The Importance of Compliance Reporting Tools in Today’s Business Environment
In the rapidly evolving landscape of business regulations and data protection laws, organisations are facing increasing pressure to ensure compliance with a myriad of requirements. Compliance reporting tools have emerged as essential assets for businesses seeking to navigate the complex web of rules and regulations governing their operations.
What are Compliance Reporting Tools?
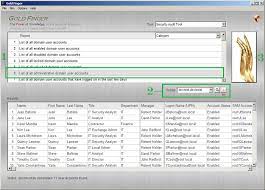
Compliance reporting tools are software solutions designed to help organisations monitor, track, and report on their adherence to various regulatory requirements. These tools provide a centralised platform for collecting, analysing, and presenting data related to compliance activities, making it easier for businesses to demonstrate their commitment to following the law.
The Benefits of Using Compliance Reporting Tools
There are several key benefits to using compliance reporting tools in today’s business environment:
- Efficiency: Compliance reporting tools automate many manual tasks associated with monitoring and reporting on regulatory compliance, saving time and resources for organisations.
- Accuracy: By centralising data collection and analysis processes, compliance reporting tools reduce the risk of errors and inconsistencies in compliance reports, ensuring that businesses have reliable information at their fingertips.
- Visibility: These tools provide real-time insights into an organisation’s compliance status, allowing stakeholders to quickly identify areas of non-compliance and take corrective action promptly.
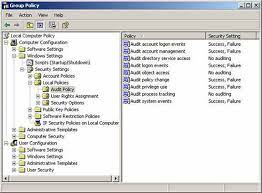
- Audit Trail: Compliance reporting tools maintain a detailed audit trail of compliance activities, making it easier for businesses to demonstrate their adherence to regulations during audits or investigations.
Choosing the Right Compliance Reporting Tool
When selecting a compliance reporting tool for your organisation, it is essential to consider factors such as the complexity of your regulatory environment, scalability requirements, integration capabilities with existing systems, and user-friendliness. Look for a tool that aligns with your specific compliance needs and provides robust features for data analysis, custom reporting, and audit support.
In Conclusion
In today’s highly regulated business environment, compliance reporting tools play a crucial role in helping organisations meet their legal obligations while minimising risks associated with non-compliance. By leveraging these tools effectively, businesses can streamline their compliance processes, enhance transparency with stakeholders, and build a strong foundation for sustainable growth in an increasingly complex regulatory landscape.
Exploring Varieties of Compliance Reporting
The Four Fundamental Components of a Compliance Framework
4. A Guide to Effective Compliance Reporting Practices
- What are compliance tools?
- What are the different types of compliance reporting?
- What are the 4 components of the compliance framework?
- How to do compliance reporting?
What are compliance tools?
Compliance tools are specialised software solutions designed to assist organisations in ensuring adherence to regulatory requirements and industry standards. These tools help businesses monitor, track, and report on their compliance activities, providing a centralised platform for managing various aspects of regulatory compliance. By automating tasks related to data collection, analysis, and reporting, compliance tools enable businesses to streamline their compliance processes, enhance accuracy in reporting, and maintain a comprehensive record of their adherence to regulations. Ultimately, compliance tools play a vital role in helping organisations navigate the complex landscape of compliance obligations efficiently and effectively.
What are the different types of compliance reporting?
When it comes to compliance reporting, there are several different types that organisations may need to consider. These include regulatory compliance reporting, which focuses on meeting specific legal requirements set forth by governing bodies; internal compliance reporting, which involves adherence to internal policies and procedures within an organisation; financial compliance reporting, which pertains to financial regulations and standards such as SOX compliance; and industry-specific compliance reporting, which addresses regulations unique to particular sectors. Each type of compliance reporting serves a distinct purpose in ensuring that businesses operate ethically, transparently, and in accordance with applicable laws and standards.
What are the 4 components of the compliance framework?
In the realm of compliance reporting tools, understanding the fundamental components of a compliance framework is crucial for ensuring effective adherence to regulatory requirements. The four key components of a compliance framework typically include policies and procedures, risk assessment, monitoring and testing, and enforcement and response. Policies and procedures establish the rules and guidelines that govern compliance efforts, while risk assessment helps identify potential areas of non-compliance. Monitoring and testing involve ongoing evaluation of processes to ensure compliance, while enforcement and response mechanisms address violations and implement corrective actions swiftly. By integrating these components into their compliance framework, organisations can establish a robust system for maintaining regulatory compliance and mitigating risks effectively.
How to do compliance reporting?
When it comes to compliance reporting, the process typically involves several key steps to ensure that an organisation meets regulatory requirements effectively. To begin, businesses need to identify the specific regulations that apply to their industry and operations. Next, they must establish clear policies and procedures for collecting relevant data and monitoring compliance activities. Implementing a robust compliance reporting tool can streamline this process by automating data collection, analysis, and report generation. Regularly reviewing and auditing the compliance reports is crucial to identifying any issues or discrepancies promptly. By following a structured approach and leveraging the right tools, organisations can navigate the complexities of compliance reporting with confidence and accuracy.