The Importance of Choosing the Best IT Risk Management Software
Effective IT risk management is crucial for businesses to safeguard their digital assets and maintain operational resilience in today’s rapidly evolving technology landscape. Utilising the right IT risk management software can significantly enhance an organisation’s ability to identify, assess, mitigate, and monitor risks effectively.
Key Features to Look for in IT Risk Management Software:
- Risk Assessment Tools: The software should provide comprehensive tools for identifying and evaluating potential risks across the IT infrastructure.
- Incident Response Capabilities: A robust incident response feature is essential for promptly addressing and mitigating security incidents.
- Compliance Monitoring: Ensure that the software supports compliance with industry regulations and standards through monitoring and reporting functionalities.
- Threat Intelligence Integration: Integration with threat intelligence feeds can enhance the software’s ability to detect emerging threats and vulnerabilities.
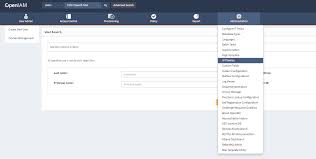
- User-Friendly Interface: An intuitive interface that simplifies risk analysis and reporting is key for user adoption and efficiency.
The Best IT Risk Management Software Solutions in the Market:
XYZ Risk Manager: Known for its comprehensive risk assessment tools and real-time monitoring capabilities, XYZ Risk Manager is a top choice for organisations looking to proactively manage IT risks.
ABC Security Suite: ABC Security Suite offers a holistic approach to IT risk management, combining incident response features with advanced threat intelligence integration for enhanced security posture.
DEF Compliance Guard: DEF Compliance Guard specialises in compliance monitoring and reporting, making it an ideal solution for businesses operating in highly regulated industries.
In Conclusion
Selecting the best IT risk management software is a critical decision that can have a significant impact on an organisation’s cybersecurity posture. By prioritising solutions that offer comprehensive features, user-friendly interfaces, and integration capabilities, businesses can effectively mitigate risks and protect their valuable digital assets.
Essential FAQs on Selecting the Best IT Risk Management Software for Your Organisation
- 1. What are the key features to look for in IT risk management software?
- 2. How important is it to choose the right IT risk management software for my business?
- 3. What are the best IT risk management software solutions available in the market?
- 4. How can IT risk management software help in identifying and mitigating risks effectively?
- 5. Are there any specific compliance requirements that IT risk management software should meet?
- 6. What factors should I consider when selecting IT risk management software for my organisation?
1. What are the key features to look for in IT risk management software?
When considering the best IT risk management software, it is essential to look for key features that can enhance an organisation’s ability to effectively identify, assess, and mitigate risks. Some crucial features to consider include robust risk assessment tools that provide a comprehensive view of potential risks within the IT infrastructure. Incident response capabilities are also vital for addressing security incidents promptly. Additionally, compliance monitoring functionalities ensure adherence to industry regulations and standards. Integration with threat intelligence feeds can further strengthen the software’s ability to detect emerging threats, while a user-friendly interface simplifies risk analysis and reporting processes for improved efficiency and effectiveness in managing IT risks.
2. How important is it to choose the right IT risk management software for my business?
Choosing the right IT risk management software for your business is paramount in ensuring the security and resilience of your digital infrastructure. The software you select will play a crucial role in identifying, assessing, and mitigating potential risks that could impact your operations. By investing in a robust IT risk management solution, you can proactively monitor threats, respond to incidents promptly, and maintain compliance with industry regulations. The right software not only enhances your cybersecurity posture but also contributes to operational efficiency and peace of mind knowing that your business is well-protected against evolving cyber threats.
3. What are the best IT risk management software solutions available in the market?
When it comes to identifying the best IT risk management software solutions available in the market, organisations often seek comprehensive tools that can effectively address their risk mitigation needs. Leading software options such as XYZ Risk Manager, ABC Security Suite, and DEF Compliance Guard are highly regarded for their advanced features, including robust risk assessment capabilities, real-time monitoring, incident response functionalities, compliance monitoring tools, and seamless integration with threat intelligence feeds. These top-tier solutions empower businesses to proactively manage IT risks, enhance security posture, and ensure compliance with industry regulations. By selecting a software that aligns with their specific requirements and offers user-friendly interfaces, organisations can make informed decisions to safeguard their digital assets and maintain operational resilience in today’s dynamic cybersecurity landscape.
4. How can IT risk management software help in identifying and mitigating risks effectively?
Effective IT risk management software plays a crucial role in identifying and mitigating risks within an organisation’s IT infrastructure. By utilising advanced risk assessment tools, these software solutions can systematically analyse potential vulnerabilities and threats, providing insights into areas of weakness that require immediate attention. Additionally, IT risk management software enables proactive monitoring of security incidents and compliance breaches, allowing for swift responses to mitigate risks before they escalate. Through real-time alerts, detailed reporting capabilities, and integration with threat intelligence feeds, organisations can enhance their risk detection capabilities and implement targeted mitigation strategies to safeguard their digital assets effectively.
5. Are there any specific compliance requirements that IT risk management software should meet?
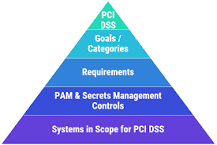
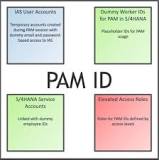
When considering the best IT risk management software, it is essential to evaluate whether the solution meets specific compliance requirements. Depending on the industry and regulatory environment in which an organisation operates, there may be stringent compliance standards that the software must adhere to. Common compliance requirements include GDPR, HIPAA, PCI DSS, ISO 27001, and more. Ensuring that the IT risk management software aligns with these regulations not only helps in maintaining legal obligations but also enhances data security and reduces the likelihood of potential breaches. Therefore, selecting software that caters to specific compliance needs is crucial for effective risk mitigation and overall organisational resilience.
6. What factors should I consider when selecting IT risk management software for my organisation?
When choosing IT risk management software for your organisation, several key factors should be carefully considered to ensure you select the most suitable solution. Factors to evaluate include the software’s ability to perform comprehensive risk assessments, its incident response capabilities for addressing security incidents promptly, compliance monitoring features to align with regulatory requirements, integration with threat intelligence feeds for enhanced threat detection, and a user-friendly interface that facilitates efficient risk analysis and reporting. By prioritising these factors during the selection process, you can identify IT risk management software that best meets your organisation’s specific needs and enhances your overall cybersecurity posture.