The Importance of SAP Cloud Identity Access Governance
In today’s digital landscape, where data breaches and cyber threats are on the rise, ensuring secure access to sensitive information is paramount for organisations. SAP Cloud Identity Access Governance (IAG) plays a crucial role in managing user identities, permissions, and access rights within the SAP ecosystem.
With the increasing adoption of cloud-based solutions and remote work scenarios, traditional methods of managing user access have become outdated and ineffective. SAP Cloud IAG provides a comprehensive framework for governing access to SAP applications and data in a streamlined and efficient manner.
Key Benefits of SAP Cloud IAG:
- Enhanced Security: By centralising identity management and access control, SAP Cloud IAG helps prevent unauthorised access to critical systems and data. It allows organisations to set up role-based access controls, segregation of duties, and automated provisioning/deprovisioning processes.
- Compliance Management: With regulatory requirements becoming more stringent, maintaining compliance with industry standards such as GDPR, HIPAA, or SOX is essential. SAP Cloud IAG offers tools for audit trails, policy enforcement, and reporting to ensure adherence to compliance regulations.
- Improved User Experience: Simplifying user access through single sign-on (SSO) capabilities enhances user productivity and reduces the burden on IT support teams. Users can securely access multiple applications with a single set of credentials.
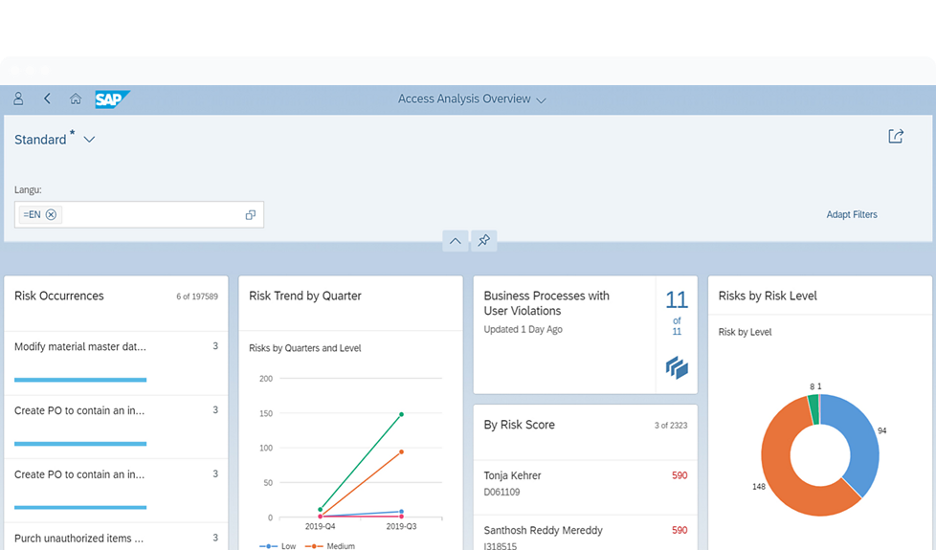
- Risk Mitigation: Proactively identifying and mitigating security risks is crucial in today’s threat landscape. SAP Cloud IAG enables continuous monitoring of user activities, anomaly detection, and real-time alerts to address potential security threats before they escalate.
Implementation Best Practices:
To maximise the benefits of SAP Cloud IAG implementation, organisations should follow best practices such as:
- Define Clear Policies: Establish clear policies for user roles, permissions, and access levels based on job responsibilities.
- Regular Audits: Conduct regular audits to review user access rights and identify any discrepancies or violations.
- User Training: Provide comprehensive training to users on security best practices, password management, and data protection guidelines.
- Continuous Monitoring: Implement tools for continuous monitoring of user activities to detect suspicious behaviour or unauthorised access attempts.
In conclusion, SAP Cloud Identity Access Governance is a critical component of modern IT security strategies. By implementing robust identity management practices with SAP Cloud IAG, organisations can enhance security posture, streamline compliance efforts, and improve overall operational efficiency in an increasingly digital world.
Top 5 Tips for Effective Management of SAP Cloud Identity Access Governance
- Define clear access policies and roles within SAP Cloud Identity Access Governance.
- Regularly review and update user access rights to ensure compliance with security standards.
- Implement segregation of duties to prevent conflicts of interest and reduce risks.
- Utilize automated workflows for access requests, approvals, and certifications to streamline processes.
- Monitor user activity and access changes for suspicious behaviour or violations.
Define clear access policies and roles within SAP Cloud Identity Access Governance.
Defining clear access policies and roles within SAP Cloud Identity Access Governance is a foundational step towards establishing a secure and well-managed IT environment. By clearly outlining user roles, permissions, and access levels based on job responsibilities, organisations can ensure that users have the appropriate level of access to perform their tasks effectively while minimising the risk of unauthorised access to sensitive data. This proactive approach not only enhances security but also streamlines compliance efforts by aligning user access with regulatory requirements. Clear access policies and roles within SAP Cloud Identity Access Governance lay the groundwork for a robust identity management framework that supports the overall security posture of the organisation.
Regularly review and update user access rights to ensure compliance with security standards.
Regularly reviewing and updating user access rights is a fundamental practice in SAP Cloud Identity Access Governance to maintain compliance with security standards. By conducting periodic audits of user permissions and access levels, organisations can identify and rectify any discrepancies or potential security risks. This proactive approach not only helps in ensuring that users have the necessary access for their roles but also mitigates the risk of unauthorised access to sensitive data. By staying vigilant and responsive to changes in user access requirements, organisations can strengthen their security posture and uphold compliance with industry regulations effectively.
Implement segregation of duties to prevent conflicts of interest and reduce risks.
Implementing segregation of duties within SAP Cloud Identity Access Governance is a crucial step in mitigating risks and ensuring a robust security posture. By defining clear boundaries and assigning specific access privileges based on job roles, organisations can prevent conflicts of interest and reduce the likelihood of fraudulent activities. Segregation of duties helps maintain accountability, transparency, and compliance with regulatory requirements by ensuring that no single user has unchecked control over critical systems or data. This proactive measure enhances overall security resilience and minimises the potential impact of internal threats within the SAP environment.
Utilize automated workflows for access requests, approvals, and certifications to streamline processes.
By utilising automated workflows for access requests, approvals, and certifications within SAP Cloud Identity Access Governance, organisations can streamline their processes effectively. Automation enables the swift handling of access requests, accelerates approval cycles, and ensures timely certifications of user access rights. By automating these tasks, companies can enhance operational efficiency, reduce manual errors, and maintain a more secure and compliant environment. This proactive approach to managing access controls not only saves time and resources but also strengthens overall security measures within the organisation’s SAP ecosystem.
Monitor user activity and access changes for suspicious behaviour or violations.
Monitoring user activity and access changes is a crucial aspect of SAP Cloud Identity Access Governance. By keeping a close eye on user interactions within the system, organisations can proactively detect any suspicious behaviour or violations that may indicate a security threat. Real-time monitoring allows for immediate response to potential risks, ensuring the integrity of sensitive data and maintaining compliance with regulatory requirements. By staying vigilant and promptly addressing any anomalies in user activity, organisations can enhance their overall security posture and mitigate potential threats effectively.