The Importance of Networks in Today’s Digital World
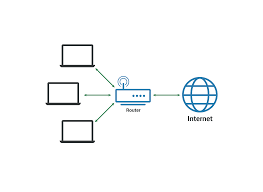
In today’s interconnected world, networks play a crucial role in enabling communication and data exchange across various devices and systems. A network can be defined as a collection of computers, servers, mainframes, network devices, and other interconnected devices that allow them to communicate with each other.
Networks are the backbone of modern technology infrastructure, facilitating the transfer of information and resources between users and systems. They can be classified into different types based on their size, scope, and purpose. Local Area Networks (LANs) connect devices within a limited geographical area such as an office building, while Wide Area Networks (WANs) span larger distances and connect multiple LANs across different locations.
One of the key benefits of networks is their ability to enhance collaboration and productivity. By enabling seamless communication between individuals and systems, networks empower organisations to share information efficiently, streamline processes, and improve decision-making. This connectivity is essential for businesses looking to stay competitive in today’s fast-paced digital landscape.
Moreover, networks play a vital role in enabling access to the internet and cloud services. With the rise of cloud computing, organisations can leverage network infrastructure to access scalable resources on-demand, store data securely off-site, and deploy applications globally. This flexibility allows businesses to adapt to changing market demands and scale their operations effectively.
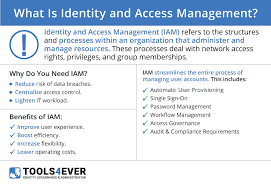
Security is another critical aspect of networks that cannot be overlooked. With cyber threats becoming increasingly sophisticated, it is essential for organisations to implement robust network security measures to protect sensitive data and prevent unauthorised access. Firewalls, encryption protocols, intrusion detection systems, and regular security audits are some of the tools used to safeguard network infrastructure from cyber attacks.
In conclusion, networks form the foundation of modern digital ecosystems by facilitating communication, collaboration, access to resources, and security measures. As technology continues to evolve rapidly, the importance of robust network infrastructure will only grow stronger in ensuring connectivity and efficiency across various industries.
6 Essential Tips for Safeguarding Your Network
- Ensure your network is secure by using strong passwords and encryption.
- Regularly update your network devices’ firmware to protect against vulnerabilities.
- Implement access controls to restrict unauthorized users from accessing your network.
- Monitor your network traffic for any suspicious activities or potential security breaches.
- Backup your important data regularly to prevent data loss in case of a network failure.
- Consider using a virtual private network (VPN) for secure remote access to your network.
Ensure your network is secure by using strong passwords and encryption.
To ensure the security of your network, it is essential to implement robust measures such as using strong passwords and encryption. Strong passwords that are complex and unique help prevent unauthorised access to sensitive data and systems. Additionally, encryption adds an extra layer of protection by encoding information transmitted over the network, making it unreadable to anyone without the decryption key. By incorporating these security practices, you can significantly reduce the risk of cyber threats and safeguard your network from potential vulnerabilities.
Regularly update your network devices’ firmware to protect against vulnerabilities.
Regularly updating your network devices’ firmware is a crucial step in safeguarding your network against potential vulnerabilities. Firmware updates often contain patches and security enhancements that address known weaknesses and protect your devices from exploitation by cyber threats. By staying proactive and ensuring that your network devices are running the latest firmware versions, you can significantly reduce the risk of security breaches and enhance the overall resilience of your network infrastructure.
Implement access controls to restrict unauthorized users from accessing your network.
Implementing access controls is a fundamental step in safeguarding your network from potential security threats. By setting up restrictions to prevent unauthorised users from accessing sensitive resources, you can significantly reduce the risk of data breaches and cyber attacks. Access controls allow you to define user permissions, authentication mechanisms, and encryption protocols to ensure that only authorised individuals can enter your network. This proactive approach not only enhances the overall security posture of your network but also helps maintain compliance with data protection regulations.
Monitor your network traffic for any suspicious activities or potential security breaches.
Monitoring your network traffic for any suspicious activities or potential security breaches is a crucial aspect of maintaining a secure and efficient network infrastructure. By regularly analysing the data flow within your network, you can proactively identify unusual patterns, unauthorised access attempts, or any signs of malicious activity that may indicate a security threat. Implementing robust monitoring tools and protocols allows you to detect and respond to potential breaches promptly, minimising the risk of data loss, system downtime, or other detrimental consequences. Stay vigilant and proactive in monitoring your network traffic to safeguard your digital assets and protect against cyber threats.
Backup your important data regularly to prevent data loss in case of a network failure.
Regularly backing up your important data is a crucial precautionary measure to safeguard against potential data loss in the event of a network failure. By creating backups of your critical information and storing them securely, you can mitigate the risks associated with unexpected network disruptions or outages. This proactive approach ensures that even if a network failure occurs, you can quickly recover and restore your data, minimising downtime and preserving business continuity. Remember, prevention through regular backups is key to maintaining the integrity and availability of your valuable information assets.
Consider using a virtual private network (VPN) for secure remote access to your network.
When looking to enhance the security of remote access to your network, it is advisable to consider implementing a virtual private network (VPN). By utilising a VPN, you can create a secure and encrypted connection between remote devices and your network, ensuring that sensitive data transmitted over the internet remains protected from potential threats. VPNs provide an additional layer of security by masking the user’s IP address and encrypting data traffic, making it challenging for cybercriminals to intercept or eavesdrop on communications. This proactive measure not only safeguards your network from unauthorised access but also offers peace of mind when accessing critical resources remotely.