The Importance of Cybersecurity in Today’s Digital World
The Importance of Cybersecurity in Today’s Digital World
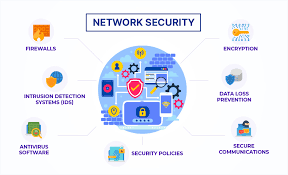
In an increasingly interconnected world where digital technologies play a central role in our daily lives, cybersecurity has become a critical concern for individuals, businesses, and governments alike. The term “cybersecurity” refers to the practice of protecting computer systems, networks, and data from digital attacks and unauthorised access.
Cyber threats come in various forms, including malware, phishing scams, ransomware, and hacking attempts. These threats can result in data breaches, financial losses, reputation damage, and even disruption of essential services. As such, maintaining robust cybersecurity measures is essential to safeguarding sensitive information and ensuring the smooth functioning of digital infrastructure.
Businesses are particularly vulnerable to cyber attacks due to the vast amount of data they store and process. A breach in security can have severe consequences, leading to financial losses, legal repercussions, and loss of customer trust. Implementing effective cybersecurity measures is not only a matter of compliance but also a strategic investment in protecting valuable assets.
Individuals are also at risk in the digital landscape. Personal information stored online can be targeted by cybercriminals for identity theft or fraud. By practising good cybersecurity habits such as using strong passwords, keeping software updated, and being cautious of suspicious emails or links, individuals can reduce their vulnerability to cyber attacks.
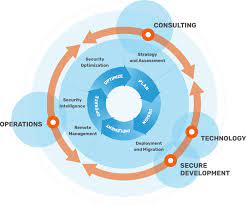
Government agencies play a crucial role in cybersecurity as well. Protecting national security interests and critical infrastructure from cyber threats is paramount in today’s geopolitical landscape. Collaboration between public and private sectors is essential to sharing threat intelligence and developing coordinated responses to cyber incidents.
As technology continues to advance at a rapid pace, the need for robust cybersecurity measures will only increase. It is imperative for individuals, businesses, and governments to stay vigilant against evolving cyber threats and invest in proactive security measures to mitigate risks effectively.
By prioritising cybersecurity awareness, education, and best practices, we can collectively create a safer digital environment for all stakeholders involved. Remember: when it comes to cybersecurity, prevention is always better than cure.
9 Key Benefits of Cyber-Security: Protecting Data, Finances, and Trust
- Protects sensitive data from unauthorised access
- Prevents financial losses due to cyber attacks
- Safeguards personal information from identity theft
- Ensures the continuity of business operations
- Mitigates risks of malware infections and ransomware attacks
- Enhances trust and credibility with clients and customers
- Helps in compliance with data protection regulations
- Improves overall system performance and efficiency
- Strengthens national security against cyber threats
The Hidden Drawbacks of Cybersecurity: 7 Key Challenges
- Cybersecurity measures can be costly to implement and maintain, especially for small businesses with limited budgets.
- Over-reliance on technology-based security solutions may create a false sense of security, leading to vulnerabilities being overlooked.
- Constantly evolving cyber threats require regular updates and adaptations to security protocols, which can be time-consuming and resource-intensive.
- Complex cybersecurity measures may impede user experience and productivity within an organisation.
- Human error remains a significant factor in cybersecurity breaches, as employees may inadvertently compromise security through actions like clicking on malicious links or sharing sensitive information.
- The interconnected nature of digital systems means that a breach in one area can have far-reaching consequences across multiple networks and devices.
- Cybersecurity incidents often result in reputational damage for businesses, eroding customer trust and confidence.
Protects sensitive data from unauthorised access
In today’s digital landscape, one of the key advantages of robust cybersecurity measures is the protection of sensitive data from unauthorised access. By implementing strong security protocols, encryption techniques, and access controls, organisations can safeguard confidential information such as customer data, financial records, and intellectual property from malicious actors. Preventing unauthorised access not only helps maintain the trust of stakeholders but also ensures compliance with data protection regulations. Effective cybersecurity measures act as a barrier against potential breaches, mitigating the risk of data theft and preserving the integrity and confidentiality of valuable information.
Prevents financial losses due to cyber attacks
Effective cybersecurity measures play a crucial role in preventing financial losses resulting from cyber attacks. By implementing robust security protocols and staying vigilant against potential threats, businesses can safeguard their valuable assets and sensitive financial information from falling into the hands of cybercriminals. Proactive cybersecurity not only helps in avoiding costly data breaches and ransom demands but also protects organisations from potential legal liabilities and reputational damage that may arise from successful cyber attacks. Investing in cybersecurity is an essential strategy for mitigating financial risks and ensuring the long-term stability and resilience of businesses in today’s digital landscape.
In today’s digital age, one of the key advantages of robust cybersecurity measures is their ability to safeguard personal information from identity theft. By implementing strong security protocols and encryption techniques, individuals can protect their sensitive data from falling into the hands of cybercriminals who seek to exploit it for fraudulent purposes. Preventing identity theft through cybersecurity not only preserves individuals’ privacy and financial well-being but also fosters a sense of trust and confidence in online interactions and transactions.
Ensures the continuity of business operations
Cybersecurity plays a crucial role in ensuring the continuity of business operations. By implementing robust security measures, organisations can safeguard their digital assets and systems from cyber threats that could disrupt normal business activities. Preventing data breaches, malware attacks, and other cyber incidents not only protects sensitive information but also helps maintain the integrity and availability of critical systems. With a strong cybersecurity framework in place, businesses can operate smoothly without the fear of downtime or financial losses caused by cyber disruptions, thus enabling them to focus on their core operations and strategic goals with confidence.
Mitigates risks of malware infections and ransomware attacks
Incorporating robust cybersecurity measures helps mitigate the risks associated with malware infections and ransomware attacks. By implementing effective security protocols, organisations can significantly reduce the likelihood of malicious software infiltrating their systems and compromising sensitive data. Proactive measures such as regular software updates, network monitoring, and employee training on cybersecurity best practices play a crucial role in fortifying defences against these prevalent cyber threats. By prioritising cybersecurity, businesses can safeguard their operations against the potentially devastating consequences of malware and ransomware attacks, ensuring continuity and integrity in their digital environments.
Enhances trust and credibility with clients and customers
In today’s digital age, one significant advantage of prioritising cybersecurity is that it enhances trust and credibility with clients and customers. By implementing robust security measures to protect sensitive data and prevent cyber threats, businesses demonstrate their commitment to safeguarding customer information and maintaining the confidentiality of transactions. This proactive approach not only builds trust with clients but also enhances the reputation of the organisation as a reliable and secure partner in an increasingly interconnected world. Ultimately, investing in cybersecurity not only protects valuable assets but also strengthens relationships with customers by instilling confidence in the security of their data.
Helps in compliance with data protection regulations
Ensuring robust cybersecurity measures in place not only safeguards sensitive data from potential breaches but also plays a crucial role in compliance with data protection regulations. By implementing strong security protocols and encryption methods, organisations can effectively protect personal information and maintain the confidentiality and integrity of data as required by various data protection laws. Compliance with these regulations not only helps in avoiding hefty fines and legal consequences but also fosters trust with customers and stakeholders, demonstrating a commitment to upholding privacy rights and security standards in today’s digital landscape.
Enhancing cyber-security not only fortifies digital defences against potential threats but also contributes to improving overall system performance and efficiency. By implementing robust security measures, such as firewalls, encryption protocols, and intrusion detection systems, organisations can streamline operations and reduce the risk of system downtime caused by cyber attacks. A secure network environment allows for smoother data flow, faster response times, and optimal resource allocation, ultimately leading to enhanced productivity and a more resilient IT infrastructure.
Strengthens national security against cyber threats
In the realm of cybersecurity, one significant benefit is its ability to bolster national security by fortifying defences against cyber threats. As governments increasingly rely on digital infrastructure for critical operations and communication, the protection of sensitive data and systems from malicious actors becomes paramount. By implementing robust cybersecurity measures, nations can enhance their resilience against cyber attacks, safeguarding vital information, infrastructure, and services essential for maintaining national security in an ever-evolving digital landscape.
Cybersecurity measures can be costly to implement and maintain, especially for small businesses with limited budgets.
Implementing and maintaining cybersecurity measures can pose a significant financial challenge, particularly for small businesses operating with constrained budgets. The cost of acquiring and deploying robust security solutions, conducting regular assessments, and training staff on cybersecurity best practices can quickly add up, placing a strain on limited resources. As a result, small businesses may find it challenging to allocate sufficient funds towards comprehensive cybersecurity measures, leaving them more vulnerable to cyber threats and potential data breaches. Balancing the need for effective security with budgetary constraints remains a pressing concern for many small enterprises navigating the complex landscape of cybersecurity.
Over-reliance on technology-based security solutions may create a false sense of security, leading to vulnerabilities being overlooked.
In the realm of cybersecurity, one significant con to be wary of is the potential danger posed by an over-reliance on technology-based security solutions. While advanced tools and software can provide a layer of protection, solely depending on them may foster a false sense of security. This false sense can lead to critical vulnerabilities being overlooked or underestimated, leaving systems exposed to sophisticated cyber threats that can circumvent traditional defences. It is essential for organisations and individuals to complement technology-based solutions with robust risk assessment practices and human oversight to ensure comprehensive protection against evolving cyber risks.
Constantly evolving cyber threats require regular updates and adaptations to security protocols, which can be time-consuming and resource-intensive.
In the realm of cybersecurity, one significant challenge lies in the ever-evolving nature of cyber threats. The need for regular updates and adaptations to security protocols is paramount to staying ahead of malicious actors. However, this process can be both time-consuming and resource-intensive for organisations. Keeping pace with the rapidly changing landscape of cyber threats demands continuous monitoring, analysis, and implementation of new security measures, often requiring significant investments in technology, personnel training, and infrastructure upgrades. Balancing the need for robust cybersecurity with the practical constraints of time and resources poses a complex dilemma that organisations must navigate diligently to protect their digital assets effectively.
Complex cybersecurity measures may impede user experience and productivity within an organisation.
Complex cybersecurity measures, while crucial for protecting sensitive data and systems, can inadvertently hinder user experience and productivity within an organisation. Excessive security protocols, such as frequent password changes, multi-factor authentication, and strict access controls, may create barriers that slow down employees’ workflow and impede collaboration. When cybersecurity measures become overly cumbersome or time-consuming, employees may resort to workarounds or bypass security protocols altogether, compromising the effectiveness of the security framework. Striking a balance between robust cybersecurity practices and user-friendly processes is essential to ensure that security measures do not unnecessarily disrupt operational efficiency and employee productivity.
Human error remains a significant factor in cybersecurity breaches, as employees may inadvertently compromise security through actions like clicking on malicious links or sharing sensitive information.
Human error stands out as a prominent drawback in the realm of cybersecurity, often leading to breaches and vulnerabilities within systems. Employees, whether due to lack of awareness or oversight, can unknowingly jeopardise security by engaging in risky behaviours such as clicking on malicious links or disclosing confidential information. These actions not only expose sensitive data to potential threats but also highlight the critical need for continuous training and vigilance among individuals to mitigate the impact of human error on cybersecurity measures.
The interconnected nature of digital systems means that a breach in one area can have far-reaching consequences across multiple networks and devices.
The interconnected nature of digital systems poses a significant con in cybersecurity as a breach in one area can have cascading effects across multiple networks and devices. A vulnerability exploited in one system can potentially spread like a domino effect, compromising the security of interconnected systems and amplifying the impact of the initial breach. This interconnectedness underscores the importance of comprehensive cybersecurity measures to not only protect individual networks but also to mitigate the potential ripple effects of cyber attacks on a broader scale.
Cybersecurity incidents often result in reputational damage for businesses, eroding customer trust and confidence.
Cybersecurity incidents pose a significant con for businesses as they can lead to reputational damage, ultimately eroding customer trust and confidence. When a company falls victim to a cyber attack or data breach, it not only faces financial losses and operational disruptions but also risks tarnishing its reputation in the eyes of customers. The loss of trust from clients and stakeholders can have long-lasting implications, impacting customer loyalty and brand credibility. Rebuilding trust post-incident can be challenging and time-consuming, highlighting the critical importance of robust cybersecurity measures in safeguarding both data integrity and business reputation.