The Benefits of Bomgar Privileged Access Management (PAM)
In today’s digital landscape, securing privileged access to critical systems and data is paramount for organisations to prevent cyber threats and ensure data integrity. Bomgar Privileged Access Management (PAM) offers a comprehensive solution to manage, monitor, and secure privileged accounts within an organisation.
Enhanced Security
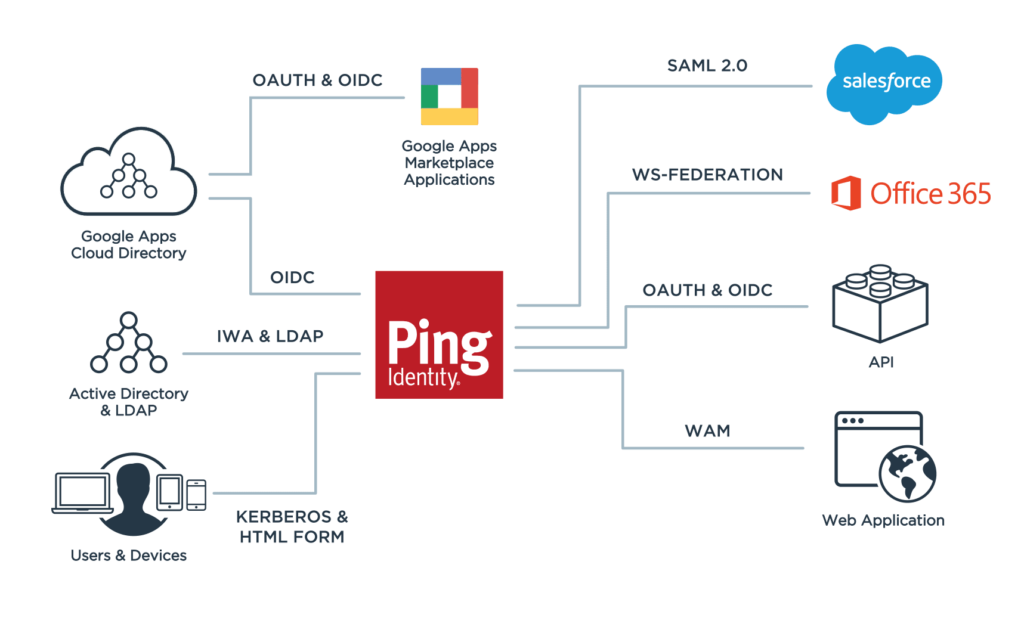
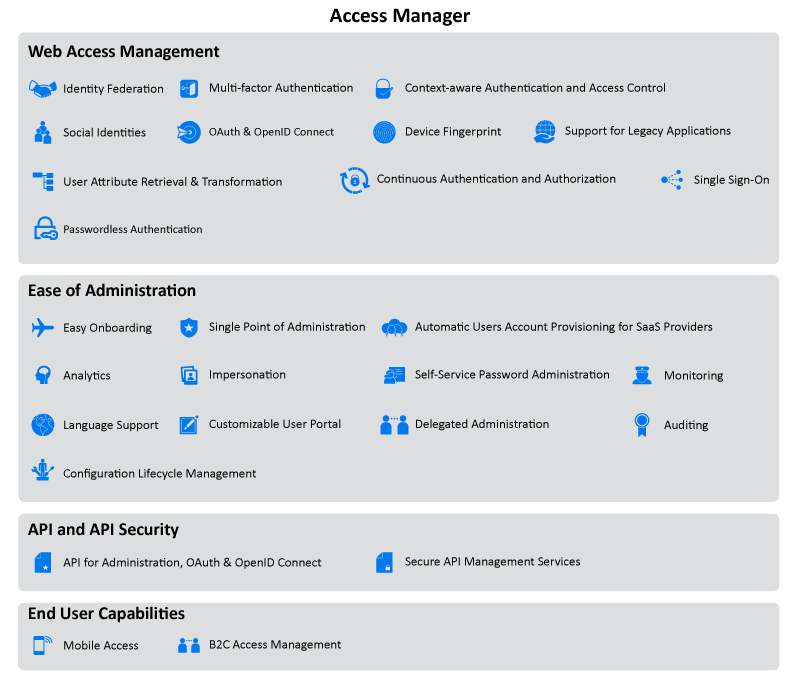
Bomgar PAM provides robust security measures that help prevent unauthorised access to sensitive information. By implementing granular access controls, session monitoring, and multi-factor authentication, organisations can significantly reduce the risk of insider threats and external attacks.
Efficient Access Management
With Bomgar PAM, administrators can streamline the management of privileged accounts across the enterprise. The platform offers centralised control over user access rights, simplifying account provisioning and deprovisioning processes. This ensures that only authorised personnel have access to critical systems and data.
Auditing and Compliance
Bomgar PAM facilitates comprehensive auditing capabilities that enable organisations to track all privileged account activities in real-time. By generating detailed audit logs and reports, organisations can demonstrate compliance with industry regulations and internal security policies.
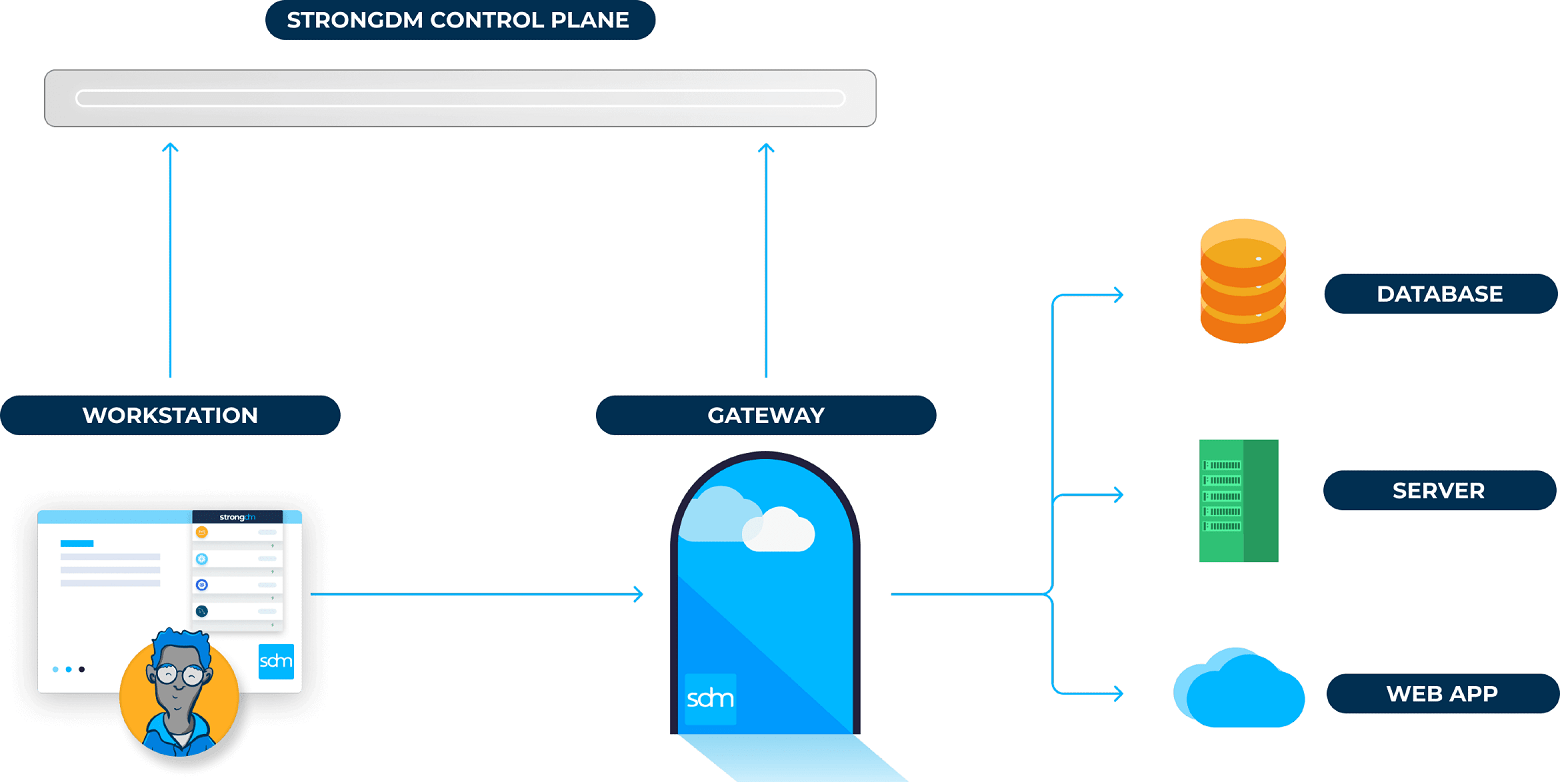
Secure Remote Access
One of the key features of Bomgar PAM is its secure remote access functionality. Organisations can allow users to remotely access systems without compromising security. The platform encrypts all remote sessions and provides secure channels for data transfer, ensuring that sensitive information remains protected at all times.
Scalability and Flexibility
Bomgar PAM is designed to scale according to the needs of an organisation. Whether managing a small team or a large enterprise, the platform offers flexibility in deployment options and customisation capabilities. This ensures that organisations can adapt their privileged access management strategy as their business grows.
Conclusion
In conclusion, Bomgar Privileged Access Management (PAM) is a powerful tool for organisations looking to enhance their cybersecurity posture and protect critical assets from potential threats. By implementing Bomgar PAM, organisations can achieve greater control over privileged accounts, strengthen security protocols, and ensure compliance with regulatory requirements.
Top 6 Tips for Enhancing Security and Efficiency with Bomgar PAM
- Ensure all users have strong, unique passwords for their Bomgar PAM accounts.
- Regularly review and update access permissions within Bomgar PAM to align with current roles and responsibilities.
- Enable multi-factor authentication (MFA) for an added layer of security when accessing Bomgar PAM.
- Monitor and log all activities within Bomgar PAM to detect any suspicious behaviour or unauthorized access.
- Regularly patch and update the Bomgar PAM software to protect against known vulnerabilities.
- Provide comprehensive training to users on how to effectively use Bomgar PAM’s features and security best practices.
Ensure all users have strong, unique passwords for their Bomgar PAM accounts.
To enhance the security of your organisation’s privileged access management, it is crucial to ensure that all users have strong and unique passwords for their Bomgar PAM accounts. Strong passwords significantly reduce the risk of unauthorised access to sensitive systems and data. Encouraging users to create complex passwords with a combination of letters, numbers, and special characters can bolster the overall security posture of your organisation. Regularly updating passwords and avoiding password reuse further strengthens the protection of privileged accounts within the Bomgar PAM system.
Regularly review and update access permissions within Bomgar PAM to align with current roles and responsibilities.
It is crucial to regularly review and update access permissions within Bomgar Privileged Access Management (PAM) to ensure alignment with current roles and responsibilities within the organisation. By conducting periodic reviews, administrators can verify that users have the appropriate level of access needed to perform their job functions effectively. Updating access permissions helps prevent unauthorised access and reduces the risk of security breaches. By maintaining accurate access controls in Bomgar PAM, organisations can enhance security measures and maintain compliance with internal policies and regulatory requirements.
Enable multi-factor authentication (MFA) for an added layer of security when accessing Bomgar PAM.
Enabling multi-factor authentication (MFA) is a crucial step in enhancing the security of your access to Bomgar Privileged Access Management (PAM). By requiring an additional verification method beyond just a password, such as a unique code sent to your mobile device, MFA adds an extra layer of protection against unauthorised access attempts. This proactive security measure significantly reduces the risk of account compromise and strengthens the overall security posture of your privileged accounts within the Bomgar PAM platform.
Monitor and log all activities within Bomgar PAM to detect any suspicious behaviour or unauthorized access.
To maximise the security benefits of Bomgar Privileged Access Management (PAM), it is crucial to diligently monitor and log all activities within the platform. By keeping a close eye on user actions and system events, organisations can swiftly detect any signs of suspicious behaviour or unauthorised access attempts. Real-time monitoring and detailed logging provide valuable insights into user activities, enabling prompt response to potential security threats. This proactive approach enhances overall cybersecurity posture and helps maintain the integrity of privileged accounts within the organisation.
Regularly patch and update the Bomgar PAM software to protect against known vulnerabilities.
Regularly patching and updating the Bomgar Privileged Access Management (PAM) software is essential to safeguarding your organisation’s security posture. By staying current with software updates, you can effectively mitigate known vulnerabilities and ensure that your PAM system remains resilient against emerging cyber threats. Timely updates not only enhance the overall security of your privileged access management solution but also demonstrate a proactive approach to maintaining a secure IT environment.
Provide comprehensive training to users on how to effectively use Bomgar PAM’s features and security best practices.
It is crucial to provide comprehensive training to users on how to effectively utilise Bomgar Privileged Access Management (PAM)’s features and adhere to security best practices. By educating users on the functionalities of Bomgar PAM and the importance of following security protocols, organisations can enhance overall cybersecurity posture. Training sessions can empower users to make informed decisions when accessing privileged accounts, reducing the risk of security breaches and ensuring that sensitive information remains protected. Investing in user training demonstrates a commitment to maintaining a secure environment and maximising the benefits of Bomgar PAM within the organisation.