The Role of GRC Software in Ensuring Compliance and Risk Management: Insights from Gartner
In today’s complex business landscape, organisations face a myriad of challenges when it comes to governance, risk management, and compliance (GRC). To navigate these challenges effectively, many businesses are turning to GRC software solutions for assistance. According to Gartner, a leading research and advisory company, the adoption of GRC software is becoming increasingly crucial for businesses seeking to enhance their operational efficiency and mitigate risks.
What is GRC Software?
GRC software refers to a set of tools and technologies that help organisations streamline their governance, risk management, and compliance processes. These software solutions are designed to centralise data, automate workflows, and provide real-time insights into an organisation’s risk and compliance posture. By leveraging GRC software, businesses can proactively identify potential risks, ensure regulatory compliance, and make informed decisions to protect their assets.
The Benefits of GRC Software
One of the key advantages of implementing GRC software is its ability to integrate disparate functions within an organisation. By consolidating governance, risk management, and compliance activities onto a single platform, businesses can achieve greater visibility into their operations and improve collaboration across departments. This integrated approach enables organisations to identify interdependencies between different risk factors and compliance requirements more effectively.
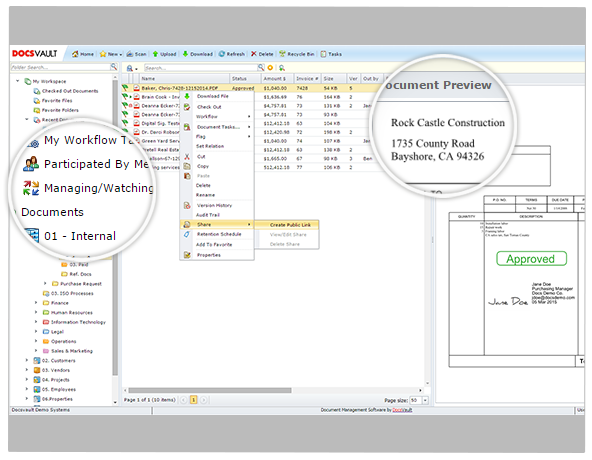
Furthermore, GRC software automates many manual processes associated with risk assessment, policy management, audit trails, and reporting. This automation not only saves time and resources but also reduces the likelihood of human error in critical compliance tasks. By leveraging data analytics capabilities embedded in GRC software solutions, organisations can gain valuable insights into emerging risks and trends that may impact their business operations.
Gartner’s Insights on GRC Software
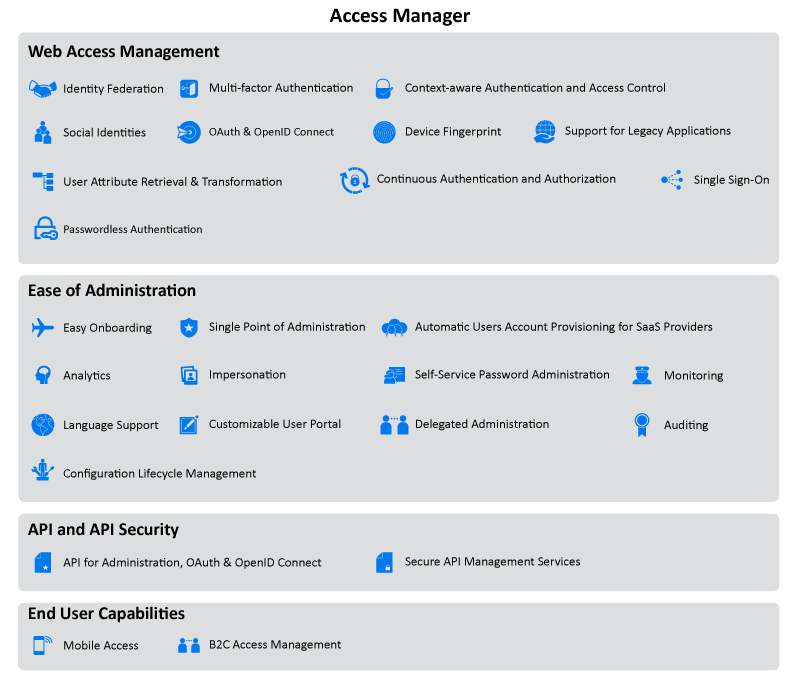
According to Gartner’s research findings, the adoption of GRC software is on the rise as businesses recognise the need for a more holistic approach to managing risks and ensuring compliance. Gartner highlights that effective GRC software should offer robust features such as configurable workflows, real-time monitoring capabilities, predictive analytics tools, and integration with other enterprise systems.
Gartner also emphasises the importance of selecting a GRC software solution that aligns with an organisation’s specific needs and industry requirements. Customisability and scalability are key factors that businesses should consider when evaluating different GRC software vendors. Additionally, Gartner recommends that organisations invest in training programmes to ensure that employees are proficient in using the selected GRC software effectively.
Conclusion
In conclusion, the adoption of GRC software is essential for modern businesses looking to stay ahead in an ever-changing regulatory environment. By leveraging advanced technologies offered by reputable vendors like those recognised by Gartner, organisations can enhance their risk management practices, achieve regulatory compliance more efficiently, and ultimately safeguard their reputation in the marketplace.
Essential Insights from Gartner: Addressing Key Questions on Selecting and Utilising GRC Software
- What criteria should I consider when selecting GRC software according to Gartner?
- How can GRC software help my organisation improve compliance with regulations?
- What are the key features that Gartner recommends looking for in GRC software?
- Is there a specific GRC software vendor recommended by Gartner for certain industries?
- What training or resources does Gartner suggest for maximising the benefits of GRC software?
- How does Gartner evaluate and rank different GRC software solutions in their reports?
What criteria should I consider when selecting GRC software according to Gartner?
When selecting GRC software according to Gartner’s recommendations, several key criteria should be considered to ensure that the chosen solution meets the specific needs of your organisation. Gartner advises businesses to evaluate factors such as the software’s configurability to align with unique business processes, its real-time monitoring capabilities for proactive risk management, its predictive analytics tools for identifying emerging risks, and its integration capabilities with other enterprise systems. Customisability and scalability are also crucial considerations, as well as the availability of training programmes to ensure that users can effectively utilise the selected GRC software. By carefully assessing these criteria in line with Gartner’s guidelines, organisations can make informed decisions when choosing GRC software that best suits their governance, risk management, and compliance requirements.
How can GRC software help my organisation improve compliance with regulations?
Implementing GRC software can significantly enhance your organisation’s compliance with regulations by providing a centralised platform to manage and monitor regulatory requirements efficiently. GRC software streamlines compliance processes, automates tasks such as policy management and audit trails, and offers real-time insights into your organisation’s adherence to regulations. By leveraging the capabilities of GRC software recommended by Gartner, your organisation can proactively identify compliance gaps, track regulatory changes, and ensure timely responses to evolving requirements. This proactive approach not only reduces the risk of non-compliance but also enhances operational efficiency and transparency in meeting regulatory obligations.
What are the key features that Gartner recommends looking for in GRC software?
When considering GRC software solutions, Gartner recommends looking for key features that can enhance governance, risk management, and compliance practices within an organisation. Some of the essential features highlighted by Gartner include configurable workflows that align with specific business processes, real-time monitoring capabilities to track risk indicators promptly, predictive analytics tools for proactive risk identification, and seamless integration with existing enterprise systems to ensure data consistency. Gartner also emphasises the importance of customisability and scalability in GRC software to accommodate evolving business needs and industry requirements effectively. By prioritising these key features in their selection process, organisations can choose GRC software solutions that offer comprehensive functionality and support their long-term risk management objectives.
Is there a specific GRC software vendor recommended by Gartner for certain industries?
When it comes to the question of whether Gartner recommends a specific GRC software vendor for certain industries, the answer is not straightforward. Gartner’s evaluations and recommendations are typically based on a vendor’s overall capabilities, product features, and market performance rather than industry-specific preferences. While Gartner may highlight vendors that excel in particular industries due to their tailored solutions or domain expertise, the choice of GRC software vendor ultimately depends on an organisation’s unique requirements, compliance needs, and risk management objectives. It is essential for businesses to conduct thorough research and engage in vendor evaluations to identify the best-fit solution that aligns with their industry-specific challenges and regulatory demands.
What training or resources does Gartner suggest for maximising the benefits of GRC software?
When it comes to maximising the benefits of GRC software, Gartner suggests that organisations invest in comprehensive training programs for their employees. These training initiatives should focus on building proficiency in using GRC software effectively and understanding its full capabilities. By providing employees with the necessary skills and knowledge, businesses can ensure that their teams are equipped to leverage the features of GRC software optimally. Additionally, Gartner recommends accessing resources such as vendor-provided documentation, online tutorials, and user forums to deepen understanding and address any challenges that may arise during the implementation and usage of GRC software.
How does Gartner evaluate and rank different GRC software solutions in their reports?
Gartner evaluates and ranks different GRC software solutions in their reports through a rigorous and systematic process that involves various criteria. Gartner analysts assess GRC software based on factors such as functionality, usability, performance, scalability, innovation, and market presence. They conduct in-depth research, gather feedback from users and vendors, analyse product demonstrations, and consider customer reviews to provide an objective evaluation of each solution. Gartner’s Magic Quadrant methodology is widely recognised for categorising vendors into Leaders, Challengers, Visionaries, and Niche Players based on their ability to execute and completeness of vision. By utilising this comprehensive approach, Gartner offers valuable insights to businesses seeking to make informed decisions when selecting the most suitable GRC software for their specific needs.