The Importance of User Identity Management System in Modern Businesses
In today’s digital age, where data breaches and cyber threats are on the rise, ensuring secure access to sensitive information is paramount for businesses of all sizes. This is where a robust User Identity Management System plays a crucial role.
What is a User Identity Management System?
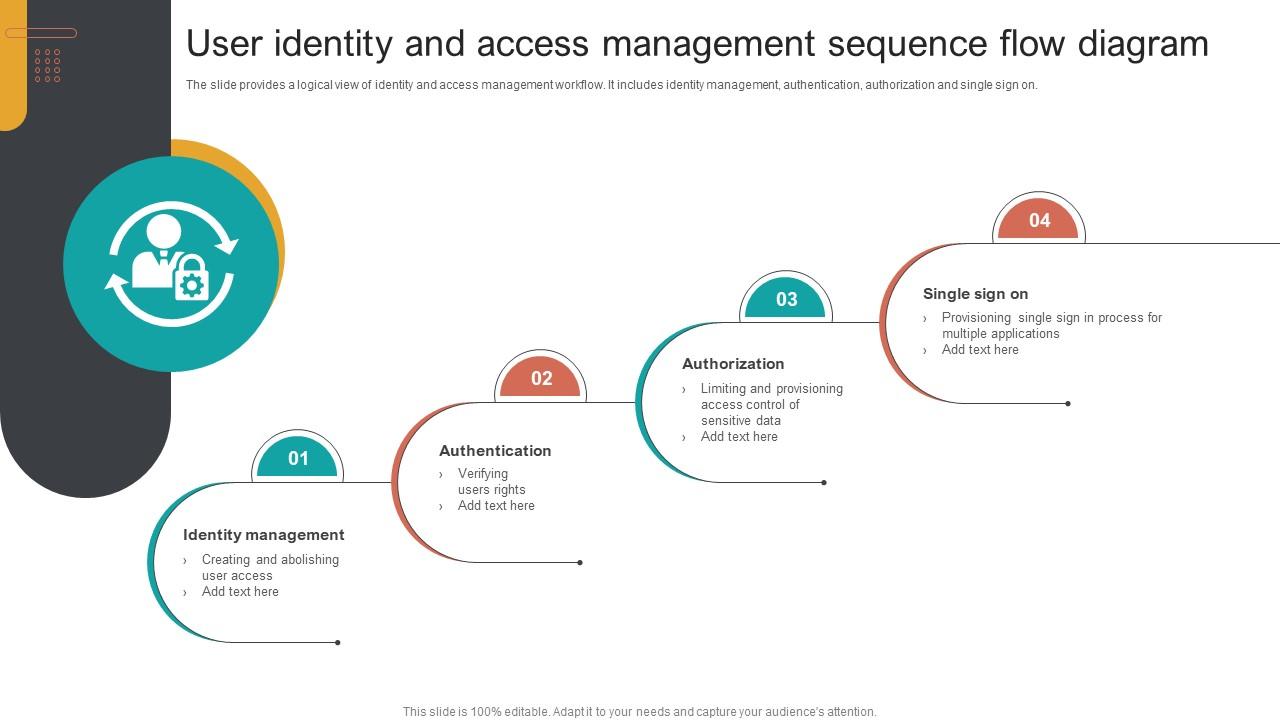
A User Identity Management System, often referred to as IAM (Identity and Access Management), is a framework of policies and technologies that ensure the right individuals have the appropriate access to resources within an organisation’s IT infrastructure. It involves managing digital identities, defining user roles and permissions, and monitoring user activities.
The Benefits of Implementing a User Identity Management System:
- Enhanced Security: By centralising user access control and authentication processes, IAM systems help prevent unauthorised access to sensitive data.
- Improved Compliance: Organisations can easily enforce regulatory requirements by managing user permissions and tracking access activities.
- Increased Productivity: Streamlining user authentication processes reduces the time spent on manual tasks, enabling employees to focus on their core responsibilities.
- Cyber Threat Mitigation: IAM systems provide real-time monitoring capabilities that detect suspicious activities and potential security breaches.
- Cost Efficiency: By automating user provisioning and deprovisioning processes, businesses can reduce administrative overheads associated with managing user accounts.
Key Features of a User Identity Management System:
Modern IAM solutions offer a range of features to meet the evolving security needs of businesses, including:
- User Authentication
- Role-based Access Control
- Password Management
- Single Sign-On (SSO)
- Multi-factor Authentication (MFA)
- Audit Trails and Reporting
- User Provisioning and Deprovisioning
In Conclusion
A User Identity Management System is no longer just an option but a necessity for organisations looking to safeguard their digital assets and maintain regulatory compliance. By implementing an effective IAM solution, businesses can enhance security, improve operational efficiency, and mitigate cyber risks in today’s interconnected world.
Understanding User Identity Management Systems: Key Concepts and FAQs
- What are the 4 pillars of IAM?
- What is the difference between user management and IAM?
- What is user identity management?
- What is the difference between UAM and IAM?
- How does the IAM system work?
- What is an IAM system?
- Which IAM tool is best?
- Is Microsoft Mim end of life?
What are the 4 pillars of IAM?
In the realm of User Identity Management Systems, the concept of the “4 pillars of IAM” refers to the fundamental components that form the foundation of a robust IAM framework. These pillars typically include Identity Governance, Access Management, Privileged Access Management, and Identity Lifecycle Management. Each pillar plays a crucial role in ensuring secure access control, governance, and compliance within an organisation’s IT infrastructure. By focusing on these key pillars, businesses can establish a comprehensive IAM strategy that effectively manages user identities, controls access to resources, and mitigates security risks across their digital ecosystem.
What is the difference between user management and IAM?
When discussing user identity management systems, it is essential to understand the distinction between user management and Identity and Access Management (IAM). User management typically refers to the basic processes of creating, updating, and deleting user accounts within an organisation’s IT environment. On the other hand, IAM goes beyond just managing user accounts; it encompasses a comprehensive framework of policies and technologies that govern user access to resources based on defined roles and permissions. IAM solutions provide advanced features such as authentication, authorisation, and auditing capabilities to ensure secure and efficient access control across an organisation’s digital assets. In essence, while user management focuses on account administration, IAM offers a holistic approach to managing identities and access rights within an organisation’s ecosystem.
What is user identity management?
User Identity Management, often abbreviated as IAM (Identity and Access Management), refers to the process of managing digital identities within an organisation’s IT infrastructure. It involves defining and controlling user roles, permissions, and access to resources such as applications, data, and systems. User Identity Management ensures that individuals are authenticated securely and granted appropriate levels of access based on their roles and responsibilities. By centralising user authentication processes and enforcing security policies, IAM systems play a crucial role in enhancing data security, regulatory compliance, and overall operational efficiency within businesses.
What is the difference between UAM and IAM?
When discussing user identity management systems, a common question that arises is the distinction between User Access Management (UAM) and Identity and Access Management (IAM). While both UAM and IAM are crucial components of securing digital resources within an organisation, they serve distinct purposes. UAM primarily focuses on managing user access rights to specific applications or resources based on their roles or responsibilities. On the other hand, IAM encompasses a broader scope by not only managing user access but also handling user identities, authentication, authorisation, and governance across the entire IT infrastructure. In essence, UAM deals with access control at a more granular level, while IAM provides a comprehensive framework for managing identities and access rights organisation-wide. Understanding this difference is essential for businesses to implement the most suitable security measures tailored to their specific needs.
How does the IAM system work?
The IAM system, short for Identity and Access Management, operates by managing digital identities and controlling user access to resources within an organisation’s IT environment. It works through a framework of policies and technologies that authenticate users, assign appropriate roles and permissions based on predefined criteria, and monitor user activities to ensure compliance with security policies. By centralising user identity management processes, the IAM system streamlines authentication procedures, enforces security protocols, and provides real-time monitoring capabilities to detect and respond to potential security threats effectively. Overall, the IAM system plays a critical role in enhancing data security, regulatory compliance, and operational efficiency within modern businesses.
What is an IAM system?
An IAM system, short for Identity and Access Management system, is a comprehensive framework comprising policies and technologies designed to manage digital identities and control access to resources within an organisation’s IT infrastructure. Essentially, an IAM system ensures that the right individuals have the appropriate levels of access to data, systems, and applications based on their roles and responsibilities. By centralising user authentication, authorisation, and monitoring processes, IAM systems play a vital role in enhancing security, streamlining compliance efforts, and improving overall operational efficiency within modern businesses.
Which IAM tool is best?
When it comes to selecting the best Identity and Access Management (IAM) tool for your organisation, there is no one-size-fits-all answer. The choice of an IAM tool depends on various factors such as the size of your business, specific security requirements, budget constraints, and scalability needs. It is essential to conduct a thorough assessment of your organisation’s IAM needs, evaluate different tools based on their features and compatibility with your existing infrastructure, and consider factors like user experience and vendor support. Ultimately, the best IAM tool is one that aligns closely with your organisation’s unique requirements and provides a comprehensive solution to manage user identities effectively while enhancing security measures.
Is Microsoft Mim end of life?
The question of whether Microsoft Identity Manager (MIM) has reached its end of life is a common concern among users of identity management systems. As of now, Microsoft has announced that MIM will not receive any major updates or new features, indicating a shift towards other identity management solutions within their product portfolio. While MIM may still be supported for a period, organisations are advised to consider alternative options to ensure continued support and security for their user identity management needs in the long term. It is recommended to stay informed about Microsoft’s roadmap for identity management solutions and explore migration paths to newer technologies that align with evolving security requirements.