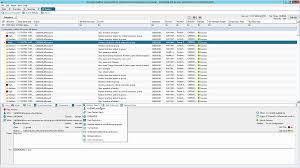
Nessus Active Directory Audit is a powerful tool that can help organisations proactively monitor and assess the security of their Active Directory implementation. Nessus, known for its robust vulnerability scanning capabilities, extends its functionality to provide comprehensive auditing features specifically tailored for Active Directory environments.
Key Benefits of Nessus Active Directory Audit:
- Vulnerability Detection: Nessus actively scans your Active Directory environment to identify potential security vulnerabilities, misconfigurations, and weaknesses that could be exploited by attackers.
- Policy Compliance: Ensure that your Active Directory setup complies with industry standards and regulatory requirements by running predefined compliance checks provided by Nessus.
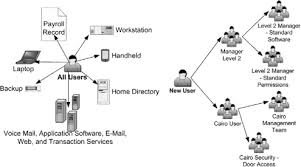
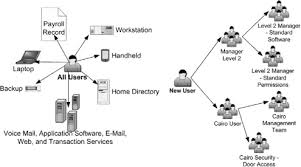
- User Activity Monitoring: Track user activity within your Active Directory, including logon events, account modifications, and access permissions changes to detect suspicious behaviour or unauthorised actions.
- Real-time Alerts: Receive immediate alerts for critical events or policy violations within your Active Directory environment, allowing you to respond swiftly to potential security incidents.
- Reporting and Analysis: Generate detailed reports on the security posture of your Active Directory infrastructure, including actionable insights and recommendations for improving overall security.
By leveraging Nessus Active Directory Audit, organisations can enhance their cybersecurity defences and reduce the risk of data breaches or compliance violations. The proactive monitoring and auditing capabilities provided by Nessus empower IT teams to stay ahead of emerging threats and maintain a secure Active Directory environment.
In conclusion, investing in Nessus Active Directory Audit is a proactive step towards strengthening your organisation’s cybersecurity posture and safeguarding sensitive information stored within your Active Directory. With its comprehensive features and robust scanning capabilities, Nessus provides the tools needed to effectively audit and secure your Active Directory infrastructure in today’s ever-evolving threat landscape.
Top 7 Advantages of Using Nessus for Active Directory Audits
- Comprehensive vulnerability detection for Active Directory environment
- Real-time monitoring of user activity and security events
- Automated compliance checks to ensure adherence to industry standards
- Detailed reporting and analysis for actionable insights
- Customisable alerts for immediate response to security incidents
- Integration with Nessus’ powerful vulnerability scanning capabilities
- User-friendly interface for easy configuration and management
Challenges of Nessus Active Directory Audits: Learning Curves, Costs, and Configuration Complexities
- Steep Learning Curve
- Resource Intensive
- Costly Licensing
- Complex Configuration
- False Positives
- Limited Customisation
- Integration Challenges
Comprehensive vulnerability detection for Active Directory environment
One of the key advantages of Nessus Active Directory Audit is its ability to provide comprehensive vulnerability detection specifically tailored for the Active Directory environment. By actively scanning and assessing the security posture of Active Directory components, Nessus can identify potential vulnerabilities, misconfigurations, and weaknesses that could be exploited by malicious actors. This proactive approach to vulnerability detection allows organisations to address security gaps promptly, enhancing the overall resilience of their Active Directory infrastructure and reducing the risk of cyber threats impacting critical business operations.
Real-time monitoring of user activity and security events
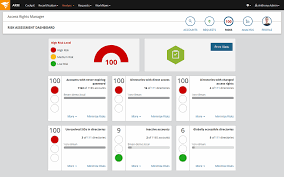
One significant advantage of Nessus Active Directory Audit is its capability for real-time monitoring of user activity and security events within the Active Directory environment. This feature allows organisations to promptly detect and respond to any suspicious behaviour or security incidents, ensuring enhanced visibility and control over user actions. By monitoring user activity in real-time, Nessus empowers IT teams to proactively identify potential threats, unauthorised access attempts, or policy violations, thereby strengthening the overall security posture of the Active Directory infrastructure.
Automated compliance checks to ensure adherence to industry standards
One significant advantage of Nessus Active Directory Audit is its capability to conduct automated compliance checks, guaranteeing adherence to industry standards and regulatory requirements. By automating the process of verifying compliance with established guidelines, organisations can efficiently assess their Active Directory environment’s alignment with best practices and regulations without the need for manual intervention. This feature not only saves time and resources but also provides a proactive approach to maintaining a secure and compliant IT infrastructure, ultimately enhancing overall cybersecurity posture.
Detailed reporting and analysis for actionable insights
One of the key advantages of Nessus Active Directory Audit is its capability to provide detailed reporting and analysis, offering actionable insights for IT teams. By generating comprehensive reports on the security status of the Active Directory environment, Nessus enables organisations to gain valuable visibility into potential vulnerabilities, policy compliance issues, and user activity. These insights empower IT professionals to make informed decisions and take proactive measures to enhance security, address weaknesses, and mitigate risks effectively.
Customisable alerts for immediate response to security incidents
One significant advantage of Nessus Active Directory Audit is its customisable alerts feature, which enables organisations to set up tailored notifications for specific security events within their Active Directory environment. This capability allows for immediate response to potential security incidents, ensuring that IT teams can swiftly address and mitigate threats as they arise. By configuring alerts based on predefined criteria or user-defined parameters, organisations can proactively monitor their Active Directory infrastructure and take prompt action to safeguard against cyber threats and unauthorised activities.
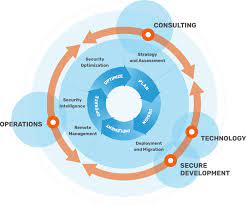
Integration with Nessus’ powerful vulnerability scanning capabilities
One significant advantage of Nessus Active Directory Audit is its seamless integration with Nessus’ formidable vulnerability scanning capabilities. By leveraging this integration, organisations can benefit from a comprehensive security assessment that not only audits Active Directory settings but also identifies potential vulnerabilities within the network infrastructure. This synergy allows for a holistic approach to cybersecurity, enabling IT teams to proactively address security gaps and strengthen defences against emerging threats. The combination of Active Directory auditing and vulnerability scanning empowers organisations to enhance their overall security posture and mitigate risks effectively.
User-friendly interface for easy configuration and management
One of the standout benefits of Nessus Active Directory Audit is its user-friendly interface, which simplifies the configuration and management process for IT professionals. With an intuitive design and straightforward navigation, users can easily set up audit scans, configure monitoring parameters, and manage security policies without the need for extensive training or technical expertise. This streamlined approach not only saves time but also enhances overall efficiency, allowing organisations to proactively assess and secure their Active Directory environment with ease.
Steep Learning Curve
One notable drawback of Nessus Active Directory Audit is its steep learning curve, which may pose a challenge for users looking to maximise the benefits of its features and functionalities. Navigating through the complexities of the tool and understanding how to effectively interpret and act upon the audit results may require a significant investment of time and resources. This learning curve could potentially slow down the implementation process and hinder the immediate effectiveness of Nessus Active Directory Audit in enhancing the security posture of an organisation’s Active Directory environment.
Resource Intensive
One significant drawback of using Nessus Active Directory Audit is its resource-intensive nature. Conducting regular scans and audits with Nessus can place a heavy demand on system resources, potentially leading to a degradation in the performance of the Active Directory environment. The extensive scanning processes and data collection activities carried out by Nessus may strain server capacities, causing delays in user authentication, slower response times, and overall system inefficiencies. Organisations must carefully balance the benefits of thorough auditing with the potential impact on system performance when utilising Nessus for Active Directory security assessments.
Costly Licensing
One significant drawback of implementing Nessus Active Directory Audit is the potentially high cost associated with licensing. For organisations operating on limited budgets, the expense of Nessus licensing fees, particularly when factoring in additional modules or support services, can pose a financial challenge. The substantial investment required to acquire and maintain Nessus licenses may deter some organisations from fully utilising this powerful auditing tool, impacting their ability to enhance the security and compliance of their Active Directory environment effectively.
Complex Configuration
One significant drawback of using Nessus Active Directory Audit is the complexity involved in configuring the tool for auditing purposes. Setting up Nessus to effectively audit an Active Directory environment can be a challenging task that demands a certain level of expertise and time investment to ensure proper configuration. Organisations may face hurdles in navigating the intricacies of Nessus settings and customising them to align with their specific Active Directory requirements. This complexity can potentially lead to delays in implementation and require additional training or resources to overcome, making it a notable con for those seeking a straightforward auditing solution.
False Positives
False Positives are a notable drawback of using Nessus Active Directory Audit. As with any scanning tool, Nessus has the potential to produce false positives, indicating security issues that may not actually exist within the Active Directory environment. These false alerts can result in unnecessary investigations and actions, consuming valuable time and resources. Organisations must be vigilant in distinguishing between genuine security threats and false positives identified by Nessus to ensure an efficient and effective auditing process.
Limited Customisation
Some users have expressed a con regarding Nessus Active Directory Audit, citing limited customisation options. They find that the level of customisation available may not be as extensive as they require to meet their specific needs. This limitation can potentially hinder users who seek more tailored audit configurations to address unique aspects of their Active Directory environment.
Integration Challenges
One notable drawback of Nessus Active Directory Audit is the potential integration challenges it poses. The process of integrating Nessus with pre-existing security tools or workflows may encounter obstacles, primarily stemming from compatibility issues or configuration conflicts. These challenges can lead to delays in implementation and may require additional resources to resolve, impacting the efficiency and effectiveness of the overall security audit process. Organizations considering the adoption of Nessus Active Directory Audit should be prepared to address these integration hurdles to fully leverage its capabilities and benefits.