The Importance of HIPAA Compliant Document Management Software
Healthcare organisations handle vast amounts of sensitive patient information on a daily basis. To ensure the confidentiality, integrity, and availability of this data, compliance with regulations such as the Health Insurance Portability and Accountability Act (HIPAA) is crucial. HIPAA sets the standard for protecting sensitive patient data and requires healthcare providers to implement appropriate safeguards.
One key aspect of HIPAA compliance is the secure management of electronic documents containing protected health information (PHI). This is where HIPAA compliant document management software plays a vital role. Such software is specifically designed to meet the stringent security requirements outlined by HIPAA, providing healthcare organisations with a secure platform to store, manage, and share sensitive patient data.
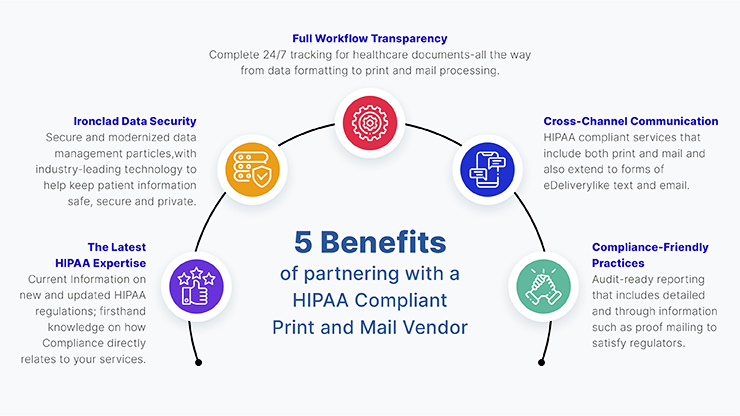
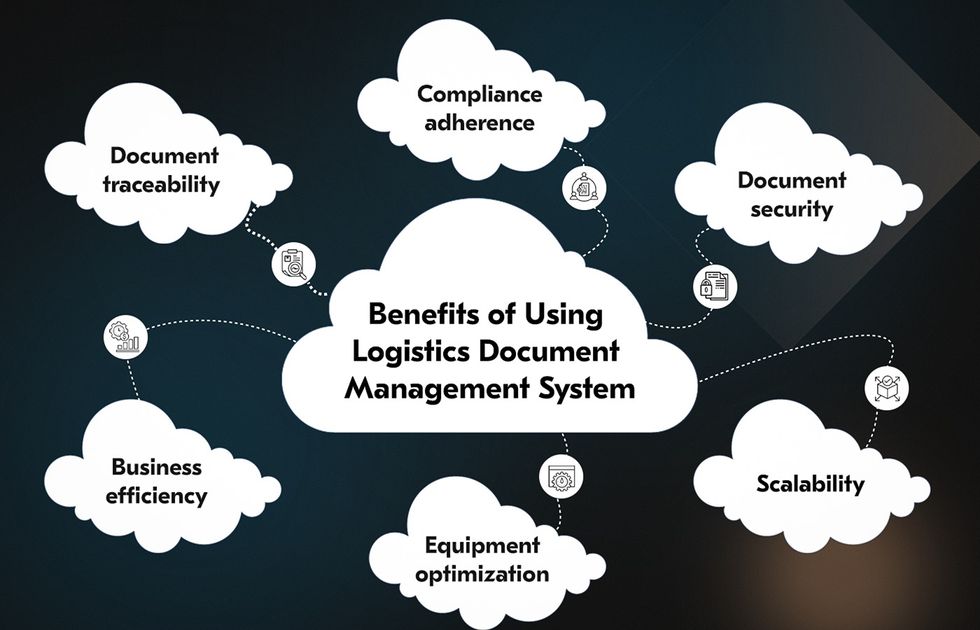
Benefits of HIPAA Compliant Document Management Software:
- Data Encryption: HIPAA compliant document management software uses encryption techniques to protect PHI from unauthorised access or breaches.
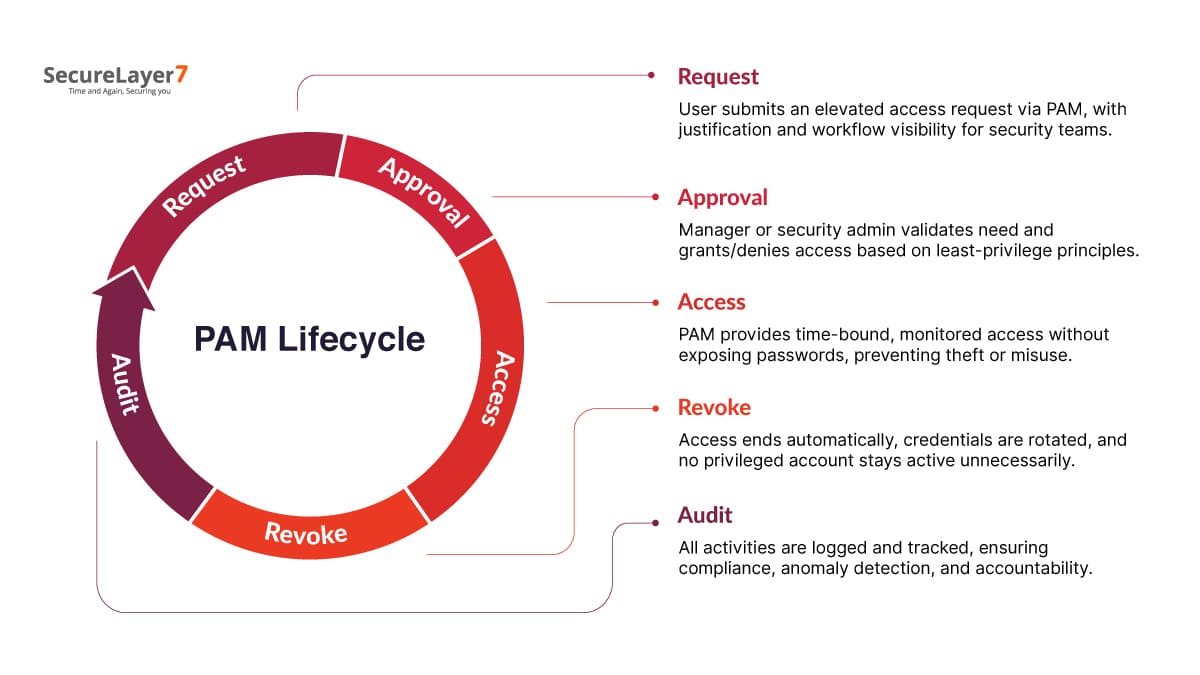
- Audit Trails: The software maintains detailed audit logs that track user activities within the system, ensuring accountability and transparency.
- Access Controls: Role-based access controls restrict data access to authorised personnel only, reducing the risk of data leaks or misuse.
- Secure Sharing: Secure file sharing features enable healthcare providers to collaborate on patient records while maintaining data security.
- Compliance Reporting: The software generates compliance reports that demonstrate adherence to HIPAA regulations during audits or inspections.
In addition to enhancing data security and regulatory compliance, HIPAA compliant document management software streamlines document workflows, improves efficiency in managing patient records, and reduces the risk of human errors or paper-based vulnerabilities. By centralising document storage and ensuring secure access controls, healthcare organisations can mitigate risks associated with data breaches and non-compliance penalties.
Investing in HIPAA compliant document management software is not just a regulatory requirement but a proactive step towards safeguarding patient privacy and maintaining trust in healthcare services. By leveraging technology that prioritises security and compliance, healthcare providers can focus on delivering quality care while ensuring the confidentiality of patient information remains paramount.
Top 5 Advantages of HIPAA-Compliant Document Management Software
- Enhanced data security through encryption techniques
- Detailed audit trails for tracking user activities
- Role-based access controls to restrict data access
- Secure file sharing features for collaboration
- Compliance reporting to demonstrate adherence to HIPAA regulations
Challenges of HIPAA Compliant Document Management Software: Costs, Complexity, and Customisation Limits
- Initial Cost
- Complexity
- Integration Challenges
- User Training
- Maintenance Overhead
- Limited Customisation
Enhanced data security through encryption techniques
HIPAA compliant document management software offers enhanced data security through the implementation of robust encryption techniques. By encrypting sensitive patient information stored within the system, healthcare organisations can safeguard against unauthorised access and data breaches. Encryption transforms data into a secure format that can only be deciphered with the appropriate decryption key, ensuring that patient records remain protected from cyber threats and malicious actors. This proactive approach to data security not only helps healthcare providers comply with HIPAA regulations but also instils confidence in patients that their confidential information is being handled with the utmost care and diligence.
Detailed audit trails for tracking user activities
One significant advantage of HIPAA compliant document management software is its provision of detailed audit trails for tracking user activities. This feature enables healthcare organisations to maintain a comprehensive record of who accessed, modified, or shared sensitive patient information within the system. By having visibility into user interactions with PHI, healthcare providers can enhance accountability, detect any unauthorised access or suspicious behaviour promptly, and demonstrate compliance with HIPAA regulations during audits. The detailed audit trails offered by this software not only bolster data security but also serve as a valuable tool in ensuring transparency and maintaining the integrity of patient records.
Role-based access controls to restrict data access
One of the key advantages of HIPAA compliant document management software is its implementation of role-based access controls to restrict data access. This feature allows healthcare organisations to assign specific access permissions to users based on their roles and responsibilities, ensuring that only authorised personnel can view or modify sensitive patient information. By limiting data access to relevant individuals, healthcare providers can enhance data security, prevent unauthorised disclosures, and maintain compliance with HIPAA regulations.
Secure file sharing features for collaboration
One significant advantage of HIPAA compliant document management software is its secure file sharing features that facilitate seamless collaboration among healthcare professionals. By providing a safe platform for sharing sensitive patient information, this feature ensures that data remains protected and confidential throughout the collaboration process. Healthcare providers can efficiently work together on patient records, treatment plans, and other critical documents without compromising data security, thereby enhancing teamwork and productivity while maintaining compliance with HIPAA regulations.
Compliance reporting to demonstrate adherence to HIPAA regulations
One significant advantage of HIPAA compliant document management software is its capability to generate compliance reports that showcase adherence to HIPAA regulations. These detailed reports serve as valuable documentation during audits or inspections, providing healthcare organisations with a clear and structured overview of their compliance efforts. By easily demonstrating adherence to regulatory requirements through comprehensive reporting, healthcare providers can instil confidence in patients, regulatory bodies, and stakeholders while ensuring the security and confidentiality of sensitive patient information.
Initial Cost
One notable drawback of HIPAA compliant document management software is the initial cost associated with its implementation. Healthcare organisations may face substantial upfront expenses for acquiring the software, setting it up, and providing necessary training to staff members. These costs can pose a financial challenge, especially for smaller healthcare facilities or practices with limited budgets. The investment required for HIPAA compliant document management software may deter some organisations from prioritising data security and compliance, despite the long-term benefits it offers in safeguarding patient information.
Complexity
The complexity associated with HIPAA compliant document management software poses a significant challenge for healthcare organisations. Meeting the intricate requirements of HIPAA regulations demands dedicated resources and specialised expertise to navigate the nuances of proper configuration and ensure continuous compliance. The need for ongoing monitoring, updates, and staff training adds to the complexity, potentially straining organisational resources and requiring a substantial investment in time and personnel. Balancing the intricacies of HIPAA compliance with day-to-day operations can be a daunting task, highlighting the importance of adequate planning and support to effectively manage the complexities associated with implementing and maintaining compliant document management software within healthcare settings.
Integration Challenges
One significant drawback of HIPAA compliant document management software is the integration challenges it poses. Incorporating the software into existing systems or workflows within a healthcare organisation can be a complex and time-consuming process, potentially causing disruptions to daily operations. The need to align different technologies, data formats, and processes may require extensive planning and resources to ensure a seamless integration without compromising data security or regulatory compliance. Despite the benefits of enhanced security and compliance that HIPAA compliant software offers, overcoming integration hurdles remains a notable concern for healthcare providers seeking to implement such solutions.
User Training
Implementing HIPAA compliant document management software comes with its challenges, including the con of user training. Ensuring that staff are proficient in using the software effectively and in adherence to HIPAA regulations can be a time-consuming process that demands additional resources. Training sessions need to cover not only the technical aspects of the software but also the specific protocols and security measures required by HIPAA. Allocating sufficient time for training and ongoing education is essential to mitigate risks associated with human error and ensure that all users understand their role in maintaining data security and compliance within the healthcare environment.
Maintenance Overhead
Regular maintenance, updates, and monitoring are essential for ensuring the continued compliance of HIPAA compliant document management software, which can contribute to increased operational overhead. Healthcare organisations must allocate resources and manpower to manage the upkeep of the software, including installing updates, conducting regular audits, and monitoring system performance. This ongoing maintenance requirement adds to the workload of IT teams and may require additional training or expertise to ensure that the software remains compliant with evolving HIPAA regulations. The maintenance overhead associated with HIPAA compliant document management software underscores the importance of proactive planning and resource allocation to sustain data security and regulatory adherence in healthcare environments.
Limited Customisation
Some HIPAA compliant document management software solutions may present a challenge due to their limited customisation capabilities, which can restrict the software’s scalability to accommodate specific organisational requirements. Organisations with unique workflows or specialised data management needs may find themselves constrained by the rigid structure of certain HIPAA compliant software, potentially leading to inefficiencies in document handling and workflow processes. It is crucial for healthcare providers to carefully assess the customisation options offered by such software solutions to ensure that they align with their operational demands and can effectively support their individualised workflows while maintaining compliance with HIPAA regulations.