The Power of Reporting Software: Enhancing Business Insights
In today’s data-driven world, businesses rely on accurate and timely information to make informed decisions. Reporting software plays a crucial role in collecting, analysing, and presenting data in a meaningful way that empowers organisations to gain valuable insights.
Efficiency and Accuracy
Reporting software automates the process of data collection and analysis, eliminating the need for manual data entry and manipulation. This not only saves time but also reduces the risk of human error, ensuring that reports are accurate and reliable.
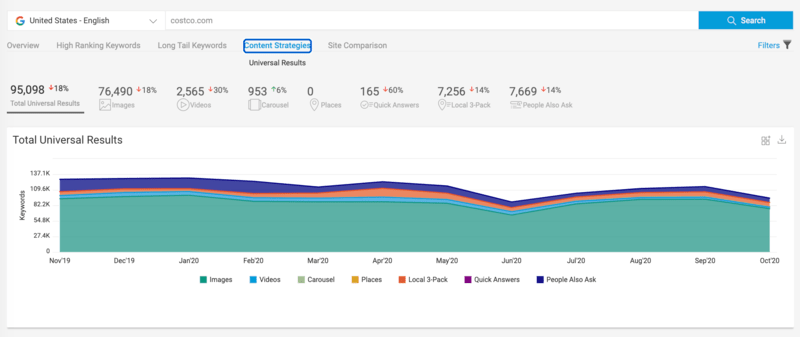
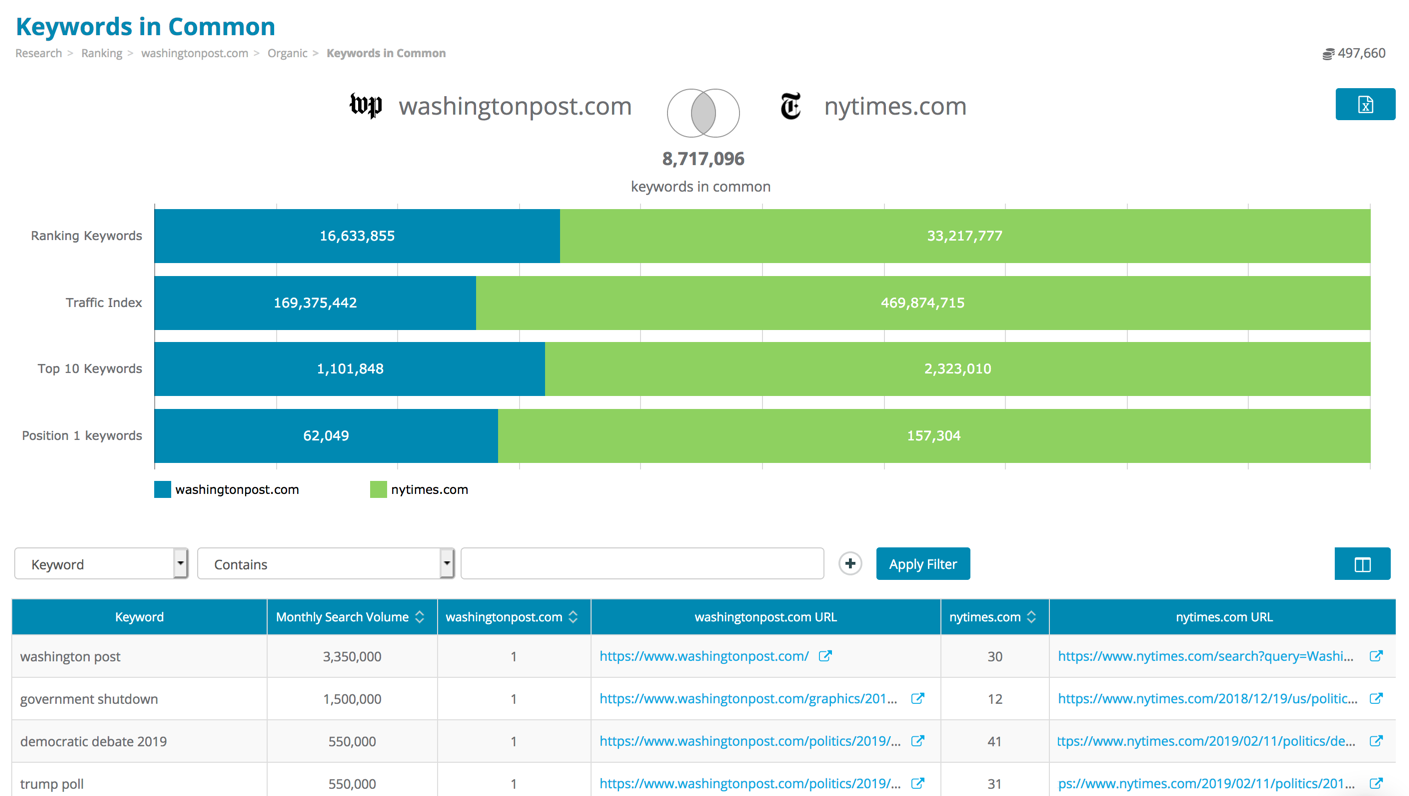
Data Visualisation
Visual representations of data through charts, graphs, and dashboards help users understand complex information at a glance. Reporting software allows businesses to customise visualisations to suit their specific needs, making it easier to identify trends, patterns, and outliers within the data.
Real-Time Insights
With reporting software, businesses can access real-time data updates and generate reports on-demand. This agility enables organisations to respond quickly to changing market conditions and make informed decisions based on the most up-to-date information available.
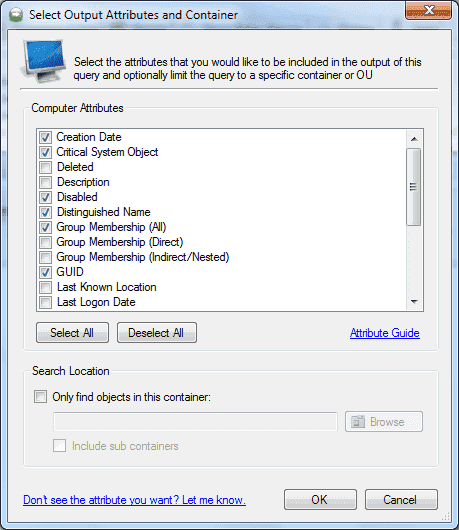
Customisation and Flexibility
Reporting software offers flexibility in report customisation, allowing users to tailor reports according to their requirements. Whether it’s adjusting parameters, adding filters, or choosing specific metrics to display, businesses can create reports that align with their unique needs and goals.
Compliance and Governance
Reporting software helps businesses ensure compliance with regulations by providing audit trails and documentation of data sources. This transparency not only enhances governance but also builds trust with stakeholders by demonstrating a commitment to data integrity and security.
Conclusion
Reporting software is a powerful tool that empowers businesses with actionable insights derived from data analysis. By leveraging reporting software effectively, organisations can streamline decision-making processes, improve operational efficiency, and drive business growth in today’s competitive landscape.
Understanding Reporting Software: Key Questions and Answers
- What is a reporting software?
- What is MIS reporting tool?
- What is the best tool for reporting?
- What are the 3 types of reporting?
- What is reporting software?
- What are different types of reporting tools?
- Which software is best for reporting?
- What are reporting tools examples?
What is a reporting software?
A reporting software is a specialised tool designed to collect, analyse, and present data in a structured format for businesses and organisations. It automates the process of generating reports by extracting information from various data sources, transforming it into meaningful insights through visualisations such as charts and graphs. Reporting software enables users to create customised reports tailored to their specific needs, providing valuable insights that support informed decision-making. By simplifying data analysis and presentation, reporting software enhances efficiency, accuracy, and agility in accessing real-time information crucial for driving business success.
What is MIS reporting tool?
An MIS reporting tool, short for Management Information System reporting tool, is a software application designed to gather, analyse, and present data from various sources within an organisation to support managerial decision-making. This tool enables users to generate customised reports that provide insights into key performance indicators, trends, and metrics relevant to the organisation’s operations. By offering a comprehensive view of data in a structured format, MIS reporting tools help managers monitor performance, track progress towards goals, and identify areas for improvement across different departments or functions within the business.
What is the best tool for reporting?
When it comes to determining the best tool for reporting, the answer largely depends on the specific needs and requirements of the organisation. There is a wide range of reporting software available in the market, each offering unique features and capabilities tailored to different industries and business sizes. Factors such as data complexity, user-friendliness, customisation options, integration capabilities, and budget constraints all play a crucial role in selecting the most suitable reporting tool. It is essential for businesses to thoroughly evaluate their reporting needs and conduct thorough research to identify a solution that aligns closely with their objectives and enhances their ability to derive meaningful insights from data analysis.
What are the 3 types of reporting?
In the realm of reporting software, there are three primary types of reporting that cater to different informational needs within an organisation. The first type is operational reporting, which focuses on providing day-to-day insights into business activities and processes. This type of reporting is crucial for monitoring key performance indicators and ensuring operational efficiency. The second type is tactical reporting, which delves deeper into specific areas of the business to support decision-making at a departmental level. Tactical reports often highlight trends, patterns, and exceptions that require immediate attention. Lastly, strategic reporting offers a broader view of the overall performance of the organisation by analysing long-term trends and forecasting future opportunities or challenges. Strategic reports are instrumental in guiding high-level strategic decisions that shape the direction of the business. Each type of reporting serves a distinct purpose in helping businesses extract meaningful insights from their data to drive success and growth.
What is reporting software?
Reporting software is a specialised tool designed to collect, analyse, and present data in a structured format to facilitate informed decision-making within organisations. It automates the process of generating reports by extracting data from various sources, transforming it into meaningful insights through visualisations such as charts and graphs, and delivering actionable information to users. Reporting software enables businesses to track key performance indicators, monitor trends, and gain valuable insights into their operations, ultimately enhancing efficiency and driving strategic decision-making processes.
What are different types of reporting tools?
When exploring the realm of reporting software, it is common to encounter the frequently asked question: “What are different types of reporting tools?” There is a diverse range of reporting tools available to cater to various business needs and preferences. Some popular types include business intelligence tools, which offer advanced analytics and data visualisation capabilities; self-service reporting tools that empower users to create custom reports without IT assistance; dashboarding tools for real-time monitoring and KPI tracking; and ad-hoc reporting tools that allow for on-the-fly report generation based on specific criteria. Each type of reporting tool serves a unique purpose in helping businesses extract insights from their data and make informed decisions.
Which software is best for reporting?
When it comes to determining the best software for reporting, the answer largely depends on the specific needs and requirements of the individual or organisation seeking a reporting solution. There is a wide range of reporting software available in the market, each offering unique features and capabilities tailored to different industries and use cases. Factors to consider when selecting reporting software include ease of use, scalability, integration capabilities with existing systems, customisation options, data visualisation tools, real-time reporting capabilities, and compliance with industry regulations. It is recommended to conduct thorough research, evaluate demo versions, seek recommendations from industry peers, and consider consulting with experts to identify the best reporting software that aligns with your objectives and delivers the insights needed to drive informed decision-making.
What are reporting tools examples?
Reporting tools are essential components for businesses seeking to streamline data analysis and presentation. Examples of popular reporting tools include Microsoft Power BI, Tableau, Google Data Studio, and SAP Crystal Reports. These tools offer a range of features such as data visualisation, customisable dashboards, and real-time reporting capabilities. By utilising these reporting tools, organisations can effectively transform raw data into actionable insights, enabling informed decision-making and enhancing overall business performance.