The Importance of Access Management in IT Security
Access management is a critical component of maintaining a secure and efficient IT environment. In today’s digital age, where data breaches and cyber threats are prevalent, controlling who has access to what resources within an organisation is paramount to safeguarding sensitive information and preventing unauthorised activities.
What is Access Management?
Access management refers to the process of granting or revoking permissions to users, allowing them to interact with specific systems, applications, or data. It involves defining user roles, setting access levels, enforcing security policies, and monitoring user activities to ensure compliance with organisational rules and regulations.
The Benefits of Effective Access Management
Implementing robust access management practices offers several benefits:
- Enhanced Security: By restricting access to sensitive data only to authorised personnel, organisations can mitigate the risk of data breaches and insider threats.
- Compliance: Access management helps organisations comply with industry regulations and standards by ensuring that only approved individuals can access confidential information.
- Improved Productivity: Streamlining access permissions reduces the time spent on manual access requests and approvals, allowing employees to focus on their core tasks.
- Audit Trails: Monitoring user activities through access management tools provides valuable insights into who accessed what information and when, aiding in forensic investigations and compliance audits.
- Cross-Platform Integration: Access management solutions can be integrated across various platforms and applications, providing a seamless user experience while maintaining security controls.
Best Practices for Access Management
To ensure effective access management, organisations should consider the following best practices:
- User Authentication: Implement multi-factor authentication methods to verify users’ identities before granting access.
- User Provisioning: Automate the process of creating, modifying, and deleting user accounts based on predefined roles and responsibilities.
- Role-Based Access Control (RBAC): Assign permissions based on job roles rather than individual users to simplify access control.
- Regular Reviews: Conduct periodic reviews of user privileges to ensure that they align with current job requirements and responsibilities.
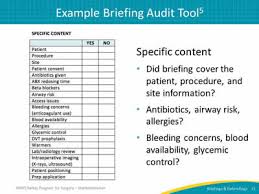
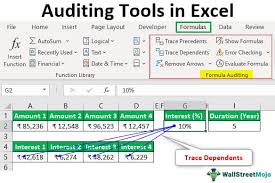
- Auditing and Monitoring: Monitor user activities in real-time and maintain audit logs for accountability and compliance purposes.
In conclusion, effective access management is essential for safeguarding sensitive information, ensuring regulatory compliance, enhancing productivity, and mitigating security risks. By implementing robust access control measures and adhering to best practices, organisations can fortify their IT security posture in an increasingly interconnected digital landscape.
Top 5 Benefits of Effective Access Management for Organisations
- Enhanced security by restricting access to sensitive data only to authorised personnel.
- Compliance with industry regulations and standards through controlled access to confidential information.
- Improved productivity by streamlining access permissions and reducing manual approval processes.
- Creation of audit trails for monitoring user activities and aiding in forensic investigations.
- Seamless integration across platforms and applications for a unified user experience with maintained security controls.
Challenges in Access Management: Navigating Complexity, User Resistance, Costs, Overhead, and Security Misconceptions
Enhanced security by restricting access to sensitive data only to authorised personnel.
One of the key advantages of access management is the bolstering of security through the restriction of sensitive data access exclusively to authorised personnel. By implementing stringent access controls, organisations can significantly reduce the risk of data breaches and insider threats. This proactive approach ensures that confidential information remains protected from unauthorised access, enhancing overall data security and safeguarding critical assets from potential malicious activities.
Compliance with industry regulations and standards through controlled access to confidential information.
Ensuring compliance with industry regulations and standards is a crucial benefit of access management. By controlling access to confidential information and limiting it to authorised personnel only, organisations can adhere to regulatory requirements and uphold industry standards effectively. This proactive approach not only mitigates the risk of non-compliance penalties but also instils trust among stakeholders by demonstrating a commitment to data security and privacy. Access management plays a pivotal role in maintaining the integrity of sensitive information while aligning with the legal frameworks that govern data protection across various sectors.
Improved productivity by streamlining access permissions and reducing manual approval processes.
Improved productivity is a significant benefit of access management, achieved through the streamlining of access permissions and the reduction of manual approval processes. By implementing efficient access controls, organisations can empower employees to swiftly access the resources they need to perform their tasks without unnecessary delays or bureaucratic hurdles. This streamlined approach not only saves time but also enhances overall operational efficiency, allowing staff to focus on their core responsibilities and contribute more effectively to the organisation’s goals.
Creation of audit trails for monitoring user activities and aiding in forensic investigations.
The creation of audit trails through access management plays a crucial role in monitoring user activities and assisting in forensic investigations. By maintaining detailed records of who accessed what information and when, organisations can track user behaviour, detect anomalies, and investigate security incidents effectively. These audit trails not only provide transparency and accountability but also serve as valuable evidence in identifying the source of breaches or unauthorised access, helping organisations enhance their overall security posture and compliance efforts.
Seamless integration across platforms and applications for a unified user experience with maintained security controls.
Seamless integration across platforms and applications is a key advantage of access management, enabling organisations to provide a unified user experience while upholding stringent security controls. By implementing access management solutions that can span multiple systems and applications, businesses can streamline user interactions, simplify authentication processes, and ensure consistent security protocols across their entire IT infrastructure. This seamless integration not only enhances user productivity and satisfaction but also strengthens overall security measures by maintaining a cohesive approach to access control and data protection across diverse platforms.
Complexity
The complexity associated with implementing and managing access management systems poses a significant challenge for organisations. It demands a high level of expertise and dedicated resources to navigate the intricacies of setting up and maintaining effective access controls. From defining user roles and permissions to integrating access management across multiple platforms, the intricacy of these systems can lead to potential errors, delays, and increased operational costs. Balancing security requirements with user convenience while ensuring compliance further adds to the complexity, making it essential for organisations to invest in skilled professionals and robust resources to address this con effectively.
User Resistance
User resistance is a common con of access management within organisations. Employees may push back against access restrictions that impose limitations on their flexibility or convenience. When users feel that their ability to perform tasks efficiently is hindered by stringent access controls, they may become frustrated and less inclined to comply with security protocols. This resistance can create challenges for IT administrators in enforcing access policies and maintaining a secure environment, highlighting the importance of striking a balance between security measures and user convenience to ensure successful implementation of access management strategies.
Cost
One notable drawback of access management is the financial aspect, particularly the costs involved. Implementing access management solutions often requires a substantial initial investment in software, hardware, and implementation services. Additionally, ongoing maintenance expenses for updates, licensing fees, and staff training can further strain the budget. The financial burden of access management can be a deterrent for some organisations, especially smaller businesses with limited resources, making it challenging to fully embrace comprehensive access control measures despite their importance in enhancing security and compliance.
Overhead
One significant drawback of access management is the potential for increased administrative overhead. The process of maintaining access controls, including tasks like user provisioning and role management, can be time-consuming and resource-intensive for organisations. This administrative burden may lead to delays in granting access permissions, complexities in managing user roles, and challenges in keeping up with evolving security requirements. The overhead associated with access management can strain IT resources and impact operational efficiency, highlighting the need for streamlined processes and automation to alleviate this con.
False Sense of Security
Relying solely on access management measures can lead to a false sense of security within an organisation. While access controls are crucial in restricting user permissions and data access, they are not foolproof against all security threats. Overemphasis on access management may overshadow other potential vulnerabilities that could be exploited by malicious actors. It is essential for organisations to adopt a holistic approach to cybersecurity that addresses various layers of protection to effectively mitigate risks and safeguard sensitive information from evolving cyber threats.