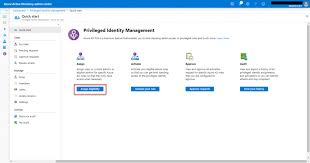
Azure AD Privileged Identity Management: Enhancing Security in the Cloud
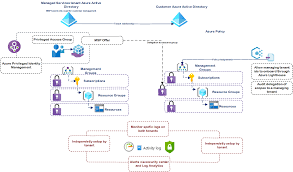
In today’s digital landscape, securing privileged identities is crucial for safeguarding sensitive data and preventing cyber threats. Azure Active Directory (Azure AD) Privileged Identity Management (PIM) is a powerful tool that helps organisations manage, control, and monitor access to critical resources within their Azure environment.
What is Azure AD Privileged Identity Management?
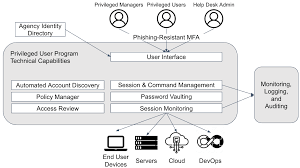
Azure AD PIM enables organisations to manage and monitor access to privileged roles in Azure AD, Azure resources, and other Microsoft Online Services. By using Azure AD PIM, administrators can enforce just-in-time access, multi-factor authentication, and approval workflows for users requesting elevated permissions.
Key Features of Azure AD PIM:
- Just-In-Time Access: Users can request privileged roles for a limited duration, reducing the risk of long-term exposure.
- Multi-Factor Authentication: Additional layer of security to verify the identity of users accessing privileged roles.
- Approval Workflows: Requests for elevated permissions can be routed to designated approvers for review and authorisation.
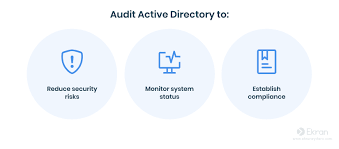
- Audit Logs: Detailed logs capture all changes made by users with privileged access, aiding in compliance and security investigations.
- Schedule Reviews: Regular reviews of privileged roles ensure that only authorised users have access to critical resources.
The Benefits of Using Azure AD PIM:
Azure AD PIM offers several benefits to organisations looking to enhance their security posture:
- Reduced Exposure: Just-in-time access minimises the risk of prolonged exposure to elevated permissions.
- Improved Compliance: Audit logs and role reviews help organisations meet regulatory requirements and internal policies.
- Elevated Security: Multi-factor authentication adds an extra layer of protection against unauthorised access.
- Easier Monitoring: Centralised dashboard provides visibility into who has access to what resources and when.
In Conclusion
Azure AD Privileged Identity Management is a valuable tool for organisations seeking to strengthen their security posture in the cloud. By implementing just-in-time access, multi-factor authentication, approval workflows, and audit capabilities, organisations can effectively manage and monitor privileged identities within their Azure environment. With Azure AD PIM, businesses can reduce risks associated with elevated permissions while maintaining compliance with industry regulations.
Top 8 Benefits of Azure AD Privileged Identity Management for Enhanced Security and Compliance
- Enhances security by enforcing just-in-time access to privileged roles.
- Reduces the risk of prolonged exposure to elevated permissions.
- Provides multi-factor authentication for added security.
- Offers approval workflows for reviewing and authorising access requests.
- Facilitates regular reviews of privileged roles to ensure compliance.
- Generates detailed audit logs for tracking changes made by users with privileged access.
- Centralised dashboard provides visibility into who has access to critical resources.
- Helps organisations meet regulatory requirements and internal security policies.
Challenges of Azure AD Privileged Identity Management: Configuration, Costs, Adoption, and Customisation
Enhances security by enforcing just-in-time access to privileged roles.
Azure AD Privileged Identity Management enhances security by enforcing just-in-time access to privileged roles. This proactive approach ensures that users only have temporary access to elevated permissions when needed, reducing the risk of prolonged exposure and potential misuse of privileges. By granting access on a temporary basis, organisations can effectively limit the window of vulnerability, enhancing overall security posture and mitigating the threat of unauthorised access to critical resources within their Azure environment.
Reduces the risk of prolonged exposure to elevated permissions.
Azure AD Privileged Identity Management’s capability to reduce the risk of prolonged exposure to elevated permissions is a significant advantage for organisations aiming to enhance their security posture. By implementing just-in-time access controls, users are granted temporary privileged roles only when needed, minimising the window of vulnerability. This proactive approach helps mitigate the chances of unauthorised access or misuse of elevated permissions over an extended period, thereby bolstering overall security and reducing potential threats within the Azure environment.
Provides multi-factor authentication for added security.
Azure AD Privileged Identity Management offers a significant advantage by providing multi-factor authentication for enhanced security. This feature adds an extra layer of protection to verify the identity of users accessing privileged roles within the Azure environment. By requiring multiple forms of verification, such as passwords, biometrics, or security tokens, organisations can significantly reduce the risk of unauthorised access to critical resources. Multi-factor authentication is a powerful tool in mitigating cybersecurity threats and ensuring that only authorised personnel can utilise elevated permissions, thereby bolstering overall security measures in the cloud environment.
Offers approval workflows for reviewing and authorising access requests.
Azure AD Privileged Identity Management provides a valuable feature by offering approval workflows for reviewing and authorising access requests. This capability ensures that requests for elevated permissions undergo a structured review process, where designated approvers can assess the necessity and legitimacy of the access before granting it. By incorporating approval workflows, organisations can enforce a layer of accountability and oversight in managing privileged identities, enhancing security measures and compliance with regulatory standards.
Facilitates regular reviews of privileged roles to ensure compliance.
Azure AD Privileged Identity Management facilitates regular reviews of privileged roles to ensure compliance with regulatory requirements and internal policies. By enabling organisations to schedule periodic reviews of who has access to elevated permissions, Azure AD PIM helps maintain a secure and accountable environment. These regular audits not only enhance security by identifying and addressing any unnecessary or outdated privileges but also demonstrate a commitment to governance and data protection standards. Regular role reviews are essential in mitigating risks associated with privileged access and ensuring that access rights align with business needs and security best practices.
Generates detailed audit logs for tracking changes made by users with privileged access.
Azure AD Privileged Identity Management offers the valuable benefit of generating detailed audit logs that track changes made by users with privileged access. These logs provide organisations with a comprehensive record of activities, allowing them to monitor and analyse any modifications made to critical resources. By maintaining a clear trail of actions taken by privileged users, Azure AD PIM enhances transparency, accountability, and security within the Azure environment. Organizations can leverage these audit logs to investigate incidents, ensure compliance with regulations, and proactively detect any unauthorised or suspicious activities, ultimately strengthening their overall cybersecurity posture.
Centralised dashboard provides visibility into who has access to critical resources.
The centralised dashboard feature of Azure AD Privileged Identity Management offers a significant advantage by providing clear visibility into the individuals who have access to critical resources within an organisation’s Azure environment. This functionality allows administrators to easily monitor and track privileged access, ensuring that only authorised users are granted permissions to sensitive data and resources. By having a comprehensive overview of access rights through the centralised dashboard, organisations can effectively manage security risks, detect any anomalies, and maintain a secure environment in line with best practices and compliance standards.
Helps organisations meet regulatory requirements and internal security policies.
Azure AD Privileged Identity Management plays a crucial role in helping organisations meet regulatory requirements and internal security policies. By providing detailed audit logs, role reviews, and just-in-time access controls, Azure AD PIM enables businesses to monitor and manage privileged identities effectively. This proactive approach not only enhances security measures but also ensures compliance with industry regulations and internal security protocols. Organizations can rest assured that their critical resources are accessed only by authorised personnel, reducing the risk of data breaches and maintaining a robust security posture in the cloud environment.
Complex Configuration
Setting up Azure AD Privileged Identity Management can present a significant challenge due to its complex configuration requirements. Implementing the necessary settings and policies may demand a considerable investment of time and expertise from IT administrators. The intricate nature of configuring Azure AD PIM can lead to potential delays in deployment and may require additional training to ensure proper setup and management. Organizations considering the adoption of Azure AD PIM should be prepared for the complexities involved in the initial configuration process to effectively leverage its security benefits in the long run.
Cost Consideration
Cost Consideration: One significant drawback of implementing Azure AD Privileged Identity Management is the potential increase in costs, particularly for organisations with a substantial number of users or resources. The additional expenses associated with licensing, user subscriptions, and potentially required infrastructure upgrades can pose a financial challenge for some businesses. It is essential for organisations to carefully assess and plan for these costs before deciding to adopt Azure AD PIM to ensure that the benefits outweigh the financial implications.
User Adoption Challenges
User Adoption Challenges can pose a significant con when implementing Azure AD Privileged Identity Management. Users may encounter difficulties in adjusting to the new access management procedures introduced by Azure AD PIM, resulting in resistance or confusion. This resistance can hinder the smooth transition to more secure access practices and potentially delay the full realisation of the benefits that Azure AD PIM offers. Effective communication, training, and support are essential to address these challenges and ensure successful user adoption of the new privileged identity management processes.
Limited Customisation
Some organisations may encounter a drawback of Azure AD Privileged Identity Management in its limited customisation capabilities. While the tool offers robust security features, some businesses with unique security needs may find that the level of customisation options provided by Azure AD PIM is insufficient to address their specific requirements. This limitation could potentially hinder organisations that require highly tailored security configurations to align with their internal policies or industry regulations. In such cases, organisations may need to explore additional solutions or workarounds to complement Azure AD PIM and achieve a more bespoke security setup.