The Importance of Software Configuration Management
Software Configuration Management (SCM) is a critical process in software development that ensures the consistency and integrity of software products throughout their lifecycle. It involves managing and controlling changes to software artifacts, such as source code, documentation, and configuration files, to improve quality, facilitate collaboration, and streamline development processes.
Key Benefits of SCM:
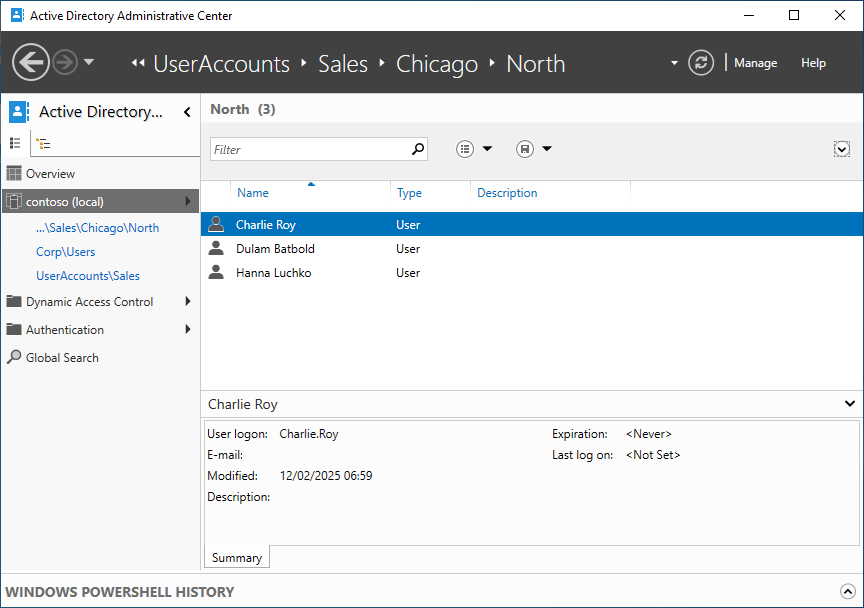
- Version Control: SCM helps developers track changes made to code over time, enabling them to revert to previous versions if needed and collaborate effectively in a team environment.
- Configuration Identification: By uniquely identifying software components and their versions, SCM allows for accurate tracking of changes and dependencies.
- Change Management: SCM provides mechanisms for managing change requests, evaluating their impact, and ensuring that only approved changes are implemented.
- Build Automation: SCM tools can automate the build process, ensuring that the software is built consistently across different environments.
- Auditing and Compliance: SCM maintains a detailed record of changes made to software artifacts, which is crucial for auditing purposes and compliance with regulatory requirements.
Best Practices in SCM:
To maximise the benefits of Software Configuration Management, organisations should adhere to best practices such as:
- Establishing Clear Policies: Define clear guidelines for version control, branching strategies, code reviews, and release management.
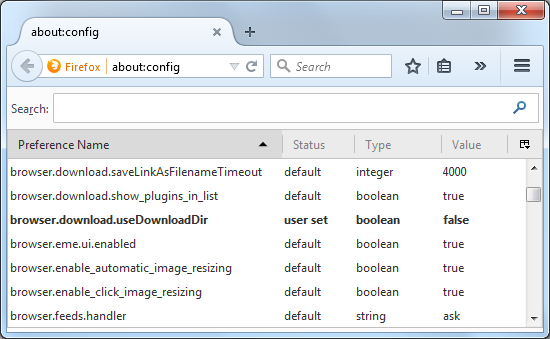
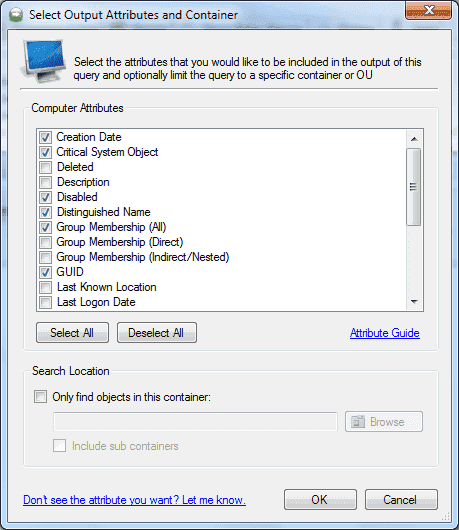
- Automating Processes: Use automated tools for version control, continuous integration, testing, and deployment to improve efficiency and reduce errors.
- Cross-Functional Collaboration: Encourage collaboration between development, testing, operations teams to ensure seamless integration of changes.
- Rigorous Testing: Implement robust testing procedures to validate changes before they are integrated into the main codebase.
- Maintaining Documentation: Document all configuration items, change requests, and release notes to facilitate transparency and knowledge sharing.
In conclusion, Software Configuration Management plays a vital role in ensuring the reliability, scalability and maintainability of software applications. By implementing effective SCM practices and leveraging modern tools and technologies, organisations can streamline their development processes, enhance collaboration among team members,
mitigate risks associated with change management,
comply with industry standards,
achieve faster time-to-market,
thereby delivering high-quality software products that meet customer expectations.
Understanding Software Configuration Management: Key FAQs and Best Practices
- What is Software Configuration Management (SCM)?
- Why is Software Configuration Management important in software development?
- What are the key benefits of implementing Software Configuration Management?
- How does Version Control contribute to Software Configuration Management?
- What are the best practices for effective Software Configuration Management?
- How can Automation tools improve Software Configuration Management processes?
- What role does Compliance and Auditing play in Software Configuration Management?
What is Software Configuration Management (SCM)?
Software Configuration Management (SCM) is a fundamental process in software development that encompasses the management and control of changes to software artifacts throughout their lifecycle. SCM involves maintaining the integrity and consistency of software components, such as source code, documentation, and configuration files, to facilitate collaboration, enhance quality, and streamline development workflows. By implementing SCM practices, organisations can effectively track versions of software components, manage change requests, automate build processes, ensure compliance with regulatory standards, and improve overall project management efficiency. SCM is essential for maintaining a structured approach to software development and ensuring that software products are delivered successfully with minimal risks and errors.
Why is Software Configuration Management important in software development?
Software Configuration Management (SCM) is crucial in software development for several reasons. Firstly, SCM ensures the consistency and integrity of software products by managing changes to code, documentation, and other artifacts. This consistency is essential for maintaining the quality and reliability of the software throughout its lifecycle. Secondly, SCM facilitates collaboration among team members by providing version control mechanisms that enable developers to work on the same codebase concurrently without conflicts. Additionally, SCM helps in tracking changes, identifying dependencies, and managing configurations effectively, which is vital for project scalability and maintenance. Overall, Software Configuration Management plays a pivotal role in enhancing productivity, ensuring traceability of changes, and enabling efficient development processes in software projects.
What are the key benefits of implementing Software Configuration Management?
When considering the implementation of Software Configuration Management (SCM), it is essential to understand the key benefits it offers to software development processes. By implementing SCM practices, organisations can achieve improved version control, ensuring that changes to software artifacts are tracked and managed effectively. Additionally, SCM aids in configuration identification, enabling accurate tracking of software components and their dependencies. Change management is streamlined through SCM, allowing for the evaluation and implementation of approved changes while maintaining a clear audit trail. Automation of build processes and compliance with regulatory requirements are further advantages of implementing SCM, ultimately leading to enhanced collaboration, efficiency, and quality in software development projects.
How does Version Control contribute to Software Configuration Management?
Version control is a fundamental aspect of Software Configuration Management that significantly contributes to the overall integrity and efficiency of software development processes. By implementing version control systems, developers can track changes made to code, documentation, and other software artifacts over time. This capability enables teams to collaborate effectively, maintain a history of modifications, revert to previous versions if necessary, and ensure consistency across different environments. Version control plays a crucial role in managing configurations, facilitating change management, enhancing traceability, and ultimately improving the quality and reliability of software products throughout their lifecycle.
What are the best practices for effective Software Configuration Management?
When it comes to effective Software Configuration Management, adhering to best practices is essential for ensuring the integrity and efficiency of software development processes. Some key best practices include establishing clear policies and guidelines for version control, branching strategies, code reviews, and release management. Automation of processes such as version control, continuous integration, testing, and deployment can significantly improve productivity and reduce errors. Encouraging cross-functional collaboration between development, testing, and operations teams is crucial for seamless integration of changes. Rigorous testing procedures should be implemented to validate changes before integration into the main codebase. Documentation of all configuration items, change requests, and release notes is also vital for transparency and knowledge sharing within the team. By following these best practices, organisations can enhance their Software Configuration Management processes and deliver high-quality software products efficiently.
How can Automation tools improve Software Configuration Management processes?
Automation tools play a pivotal role in enhancing Software Configuration Management processes by streamlining repetitive tasks, reducing human error, and increasing efficiency. These tools enable automatic version control, continuous integration, testing, and deployment, ensuring that software artifacts are managed consistently and accurately. By automating routine procedures, teams can focus on more strategic aspects of development, such as code quality and innovation. Automation tools also facilitate collaboration among team members by providing a centralised platform for tracking changes and coordinating workflows. Overall, the use of automation tools in Software Configuration Management leads to improved productivity, faster time-to-market, and higher software quality standards.
What role does Compliance and Auditing play in Software Configuration Management?
Compliance and auditing are integral aspects of Software Configuration Management (SCM) as they ensure that software development processes adhere to regulatory requirements, industry standards, and internal policies. Compliance measures help organisations mitigate risks, maintain data integrity, and protect sensitive information. Auditing in SCM involves conducting regular reviews and assessments of configuration items, changes made to the software, and access controls to ensure accountability and traceability. By incorporating compliance and auditing practices into SCM processes, companies can demonstrate transparency, improve governance, and enhance the overall quality of their software products while meeting legal obligations and industry best practices.