The Importance of Entitlement Management Systems in Modern Businesses
In today’s digital landscape, where data breaches and cyber threats are prevalent, managing user access to sensitive information has become a critical concern for businesses. This is where Entitlement Management Systems (EMS) play a crucial role in ensuring the security and integrity of an organisation’s data.
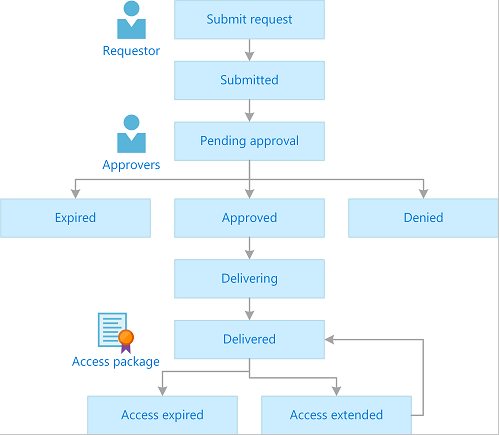
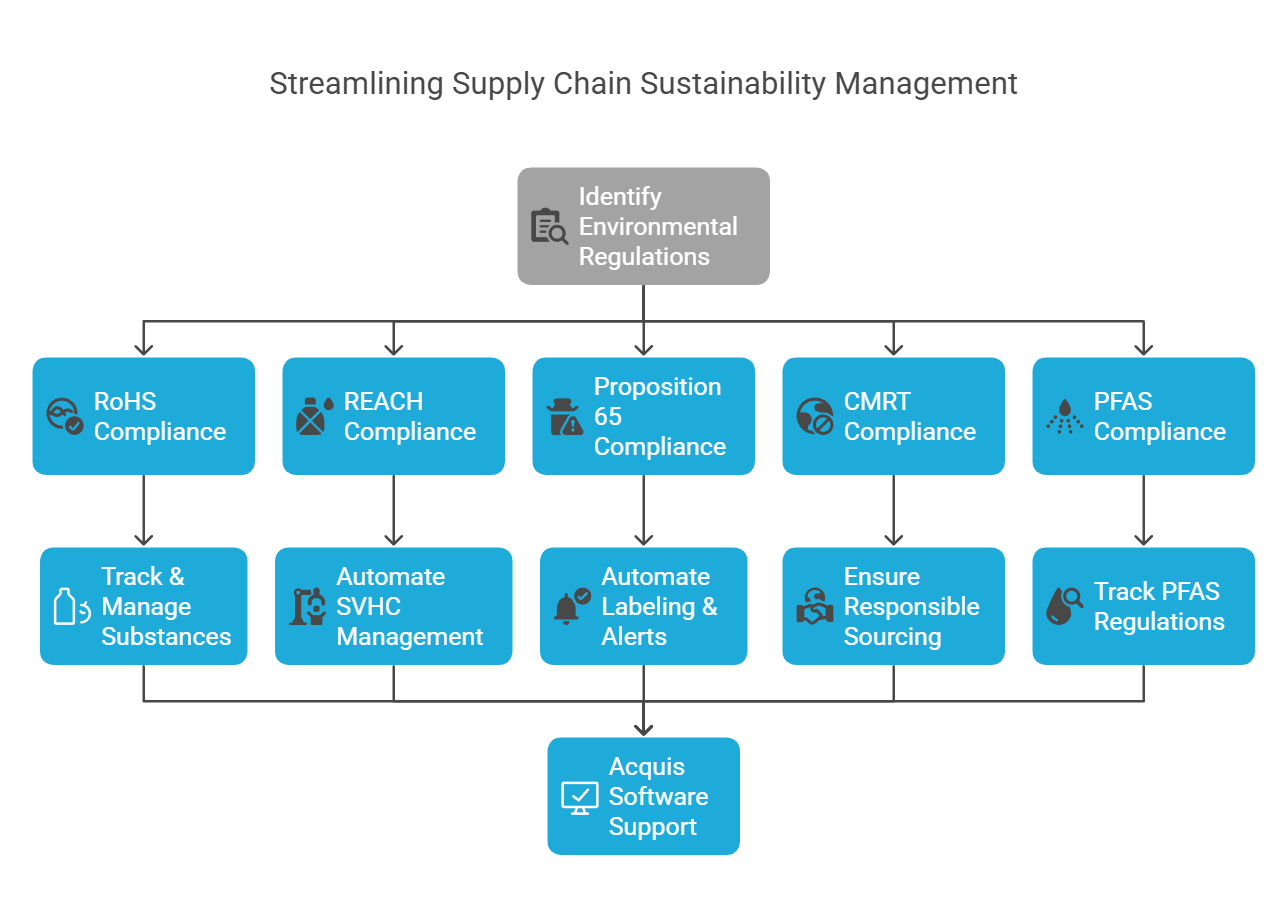
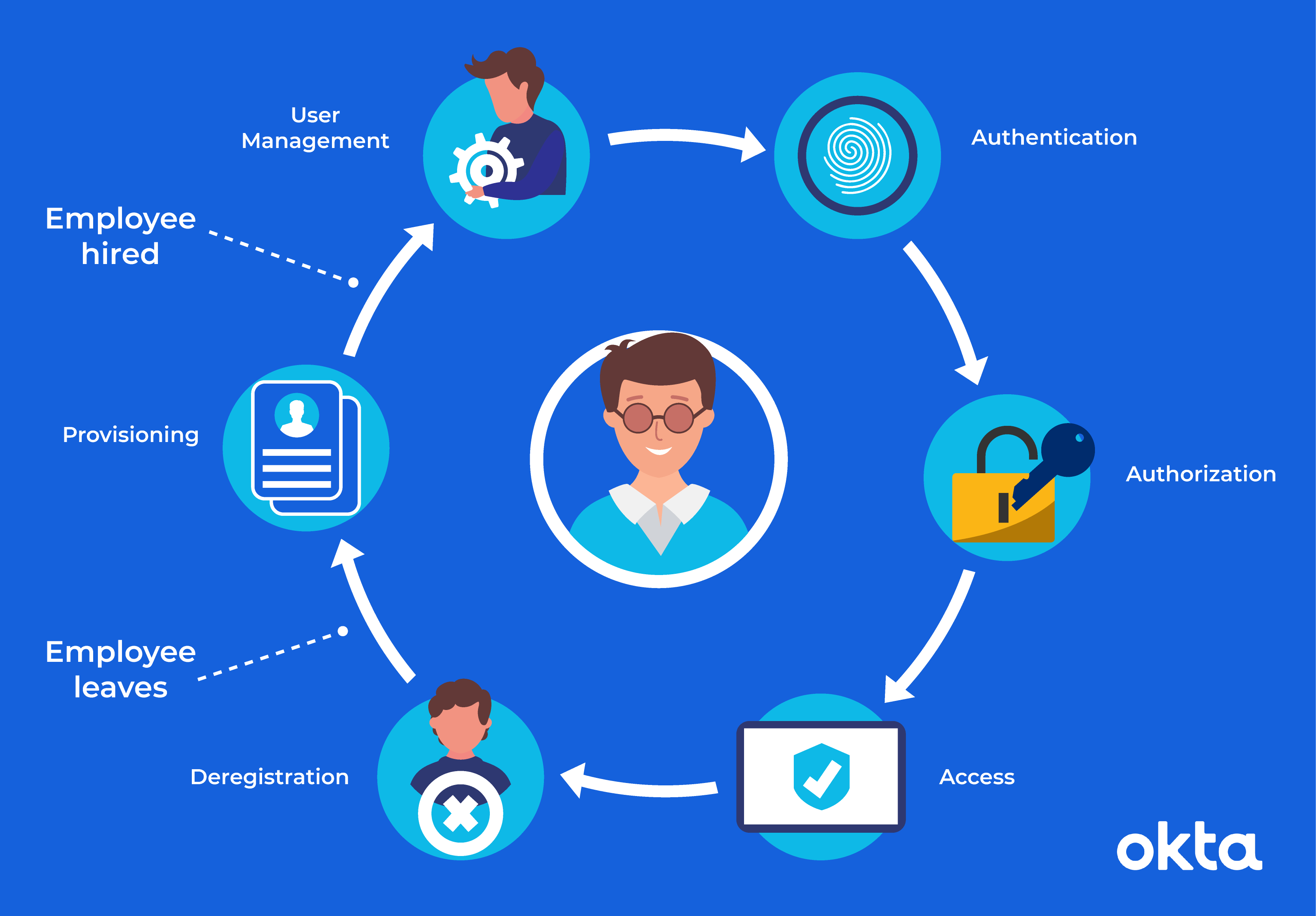
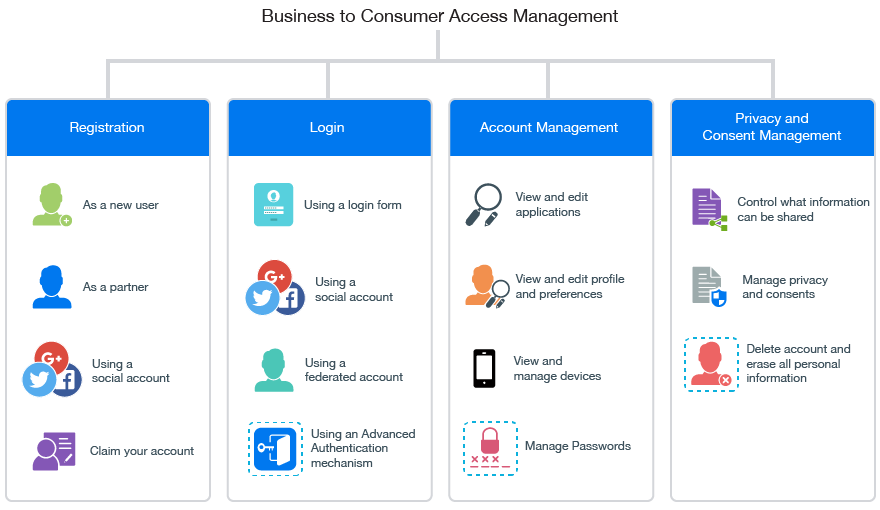
Entitlement Management Systems are sophisticated software solutions that govern and control user access rights within an organisation’s IT infrastructure. These systems enable businesses to define, manage, and enforce policies regarding who can access what information, under what circumstances, and for how long.
Key Benefits of Entitlement Management Systems:
- Enhanced Security: EMS help prevent unauthorised access to sensitive data by ensuring that only authorised users have the necessary permissions to view or modify specific information.
- Compliance: In industries with strict regulatory requirements such as healthcare or finance, EMS assist in maintaining compliance by providing detailed audit trails of user activities and access permissions.
- Efficiency: By automating user access management processes, EMS streamline workflows and reduce the burden on IT administrators, allowing them to focus on more strategic tasks.
- Risk Mitigation: With EMS in place, businesses can proactively identify potential security risks and vulnerabilities within their systems before they can be exploited by malicious actors.
Implementation Challenges:
While the benefits of Entitlement Management Systems are clear, implementing them effectively can pose certain challenges for organisations. Common challenges include defining granular access policies, integrating EMS with existing IT infrastructure, ensuring user adoption and compliance with security protocols, and managing the complexity of large-scale deployments.
The Future of Entitlement Management:
As cyber threats continue to evolve and become more sophisticated, the role of Entitlement Management Systems will only grow in importance. Future advancements in EMS technology may include AI-driven access control mechanisms, biometric authentication integration, enhanced anomaly detection capabilities, and seamless integration with cloud-based services.
In conclusion, Entitlement Management Systems are indispensable tools for modern businesses looking to safeguard their sensitive data assets while maintaining operational efficiency and regulatory compliance. By investing in robust EMS solutions tailored to their specific needs, organisations can stay ahead of evolving cyber threats and protect their most valuable resource – their data.
Maximising Security and Efficiency: The 7 Key Benefits of an Entitlement Management System
- Enhanced security by controlling user access to sensitive data
- Improved compliance with regulatory requirements through detailed access management
- Streamlined workflows and increased operational efficiency
- Proactive risk mitigation through identification of security vulnerabilities
- Automated user access management reduces administrative burden
- Customisable access policies for granular control over data accessibility
- Scalable solutions that can adapt to the evolving needs of businesses
Challenges of Entitlement Management Systems: Navigating Complex Implementation and Beyond
- Complex Implementation Process
- High Initial Costs
- User Resistance
- Maintenance Overhead
- Integration Issues
- Potential Performance Impact
- Overly Restrictive Policies
Enhanced security by controlling user access to sensitive data
One of the key benefits of an Entitlement Management System is its ability to enhance security by controlling user access to sensitive data. By defining and enforcing strict access policies, organisations can ensure that only authorised users have the necessary permissions to view or modify specific information. This proactive approach significantly reduces the risk of unauthorised access and data breaches, safeguarding sensitive data from internal and external threats. With granular control over user privileges, businesses can maintain a secure environment and protect their valuable assets from potential security vulnerabilities.
Improved compliance with regulatory requirements through detailed access management
One of the key advantages of implementing an Entitlement Management System is the significant improvement in compliance with regulatory requirements. By enforcing detailed access management policies, organisations can ensure that only authorised personnel have access to sensitive data, thus reducing the risk of non-compliance with industry regulations. This level of control and oversight provided by the system allows businesses to maintain a comprehensive audit trail of user activities, monitor access permissions in real-time, and demonstrate adherence to regulatory standards during audits. Overall, enhanced compliance through meticulous access management not only mitigates risks but also fosters trust with regulatory bodies and stakeholders.
Streamlined workflows and increased operational efficiency
One of the key advantages of implementing an Entitlement Management System is the ability to streamline workflows and enhance operational efficiency within an organisation. By automating user access management processes and defining clear access policies, businesses can reduce manual intervention, minimise errors, and expedite the granting or revocation of user permissions. This streamlined approach not only saves time and resources but also allows IT administrators to focus on more strategic tasks, ultimately improving overall operational productivity and effectiveness.
Proactive risk mitigation through identification of security vulnerabilities
One of the key advantages of implementing an Entitlement Management System is its ability to proactively mitigate risks by identifying security vulnerabilities within an organisation’s IT infrastructure. By continuously monitoring user access rights and activities, the system can detect potential weaknesses or suspicious behaviour that may indicate a security threat. This early detection allows businesses to address vulnerabilities before they can be exploited by cyber attackers, strengthening their overall security posture and reducing the likelihood of data breaches or other malicious incidents.
Automated user access management reduces administrative burden
Automated user access management offered by Entitlement Management Systems significantly reduces the administrative burden on IT teams. By automating the process of granting and revoking user access rights based on predefined policies, organisations can streamline their operations and free up valuable time for IT administrators to focus on more strategic tasks. This efficiency not only improves overall productivity but also minimises the risk of human errors in access control, ultimately enhancing the organisation’s security posture.
Customisable access policies for granular control over data accessibility
One of the key advantages of Entitlement Management Systems is their ability to offer customisable access policies, allowing organisations to exert granular control over data accessibility. By tailoring access policies to specific user roles or departments, businesses can ensure that only authorised individuals have access to sensitive information, while restricting unnecessary privileges. This level of granularity not only enhances security by minimising the risk of data breaches but also promotes compliance with regulatory requirements by enforcing strict access controls. Customisable access policies empower organisations to strike a balance between providing employees with the necessary resources to perform their duties effectively and safeguarding critical data assets from unauthorised access or misuse.
Scalable solutions that can adapt to the evolving needs of businesses
One significant advantage of Entitlement Management Systems is their scalability, allowing them to flexibly accommodate the changing requirements and growth of businesses over time. These solutions are designed to adapt to the evolving needs of organisations, whether it involves expanding user bases, integrating new systems, or adjusting security policies. By offering scalable capabilities, Entitlement Management Systems provide businesses with the flexibility to scale their access management processes efficiently and cost-effectively, ensuring that security measures remain robust and aligned with the dynamic nature of modern enterprises.
Complex Implementation Process
One notable drawback of Entitlement Management Systems is the complex implementation process they entail. Setting up an EMS can be a time-consuming endeavour that demands substantial IT resources. From defining intricate access policies to integrating the system with existing IT infrastructure, the implementation phase can pose challenges for organisations. The need for thorough planning, testing, and training further adds to the complexity, potentially leading to delays in deployment and increased resource allocation. The intricate nature of setting up an EMS underscores the importance of careful consideration and investment in order to navigate through the complexities effectively.
High Initial Costs
One significant drawback of Entitlement Management Systems is the high initial costs associated with acquiring and implementing them. Businesses considering the adoption of an EMS may face substantial upfront expenses, including investment in software licenses, comprehensive training programmes for staff members, and potentially necessary infrastructure upgrades to support the system. These initial financial outlays can pose a barrier for some organisations, particularly smaller businesses or those operating on tighter budgets, making the implementation of an EMS a challenging prospect despite its long-term benefits.
User Resistance
User resistance is a significant con of Entitlement Management Systems, as employees may push back against the changes imposed by such systems. This resistance can result in adoption challenges and potential disruptions to productivity within an organisation. Employees who are accustomed to certain access privileges or workflows may find it difficult to adjust to new restrictions or authentication processes enforced by an EMS. Overcoming user resistance through effective communication, training, and demonstrating the benefits of enhanced security and compliance is crucial to successfully implementing an EMS without causing undue friction in day-to-day operations.
Maintenance Overhead
One significant drawback of Entitlement Management Systems is the maintenance overhead they entail. Continuous upkeep of the system, which includes performing updates, conducting regular user access reviews, and making policy adjustments, can be a resource-intensive task for organisations. This ongoing maintenance requires dedicated time and effort from IT personnel to ensure that the system remains effective and aligned with the evolving needs of the business. The need for consistent monitoring and management of user access rights can add to the workload of IT teams, potentially leading to increased operational costs and complexities in maintaining the system’s efficiency over time.
Integration Issues
One significant drawback of Entitlement Management Systems is the potential for integration issues when implementing them alongside existing IT systems and applications. The process of integrating an EMS can be intricate and challenging, often necessitating customisation to guarantee smooth operation. Compatibility issues, data migration complexities, and the need to align access control policies across diverse platforms can all contribute to the complexity of integration. This hurdle may require additional time, resources, and expertise to overcome, posing a barrier to the efficient deployment of an EMS within an organisation’s IT infrastructure.
Potential Performance Impact
One significant drawback of Entitlement Management Systems is the potential performance impact they may have on accessing data. Depending on the scale of implementation and the complexity of access policies, an EMS could introduce latency or performance issues that hinder the seamless retrieval of information. This can be particularly problematic in environments where real-time data access is crucial, as delays or slowdowns in accessing data can impede business operations and user productivity. Organisations must carefully evaluate and optimise their Entitlement Management System to strike a balance between security and performance to minimise any adverse effects on operational efficiency.
Overly Restrictive Policies
One significant drawback of Entitlement Management Systems is the risk of implementing overly restrictive policies. When access policies are poorly configured within the EMS, it can result in unnecessary limitations on data access for users. This can lead to user frustration and hinder productivity as individuals may find themselves unable to access essential information required to perform their tasks efficiently. Striking the right balance between security and usability is crucial in ensuring that Entitlement Management Systems effectively protect sensitive data without impeding legitimate user activities.