The Importance of Access Control Auditing Software
Access control auditing software plays a crucial role in maintaining the security and integrity of an organisation’s digital assets. In today’s interconnected world, where cyber threats are ever-present, having robust access control measures is essential to prevent unauthorised access and potential data breaches.
What is Access Control Auditing Software?
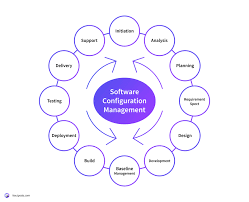
Access control auditing software is a tool that allows organisations to monitor and manage user access to their systems, applications, and data. It provides detailed insights into who has access to what resources, when they accessed them, and what actions they performed. By maintaining a comprehensive audit trail of user activities, organisations can track changes, detect anomalies, and ensure compliance with security policies and regulations.
The Benefits of Access Control Auditing Software
Implementing access control auditing software offers several benefits:
- Enhanced Security: By monitoring user activities in real-time and generating alerts for suspicious behaviour, access control auditing software helps prevent security incidents before they escalate.
- Compliance: Organisations can demonstrate compliance with industry regulations such as GDPR, HIPAA, or PCI DSS by maintaining detailed audit logs of user access and actions.
- Risk Mitigation: Identifying potential security risks and vulnerabilities through regular audits enables proactive risk mitigation strategies to be implemented.
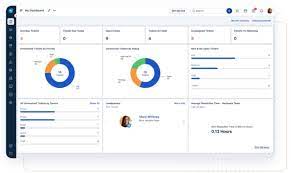
- Operational Efficiency: Streamlining access management processes and automating audit tasks improve operational efficiency and reduce the burden on IT teams.
- Audit Trail: Having a complete audit trail of user activities facilitates forensic investigations in the event of a security incident or data breach.
Choosing the Right Access Control Auditing Software
When selecting access control auditing software for your organisation, consider the following factors:
- Scalability: Ensure that the software can scale with your organisation’s growth and adapt to changing security requirements.
- User-Friendly Interface: Look for intuitive dashboards and reporting tools that make it easy to interpret audit data.
- Integration Capabilities: Choose software that seamlessly integrates with your existing IT infrastructure for smooth implementation.
- Audit Customisation: The ability to customise audit policies based on your unique security needs is essential for effective monitoring.
…
Seven Essential Tips for Enhancing Security with Access Control Auditing Software
- Regularly review and update access control policies.
- Implement role-based access control to assign permissions effectively.
- Monitor user activities and access logs for any suspicious behaviour.
- Ensure segregation of duties to prevent conflicts of interest.
- Utilise automation to streamline auditing processes and improve efficiency.
- Conduct regular audits to identify security gaps and compliance issues.
- Provide training to employees on access control best practices.
Regularly review and update access control policies.
Regularly reviewing and updating access control policies is a fundamental practice in ensuring the effectiveness of access control auditing software. By periodically revisiting and adjusting access control policies, organisations can align security measures with evolving threats and business requirements. This proactive approach not only enhances the accuracy of access permissions but also helps in identifying and addressing potential vulnerabilities before they are exploited. Consistent policy reviews contribute to a more robust security posture, enabling organisations to maintain compliance with regulations and safeguard their sensitive data effectively.
Implement role-based access control to assign permissions effectively.
To enhance security and streamline access management, it is advisable to implement role-based access control when utilising access control auditing software. By assigning permissions based on predefined roles within the organisation, administrators can effectively control who has access to specific resources and functionalities. This approach not only simplifies the process of granting and revoking access but also ensures that users are only granted permissions necessary for their roles, reducing the risk of unauthorised activities and data breaches. Role-based access control promotes a granular level of security while maintaining operational efficiency in managing user privileges within the system.
Monitor user activities and access logs for any suspicious behaviour.
Monitoring user activities and access logs for any suspicious behaviour is a fundamental tip when utilising access control auditing software. By keeping a vigilant eye on the actions of users within the system, organisations can swiftly identify any anomalies or potential security threats. Detecting unusual patterns or unauthorised access attempts allows for prompt intervention to mitigate risks and safeguard sensitive data. This proactive approach to monitoring not only enhances security posture but also helps in maintaining compliance with regulatory requirements by ensuring accountability and transparency in user interactions with critical resources.
Ensure segregation of duties to prevent conflicts of interest.
Ensuring the segregation of duties is a fundamental principle in access control auditing software to prevent conflicts of interest and maintain the integrity of an organisation’s security practices. By assigning specific roles and responsibilities to different individuals, organisations can minimise the risk of fraud, errors, and misuse of privileges. Segregation of duties helps create checks and balances within the system, ensuring that no single individual has excessive control over critical processes or sensitive data. This practice not only enhances security but also promotes accountability and transparency in access management procedures.
Utilise automation to streamline auditing processes and improve efficiency.
By utilising automation in access control auditing software, organisations can streamline their auditing processes and enhance overall efficiency. Automation enables the software to perform routine tasks such as log collection, analysis, and reporting without manual intervention, saving time and reducing the risk of human error. By automating repetitive tasks, IT teams can focus on more strategic security initiatives while ensuring that audit activities are consistently and accurately carried out. This not only improves operational efficiency but also enhances the organisation’s ability to proactively monitor access control measures and respond promptly to security incidents.
Conduct regular audits to identify security gaps and compliance issues.
Conducting regular audits using access control auditing software is a proactive approach to identifying potential security gaps and ensuring compliance with regulatory requirements. By systematically reviewing user access permissions, monitoring activity logs, and analysing audit trails, organisations can pinpoint vulnerabilities and address them before they are exploited by malicious actors. These audits not only enhance the overall security posture of the IT environment but also demonstrate a commitment to maintaining data integrity and protecting sensitive information from unauthorised access.
Provide training to employees on access control best practices.
Providing training to employees on access control best practices is essential in ensuring the effective implementation of access control auditing software. Educating staff members on the importance of securely managing their access rights, following password protocols, and recognising potential security threats can significantly enhance the overall security posture of an organisation. By empowering employees with the knowledge and skills to navigate access control systems responsibly, businesses can minimise the risk of insider threats and data breaches, ultimately contributing to a more secure and resilient IT environment.