The Importance of Cloud Network Security
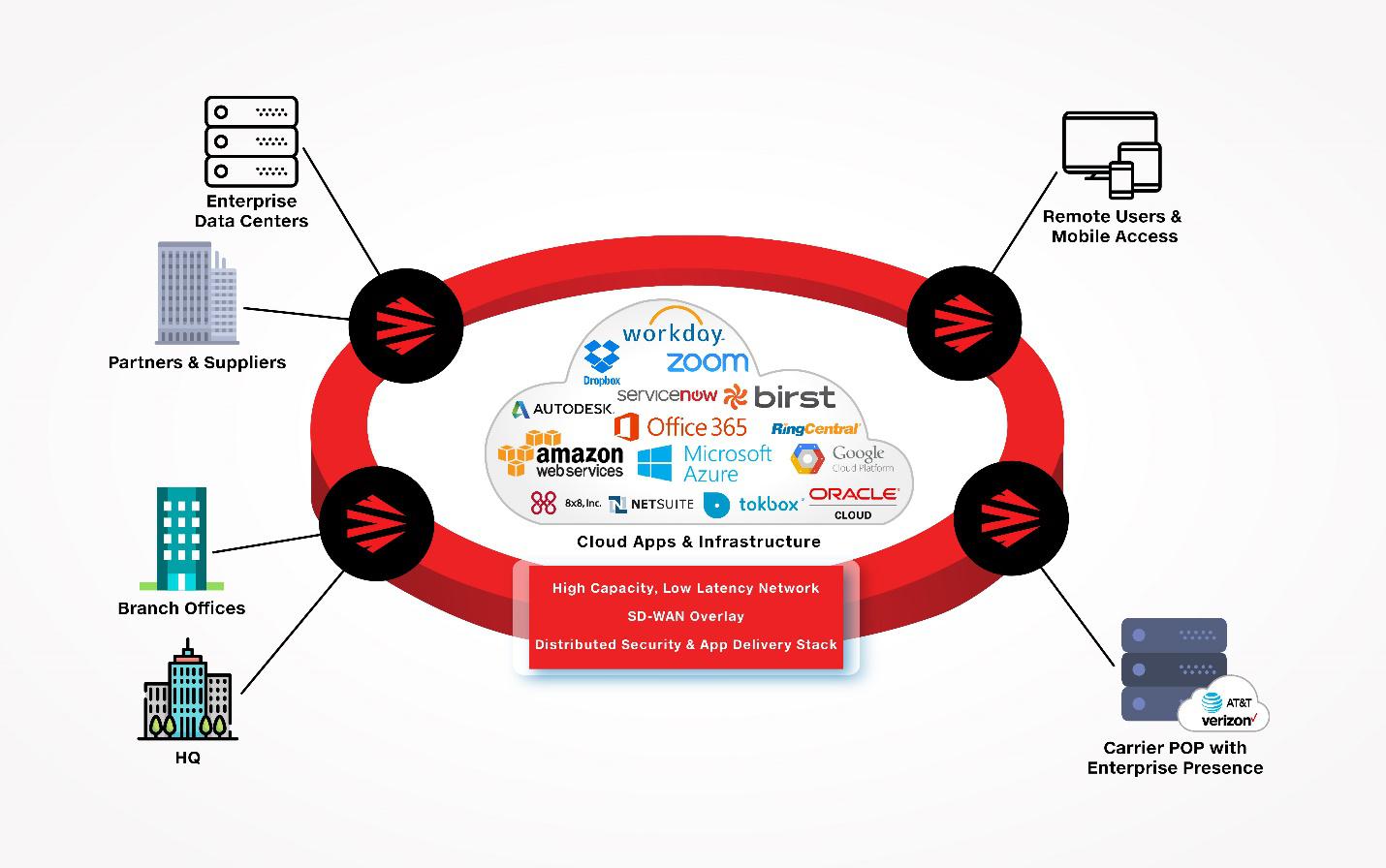
In today’s digital age, the adoption of cloud computing has revolutionised the way businesses operate. Cloud services offer flexibility, scalability, and cost-efficiency, making them a popular choice for organisations of all sizes. However, with the benefits of cloud technology come significant security challenges, particularly in the realm of cloud network security.
Securing Data in Transit and at Rest
One of the primary concerns in cloud network security is ensuring that data is protected both during transmission and while at rest in cloud storage. Encryption plays a crucial role in safeguarding sensitive information from unauthorised access. Implementing strong encryption protocols helps mitigate the risk of data breaches and ensures data confidentiality.
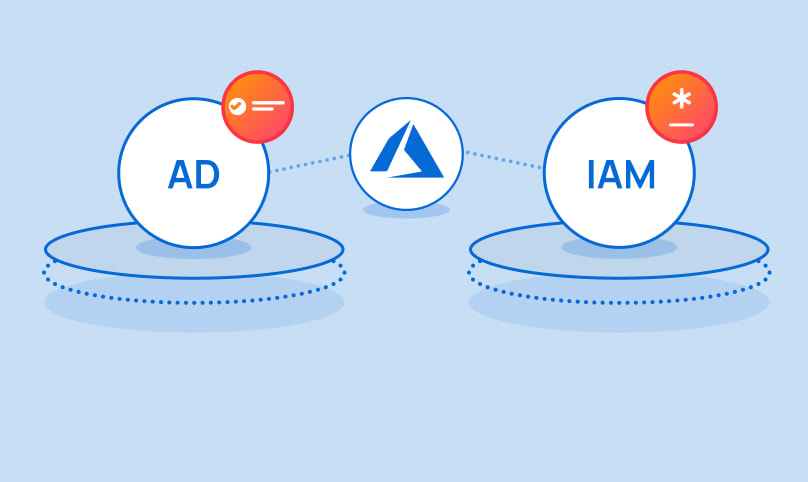
Access Control and Identity Management
Effective access control mechanisms are essential for maintaining the security of cloud networks. Identity and access management (IAM) tools enable organisations to define and enforce policies regarding user permissions and privileges. By implementing robust authentication measures such as multi-factor authentication (MFA), businesses can reduce the likelihood of unauthorised access to cloud resources.
Network Monitoring and Threat Detection
Continuous monitoring of network traffic is vital for detecting potential security threats in a cloud environment. Utilising intrusion detection systems (IDS) and intrusion prevention systems (IPS) helps identify suspicious activities and respond to incidents promptly. Automated threat detection tools can provide real-time alerts to security teams, enabling them to take immediate action to mitigate risks.
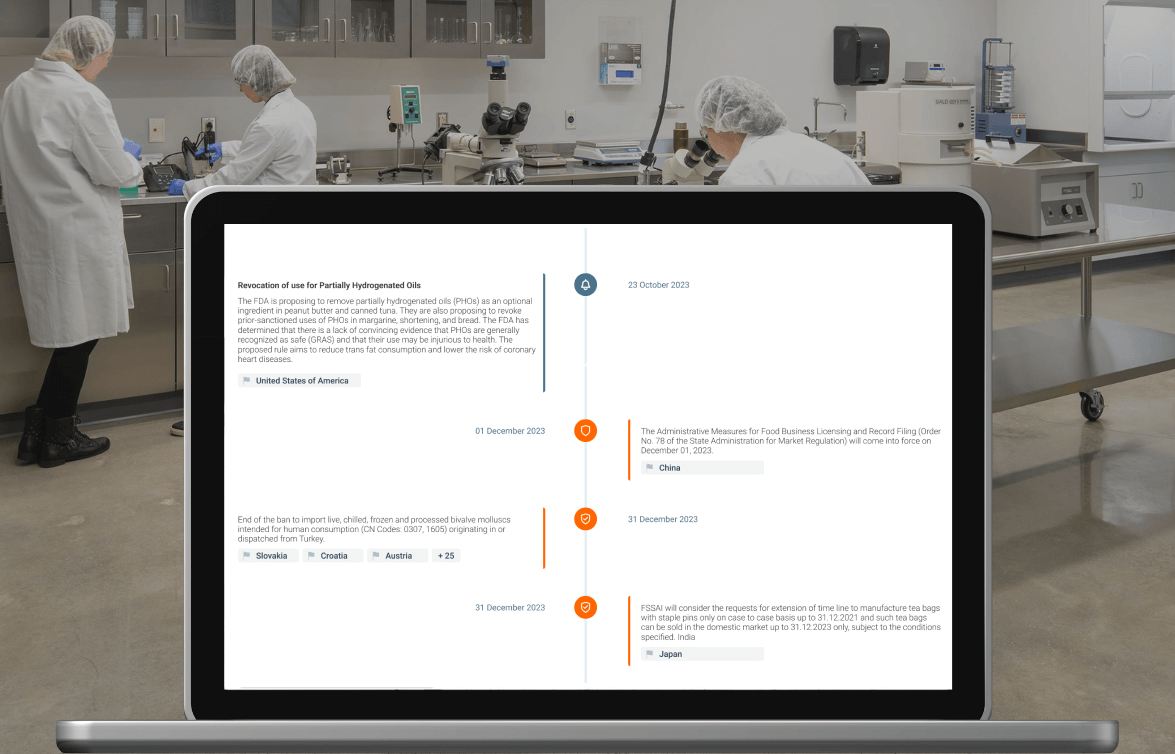
Compliance and Regulatory Requirements
Compliance with industry regulations and data protection laws is a critical aspect of cloud network security. Organisations must adhere to relevant standards such as GDPR, HIPAA, or PCI DSS when storing and processing data in the cloud. Implementing security controls that align with regulatory requirements not only protects sensitive information but also helps build trust with customers and partners.
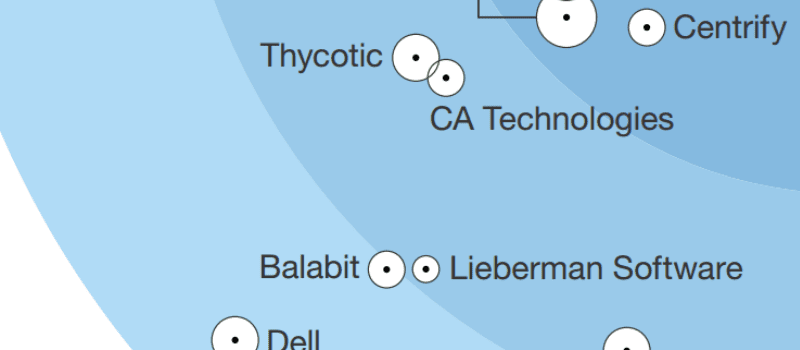
The Future of Cloud Network Security
As cyber threats continue to evolve, so too must cloud network security strategies. Emerging technologies such as artificial intelligence (AI) and machine learning are being leveraged to enhance threat detection capabilities and automate incident response processes. By staying abreast of industry trends and investing in advanced security solutions, businesses can strengthen their defences against cyber attacks in the cloud.
In conclusion, safeguarding cloud networks against cyber threats requires a multi-faceted approach that encompasses encryption, access control, monitoring, compliance, and ongoing innovation. By prioritising cloud network security measures, organisations can protect their data assets, maintain operational resilience, and build a secure foundation for digital transformation.
Understanding Cloud Network Security: Key Questions and Insights
- How do I secure my cloud network?
- What are the 3 categories of cloud security?
- What are types of cloud security?
- What is the difference between cloud and network security?
How do I secure my cloud network?
Securing your cloud network involves implementing a comprehensive set of security measures to protect your data and resources in the cloud. Firstly, ensure strong access controls by managing user permissions and enforcing multi-factor authentication to prevent unauthorised access. Encrypting data both in transit and at rest is crucial for maintaining confidentiality and integrity. Regularly monitor network traffic for suspicious activities using intrusion detection systems and respond promptly to potential threats. Compliance with relevant regulations such as GDPR or PCI DSS is essential to safeguard sensitive information. By combining these strategies with ongoing risk assessment and adopting emerging technologies, you can enhance the security of your cloud network and mitigate cyber risks effectively.
What are the 3 categories of cloud security?
In the realm of cloud network security, understanding the three fundamental categories of cloud security is crucial for safeguarding data and infrastructure in the cloud environment. The first category is data security, which focuses on protecting sensitive information through encryption, access controls, and data loss prevention measures. The second category is network security, which involves securing the communication channels and connections within the cloud infrastructure to prevent unauthorised access and data breaches. Lastly, there is compliance and governance, which pertains to adhering to industry regulations, standards, and best practices to ensure that cloud deployments meet legal requirements and maintain data integrity. By addressing these three key categories of cloud security comprehensively, organisations can establish a robust security posture in the cloud.
What are types of cloud security?
Cloud security encompasses a range of measures and strategies designed to protect data, applications, and infrastructure within cloud environments. Key types of cloud security include data protection, which involves encryption and masking to safeguard sensitive information both in transit and at rest. Identity and access management (IAM) is another crucial type, focusing on ensuring that only authorised users have access to specific resources through authentication methods like multi-factor authentication. Network security is also vital, employing firewalls, intrusion detection systems (IDS), and virtual private networks (VPNs) to prevent unauthorised access and attacks. Additionally, compliance management ensures that cloud services adhere to industry regulations and standards such as GDPR or PCI DSS. Lastly, threat intelligence and monitoring involve continuous surveillance of the cloud environment to detect and respond to potential security threats in real time. Together, these types form a comprehensive approach to safeguarding cloud-based assets against cyber threats.
What is the difference between cloud and network security?
When considering the difference between cloud security and network security, it is essential to understand their respective scopes and focuses. Network security primarily pertains to safeguarding the infrastructure, devices, and communication pathways within an organisation’s local network. This includes implementing firewalls, intrusion detection systems, and VPNs to protect against external threats and unauthorised access. On the other hand, cloud security specifically addresses the unique challenges associated with securing data and applications stored in cloud environments. This involves protecting sensitive information from breaches, ensuring compliance with regulations, and managing access controls within cloud platforms. While network security focuses on on-premises resources, cloud security extends protection to data stored in remote servers accessed via the internet. Both disciplines are integral components of a comprehensive cybersecurity strategy that addresses threats at different levels of an organisation’s IT ecosystem.