The Importance of GRC (Governance, Risk, and Compliance) in Modern Business
In today’s complex business landscape, organisations face a myriad of challenges related to governance, risk management, and compliance. GRC, which stands for Governance, Risk, and Compliance, is a holistic approach that helps businesses navigate these challenges effectively.
What is GRC?
GRC encompasses the processes and practices that organisations implement to align their operations with regulatory standards, manage risks effectively, and ensure proper governance structures are in place. It involves a strategic framework that integrates various aspects of an organisation’s operations to achieve optimal performance while maintaining compliance with laws and regulations.
The Role of GRC in Business Operations
Effective GRC practices are crucial for businesses of all sizes as they help in:
- Enhancing Decision-Making: By providing a comprehensive view of risks and compliance requirements, GRC enables informed decision-making at all levels of the organisation.
- Improving Operational Efficiency: Streamlining processes through GRC frameworks can lead to increased efficiency and reduced costs.
- Managing Risks Proactively: Identifying potential risks early on allows organisations to take proactive measures to mitigate them before they escalate.
- Ensuring Regulatory Compliance: Staying compliant with industry regulations is essential for avoiding penalties and maintaining trust with stakeholders.
- Promoting Accountability: Clear governance structures established through GRC promote accountability among employees and stakeholders.
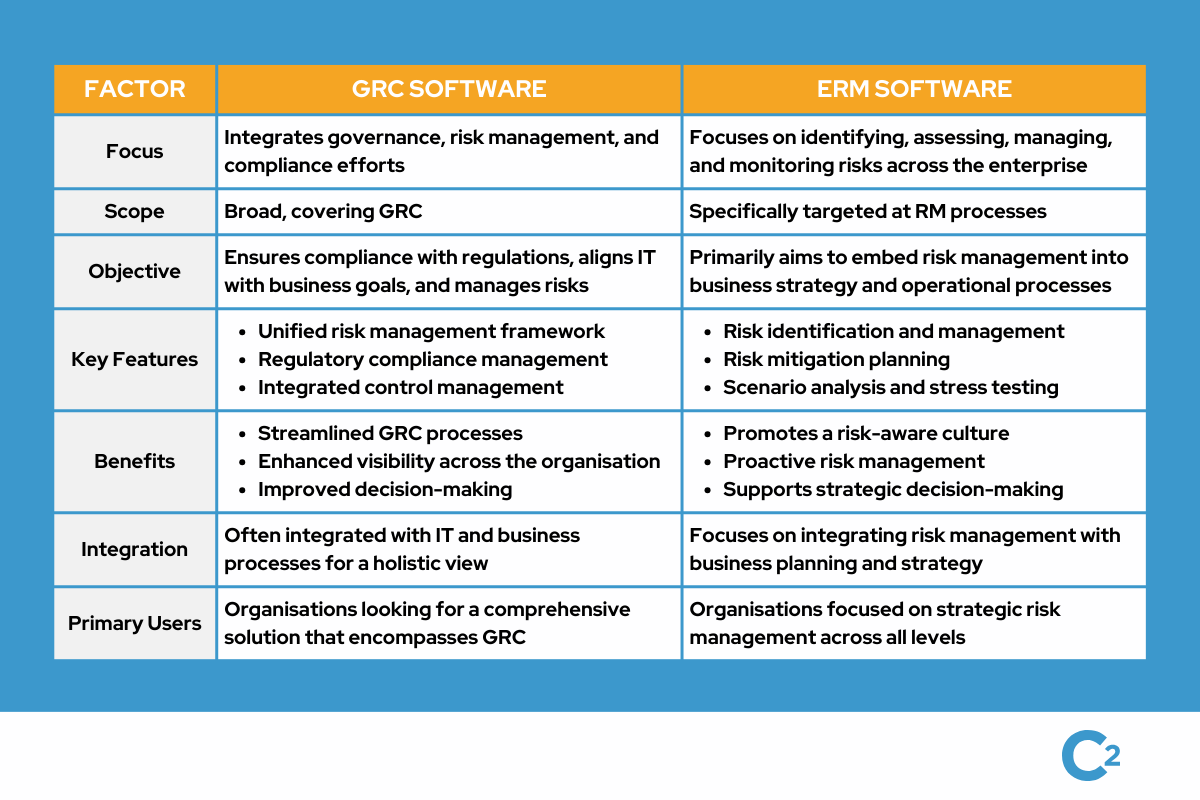
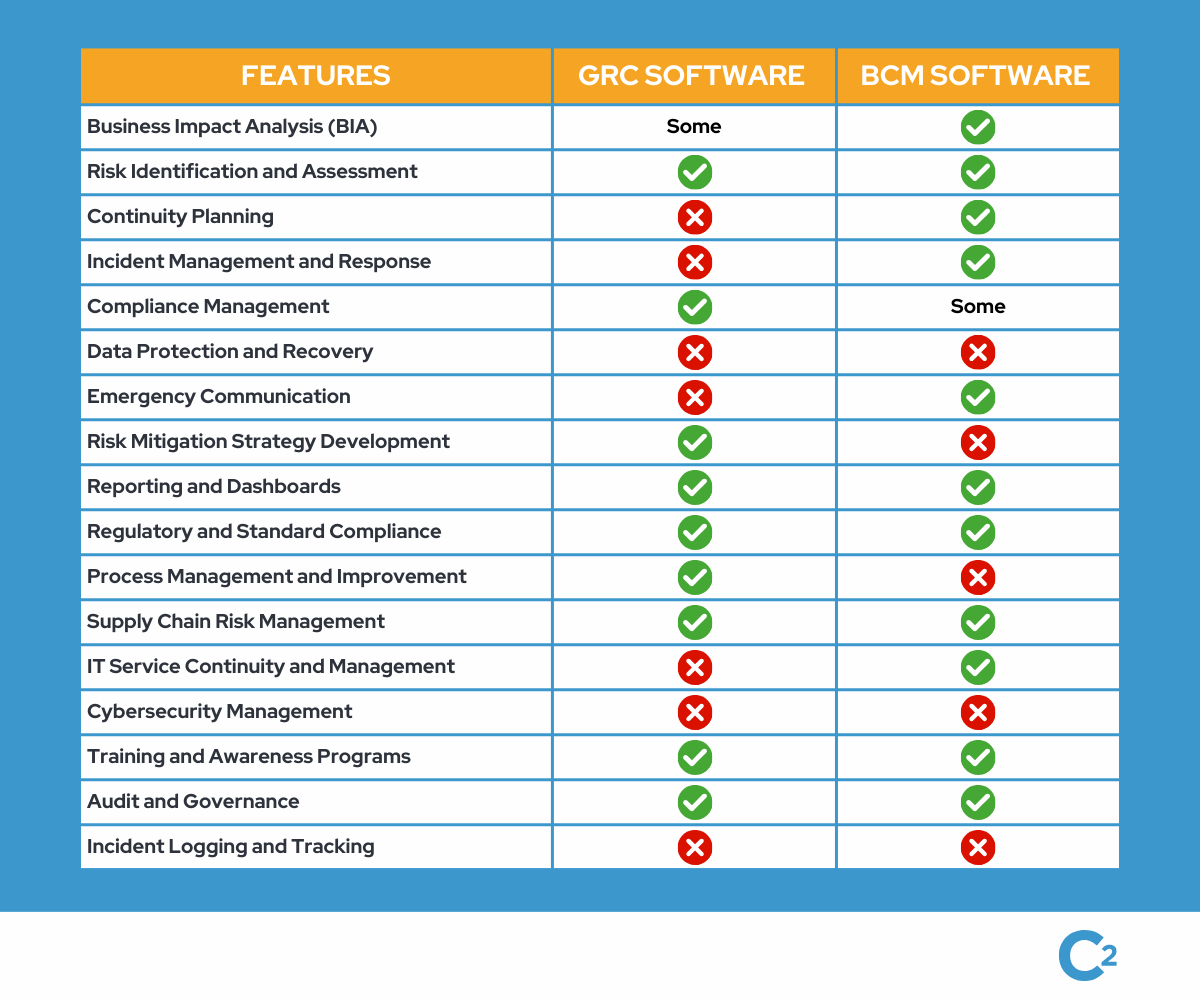
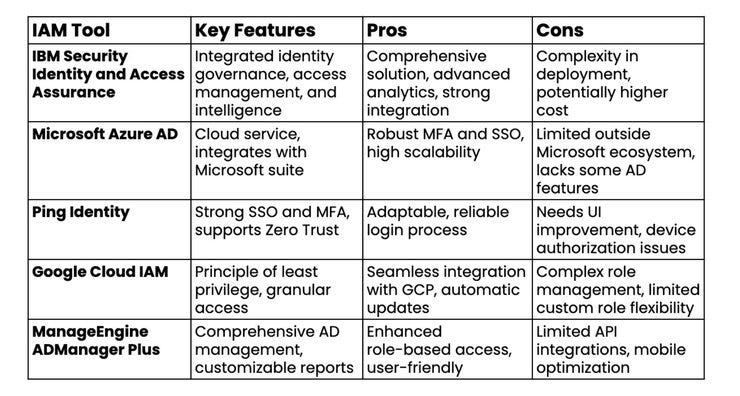
GRC Technology Solutions
To support effective GRC implementation, many organisations leverage technology solutions such as GRC software platforms. These tools help automate compliance monitoring, risk assessment processes, policy management, and reporting functions. By centralising GRC activities on a single platform, organisations can streamline their operations and enhance visibility into key risk areas.
The Future of GRC
As businesses continue to face evolving regulatory landscapes and increasing cyber threats, the role of GRC will become even more critical. Organisations that prioritise robust GRC frameworks will be better equipped to navigate uncertainties and safeguard their operations in an ever-changing environment.
9 Essential Tips for Effective Governance, Risk, and Compliance Management
- Regularly assess and identify potential risks in your organisation.
- Establish clear policies and procedures for governance, risk management, and compliance.
- Ensure that all employees are trained on risk awareness and compliance requirements.
- Implement robust controls to mitigate identified risks effectively.
- Monitor and review compliance with regulations and internal policies on a regular basis.
- Maintain accurate records of risk assessments, compliance activities, and incidents.
- Stay informed about changes in regulations that may impact your business operations.
- Encourage a culture of transparency, accountability, and ethical behaviour within the organisation.
- Regularly review and update your risk management and compliance strategies to adapt to evolving threats.
Regularly assess and identify potential risks in your organisation.
Regularly assessing and identifying potential risks within your organisation is a fundamental aspect of effective GRC risk and compliance management. By conducting thorough risk assessments on a consistent basis, businesses can proactively identify vulnerabilities, anticipate challenges, and implement mitigation strategies to safeguard their operations. This proactive approach not only helps in preventing potential issues from escalating but also allows organisations to stay ahead of regulatory requirements and industry standards, ultimately strengthening their overall risk management framework.
Establish clear policies and procedures for governance, risk management, and compliance.
Establishing clear policies and procedures for governance, risk management, and compliance is a fundamental tip in effective GRC implementation. These guidelines provide a structured framework for decision-making, outlining roles and responsibilities, defining risk tolerance levels, and ensuring adherence to regulatory requirements. Clear policies help standardise operations across the organisation, promote transparency, and facilitate accountability among employees. By establishing robust policies and procedures, businesses can proactively manage risks, enhance operational efficiency, and demonstrate a commitment to ethical practices and regulatory compliance.
Ensure that all employees are trained on risk awareness and compliance requirements.
It is essential to ensure that all employees receive comprehensive training on risk awareness and compliance requirements within the GRC framework. By equipping staff with the necessary knowledge and skills, organisations can foster a culture of accountability and proactive risk management. Training programmes should cover key areas such as identifying potential risks, understanding regulatory obligations, and adhering to internal policies. Through continuous education and reinforcement of these principles, employees become valuable assets in upholding effective governance, risk management, and compliance practices across the organisation.
Implement robust controls to mitigate identified risks effectively.
To enhance GRC risk and compliance practices, it is crucial for organisations to implement robust controls that effectively mitigate identified risks. By establishing stringent control measures tailored to address specific risks, businesses can proactively manage potential threats and vulnerabilities. These controls not only help in reducing the likelihood of risk occurrence but also enable organisations to respond swiftly and decisively in case of any incidents. Implementing robust controls demonstrates a commitment to maintaining a secure and compliant operational environment, ultimately safeguarding the organisation’s reputation and ensuring long-term sustainability.
Monitor and review compliance with regulations and internal policies on a regular basis.
It is essential for organisations to maintain a proactive approach towards GRC risk and compliance by regularly monitoring and reviewing adherence to both external regulations and internal policies. By conducting regular assessments, businesses can identify any deviations from established standards, address potential compliance gaps, and take corrective actions promptly. This ongoing monitoring ensures that the organisation remains aligned with legal requirements and internal guidelines, mitigating risks and enhancing overall governance effectiveness.
Maintain accurate records of risk assessments, compliance activities, and incidents.
It is essential for organisations to maintain accurate records of risk assessments, compliance activities, and incidents as part of their GRC (Governance, Risk, and Compliance) practices. By documenting these key aspects, businesses can track their progress in managing risks, ensuring regulatory compliance, and responding to incidents effectively. Accurate records not only provide a historical perspective on past actions but also serve as valuable resources for future decision-making and audit purposes. Keeping detailed and up-to-date records demonstrates a commitment to transparency, accountability, and continuous improvement in GRC processes.
Stay informed about changes in regulations that may impact your business operations.
Staying informed about changes in regulations that may impact your business operations is a crucial tip in GRC risk and compliance management. By keeping abreast of regulatory updates, businesses can proactively adjust their policies and practices to ensure compliance and mitigate potential risks. Failure to stay informed about regulatory changes could lead to non-compliance issues, financial penalties, and reputational damage. Therefore, maintaining a vigilant approach to monitoring and understanding evolving regulations is essential for maintaining a strong GRC framework that supports sustainable business operations.
Encourage a culture of transparency, accountability, and ethical behaviour within the organisation.
Encouraging a culture of transparency, accountability, and ethical behaviour within the organisation is a fundamental tip in GRC risk and compliance. By fostering an environment where employees feel empowered to communicate openly, take responsibility for their actions, and uphold ethical standards, businesses can strengthen their governance practices and mitigate risks effectively. This culture not only promotes trust among stakeholders but also ensures that compliance requirements are met consistently. Emphasising transparency, accountability, and ethical behaviour cultivates a positive work environment where integrity is valued and decision-making is guided by ethical principles, ultimately contributing to the overall success and sustainability of the organisation.
Regularly review and update your risk management and compliance strategies to adapt to evolving threats.
It is essential for organisations to regularly review and update their risk management and compliance strategies to adapt to evolving threats in the dynamic business environment. By staying proactive and responsive to emerging risks, businesses can strengthen their resilience and ensure ongoing compliance with regulatory requirements. Regular assessments of risk factors and compliance frameworks enable organisations to identify vulnerabilities, implement necessary controls, and adjust strategies accordingly to mitigate potential threats effectively. Embracing a culture of continuous improvement in GRC practices is key to safeguarding business operations and maintaining a competitive edge in today’s challenging landscape.