Best Active Directory Auditing Tools
The Best Active Directory Auditing Tools
Active Directory auditing is a critical aspect of maintaining the security and integrity of your IT infrastructure. By monitoring and tracking changes within your Active Directory environment, you can detect suspicious activities, ensure compliance with regulations, and prevent potential security breaches. To help you effectively audit your Active Directory, here are some of the best tools available:
SolarWinds Security Event Manager
SolarWinds Security Event Manager offers comprehensive auditing capabilities for Active Directory. It provides real-time monitoring, alerting, and reporting features to help you track user activities, group changes, and policy modifications effectively.
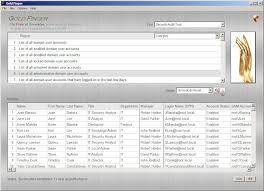
ManageEngine ADAudit Plus
ManageEngine ADAudit Plus is a robust solution that offers detailed reports on all changes made in your Active Directory environment. It allows you to monitor user logon activities, file access events, and group policy modifications to enhance security and compliance.
Netwrix Auditor for Active Directory
Netwrix Auditor for Active Directory is a powerful tool that provides visibility into all changes happening in your Active Directory infrastructure. It offers pre-defined reports, alerts on critical events, and forensic analysis capabilities to help you maintain a secure and compliant environment.
LepideAuditor for Active Directory
LepideAuditor for Active Directory is a user-friendly auditing tool that enables you to track changes in real-time and generate customised reports for compliance audits. It helps you identify insider threats, monitor privileged user activities, and streamline IT operations efficiently.
Quest Change Auditor for Active Directory
Quest Change Auditor for Active Directory delivers comprehensive auditing capabilities to help you monitor all changes in your Active Directory environment effectively. It offers detailed reports on user activity, permission changes, and security events to enhance visibility and control over your IT infrastructure.
Choosing the right active directory auditing tool is essential for maintaining the security and compliance of your organisation’s IT environment. Consider the features offered by each tool mentioned above to select the one that best fits your requirements and helps you achieve a robust auditing strategy.
Top 9 Benefits of Leading Active Directory Auditing Tools: Enhancing Security and Compliance
- Real-time monitoring of user activities
- Comprehensive reporting on changes within Active Directory
- Alerting features to notify of suspicious events
- Enhanced security through tracking policy modifications
- Facilitates compliance with regulatory requirements
- Forensic analysis capabilities for investigating incidents
- User-friendly interfaces for easy configuration and management
- Customisable reports tailored to specific auditing needs
- Integration with other security tools for a holistic approach
Challenges of Top Active Directory Auditing Tools: Costs, Complexity, and Scalability Issues
- Steep learning curve for beginners due to the complexity of features.
- Some tools may be costly, especially for small businesses with budget constraints.
- Integration with existing IT infrastructure may require additional configuration and resources.
- Certain tools may lack customisation options for specific auditing needs.
- Maintenance and updates can be time-consuming, affecting operational efficiency.
- Limited scalability in terms of handling a large volume of audit data and user activities.
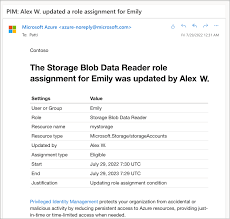
Real-time monitoring of user activities
Real-time monitoring of user activities is a crucial advantage offered by the best Active Directory auditing tools. This feature allows organisations to track and analyse user interactions within the Active Directory environment as they occur, providing immediate visibility into any suspicious or unauthorised behaviour. By monitoring user activities in real-time, IT administrators can swiftly detect potential security threats, identify anomalous patterns, and take proactive measures to mitigate risks effectively. This capability enhances overall security posture, enables rapid incident response, and helps maintain the integrity of the IT infrastructure in a dynamic and evolving threat landscape.
Comprehensive reporting on changes within Active Directory
Comprehensive reporting on changes within Active Directory is a crucial advantage offered by the best active directory auditing tools. These tools provide detailed insights into all modifications, user activities, group policy changes, and security events occurring within the Active Directory environment. By generating comprehensive reports, organisations can easily track and analyse every change made, helping them to identify potential security threats, ensure compliance with regulations, and maintain the integrity of their IT infrastructure. This level of visibility and transparency is essential for effective auditing and proactive security management in today’s dynamic digital landscape.
Alerting features to notify of suspicious events
Effective active directory auditing tools offer alerting features that play a crucial role in notifying administrators of suspicious events within the Active Directory environment. These alerting capabilities enable real-time monitoring and immediate detection of potentially harmful activities, such as unauthorised access attempts, unusual user behaviour, or policy violations. By promptly alerting administrators to such events, these tools empower them to take swift action to investigate and mitigate security threats, ensuring the integrity and confidentiality of the organisation’s IT infrastructure.
Enhanced security through tracking policy modifications
Enhanced security through tracking policy modifications is a crucial benefit offered by the best Active Directory auditing tools. By monitoring and recording changes made to group policies, access controls, and other security settings within the Active Directory environment, organisations can effectively identify any unauthorised alterations that could pose a security risk. This proactive approach not only helps in detecting potential threats promptly but also ensures that compliance with security policies and regulations is maintained. Through detailed tracking of policy modifications, these auditing tools play a vital role in strengthening the overall security posture of an organisation’s IT infrastructure.
Facilitates compliance with regulatory requirements
Implementing the best Active Directory auditing tools can significantly facilitate compliance with regulatory requirements. These tools offer comprehensive monitoring and reporting capabilities that help organisations track user activities, detect unauthorised changes, and ensure data integrity within their IT infrastructure. By maintaining detailed audit logs and generating compliance reports, these tools assist in demonstrating adherence to regulatory standards such as GDPR, HIPAA, or PCI DSS. This proactive approach not only helps in meeting legal obligations but also enhances overall data security and governance practices within the organisation.
Forensic analysis capabilities for investigating incidents
Forensic analysis capabilities offered by the best Active Directory auditing tools play a crucial role in investigating security incidents and breaches effectively. These capabilities allow organisations to delve deep into the details of any suspicious activity, track the root cause of security incidents, and gather evidence for further analysis. By providing a comprehensive view of user actions, system changes, and access permissions, Active Directory auditing tools with forensic analysis features empower IT teams to identify and respond to security threats promptly, ultimately enhancing the overall resilience of the IT infrastructure.
User-friendly interfaces for easy configuration and management
User-friendly interfaces offered by the best Active Directory auditing tools facilitate seamless configuration and management processes. These intuitive interfaces empower IT administrators to set up auditing parameters efficiently and navigate through monitoring functionalities with ease. By providing a straightforward user experience, these tools enable quick access to critical features, simplifying the task of monitoring user activities, tracking changes, and generating reports. The user-friendly nature of these interfaces enhances productivity and ensures that organisations can effectively manage their Active Directory auditing tasks without unnecessary complexity.
Customisable reports tailored to specific auditing needs
Customisable reports tailored to specific auditing needs are a key advantage of the best Active Directory auditing tools. By allowing users to create reports that align with their unique requirements, these tools enable organisations to focus on the most critical aspects of their Active Directory environment. Whether it’s tracking user activities, monitoring policy changes, or ensuring compliance with industry regulations, customisable reports provide valuable insights and actionable data that help enhance security, streamline operations, and demonstrate adherence to best practices. This flexibility empowers IT teams to efficiently address potential risks and make informed decisions based on the specific audit requirements of their organisation.
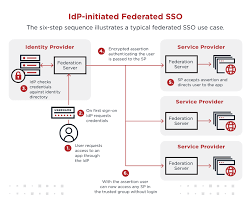
Effective Active Directory auditing tools offer a significant advantage through their integration with other security tools, enabling a holistic approach to IT security. By seamlessly integrating with complementary solutions such as SIEM platforms, threat intelligence feeds, and security information sources, these tools provide a comprehensive view of the entire security landscape. This integration allows for correlation of data across different systems, enhancing threat detection capabilities and facilitating a proactive response to potential security incidents. By adopting a holistic approach to security, organisations can strengthen their defences and better protect their Active Directory environment from evolving cyber threats.
Steep learning curve for beginners due to the complexity of features.
Navigating the realm of Active Directory auditing tools can present a significant challenge for beginners, primarily due to the steep learning curve resulting from the intricate nature of their features. The complexity of functionalities offered by these tools often requires a certain level of expertise and familiarity with IT auditing processes, making it daunting for newcomers to grasp and utilise them effectively. As a result, individuals embarking on their journey with Active Directory auditing may face hurdles in understanding and maximising the potential of these tools, necessitating dedicated time and effort to overcome the initial complexities and harness their full capabilities.
One significant drawback of utilising the best Active Directory auditing tools is the potential cost implications, which can be a challenge for small businesses operating under budget constraints. While these tools offer advanced features and robust security capabilities, their price tags may prove prohibitive for organisations with limited financial resources. Small businesses may find it difficult to justify the expense of investing in high-end auditing solutions, leading them to seek more affordable alternatives or compromise on the depth of auditing and monitoring they can achieve within their Active Directory environment.
Integration with existing IT infrastructure may require additional configuration and resources.
When considering the use of the best Active Directory auditing tools, a notable drawback is the potential need for additional configuration and resources to integrate them seamlessly with existing IT infrastructure. This con can lead to increased complexity in setup and maintenance processes, requiring careful planning and allocation of resources to ensure smooth integration. Organisations may need to invest time and effort in configuring the tools to work optimally with their specific network architecture, which could result in added costs and delays in implementation. It is crucial for businesses to evaluate this aspect carefully and be prepared for the necessary adjustments to effectively leverage the benefits of these auditing tools while minimising disruptions to their IT environment.
Certain active directory auditing tools may present a limitation in terms of customisation options for specific auditing needs. While many tools offer a wide range of features and functionalities, some organisations may find that their unique requirements cannot be fully addressed due to the lack of customisation capabilities in certain tools. This can result in difficulties in tailoring the auditing process to align with specific compliance regulations or internal security policies. Organisations seeking highly customised auditing solutions may need to carefully evaluate the available options to ensure that the chosen tool can adequately meet their individual auditing needs.
Maintenance and updates can be time-consuming, affecting operational efficiency.
Maintenance and updates of the best Active Directory auditing tools can present a significant challenge as they often require dedicated time and resources, impacting operational efficiency. Keeping the tools up-to-date with the latest security patches, feature enhancements, and compatibility updates can be a time-consuming task that diverts attention from core business activities. Moreover, the complexity of managing multiple tools and ensuring seamless integration with existing systems can further add to the maintenance burden. This con highlights the importance of careful planning and resource allocation to mitigate disruptions and maximise the effectiveness of Active Directory auditing processes.
Limited scalability in terms of handling a large volume of audit data and user activities.
One significant drawback of some of the best Active Directory auditing tools is their limited scalability when it comes to handling a large volume of audit data and user activities. As organisations grow in size and complexity, the sheer amount of data generated by user interactions within the Active Directory can overwhelm certain auditing tools, leading to performance issues and potential gaps in monitoring. This limitation can hinder the ability to effectively track and analyse all activities within the Active Directory environment, potentially compromising security and compliance efforts. Organizations looking to implement auditing tools should carefully consider scalability requirements to ensure they can accommodate future growth and maintain comprehensive visibility into their IT infrastructure.