Top Identity and Access Management Companies
Identity and Access Management (IAM) is a crucial aspect of modern cybersecurity, enabling organisations to control and secure access to their systems and data. As the digital landscape continues to evolve, the need for robust IAM solutions has never been greater. Here are some of the top companies leading the way in providing cutting-edge IAM services:
Okta
Okta is a renowned IAM provider known for its cloud-based identity solutions. With a focus on user authentication, authorisation, and management, Okta offers a comprehensive platform that helps businesses streamline their security processes.
Microsoft Azure Active Directory
Microsoft’s Azure Active Directory is a widely used IAM solution that integrates seamlessly with Microsoft’s suite of products. With features such as single sign-on, multi-factor authentication, and identity governance, Azure AD is a popular choice for businesses leveraging Microsoft technologies.
IBM Security Identity Governance and Intelligence
IBM Security’s IAM offering combines identity governance with intelligence capabilities to provide organisations with advanced insights into their access controls. With features like role-based access control and risk assessment tools, IBM Security helps businesses enhance their security posture.
Ping Identity
Ping Identity specialises in providing IAM solutions that focus on secure access for customers, employees, partners, and devices. Their platform offers features such as single sign-on, multi-factor authentication, and API security to help businesses protect their digital assets.
ForgeRock
ForgeRock offers a comprehensive IAM platform designed to address the challenges of modern digital identity management. With capabilities for customer identity management, IoT security, and consent management, ForgeRock helps businesses build trusted relationships with their users.
These are just a few of the top companies at the forefront of identity and access management today. By partnering with these industry leaders, organisations can strengthen their security posture and ensure that only authorised users have access to critical resources.
Key Insights into Leading Identity and Access Management Companies: Answers to Frequently Asked Questions
- What is Identity and Access Management (IAM) and why is it important?
- How do top IAM companies help businesses secure their systems and data?
- What are the key features to look for in an IAM solution from a top company?
- Can IAM solutions integrate with existing IT infrastructure and applications?
- How do IAM companies address compliance requirements such as GDPR or HIPAA?
- What are the benefits of using cloud-based IAM solutions from top providers?
- How can IAM solutions enhance user experience while maintaining security?
- What sets the top IAM companies apart from other providers in terms of innovation and reliability?
What is Identity and Access Management (IAM) and why is it important?
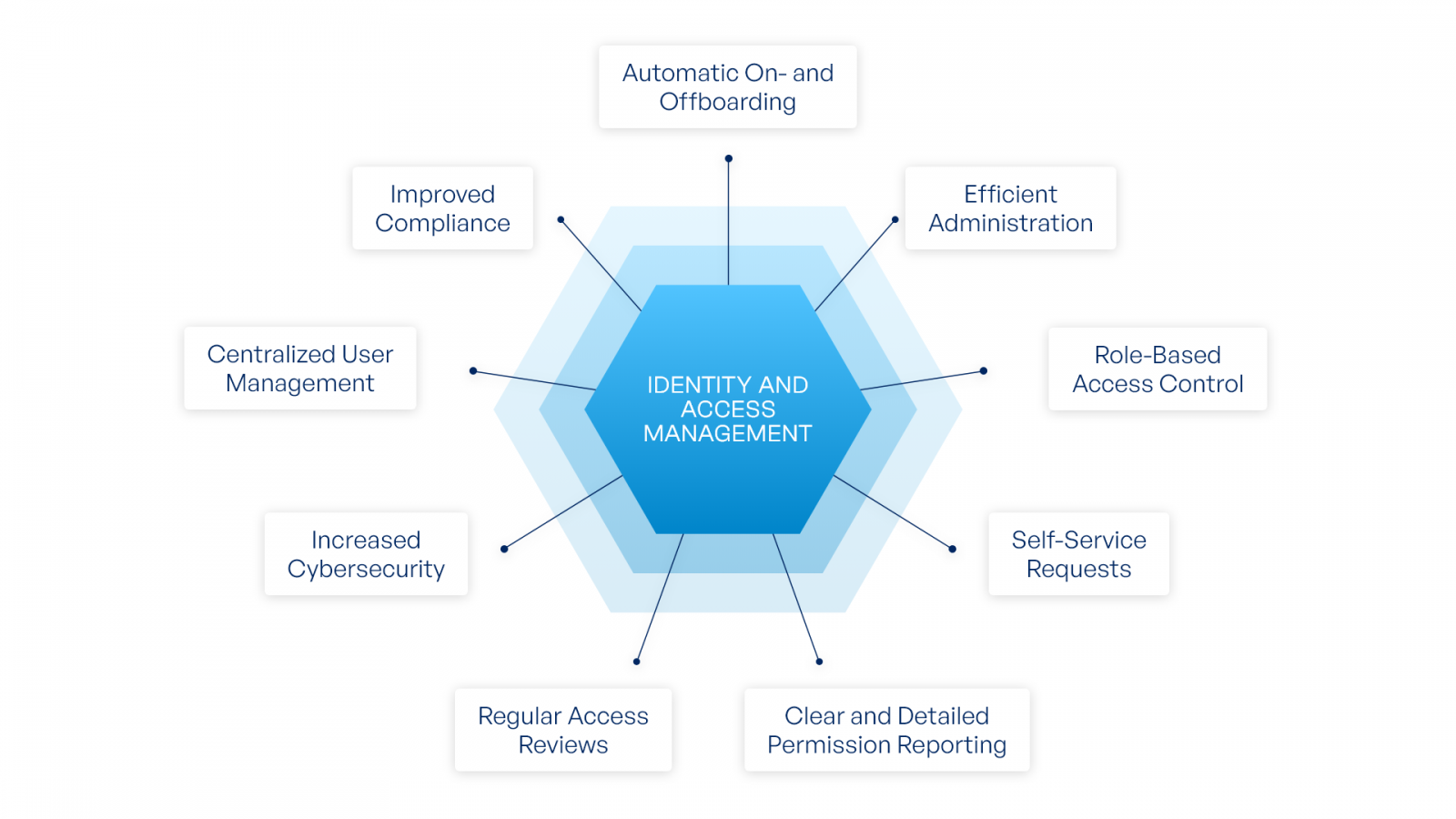
Identity and Access Management (IAM) is a critical component of cybersecurity that focuses on managing and controlling user identities and their access to digital resources within an organisation. IAM solutions encompass processes, technologies, and policies that ensure only authorised individuals can access specific systems or data. This is achieved through user authentication, authorisation, and management, which help prevent unauthorised access, reduce security risks, and maintain compliance with regulations. IAM plays a vital role in protecting sensitive information, safeguarding against data breaches, and enhancing overall cybersecurity posture for businesses of all sizes. By implementing robust IAM practices, organisations can effectively manage user identities, streamline access control processes, and mitigate potential security threats in today’s increasingly interconnected digital environment.
How do top IAM companies help businesses secure their systems and data?
Top IAM companies play a vital role in helping businesses secure their systems and data by providing advanced identity and access management solutions. These companies offer a range of tools and services that enable organisations to control user access, authenticate identities, and manage permissions effectively. By implementing robust IAM solutions, businesses can enforce security policies, ensure compliance with regulations, and mitigate the risk of unauthorised access to sensitive information. Top IAM companies also help streamline user provisioning processes, enable secure single sign-on experiences, and offer multi-factor authentication options to enhance overall security posture. With their expertise and innovative technologies, top IAM companies empower businesses to protect their digital assets and safeguard against evolving cybersecurity threats.
What are the key features to look for in an IAM solution from a top company?
When evaluating an IAM solution from a top company, there are several key features to consider. Firstly, robust authentication mechanisms such as multi-factor authentication and single sign-on are essential for ensuring secure access to systems and data. Additionally, comprehensive identity governance capabilities, including role-based access control and user provisioning, help organisations manage user permissions effectively. Integration capabilities with existing systems and applications, as well as support for compliance requirements such as GDPR and PCI DSS, are also crucial factors to look for in an IAM solution. A user-friendly interface and scalability to accommodate growing business needs further distinguish top IAM solutions from the rest.
Can IAM solutions integrate with existing IT infrastructure and applications?
IAM solutions are designed to seamlessly integrate with existing IT infrastructure and applications, making them a valuable asset for organisations seeking to enhance their security posture. By leveraging IAM platforms from top companies in the industry, businesses can ensure that their access management processes align with their current systems and applications. These solutions offer flexible integration capabilities, allowing for seamless connectivity with a wide range of technologies and protocols. Whether it’s cloud-based services, on-premises applications, or hybrid environments, IAM solutions can adapt to meet the unique needs of each organisation, providing a secure and efficient access management framework across the board.
How do IAM companies address compliance requirements such as GDPR or HIPAA?
Identity and Access Management (IAM) companies play a crucial role in helping organisations address compliance requirements such as GDPR or HIPAA. To ensure adherence to these regulations, IAM companies implement robust security measures within their solutions. For GDPR compliance, IAM providers often offer features like data encryption, user consent management, and audit trails to track access to personal data. Similarly, for HIPAA compliance, IAM solutions incorporate strong authentication methods, access controls, and activity monitoring to safeguard sensitive healthcare information. By integrating these compliance-focused features into their platforms, IAM companies assist organisations in meeting the stringent data protection standards mandated by GDPR and HIPAA.
What are the benefits of using cloud-based IAM solutions from top providers?
Cloud-based IAM solutions from top providers offer a myriad of benefits for organisations looking to enhance their security posture and streamline access management processes. One key advantage is the scalability and flexibility that cloud-based solutions provide, allowing businesses to easily adapt to changing user needs and organisational requirements. Additionally, these solutions often come with built-in security features such as multi-factor authentication and threat detection, helping to safeguard sensitive data and mitigate cybersecurity risks. Cloud-based IAM solutions also offer improved user experience through features like single sign-on and self-service capabilities, increasing productivity and reducing administrative burden. By leveraging the expertise of top providers in the field, organisations can benefit from cutting-edge technology, regular updates, and reliable support to ensure their IAM infrastructure remains robust and effective in the face of evolving threats.
How can IAM solutions enhance user experience while maintaining security?
IAM solutions play a pivotal role in enhancing user experience while maintaining robust security measures. By implementing features such as single sign-on (SSO) and multi-factor authentication (MFA), IAM solutions streamline the login process for users, reducing the need to remember multiple passwords and improving overall accessibility. Additionally, role-based access control (RBAC) ensures that users are granted appropriate permissions based on their roles within the organisation, enhancing efficiency and productivity. Furthermore, user-friendly interfaces and self-service options empower users to manage their own access rights, leading to a more seamless and personalised experience. By balancing convenience with stringent security protocols, IAM solutions create a harmonious environment where users can navigate systems effortlessly while safeguarding sensitive data from potential threats.
What sets the top IAM companies apart from other providers in terms of innovation and reliability?
When considering the top Identity and Access Management (IAM) companies, their distinction in terms of innovation and reliability becomes evident through their continuous commitment to staying ahead of evolving cybersecurity threats and industry trends. These companies invest significantly in research and development to introduce cutting-edge technologies that address the ever-changing landscape of digital security. Their innovative solutions not only anticipate potential risks but also provide proactive measures to safeguard sensitive data and ensure regulatory compliance. Moreover, the reliability of these top IAM companies lies in their proven track record of delivering robust IAM platforms that offer seamless integration, scalability, and user-friendly interfaces, empowering organisations to efficiently manage access controls while maintaining a high level of security. By prioritising innovation and reliability, these leading IAM providers set themselves apart as trusted partners in safeguarding digital identities and securing critical assets.