The Importance of HID Identity and Access Management
In today’s digital age, where data breaches and cyber threats are on the rise, ensuring the security of your organisation’s sensitive information is paramount. One crucial aspect of safeguarding your data is implementing robust identity and access management (IAM) solutions. HID Global, a leading provider of secure identity solutions, offers advanced IAM technologies that help organisations protect their assets and mitigate security risks.
What is HID Identity and Access Management?
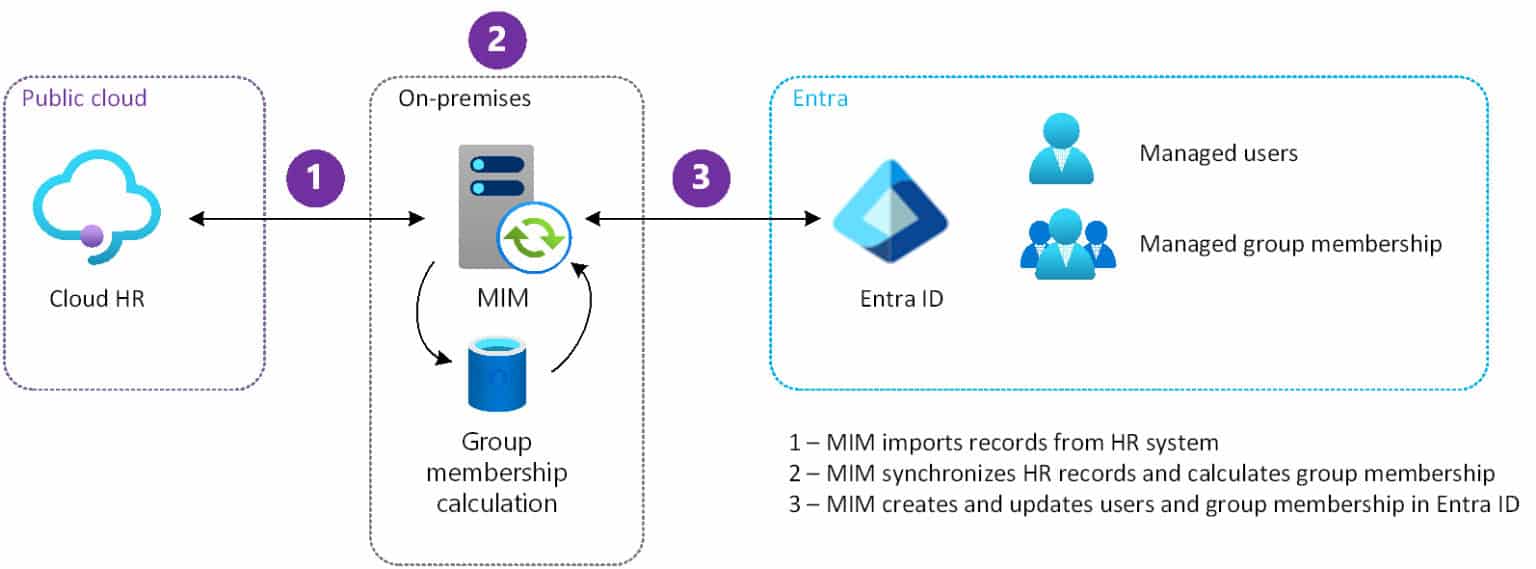
HID IAM solutions encompass a range of tools and technologies that enable organisations to manage user identities, control access to systems and resources, and ensure compliance with security policies. By centralising the management of user identities and access rights, HID IAM solutions help prevent unauthorised access to sensitive data and reduce the risk of insider threats.
The Benefits of HID IAM Solutions
Implementing HID IAM solutions offers numerous benefits to organisations, including:
- Enhanced Security: By enforcing strong authentication measures and access controls, HID IAM solutions help protect against unauthorised access and data breaches.
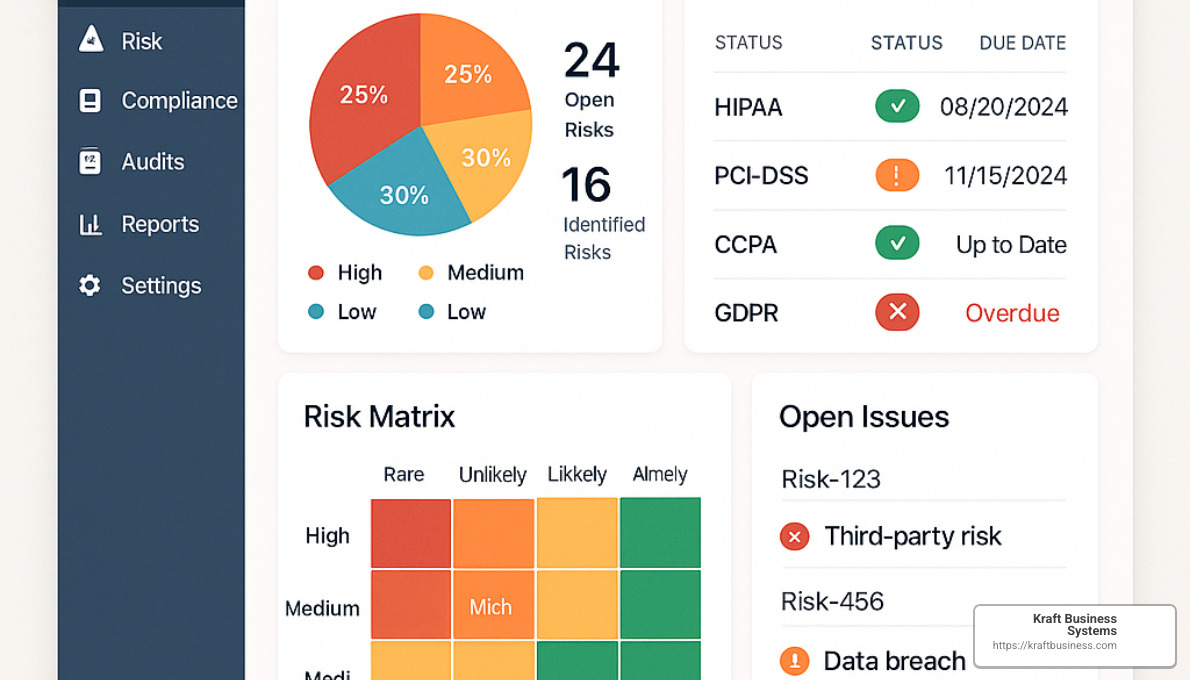
- Improved Compliance: HID IAM solutions assist organisations in meeting regulatory requirements by providing detailed audit trails and ensuring adherence to security policies.
- Increased Efficiency: Centralised identity management streamlines user provisioning and deprovisioning processes, reducing administrative overhead and enhancing operational efficiency.
- User Convenience: With single sign-on capabilities and self-service options, HID IAM solutions make it easier for users to access the resources they need securely.
HID Global’s Approach to Identity and Access Management
HID Global offers a comprehensive suite of IAM solutions tailored to meet the unique security needs of modern organisations. From multi-factor authentication tools to identity governance platforms, HID Global provides cutting-edge technologies that empower organisations to secure their digital assets effectively.
The Future of Identity and Access Management
As cyber threats continue to evolve, the importance of robust identity and access management practices will only grow. Organisations that invest in advanced IAM solutions such as those offered by HID Global can stay ahead of emerging threats and protect their critical information assets effectively.
In conclusion, implementing HID Identity and Access Management solutions is essential for safeguarding your organisation’s data, ensuring compliance with regulations, and mitigating security risks. By partnering with a trusted provider like HID Global, you can take proactive steps towards enhancing your cybersecurity posture in an increasingly digital world.
Understanding HID Identity and Access Management: Key FAQs for Organisations
- What is HID Identity and Access Management?
- Why is HID Identity and Access Management important for organisations?
- How does HID Identity and Access Management enhance cybersecurity?
- What are the key features of HID IAM solutions?
- Can HID IAM solutions help with regulatory compliance?
- How does HID Global approach identity governance in IAM?
- What are the benefits of implementing HID multi-factor authentication?
- How can organisations streamline user access management with HID IAM solutions?
What is HID Identity and Access Management?
HID Identity and Access Management (IAM) refers to a comprehensive set of tools and technologies designed to manage user identities, control access to systems and resources, and enforce security policies within an organisation. HID IAM solutions play a crucial role in safeguarding sensitive data by centralising the management of user identities, implementing strong authentication measures, and ensuring compliance with regulatory requirements. By providing a secure framework for managing user access rights and permissions, HID IAM solutions help prevent unauthorised access to critical information assets and mitigate the risk of insider threats. In essence, HID IAM is a vital component of modern cybersecurity strategies aimed at protecting organisational data from evolving cyber threats.
Why is HID Identity and Access Management important for organisations?
HID Identity and Access Management is crucial for organisations due to its pivotal role in enhancing cybersecurity measures and safeguarding sensitive data. By implementing HID IAM solutions, organisations can effectively manage user identities, control access to critical systems and resources, and enforce security policies. This not only helps prevent unauthorised access and data breaches but also ensures compliance with regulatory requirements. HID IAM solutions streamline identity management processes, improve operational efficiency, and provide a robust defence against evolving cyber threats. In today’s digital landscape, where data security is paramount, investing in HID Identity and Access Management is essential for organisations looking to protect their assets and maintain a strong security posture.
How does HID Identity and Access Management enhance cybersecurity?
HID Identity and Access Management plays a crucial role in enhancing cybersecurity by providing organisations with robust tools and technologies to safeguard their digital assets. By centralising the management of user identities, enforcing strong authentication measures, and controlling access to systems and resources, HID IAM solutions help prevent unauthorised access and reduce the risk of data breaches. Additionally, HID IAM solutions offer detailed audit trails, compliance monitoring capabilities, and streamlined user provisioning processes, all of which contribute to a more secure and resilient cybersecurity posture. By leveraging HID Identity and Access Management solutions, organisations can proactively mitigate security risks, ensure regulatory compliance, and protect their critical information assets in an increasingly interconnected digital landscape.
What are the key features of HID IAM solutions?
When exploring HID Identity and Access Management solutions, it is essential to understand the key features that set them apart. HID IAM solutions offer a range of advanced features, including robust multi-factor authentication capabilities, centralised identity management for streamlined user provisioning and deprovisioning, comprehensive access controls to enforce security policies, detailed audit trails for compliance monitoring, and user-friendly self-service options for enhanced convenience. These key features work together to provide organisations with a secure and efficient IAM solution that helps protect sensitive data, mitigate security risks, and ensure regulatory compliance.
Can HID IAM solutions help with regulatory compliance?
HID Identity and Access Management (IAM) solutions play a crucial role in helping organisations achieve regulatory compliance. By providing robust identity management, access control, and audit capabilities, HID IAM solutions enable organisations to enforce security policies, track user activities, and generate detailed reports for compliance purposes. With features such as multi-factor authentication and identity governance, HID IAM solutions assist organisations in meeting regulatory requirements effectively. By implementing HID IAM solutions, organisations can enhance their security posture, demonstrate compliance with regulations, and mitigate the risk of data breaches.
How does HID Global approach identity governance in IAM?
HID Global adopts a comprehensive approach to identity governance within its Identity and Access Management (IAM) solutions. By focusing on identity governance, HID Global ensures that organisations have the necessary tools and processes to manage user identities effectively, control access permissions, and enforce security policies. Through robust identity governance features such as role-based access control, segregation of duties, and automated provisioning workflows, HID Global empowers organisations to maintain a secure and compliant environment. By providing visibility into user access rights and activities, HID Global’s identity governance capabilities enable organisations to mitigate risks, enhance operational efficiency, and meet regulatory requirements effectively within their IAM framework.
What are the benefits of implementing HID multi-factor authentication?
Implementing HID multi-factor authentication offers a range of benefits that enhance the security posture of organisations. By requiring users to provide multiple forms of verification, such as passwords, biometrics, or smart cards, HID multi-factor authentication significantly strengthens access controls and mitigates the risk of unauthorised access. This added layer of security not only safeguards sensitive data and resources but also helps organisations comply with regulatory requirements. Additionally, HID multi-factor authentication enhances user convenience by providing secure access to systems and applications while minimising the burden of remembering complex passwords. Overall, the implementation of HID multi-factor authentication is a proactive step towards bolstering cybersecurity defences and protecting critical assets from evolving threats.
How can organisations streamline user access management with HID IAM solutions?
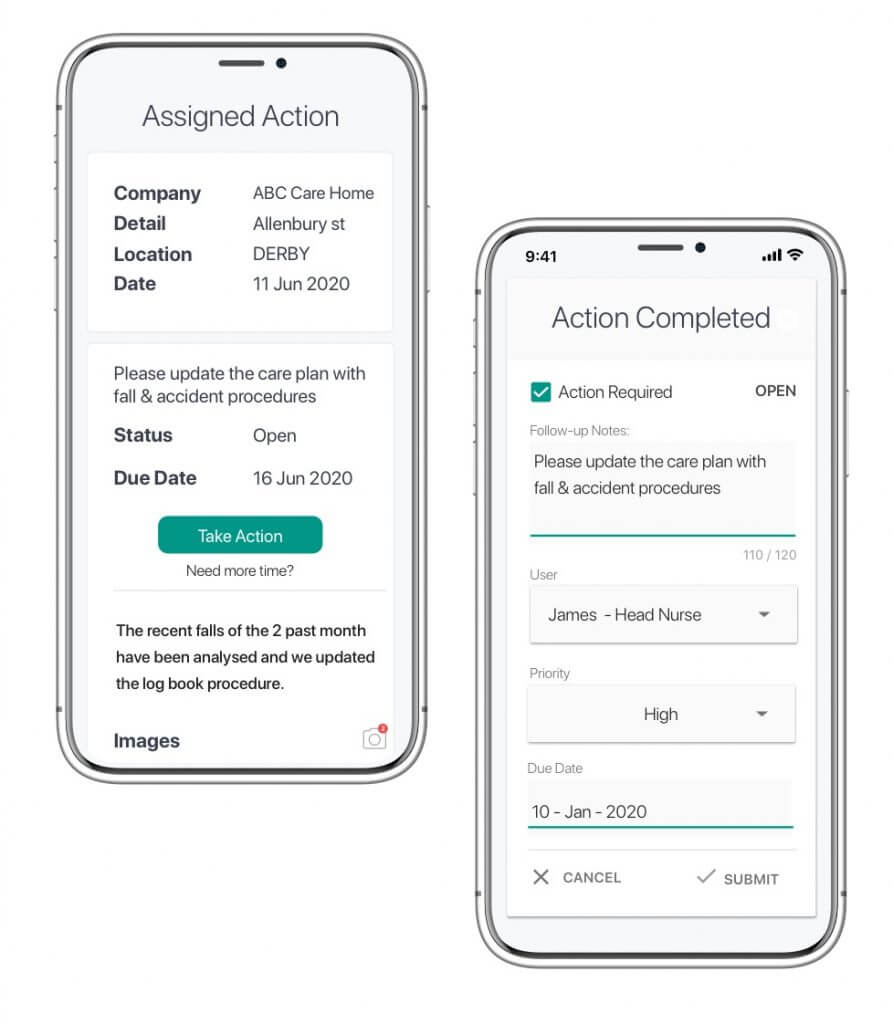
Organisations can streamline user access management with HID IAM solutions by leveraging the centralised identity management capabilities offered by HID Global. By consolidating user identities and access rights into a single platform, organisations can simplify the process of provisioning and deprovisioning user accounts, ensuring that access privileges are granted and revoked efficiently. Additionally, HID IAM solutions provide tools for enforcing strong authentication measures, such as multi-factor authentication, to enhance security while offering user-friendly features like single sign-on for a seamless access experience. With HID IAM solutions, organisations can achieve greater operational efficiency, improved security posture, and enhanced control over user access management processes.