The Power of One Identity Privileged Access Management (PAM) Solution
In today’s digital landscape, protecting sensitive data and critical systems from cyber threats is paramount. Organisations face the challenge of securing privileged accounts and managing access to ensure only authorised users have the right level of permissions. This is where One Identity’s Privileged Access Management (PAM) solution shines.
Enhanced Security
One Identity PAM provides a comprehensive set of tools to safeguard privileged accounts and prevent unauthorised access. By implementing robust authentication mechanisms, session monitoring, and privilege elevation controls, organisations can fortify their defences against internal and external threats.
Streamlined Access Management
With One Identity PAM, administrators can efficiently manage user access rights across the entire IT infrastructure. The solution offers centralised control over privileged accounts, simplifying the process of granting or revoking permissions based on user roles and responsibilities. This streamlined approach enhances operational efficiency and reduces the risk of human error.
Compliance Readiness
Meeting regulatory requirements is a critical aspect of modern cybersecurity practices. One Identity PAM assists organisations in achieving compliance by providing detailed audit logs, reporting capabilities, and policy enforcement mechanisms. By maintaining a secure and auditable environment, businesses can demonstrate adherence to industry standards and regulations.
Scalability and Flexibility
One Identity PAM is designed to scale alongside growing business needs. Whether managing a small team or a global enterprise, the solution offers flexibility in deployment options and integration with existing IT infrastructure. This scalability ensures that organisations can adapt to changing security demands without compromising performance or usability.
Conclusion
One Identity’s Privileged Access Management solution empowers organisations to proactively protect their most valuable assets while enhancing operational efficiency and compliance readiness. By leveraging advanced security features and intuitive access management tools, businesses can mitigate risks associated with privileged accounts and maintain a strong security posture in today’s evolving threat landscape.
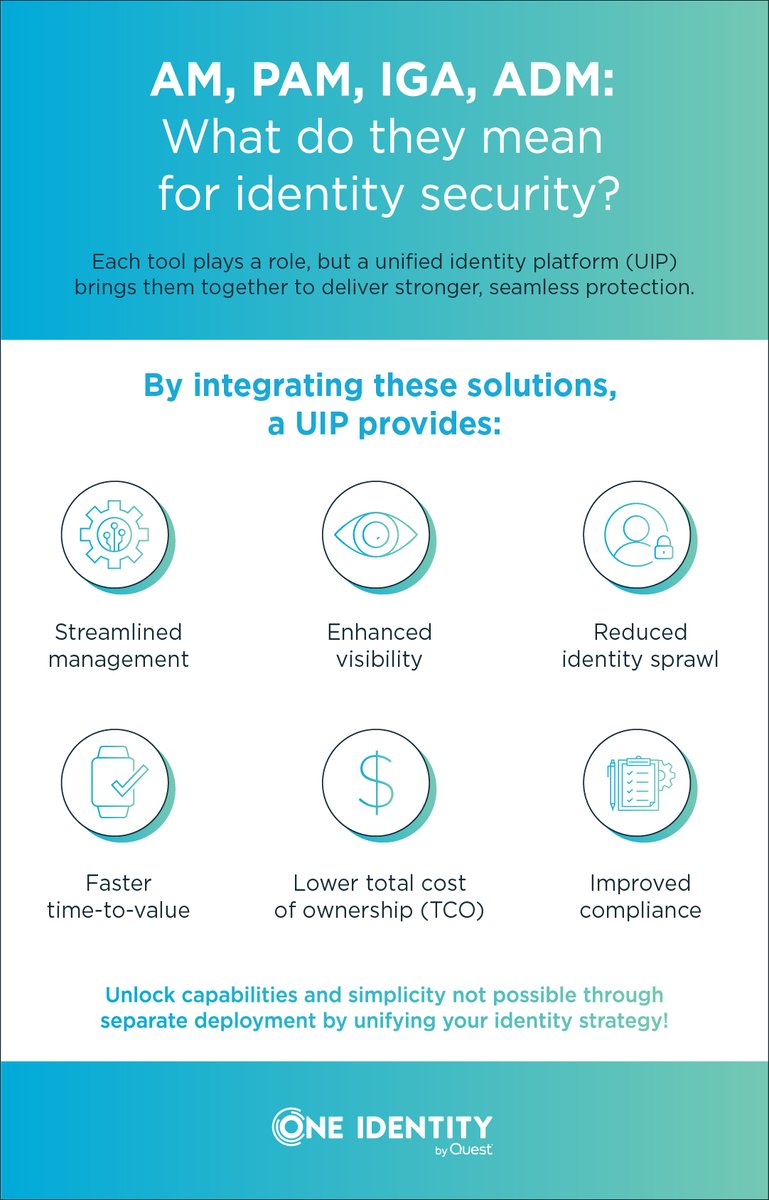
Top 7 Benefits of a Unified Identity PAM Solution for Businesses
- Enhanced security for privileged accounts
- Centralised control over user access rights
- Streamlined management of permissions
- Comprehensive audit logs and reporting capabilities
- Scalable solution adaptable to business growth
- Integration with existing IT infrastructure
- Facilitates compliance with industry regulations
Challenges of a Single Identity PAM Solution: Navigating Complexity, Cost, and Constraints
- Complex Implementation Process
- High Initial Cost
- Steep Learning Curve
- Resource Intensive
- Limited Customisation Options
- Integration Challenges
- Scalability Constraints
Enhanced security for privileged accounts
One of the key advantages of One Identity’s Privileged Access Management (PAM) solution is its ability to provide enhanced security for privileged accounts. By implementing robust authentication mechanisms, session monitoring, and privilege elevation controls, organisations can effectively safeguard their most critical assets from potential cyber threats. This heightened level of security ensures that only authorised users have access to sensitive information and systems, reducing the risk of unauthorised access and data breaches. With One Identity PAM, businesses can bolster their defences and maintain a secure environment for privileged accounts, enhancing overall cybersecurity posture.
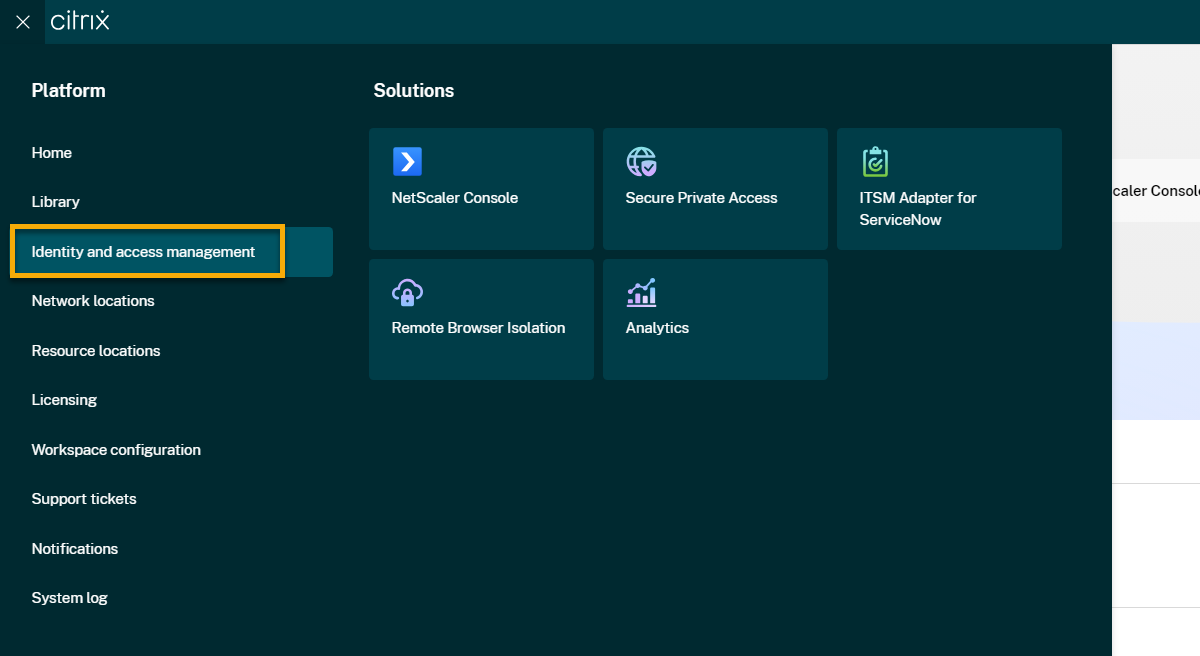
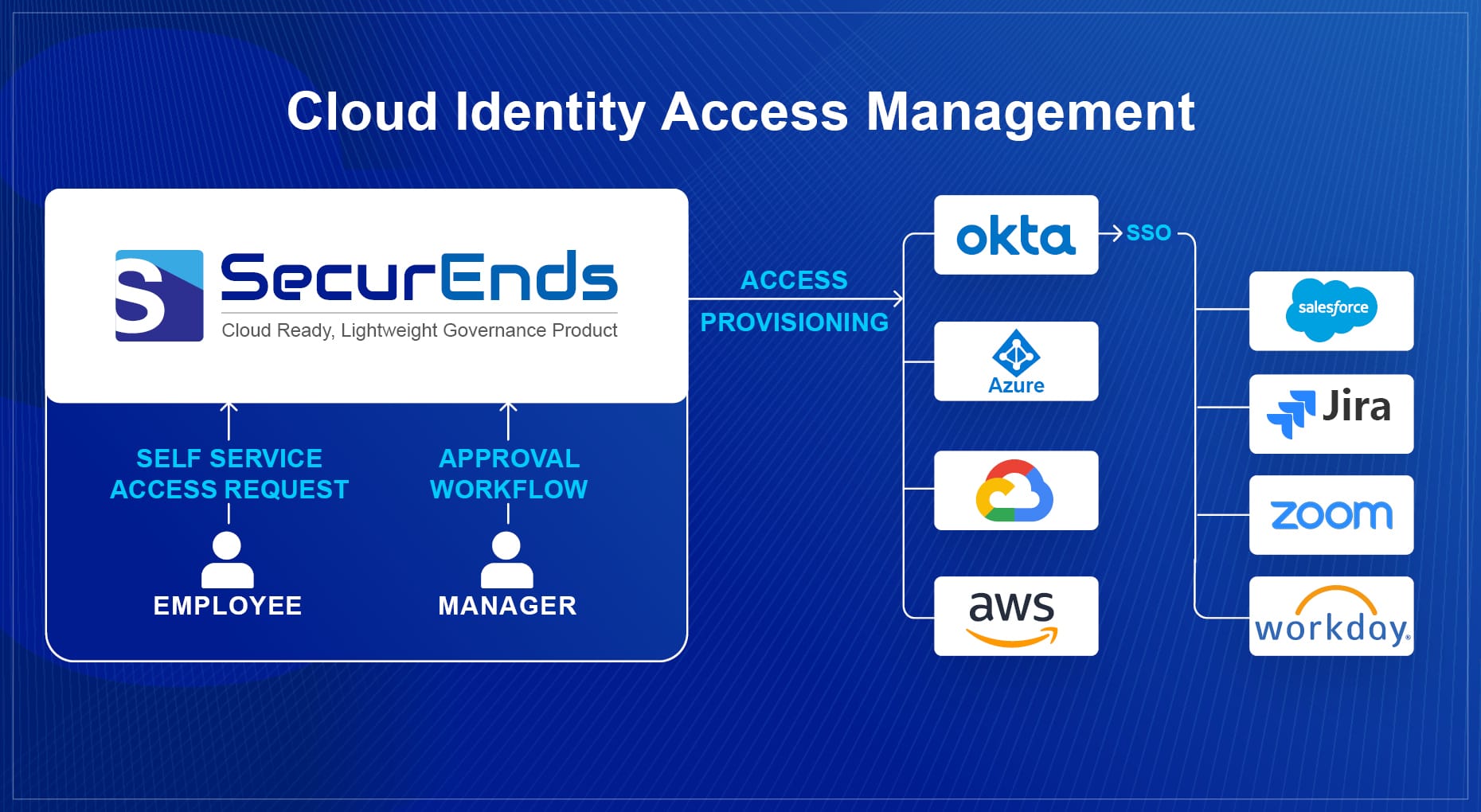
Centralised control over user access rights
One of the key advantages of the One Identity Privileged Access Management (PAM) solution is its provision of centralised control over user access rights. By consolidating the management of privileged accounts into a single, unified platform, organisations can efficiently oversee and regulate access permissions across their entire IT infrastructure. This centralised approach not only simplifies the process of granting or revoking user privileges but also enhances security by ensuring that access rights are consistently applied and monitored in a systematic manner. With centralised control over user access rights, businesses can effectively manage user permissions, reduce the risk of unauthorised access, and maintain a secure environment conducive to strong cybersecurity practices.
Streamlined management of permissions
One notable advantage of the One Identity Privileged Access Management (PAM) solution is its ability to streamline the management of permissions within an organisation’s IT infrastructure. By providing centralised control over privileged accounts, One Identity PAM simplifies the process of assigning and revoking access rights based on user roles and responsibilities. This efficient approach not only enhances operational productivity but also reduces the likelihood of errors in permission management, ultimately contributing to a more secure and well-organised access control system.
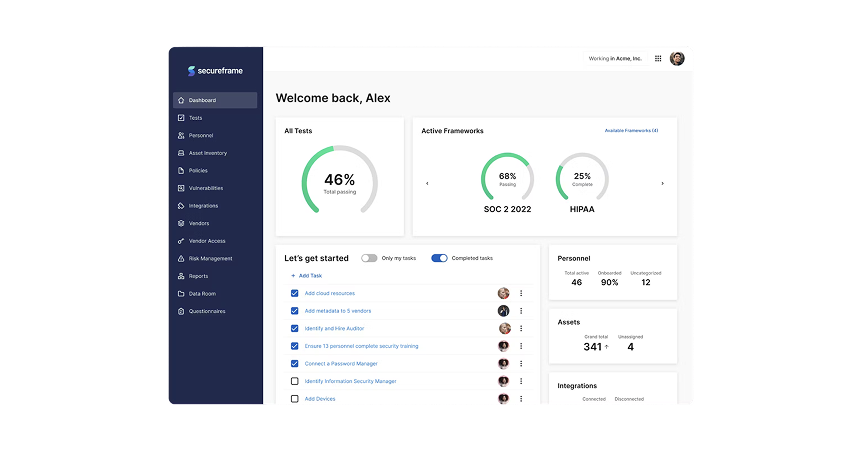
Comprehensive audit logs and reporting capabilities
One standout advantage of the One Identity Privileged Access Management (PAM) solution is its provision of comprehensive audit logs and reporting capabilities. By meticulously documenting all privileged account activities and generating detailed reports, organisations can gain valuable insights into user behaviour, system access, and security events. These audit logs not only enhance visibility into potential security threats but also facilitate regulatory compliance by providing a clear record of access controls and policy enforcement. With robust reporting features, businesses can effectively monitor and analyse their privileged access environment, enabling proactive risk mitigation and informed decision-making.
Scalable solution adaptable to business growth
One of the key advantages of the One Identity Privileged Access Management (PAM) solution is its scalability, making it highly adaptable to business growth. As organisations expand and evolve, their security needs also change. One Identity PAM offers the flexibility to accommodate these shifts by easily scaling to meet increasing demands without compromising performance or security standards. This scalability ensures that businesses can effectively manage privileged access across a growing infrastructure, providing a seamless and secure experience for users while maintaining robust protection against cyber threats.
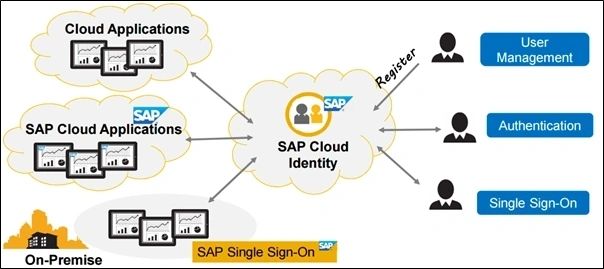
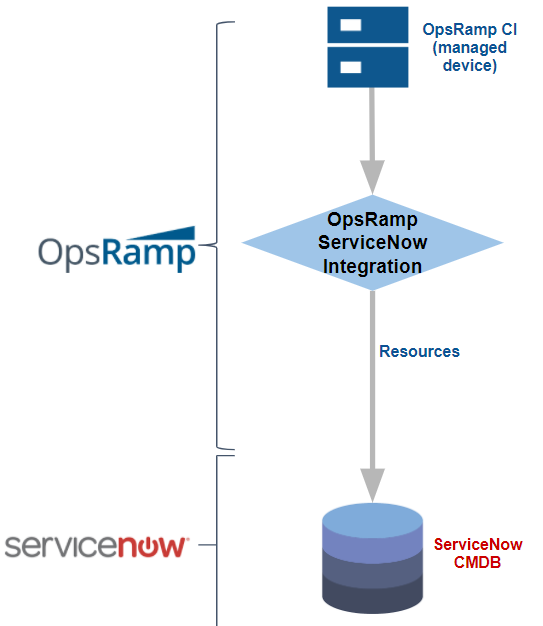
Integration with existing IT infrastructure
One of the key advantages of One Identity’s Privileged Access Management (PAM) solution is its seamless integration with existing IT infrastructure. By offering compatibility with a wide range of systems and applications, One Identity PAM ensures a smooth transition for organisations looking to enhance their security measures without disrupting their current operations. This integration capability not only simplifies deployment but also maximises the value of existing investments, allowing businesses to leverage the full potential of their IT environment while strengthening privileged access controls and overall cybersecurity posture.
Facilitates compliance with industry regulations
One of the key advantages of the One Identity Privileged Access Management (PAM) solution is its ability to facilitate compliance with industry regulations. By providing detailed audit logs, robust reporting capabilities, and policy enforcement mechanisms, One Identity PAM ensures that organisations can easily demonstrate adherence to regulatory requirements. This proactive approach not only helps businesses avoid costly penalties but also instils confidence in stakeholders by showcasing a commitment to maintaining a secure and compliant IT environment.
Complex Implementation Process
Setting up One Identity PAM can present a challenge due to its complex implementation process, which may demand a considerable amount of time and expertise from IT professionals. The intricacies involved in configuring the solution and integrating it with existing systems can lead to delays in deployment and potential resource constraints. Organisations considering One Identity PAM should be prepared to allocate sufficient time and resources to ensure a successful implementation that aligns with their security objectives and operational needs.
High Initial Cost
One significant drawback of the One Identity Privileged Access Management (PAM) solution is its high initial cost, which could potentially pose a barrier to adoption for certain organisations. The upfront investment required to implement One Identity PAM may be prohibitive for businesses with limited budgets or resource constraints. This financial hurdle could deter some organisations from reaping the benefits of enhanced security and streamlined access management that the solution offers, ultimately limiting their ability to strengthen their cybersecurity posture effectively.
Steep Learning Curve
One notable drawback of the One Identity Privileged Access Management (PAM) solution is its steep learning curve, which can pose challenges for users in effectively navigating the platform. The complexity of the system may result in usability issues as individuals struggle to grasp the intricacies of the solution and utilise its features optimally. This learning curve could potentially hinder user adoption and impact overall efficiency, requiring additional time and resources for training and acclimatisation to ensure smooth integration into existing workflows.
Resource Intensive
One significant drawback of the One Identity Privileged Access Management (PAM) solution is its resource-intensive nature. The maintenance and management of One Identity PAM often demand dedicated resources, including personnel and infrastructure, which can contribute to increased operational costs for organisations. The need for ongoing monitoring, updates, and support can strain IT teams and budgets, potentially posing a challenge for businesses looking to streamline their operations and optimise cost-efficiency.
Limited Customisation Options
Some users may encounter a drawback with One Identity’s Privileged Access Management (PAM) solution due to its limited customisation options. While the platform provides a robust set of features, some organisations with unique or highly specific requirements may find the level of customisation offered to be somewhat restrictive. This limitation could potentially hinder the ability to tailor the solution to align perfectly with their individual security protocols and operational processes, leading to challenges in fully meeting their distinct needs and preferences.
Integration Challenges
Integration Challenges: While One Identity PAM offers robust security features and access management capabilities, organisations may encounter compatibility issues when integrating the solution with existing IT systems and applications. Ensuring seamless integration and interoperability between One Identity PAM and diverse technology environments can be a complex task, requiring careful planning and potential customisation. Addressing these integration challenges is crucial to maximise the effectiveness of the solution and minimise disruptions to daily operations.
Scalability Constraints
Scalability Constraints can be a notable drawback of the One Identity PAM solution. As business requirements evolve and expand, the process of scaling up the solution to accommodate growth may encounter challenges. This limitation could potentially hinder organisations from seamlessly adapting to increased user demands or expanding infrastructures, leading to delays in implementing necessary security measures and potentially impacting operational efficiency. Addressing scalability constraints proactively through careful planning and resource allocation is essential to ensure that the One Identity PAM solution remains effective and aligned with the dynamic needs of the business environment.