The Importance of Directory Security in Safeguarding Your Data
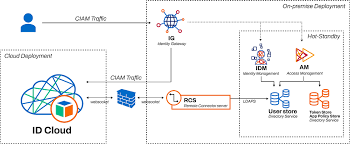
In today’s digital age, where data breaches and cyber threats are becoming increasingly prevalent, the security of your directories plays a crucial role in safeguarding sensitive information. A directory, such as Active Directory in a Windows environment or LDAP in a Linux environment, serves as a centralised database that stores user accounts, permissions, and other vital data for an organisation.
Ensuring the security of your directory is essential for protecting confidential information, preventing unauthorised access, and maintaining the integrity of your IT infrastructure. Here are some key reasons why directory security is paramount:
Access Control
Directory security enables you to control who has access to specific resources within your network. By implementing proper access controls and permissions, you can restrict users’ privileges based on their roles and responsibilities. This helps prevent unauthorised users from accessing sensitive data and minimises the risk of insider threats.
Data Protection
Directories store a wealth of critical information, including user credentials, group memberships, and organisational policies. Securing this data is vital to prevent identity theft, data loss, or manipulation by malicious actors. Robust directory security measures such as encryption and regular backups can help protect your data from cyber attacks and accidental deletions.
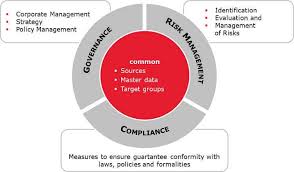
Compliance Requirements
Many industries have stringent regulatory requirements regarding data protection and privacy. Maintaining strong directory security not only helps you comply with industry standards such as GDPR or HIPAA but also demonstrates your commitment to safeguarding customer information. Failure to adhere to these regulations can result in hefty fines and reputational damage.
Business Continuity
In the event of a cyber incident or system failure, having secure directory services in place is crucial for ensuring business continuity. Regularly auditing your directories for vulnerabilities and suspicious activities can help you detect potential threats early on and mitigate risks before they escalate into full-blown security breaches.
Trust and Reputation
A strong emphasis on directory security not only protects your organisation’s assets but also enhances trust with customers, partners, and stakeholders. By demonstrating a commitment to safeguarding sensitive data through robust security practices, you can build a reputation as a reliable custodian of information and differentiate yourself from competitors.
In conclusion, prioritising directory security is fundamental in today’s digital landscape where cyber threats are ever-present. By investing in robust security measures, regular audits, employee training, and incident response plans, you can strengthen your defences against potential attacks and safeguard your organisation’s most valuable asset – its data.
Top 7 Essential Tips for Enhancing Directory Security
- Restrict access to directories by setting appropriate permissions.
- Regularly review and update directory access controls.
- Implement user authentication mechanisms to control access to directories.
- Encrypt sensitive data stored within directories.
- Monitor directory access logs for any suspicious activities.
- Backup important directories regularly to prevent data loss.
- Train employees on best practices for directory security.
Restrict access to directories by setting appropriate permissions.
To enhance directory security, it is crucial to restrict access to directories by setting appropriate permissions. By carefully managing permissions and access controls, organisations can ensure that only authorised users have the necessary privileges to view, modify, or delete sensitive data within directories. This proactive measure helps prevent unauthorised access and reduces the risk of data breaches, reinforcing the overall security posture of the IT infrastructure.
Regularly review and update directory access controls.
It is crucial to regularly review and update directory access controls to maintain a secure IT environment. By periodically assessing and adjusting user permissions, roles, and privileges within the directory, organisations can ensure that only authorised individuals have appropriate access to sensitive data and resources. This proactive approach helps mitigate the risk of unauthorised access, potential data breaches, and insider threats, ultimately strengthening the overall security posture of the system.
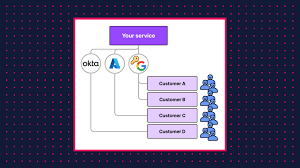
Implement user authentication mechanisms to control access to directories.
Implementing user authentication mechanisms is a crucial step in enhancing directory security. By controlling access to directories through authentication processes, organisations can ensure that only authorised users are granted entry to sensitive data and resources. User authentication adds an additional layer of protection, requiring users to verify their identities before accessing the directory, thus reducing the risk of unauthorised access and potential security breaches. This proactive approach helps organisations maintain a secure environment and safeguard critical information from malicious actors.
Encrypt sensitive data stored within directories.
To enhance directory security, it is advisable to encrypt sensitive data stored within directories. Encryption adds an extra layer of protection by converting data into a secure format that can only be accessed with the appropriate decryption key. By encrypting sensitive information such as user credentials, financial records, or personal details, organisations can mitigate the risk of unauthorised access and safeguard confidential data from potential cyber threats. Implementing encryption measures within directories helps ensure that even if a breach occurs, the stolen data remains unreadable and unusable to malicious actors, thereby strengthening overall data protection efforts.
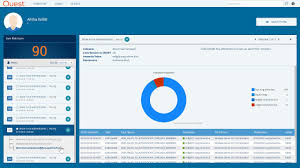
Monitor directory access logs for any suspicious activities.
Monitoring directory access logs for any suspicious activities is a crucial tip in maintaining robust directory security. By regularly reviewing access logs, organisations can proactively identify any unusual or unauthorised attempts to access sensitive data within the directory. This proactive approach allows for the prompt detection of potential security breaches or insider threats, enabling timely intervention to mitigate risks and safeguard the integrity of the directory. Regular monitoring of access logs not only enhances security posture but also demonstrates a commitment to vigilance and compliance with data protection regulations.
Backup important directories regularly to prevent data loss.
Backing up important directories regularly is a crucial tip to enhance directory security and prevent data loss. By creating routine backups of critical data stored within directories, organisations can mitigate the impact of potential cyber threats, system failures, or accidental deletions. Regular backups ensure that in the event of a security breach or data corruption, organisations can restore their information promptly and minimise downtime, thereby safeguarding valuable assets and maintaining business continuity effectively.
Train employees on best practices for directory security.
Training employees on best practices for directory security is a crucial step in safeguarding sensitive information within an organisation. By educating staff on the importance of maintaining strong passwords, recognising phishing attempts, and following proper access control protocols, businesses can empower their workforce to proactively protect valuable data stored in directories. Effective training not only enhances overall security posture but also cultivates a culture of vigilance and responsibility towards maintaining the integrity of directory systems.