The Importance of Access Lifecycle Management in IT Security
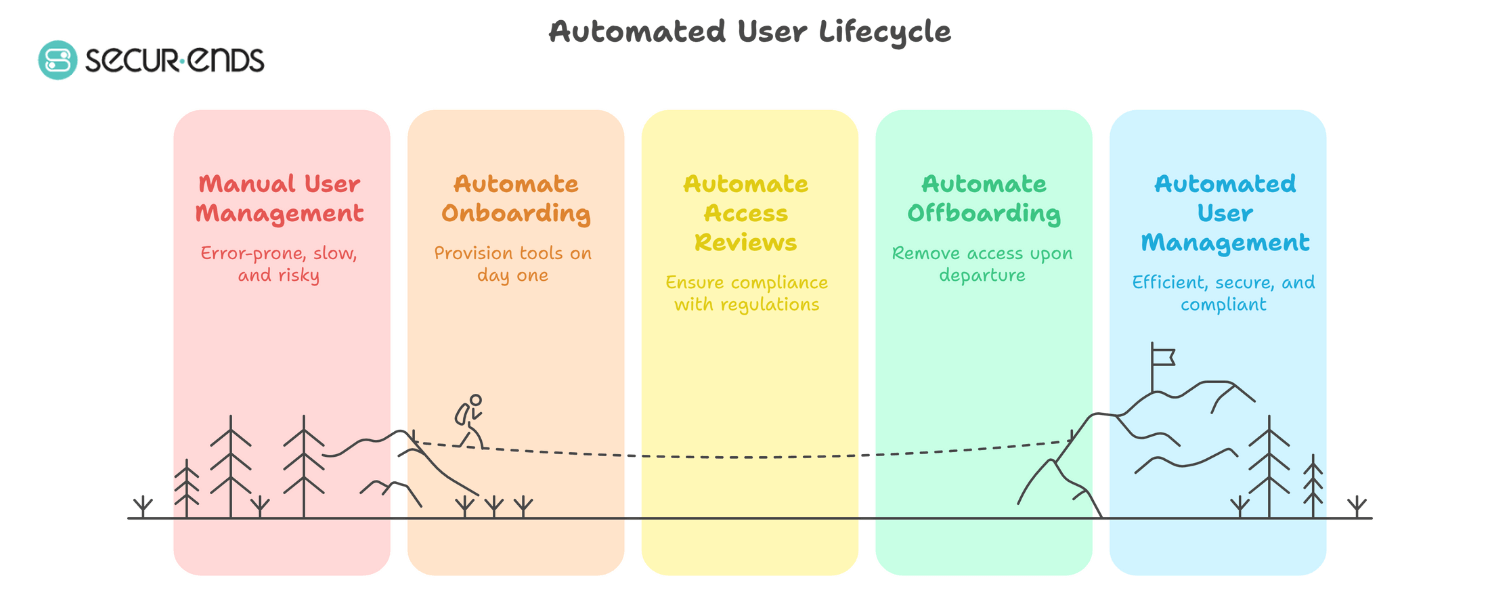
Access lifecycle management is a critical component of ensuring the security and integrity of an organisation’s IT infrastructure. It refers to the process of managing user access rights throughout their entire lifecycle within the system, from onboarding to offboarding. Effective access lifecycle management not only enhances security but also streamlines operational processes and ensures compliance with regulatory requirements.
Key Aspects of Access Lifecycle Management:
- Onboarding: When a new employee joins an organisation, access lifecycle management involves provisioning the necessary access rights based on their role and responsibilities. This step ensures that employees have the permissions required to perform their job functions effectively.
- Permissions Review: Regularly reviewing and updating user permissions is essential to prevent unauthorised access and reduce the risk of insider threats. Access lifecycle management includes periodic audits to verify that users have appropriate access levels.
- Offboarding: When an employee leaves the organisation, whether due to resignation or termination, it is crucial to promptly revoke their access rights to sensitive data and systems. Failure to deactivate accounts promptly can pose significant security risks.
- Compliance Management: Access lifecycle management plays a vital role in ensuring compliance with industry regulations and data protection laws. By maintaining accurate records of user access and permissions, organisations can demonstrate accountability and adherence to security standards.
The Benefits of Effective Access Lifecycle Management:
Implementing robust access lifecycle management practices offers several benefits for organisations:
- Enhanced Security: By controlling user access rights throughout their lifecycle, organisations can minimise the risk of data breaches and unauthorised activities.
- Improved Operational Efficiency: Streamlining the process of granting, reviewing, and revoking access rights can enhance operational efficiency and reduce administrative burdens.
- Audit Trail Visibility: Maintaining detailed records of user access activities enables organisations to track changes, investigate incidents, and demonstrate compliance during audits.
- Risk Mitigation: Proactively managing user access helps identify vulnerabilities and mitigate potential risks associated with excessive permissions or dormant accounts.
In conclusion, access lifecycle management is a fundamental aspect of IT security that should not be overlooked. By implementing effective processes for managing user access rights from onboarding to offboarding, organisations can strengthen their security posture, ensure regulatory compliance, and improve overall operational efficiency.
Five Essential Tips for Effective Access Lifecycle Management
- Regularly review and update user access permissions.
- Implement a clear access request and approval process.
- Automate provisioning and deprovisioning of user accounts.
- Monitor user activity for any unusual behaviour or access patterns.
- Provide regular training on access management best practices.
Regularly review and update user access permissions.
It is essential to regularly review and update user access permissions as part of effective access lifecycle management. By conducting periodic audits of user permissions, organisations can ensure that individuals have the appropriate level of access required to perform their job functions while minimising the risk of unauthorised access. This practice not only enhances security but also helps in maintaining compliance with regulatory requirements by keeping access permissions aligned with users’ roles and responsibilities within the organisation. Keeping user access permissions up-to-date is crucial for mitigating security risks and safeguarding sensitive data from potential threats.
Implement a clear access request and approval process.
To enhance access lifecycle management, it is crucial to implement a clear access request and approval process. By establishing structured procedures for requesting and granting access rights, organisations can ensure that permissions are assigned based on legitimate business needs and in accordance with established policies. This process helps prevent unauthorised access, reduces the risk of security breaches, and promotes accountability within the organisation. Additionally, a transparent request and approval workflow streamlines the provisioning of access rights, improves response times, and enhances overall operational efficiency.
Automate provisioning and deprovisioning of user accounts.
Automating the provisioning and deprovisioning of user accounts is a key tip in access lifecycle management that can significantly enhance security and operational efficiency. By implementing automated processes for granting and revoking access rights based on predefined rules and workflows, organisations can ensure timely provisioning for new employees and immediate deprovisioning for departing staff. Automation reduces the risk of human error, enforces consistency in access controls, and accelerates response times to access requests and changes. This proactive approach not only strengthens security by minimising the window of vulnerability but also streamlines administrative tasks, allowing IT teams to focus on more strategic initiatives.
Monitor user activity for any unusual behaviour or access patterns.
Monitoring user activity for any unusual behaviour or access patterns is a crucial aspect of access lifecycle management. By regularly reviewing user actions and access patterns, organisations can detect potential security threats such as insider attacks or unauthorised access attempts. Identifying deviations from normal user behaviour allows for timely intervention to prevent security breaches and safeguard sensitive data. Proactive monitoring not only enhances security but also helps in maintaining compliance with regulations by ensuring that access rights are used appropriately within the organisation’s IT environment.
Provide regular training on access management best practices.
It is essential to provide regular training on access management best practices as part of a comprehensive access lifecycle management strategy. By educating employees on the importance of managing access rights effectively, organisations can empower their workforce to make informed decisions when granting or revoking permissions. Training sessions can cover topics such as data security protocols, user authentication methods, and the risks associated with improper access management. Through ongoing education and awareness initiatives, employees can enhance their understanding of access control principles and contribute to maintaining a secure IT environment.