The Importance of STM Software in Academic Publishing
In the realm of academic publishing, Science, Technology, and Medicine (STM) play a crucial role in advancing knowledge and disseminating research findings. STM software has become an indispensable tool for researchers, publishers, and institutions alike, revolutionising the way scholarly content is created, reviewed, and distributed.
Enhancing Collaboration and Efficiency
STM software facilitates seamless collaboration among researchers by providing a platform for sharing data, collaborating on manuscripts, and reviewing each other’s work. This collaborative approach not only accelerates the research process but also ensures that findings are rigorously evaluated before publication.
Streamlining Peer Review Processes
Peer review is a cornerstone of academic publishing, ensuring the quality and credibility of scholarly articles. STM software streamlines the peer review process by automating manuscript submission, reviewer assignment, and feedback collection. This not only expedites the publication timeline but also improves the overall quality of published research.
Ensuring Compliance and Accessibility
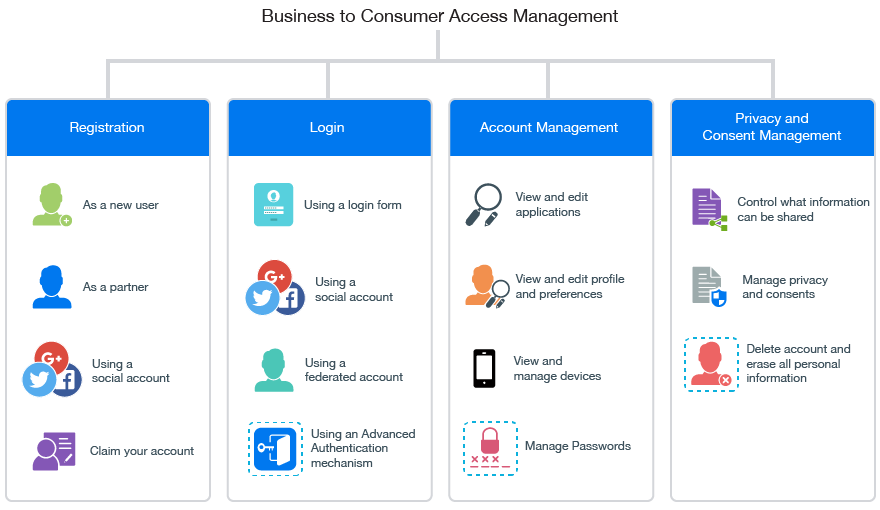
STM software plays a vital role in ensuring compliance with industry standards and regulations. From data privacy to copyright management, these tools help publishers adhere to best practices and legal requirements. Additionally, STM software enhances accessibility by providing digital archives of scholarly content that can be easily searched, accessed, and cited by researchers worldwide.
Driving Innovation in Publishing
With the rapid advancements in technology, STM software continues to drive innovation in academic publishing. From artificial intelligence-powered manuscript screening to interactive data visualisations in research articles, these tools are reshaping how scholarly content is created and consumed. By embracing these technological advancements, publishers can stay ahead of the curve and deliver cutting-edge research to their audiences.
The Future of STM Software
As the landscape of academic publishing evolves, so too will STM software. With an increasing focus on open access publishing, data sharing initiatives, and transparent peer review processes, these tools will continue to adapt to meet the changing needs of researchers and readers alike. The future of STM software holds promise for greater collaboration, efficiency, and innovation in scholarly communication.
In conclusion, STM software has become an essential component of modern academic publishing. By leveraging these tools effectively, publishers can enhance collaboration among researchers, streamline peer review processes, ensure compliance with regulations, and drive innovation in the dissemination of scholarly content. As we look towards the future of academic publishing, it is clear that STM software will play a pivotal role in shaping the way research is conducted and shared globally.
Common Questions About STM Software and Hardware: A Quick Guide
- What is STM processor?
- Is STM32 in C or C++?
- What is the cost of STM typing software?
- What is STM chip?
- What is STM software?
- Which software is used for STM32?
What is STM processor?
The term “STM processor” refers to a Scalable Tile Manycore processor, which is a type of processor architecture designed for high-performance computing tasks. STM processors are known for their ability to efficiently handle parallel processing and complex computations by utilising multiple cores arranged in a scalable tile configuration. This design allows STM processors to deliver significant computational power while maintaining energy efficiency, making them ideal for applications that require intensive data processing and analysis. Researchers and developers often turn to STM processors for tasks such as scientific simulations, artificial intelligence algorithms, and big data analytics due to their ability to handle large workloads effectively.
Is STM32 in C or C++?
The STM32 microcontroller series is primarily programmed using the C programming language, which is commonly used for embedded systems development. While C++ can also be used to program STM32 microcontrollers, C remains the dominant language due to its efficiency, simplicity, and widespread support in the embedded systems community. Developers can choose between C and C++ based on their project requirements and familiarity with each language’s features and capabilities. Ultimately, both languages are viable options for programming STM32 microcontrollers, offering flexibility and versatility in embedded systems development.
What is the cost of STM typing software?
When considering the cost of STM typing software, it is essential to understand that pricing can vary depending on the specific features, functionalities, and licensing options offered by different providers. Some STM typing software may be available as standalone products with one-time purchase fees, while others may operate on subscription-based models with monthly or annual payments. Additionally, customised solutions or enterprise-level packages tailored to the needs of academic institutions or publishing houses may involve higher costs but offer comprehensive support and scalability. It is advisable to explore various options, request quotes from vendors, and assess the value proposition of each solution to determine the most cost-effective and suitable STM typing software for your requirements.
What is STM chip?
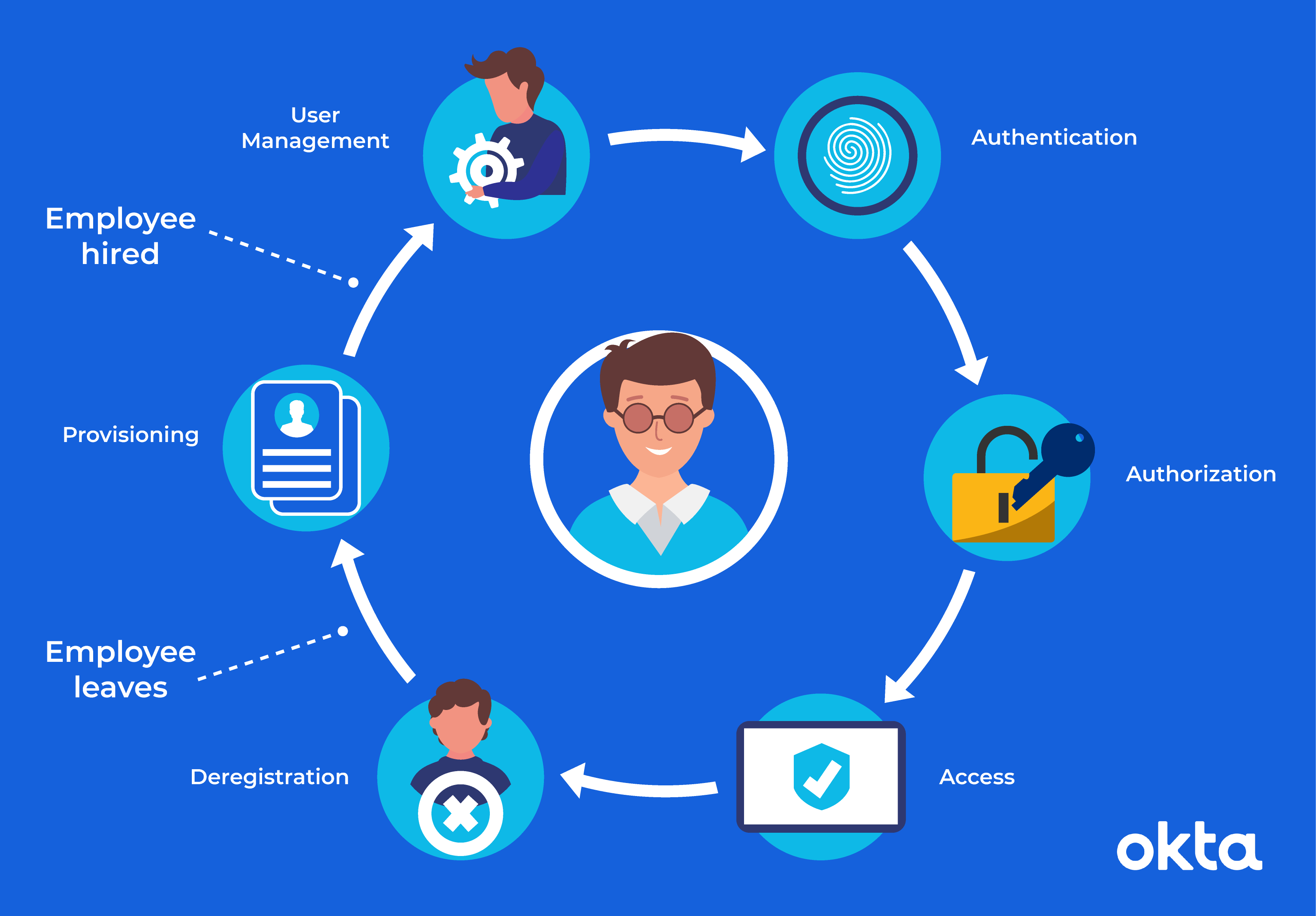
The STM chip, also known as the Security Token Module chip, is a crucial component in cybersecurity systems that provides secure storage and processing of sensitive information. This chip is designed to enhance the security of electronic devices by safeguarding cryptographic keys, authentication data, and other critical information from unauthorised access or tampering. By utilising advanced encryption techniques and secure storage mechanisms, the STM chip plays a vital role in protecting digital assets and ensuring the integrity of data transmissions in various applications, including smart cards, mobile devices, and IoT devices.
What is STM software?
STM software, short for Science, Technology, and Medicine software, is a specialised tool used in academic publishing to streamline the creation, review, and dissemination of scholarly content within these disciplines. It serves as a comprehensive platform that facilitates collaboration among researchers, manages the peer review process efficiently, ensures compliance with industry standards and regulations, and drives innovation in scholarly communication. STM software plays a pivotal role in advancing knowledge and enhancing the accessibility of research findings by providing digital archives of scholarly content that can be easily searched and accessed by researchers worldwide.
Which software is used for STM32?
When it comes to programming and development for STM32 microcontrollers, the most commonly used software is the STM32CubeIDE. This integrated development environment (IDE) is specifically designed by STMicroelectronics to support the entire STM32 portfolio, offering a comprehensive set of tools for coding, compiling, debugging, and deploying applications on STM32 devices. With its user-friendly interface and extensive features tailored for STM32 development, STM32CubeIDE has become a popular choice among developers working with STM32 microcontrollers.