The Evolution and Impact of Software Applications
In the digital era, software applications have become an integral part of both personal and professional spheres. From the early days of simple calculators and word processors to today’s advanced cloud-based solutions, software applications have undergone a remarkable transformation.
What Are Software Applications?
Software applications, often simply referred to as ‘apps’, are computer programs designed to carry out specific tasks for users. These tasks can range from editing documents to managing business operations. Applications are built on a set of coded instructions that tell the hardware of a device how to operate.
The Early Days
The inception of software applications dates back to the creation of computers themselves. Early software was developed primarily for large organisations with complex computational needs. These were custom-built and ran on mainframe computers, which were expensive and required specialised knowledge to operate.
The Personal Computer Revolution
The launch of personal computers (PCs) in the 1970s marked a significant shift in software development. As PCs became more affordable, there was a surge in demand for user-friendly applications that could be used by individuals without technical expertise. This led to the creation of iconic software like Microsoft Word and Excel, which revolutionised how people worked.
From Desktops to Mobile Devices
With the advent of the internet and mobile technology, software applications took on new forms. Web-based apps allowed users to perform tasks online without downloading software locally, while mobile apps brought about unprecedented convenience by making services available at one’s fingertips.
Impact on Business
Software applications have had a profound impact on businesses by streamlining operations, improving customer engagement, and enabling remote work. Enterprise Resource Planning (ERP) systems and Customer Relationship Management (CRM) tools are just two examples that have transformed business processes.
Impact on Society
Social media platforms like Facebook and Twitter are powerful examples of how software applications can influence society by connecting people worldwide and facilitating real-time communication.
The Future: AI and Machine Learning
The future trajectory of software applications is closely tied with advancements in artificial intelligence (AI) and machine learning (ML). These technologies allow apps to learn from user interactions, predict needs, automate tasks, and provide personalised experiences.
Privacy Concerns
As software applications continue to evolve, privacy remains a paramount concern. With apps collecting vast amounts of data, developers and regulators must work together to protect user information from misuse.
Sustainability
Another consideration is sustainability; as digital solutions become more prevalent, their environmental impact cannot be ignored. Developers are now focusing on creating energy-efficient apps that minimise carbon footprints.
Conclusion
In conclusion, software applications have come a long way since their inception. They’ve evolved from niche computational tools into ubiquitous elements that shape our daily lives. As they continue to advance with new technologies like AI and ML, it is crucial for developers, users, businesses, and regulators alike to navigate these changes responsibly—balancing innovation with ethical considerations such as privacy protection and environmental sustainability.
Five Essential Tips for Optimal Software Application Use and Security
- Ensure regular software updates to benefit from the latest features and security patches.
- Back up your data regularly to prevent loss in case of system failures or errors.
- Choose software applications that are user-friendly and intuitive for improved efficiency.
- Protect your software with strong passwords and consider enabling two-factor authentication for added security.
- Explore online tutorials and resources to enhance your knowledge and skills in using different software applications.
Ensure regular software updates to benefit from the latest features and security patches.
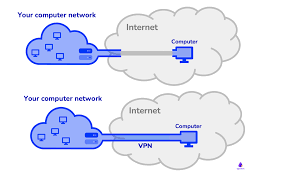
To maximise the efficiency and security of your software applications, it is essential to prioritise regular updates. By staying current with the latest updates, you not only gain access to new features and enhancements but also ensure that your applications are fortified with the latest security patches. This proactive approach helps to safeguard your systems against potential vulnerabilities and cyber threats, providing a more robust and reliable user experience.
Back up your data regularly to prevent loss in case of system failures or errors.
It is crucial to regularly back up your data to safeguard against potential loss due to system failures or errors. By creating routine backups of your important files and information, you can ensure that even in the event of a technical issue, such as hardware malfunctions or software errors, your data remains safe and accessible. Implementing a robust backup strategy not only provides peace of mind but also serves as a proactive measure to protect your valuable digital assets from unforeseen circumstances.
Choose software applications that are user-friendly and intuitive for improved efficiency.
Selecting software applications that prioritise user-friendliness and intuitive design can significantly enhance operational efficiency. When users can navigate and utilise an application with ease, they are more likely to complete tasks efficiently and accurately. Intuitive software reduces the learning curve, minimises errors, and boosts productivity by allowing users to focus on their work rather than struggling with complex interfaces. By choosing applications that are user-friendly, organisations can empower their employees to work more effectively and achieve better results in less time.
Protect your software with strong passwords and consider enabling two-factor authentication for added security.
To enhance the security of your software application, it is crucial to safeguard access with robust passwords and consider implementing two-factor authentication for an additional layer of protection. Strong passwords that are unique and complex can significantly reduce the risk of unauthorised access to your application. Two-factor authentication adds an extra level of security by requiring users to provide a second form of verification, such as a code sent to their mobile device, in addition to their password. By incorporating these security measures, you can better protect your software application from potential threats and ensure the confidentiality and integrity of your data.
Explore online tutorials and resources to enhance your knowledge and skills in using different software applications.
To enhance your knowledge and proficiency in using various software applications, consider exploring online tutorials and resources. These valuable tools offer step-by-step guidance, tips, and tricks to help you navigate through different features and functionalities effectively. By dedicating time to learning from online resources, you can expand your skill set, boost productivity, and stay updated on the latest trends in software applications. Whether you are a beginner or an experienced user, continuous learning through online tutorials can empower you to maximise the potential of software applications in your personal and professional endeavours.